MITRE Engage Home
Become an Engage Benefactor

MITRE Engage is a framework
for planning and discussing adversary engagement operations
that empowers you to engage your adversaries
and achieve your cybersecurity goals.
![]() Scroll to learn more!
Scroll to learn more!
Tools
Deception is a process, not a fire-and-forget technology stack.
The tools below will guide you through that process.
MATRIX
A shared reference that bridges gaps between defenders, decision makers, and vendors.
PLAYBOOK
Actionable and pragmatic guidance for integrating adversary engagement.
PROCESS
Methods to plan and learn from engagements, building capabilities with every operation.
COMMUNITY
Cyber professionals contributing expertise and sharing insights into adversary behaviors.
STANDARDS
Standards and terminology to apply, assess, and validate engagement operations and tools.
MINDSET
Empowering you to redefine what security means and rethink how to achieve it.
Why Engage?
With traditional cyber defense, the adversary only needs to be right once …
… but with adversary engagement, the adversary only needs to be wrong once.

TRADITIONAL APPROACH
- Secure perimeter
- Vulnerable interior
- IP and data are legitimate, so stealing this data is a win for the adversary
ADVERSARY ENGAGEMENT
- Secure perimeter
- Secure interior
- Not all IP and data are legitimate — stealing this data does not guarantee a win for the adversary

TRADITIONAL APPROACH
- Secure perimeter
- Vulnerable interior
- IP and data are legitimate, so stealing this data is a win for the adversary
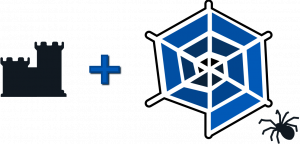
ADVERSARY ENGAGEMENT
- Secure perimeter
- Secure interior
- Not all IP and data are legitimate — stealing this data does not guarantee a win for the adversary
Why Engage is for You
Bridging the gaps between diverse users,
Engage empowers …
Defenders
Start engaging your adversaries, build capabilities with each operation, and grow the community of AE practitioners.
Decision Makers
Transform your cyber strategy, gain information instead of losing it, and effectively lead your organization.
Vendors
Provide more value to your users, expedite adoption of your tools, and assess and validate your tools.

STARTER KIT
Our starter kit contains everything you need to plan, execute, and analyze adversary engagement operations!
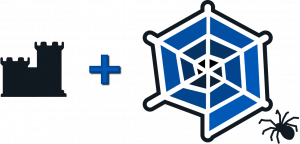
The Engage Matrix
Engage provides defenders with goal-driven approaches …
… to evolve their defenses and remain in control.
Our Engage Story
Why trust MITRE?
Our experts have used adversary engagement to defend MITRE for over a decade.
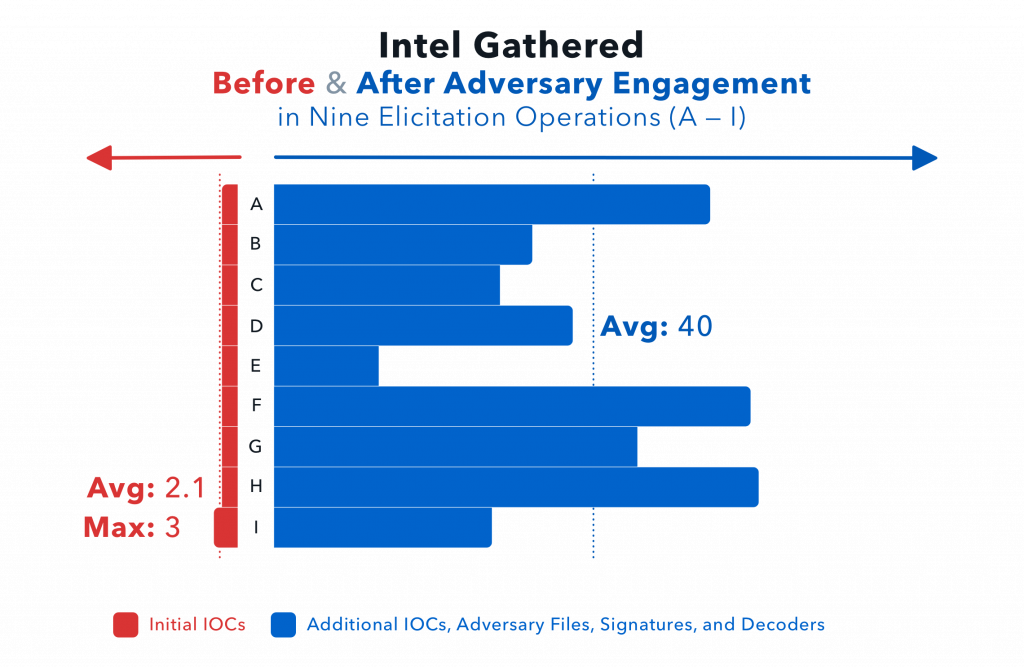
The chart below shows intel gathered in nine elicitation operations run by MITRE with and without adversary engagement. Before adversary engagement, MITRE detected only initial IOCs, with an average of about two per operation. After adversary engagement, MITRE was able to collect, on average, 40 new pieces of intel per operation!
“With the adversary engagement approach, you craft internal deception infrastructure that allows you to expose, manipulate, and understand your adversaries.”
—Dr. Stan Barr, Principal Scientist
Engage with Us
The cyber community’s needs and experiences actively shape Engage, so let’s connect!
Email us at engage@mitre.org — or fill out the form below.
Copyright © 2022 The MITRE Corporation. All Rights Reserved.