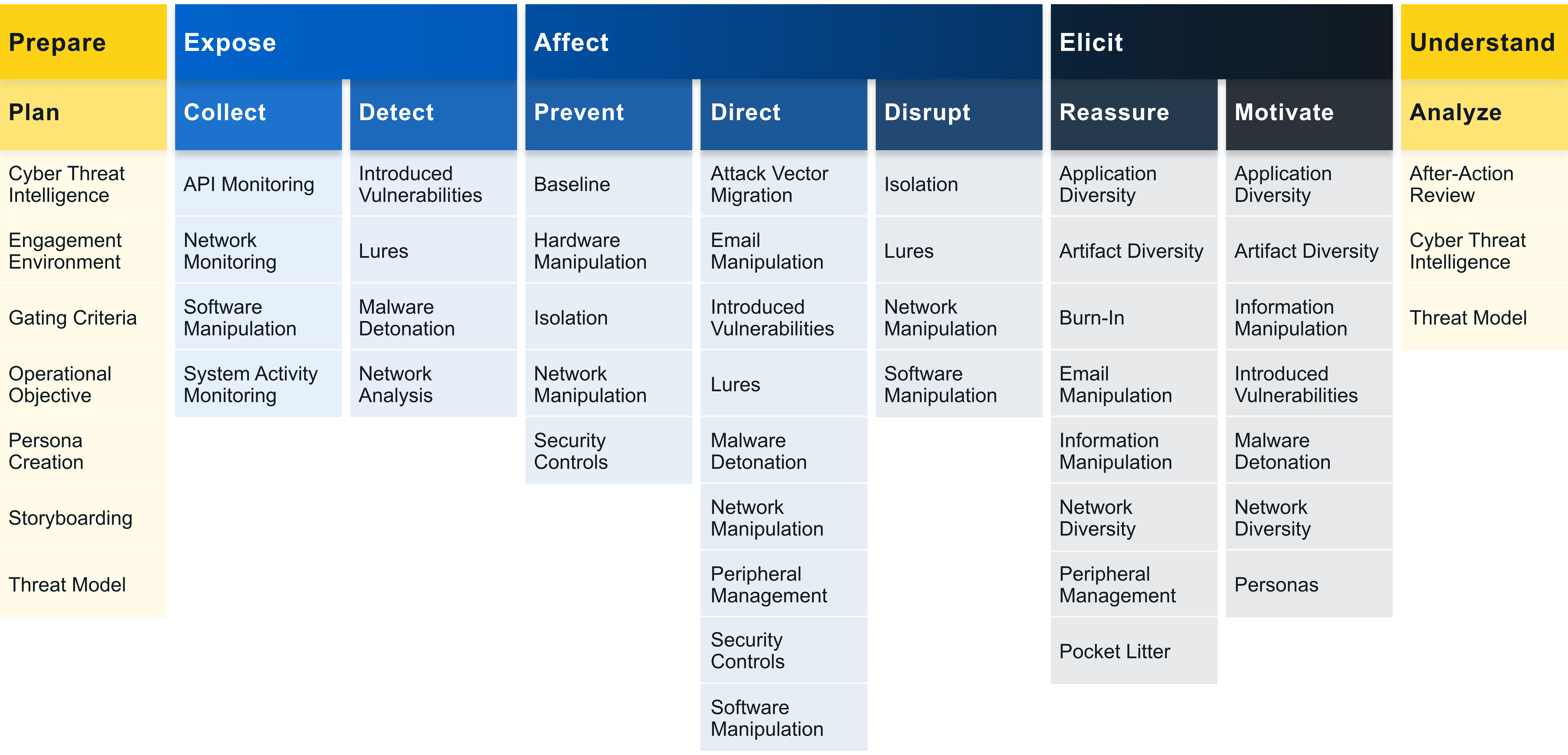
Matrix
View settings:
PGRpdiBjbGFzcz0iZXRfcGJfcm93IGV0X3BiX3Jvd18yIGFwaS1tb25pdG9yaW5nLWRldGFpbCBtYXRyaXgtZGV0YWlscyBldF9wYl9ndXR0ZXJzMSBldF9oYWRfYW5pbWF0aW9uIiBzdHlsZT0iZGlzcGxheTogbm9uZTsiPgogICAgPGRpdiBjbGFzcz0iZXRfcGJfY29sdW1uIGV0X3BiX2NvbHVtbl80XzQgZXRfcGJfY29sdW1uXzUgZXRfcGJfY3NzX21peF9ibGVuZF9tb2RlX3Bhc3N0aHJvdWdoIGV0LWxhc3QtY2hpbGQiPgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8wIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGg0IGNsYXNzPSJldF9wYl9tb2R1bGVfaGVhZGVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4gc3R5bGU9ImZvbnQtc2l6ZTogMjBweCAhaW1wb3J0YW50O2xpbmUtaGVpZ2h0OiAxICFpbXBvcnRhbnQ7Zm9udC13ZWlnaHQ6IDYwMCAhaW1wb3J0YW50Ij5BUEkgTW9uaXRvcmluZzwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBFQUMwMDAxPC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+TW9uaXRvciBsb2NhbCBBUElzIHRoYXQgbWlnaHQgYmUgdXNlZCBieSBhZHZlcnNhcnkgdG9vbHMgYW5kIGFjdGl2aXR5LjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBhcGktbW9uaXRvcmluZy1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+QVBJIE1vbml0b3JpbmcgaW52b2x2ZXMgY2FwdHVyaW5nIGFuIGludGVybmFsIE9TIGZ1bmN0aW9uIGZvciBpdHMgdXNhZ2UsIGFjY29tcGFueWluZyBhcmd1bWVudHMsIGFuZCByZXN1bHQuIFdoZW4gYSBkZWZlbmRlciBjYXB0dXJlcyB0aGlzIGluZm9ybWF0aW9uLCB0aGUgZGF0YSBnYXRoZXJlZCBjYW4gYmUgYW5hbHl6ZWQgdG8gZ2FpbiBpbnNpZ2h0cyBpbnRvIHRoZSBhY3Rpdml0eSBvZiBhbiBhZHZlcnNhcnkgYXQgYSBsZXZlbCBkZWVwZXIgdGhhbiBub3JtYWwgc3lzdGVtIGFjdGl2aXR5IG1vbml0b3JpbmcuIFRoaXMgdHlwZSBvZiBtb25pdG9yaW5nIGNhbiBhbHNvIGJlIHVzZWQgdG8gcHJvZHVjZSBoaWdoLWZpZGVsaXR5IGRldGVjdGlvbnMuIEZvciBleGFtcGxlLCB0aGUgZGVmZW5kZXIgY2FuIHRyYWNlIGFjdGl2aXR5IHRocm91Z2ggV2luU29jayBUQ1AgQVBJIGZ1bmN0aW9ucyB0byB2aWV3IHBvdGVudGlhbGx5IG1hbGljaW91cyBuZXR3b3JrIGV2ZW50cyBvciB0cmFjZSB1c2FnZSBvZiB0aGUgV2luMzIgRGVsZXRlRmlsZSgpIGZ1bmN0aW9uIHRvIGxvZyBhbGwgYXR0ZW1wdHMgYXQgZGVsZXRpbmcgYSBnaXZlbiBmaWxlLjwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgYXBpLW1vbml0b3JpbmctcmVmZXJlbmNlcyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InR0YWJsZSB0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBSZWZlcmVuY2UgTGlua3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vYXJ4aXYub3JnL3BkZi8yMDA1LjAwMzIzIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+RGVzaWduaW5nIFJvYnVzdCBBUEkgTW9uaXRvcmluZyBTb2x1dGlvbnM8L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vbGluay5zcHJpbmdlci5jb20vY2hhcHRlci8xMC4xMDA3Lzk3OC0zLTY0Mi00MTI4NC00XzciIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5JbnRlcm5hdGlvbmFsIFdvcmtzaG9wIE9uIFJlY2VudCBBZHZhbmNlcyBJbiBJbnRydXNpb24gRGV0ZWN0aW9uPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2FqYXltYXMuZ2l0aHViLmlvL0lTREEyMDE5LnBkZiIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPkFQSSBDYWxsIEJhc2VkIE1hbHdhcmUgRGV0ZWN0aW9uIEFwcHJvYWNoIFVzaW5nIFJlY3VycmVudCBOZXVyYWwgTmV0d29yay0tLUxTVE08L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgYXBpLW1vbml0b3JpbmctYXR0YWNrLW1hcHBpbmdzIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPkVudGVycHJpc2U8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA3Ij5EaXNjb3Zlcnk8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggdGhlIGVudmlyb25tZW50IG9yIHBlcnNvbmFzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHdoZW4gdGhleSBjb2xsZWN0LCBvYnNlcnZlLCBvciBtYW5pcHVsYXRlIHN5c3RlbSBhcnRpZmFjdHMgb3IgaW5mb3JtYXRpb24uIE1hbmlwdWxhdGVkIGRhdGEgbWF5IGNhdXNlIHRoZW0gdG8gcmV2ZWFsIGJlaGF2aW9ycywgdXNlIGFkZGl0aW9uYWwgb3IgbW9yZSBhZHZhbmNlZCBjYXBhYmlsaXRpZXMgYWdhaW5zdCB0aGUgdGFyZ2V0LCBhbmQvb3IgaW1wYWN0IHRoZWlyIGR3ZWxsIHRpbWUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MCI+SW1wYWN0PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOCI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBuZXR3b3JrIG9yIHN5c3RlbSByZXNvdXJjZXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdHJpZ2dlcmluZyB0cmlwd2lyZXMgb3IgZW5nYWdpbmcgaW4gZWFzaWx5IGRldGVjdGFibGUsIGFub21hbG91cyBiZWhhdmlvci48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDExIj5Db21tYW5kIGFuZCBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA2Ij5DcmVkZW50aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNSI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA3Ij5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDIiPkV4ZWN1dGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MCI+SW1wYWN0PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAzIj5QZXJzaXN0ZW5jZTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNCI+UHJpdmlsZWdlIEVzY2FsYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHV0aWxpemUgb3IgYWJ1c2Ugc3lzdGVtIGZlYXR1cmVzLCBzb2Z0d2FyZSwgb3Igb3RoZXIgcmVzb3VyY2VzLCB0aGV5IG1heSBiZSB2dWxuZXJhYmxlIHRvIG1vbml0b3Jpbmcgb3IgTWFuLWluLXRoZS1NaWRkbGUgbWFuaXB1bGF0aW9uLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+TW9iaWxlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMSI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggdGhlIGVudmlyb25tZW50IG9yIHBlcnNvbmFzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHdoZW4gdGhleSBjb2xsZWN0LCBvYnNlcnZlLCBvciBtYW5pcHVsYXRlIHN5c3RlbSBhcnRpZmFjdHMgb3IgaW5mb3JtYXRpb24uIE1hbmlwdWxhdGVkIGRhdGEgbWF5IGNhdXNlIHRoZW0gdG8gcmV2ZWFsIGJlaGF2aW9ycywgdXNlIGFkZGl0aW9uYWwgb3IgbW9yZSBhZHZhbmNlZCBjYXBhYmlsaXRpZXMgYWdhaW5zdCB0aGUgdGFyZ2V0LCBhbmQvb3IgaW1wYWN0IHRoZWlyIGR3ZWxsIHRpbWUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNyI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMCI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM0Ij5JbXBhY3Q8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMjciPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMzIj5MYXRlcmFsIE1vdmVtZW50PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIG5ldHdvcmsgb3Igc3lzdGVtIHJlc291cmNlcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB0cmlnZ2VyaW5nIHRyaXB3aXJlcyBvciBlbmdhZ2luZyBpbiBlYXNpbHkgZGV0ZWN0YWJsZSwgYW5vbWFsb3VzIGJlaGF2aW9yLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwNDEiPkV4ZWN1dGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgcmVseSBvbiBzcGVjaWZpYyByZXNvdXJjZXMgdG8gYmUgZW5hYmxlZCwgYWNjZXNzaWJsZSwgYW5kL29yIHZ1bG5lcmFibGUsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdGhlaXIgb3BlcmF0aW9ucyBiZWluZyBkaXNydXB0ZWQgaWYgdGhlIHJlc291cmNlcyBhcmUgZGlzYWJsZWQsIHJlbW92ZWQsIG9yIG90aGVyd2lzZSBtYWRlIGludnVsbmVyYWJsZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMwIj5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzIiPkRpc2NvdmVyeTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MSI+RXhlY3V0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDI4Ij5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXRpbGl6ZSBvciBhYnVzZSBzeXN0ZW0gZmVhdHVyZXMsIHNvZnR3YXJlLCBvciBvdGhlciByZXNvdXJjZXMsIHRoZXkgbWF5IGJlIHZ1bG5lcmFibGUgdG8gbW9uaXRvcmluZyBvciBNYW4taW4tdGhlLU1pZGRsZSBtYW5pcHVsYXRpb24uPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAyOSI+UHJpdmlsZWdlIEVzY2FsYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGVuYWJsZWQsIGFjY2Vzc2libGUsIG9yIGludGVudGlvbmFsbHkgd2Vha2VuZWQvb3Zlcmx5IHBlcm1pc3NpdmUgcmVzb3VyY2VzIGluIHRoZSBlbnZpcm9ubWVudCAocHJvZHVjdGlvbiBvciBpc29sYXRlZCksIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gcmV2ZWFsaW5nIGFkZGl0aW9uYWwgb3IgbW9yZSBhZHZhbmNlZCBjYXBhYmlsaXRpZXMgd2hlbiBleHBsb2l0aW5nIG9yIHVzaW5nIHNhaWQgcmVzb3VyY2UuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMiI+RGlzY292ZXJ5PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBhIGRpdmVyc2Ugc2V0IG9mIGFjY2Vzc2libGUgcmVzb3VyY2VzIGFuZCBkZWNveSBhcnRpZmFjdHMgb24gdGhlIHRhcmdldCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzIGFuZCBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5JQ1M8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA1Ij5JbXBhY3Q8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDYiPkltcGFpciBQcm9jZXNzIENvbnRyb2w8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggZW5nYWdlbWVudCBlbnZpcm9ubWVudHMgYW5kIHBlcnNvbmFzLCB0aGVpciBmdXR1cmUgY2FwYWJpbGl0eSwgdGFyZ2V0aW5nLCBhbmQvb3IgaW5mcmFzdHJ1Y3R1cmUgcmVxdWlyZW1lbnRzIGFyZSB2dWxuZXJhYmxlIHRvIGluZmx1ZW5jZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA0Ij5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDciPkluaGliaXQgUmVzcG9uc2UgRnVuY3Rpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggbmV0d29yayBvciBzeXN0ZW0gcmVzb3VyY2VzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRyaWdnZXJpbmcgdHJpcHdpcmVzIG9yIGVuZ2FnaW5nIGluIGVhc2lseSBkZXRlY3RhYmxlLCBhbm9tYWxvdXMgYmVoYXZpb3IuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNSI+SW1wYWN0PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyByZWx5IG9uIHNwZWNpZmljIHJlc291cmNlcyB0byBiZSBlbmFibGVkLCBhY2Nlc3NpYmxlLCBhbmQvb3IgdnVsbmVyYWJsZSwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB0aGVpciBvcGVyYXRpb25zIGJlaW5nIGRpc3J1cHRlZCBpZiB0aGUgcmVzb3VyY2VzIGFyZSBkaXNhYmxlZCwgcmVtb3ZlZCwgb3Igb3RoZXJ3aXNlIG1hZGUgaW52dWxuZXJhYmxlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDAiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDIiPkRpc2NvdmVyeTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMyI+RXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNCI+RXhlY3V0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA1Ij5JbXBhY3Q8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDciPkluaGliaXQgUmVzcG9uc2UgRnVuY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDkiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMTAiPlBlcnNpc3RlbmNlPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTExIj5Qcml2aWxlZ2UgRXNjYWxhdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXRpbGl6ZSBvciBhYnVzZSBzeXN0ZW0gZmVhdHVyZXMsIHNvZnR3YXJlLCBvciBvdGhlciByZXNvdXJjZXMsIHRoZXkgbWF5IGJlIHZ1bG5lcmFibGUgdG8gbW9uaXRvcmluZyBvciBNYW4taW4tdGhlLU1pZGRsZSBtYW5pcHVsYXRpb24uPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgbmV0d29yay1tb25pdG9yaW5nLWRldGFpbCBtYXRyaXgtZGV0YWlscyBldF9wYl9ndXR0ZXJzMSBldF9oYWRfYW5pbWF0aW9uIiBzdHlsZT0iZGlzcGxheTogbm9uZTsiPgogICAgPGRpdiBjbGFzcz0iZXRfcGJfY29sdW1uIGV0X3BiX2NvbHVtbl80XzQgZXRfcGJfY29sdW1uXzUgZXRfcGJfY3NzX21peF9ibGVuZF9tb2RlX3Bhc3N0aHJvdWdoIGV0LWxhc3QtY2hpbGQiPgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8wIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGg0IGNsYXNzPSJldF9wYl9tb2R1bGVfaGVhZGVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4gc3R5bGU9ImZvbnQtc2l6ZTogMjBweCAhaW1wb3J0YW50O2xpbmUtaGVpZ2h0OiAxICFpbXBvcnRhbnQ7Zm9udC13ZWlnaHQ6IDYwMCAhaW1wb3J0YW50Ij5OZXR3b3JrIE1vbml0b3Jpbmc8L3NwYW4+CiAgICAgICAgICAgICAgICAgICAgPC9oND4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxoNT5JRDogRUFDMDAwMjwvaDU+CiAgICAgICAgICAgICAgICAgICAgICAgIDxwPk1vbml0b3IgbmV0d29yayB0cmFmZmljIGluIG9yZGVyIHRvIGRldGVjdCBhZHZlcnNhcnkgYWN0aXZpdHkuPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIG5ldHdvcmstbW9uaXRvcmluZy1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+TmV0d29yayBNb25pdG9yaW5nIGludm9sdmVzIGNhcHR1cmluZyBuZXR3b3JrIGFjdGl2aXR5IGRhdGEsIGluY2x1ZGluZyBjYXB0dXJpbmcgc2VydmVyLCBmaXJld2FsbCwgYW5kIG90aGVyIHJlbGV2YW50IGxvZ3MuIEEgZGVmZW5kZXIgY2FuIHNlbmQgdGhpcyBkYXRhIHRvIGEgY2VudHJhbGl6ZWQgY29sbGVjdGlvbiBsb2NhdGlvbiBmb3IgZnVydGhlciBhbmFseXNpcy4gVGhpcyBhbmFseXNpcyBjYW4gYmUgYXV0b21hdGVkIG9yIG1hbnVhbC4gSW4gZWl0aGVyIGNhc2UsIGEgZGVmZW5kZXIgY2FuIHVzZSBOZXR3b3JrIE1vbml0b3JpbmcgdG8gaWRlbnRpZnkgYW5vbWFsb3VzIHRyYWZmaWMgcGF0dGVybnMsIGxhcmdlIG9yIHVuZXhwZWN0ZWQgZGF0YSB0cmFuc2ZlcnMsIGFuZCBvdGhlciBhY3Rpdml0eSB0aGF0IG1heSByZXZlYWwgdGhlIHByZXNlbmNlIG9mIGFuIGFkdmVyc2FyeS4gIE1vbml0b3JpbmcgaXMgZXNzZW50aWFsIHRvIG1haW50YWluIHNpdHVhdGlvbmFsIGF3YXJlbmVzcyBvZiBhZHZlcnNhcnkgYWN0aXZpdGllcyB0byBlbnN1cmUgb3BlcmF0aW9uYWwgc2FmZXR5IGFuZCBtYWtlIHByb2dyZXNzIHRvd2FyZHMgdGhlIGRlZmVuZGVy4oCZcyBnb2Fscy4gQ2FyZWZ1bCBwcmUtb3BlcmF0aW9uYWwgcGxhbm5pbmcgc2hvdWxkIGJlIGRvbmUgdG8gcHJvcGVybHkgaW5zdHJ1bWVudCB0aGUgZW5nYWdlbWVudCBlbnZpcm9ubWVudCB0byBlbnN1cmUgdGhhdCBhbGwga2V5IG5ldHdvcmsgdHJhZmZpYyBpcyBjb2xsZWN0ZWQuIFNvbWUgdXNlIGNhc2VzIG9mIG5ldHdvcmsgbW9uaXRvcmluZyBpbmNsdWRlIGRldGVjdGluZyB1bmV4cGVjdGVkIG91dGJvdW5kIHRyYWZmaWMsIHN5c3RlbXMgZXN0YWJsaXNoaW5nIGNvbm5lY3Rpb25zIHVzaW5nIGVuY2Fwc3VsYXRlZCBwcm90b2NvbHMsIGFuZCBrbm93biBhZHZlcnNhcnkgQzIgcHJvdG9jb2xzLjwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgbmV0d29yay1tb25pdG9yaW5nLXJlZmVyZW5jZXMgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0dGFibGUgdGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgUmVmZXJlbmNlIExpbmtzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL3d3dy5yZXNlYXJjaGdhdGUubmV0L3B1YmxpY2F0aW9uLzMwOTIyOTI0Nl9BX1N1cnZleV9vbl9OZXR3b3JrX1NlY3VyaXR5X01vbml0b3JpbmdfU3lzdGVtcyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPkEgU3VydmV5IE9uIE5ldHdvcmsgU2VjdXJpdHkgTW9uaXRvcmluZyBTeXN0ZW1zPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL3d3dy5oaW5kYXdpLmNvbS9qb3VybmFscy9qZWNlLzIwMTYvNjI5NzQ3Ni8iIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5Qcm90ZWN0aW5nIENsb2NrIFN5bmNocm9uaXphdGlvbjogQWR2ZXJzYXJ5IERldGVjdGlvbiBUaHJvdWdoIE5ldHdvcmsgTW9uaXRvcmluZzwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cHM6Ly93d3cudXNlbml4Lm9yZy9sZWdhY3kvcHVibGljYXRpb25zL2xpYnJhcnkvcHJvY2VlZGluZ3Mvc2VjOTgvZnVsbF9wYXBlcnMvcGF4c29uL3BheHNvbi5wZGYiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5Ccm86IEEgU3lzdGVtIEZvciBEZXRlY3RpbmcgTmV0d29yayBJbnRydWRlcnMgSW4gUmVhbC1UaW1lPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL3d3dy5zY2llbmNlZGlyZWN0LmNvbS9zY2llbmNlL2FydGljbGUvcGlpL1MxMzYzNDEyNzk4ODAwMzgxIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+SW1wbGVtZW50aW5nIEEgR2VuZXJhbGl6ZWQgVG9vbCBGb3IgTmV0d29yayBNb25pdG9yaW5nPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2llZWV4cGxvcmUuaWVlZS5vcmcvYWJzdHJhY3QvZG9jdW1lbnQvNDY2MDAzMCIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPlNweW1vbjogSGlkZGVuIE5ldHdvcmsgTW9uaXRvcmluZyBGb3IgU2VjdXJpdHkgSW4gV2lyZWxlc3MgU2Vuc29yIE5ldHdvcmtzPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIG5ldHdvcmstbW9uaXRvcmluZy1hdHRhY2stbWFwcGluZ3MgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+RW50ZXJwcmlzZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDkiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMTEiPkNvbW1hbmQgYW5kIENvbnRyb2w8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDYiPkNyZWRlbnRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA1Ij5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwNDAiPkltcGFjdDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOCI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggbmV0d29yayBvciBzeXN0ZW0gcmVzb3VyY2VzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRyaWdnZXJpbmcgdHJpcHdpcmVzIG9yIGVuZ2FnaW5nIGluIGVhc2lseSBkZXRlY3RhYmxlLCBhbm9tYWxvdXMgYmVoYXZpb3IuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAxMSI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAxMCI+RXhmaWx0cmF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBleGZpbHRyYXRlIGRhdGEsIHRoZWlyIGRhdGEgYXJlIHZ1bG5lcmFibGUgdG8gb2JzZXJ2YXRpb24gb3IgbWFuaXB1bGF0aW9uIHZpYSBNYW4taW4tdGhlLU1pZGRsZSBhY3Rpdml0aWVzLiA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDExIj5Db21tYW5kIGFuZCBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA1Ij5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMTAiPkV4ZmlsdHJhdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHVzZSBlYXNpbHkgaWRlbnRpZmlhYmxlIHRlY2huaXF1ZXMsIG9yIGdlbmVyYXRlIHNpZ25hdHVyYWJsZSBwYXR0ZXJucyBpbiBkYXRhIG9yIHRyYWZmaWMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gZGV0ZWN0aW9uIG9mIHRoZWlyIGFjdGl2aXR5LjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+TW9iaWxlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMiI+RGlzY292ZXJ5PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIHRoZSBlbnZpcm9ubWVudCBvciBwZXJzb25hcywgdGhleSBhcmUgdnVsbmVyYWJsZSB3aGVuIHRoZXkgY29sbGVjdCwgb2JzZXJ2ZSwgb3IgbWFuaXB1bGF0ZSBzeXN0ZW0gYXJ0aWZhY3RzIG9yIGluZm9ybWF0aW9uLiBNYW5pcHVsYXRlZCBkYXRhIG1heSBjYXVzZSB0aGVtIHRvIHJldmVhbCBiZWhhdmlvcnMsIHVzZSBhZGRpdGlvbmFsIG9yIG1vcmUgYWR2YW5jZWQgY2FwYWJpbGl0aWVzIGFnYWluc3QgdGhlIHRhcmdldCwgYW5kL29yIGltcGFjdCB0aGVpciBkd2VsbCB0aW1lLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzUiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzciPkNvbW1hbmQgYW5kIENvbnRyb2w8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzQiPkltcGFjdDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBuZXR3b3JrIG9yIHN5c3RlbSByZXNvdXJjZXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdHJpZ2dlcmluZyB0cmlwd2lyZXMgb3IgZW5nYWdpbmcgaW4gZWFzaWx5IGRldGVjdGFibGUsIGFub21hbG91cyBiZWhhdmlvci48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMyIj5EaXNjb3Zlcnk8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHV0aWxpemUgb3IgYWJ1c2Ugc3lzdGVtIGZlYXR1cmVzLCBzb2Z0d2FyZSwgb3Igb3RoZXIgcmVzb3VyY2VzLCB0aGV5IG1heSBiZSB2dWxuZXJhYmxlIHRvIG1vbml0b3Jpbmcgb3IgTWFuLWluLXRoZS1NaWRkbGUgbWFuaXB1bGF0aW9uLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzMiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGVuYWJsZWQsIGFjY2Vzc2libGUsIG9yIGludGVudGlvbmFsbHkgd2Vha2VuZWQvb3Zlcmx5IHBlcm1pc3NpdmUgcmVzb3VyY2VzIGluIHRoZSBlbnZpcm9ubWVudCAocHJvZHVjdGlvbiBvciBpc29sYXRlZCksIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gcmV2ZWFsaW5nIGFkZGl0aW9uYWwgb3IgbW9yZSBhZHZhbmNlZCBjYXBhYmlsaXRpZXMgd2hlbiBleHBsb2l0aW5nIG9yIHVzaW5nIHNhaWQgcmVzb3VyY2UuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMiI+RGlzY292ZXJ5PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBhIGRpdmVyc2Ugc2V0IG9mIGFjY2Vzc2libGUgcmVzb3VyY2VzIGFuZCBkZWNveSBhcnRpZmFjdHMgb24gdGhlIHRhcmdldCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzIGFuZCBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMCI+RGVmZW5zZSBFdmFzaW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBtb3ZlIGRhdGEgYWNyb3NzIHRoZSBuZXR3b3JrIG9yIGludGVyYWN0IHdpdGggcmVtb3RlIHJlc291cmNlcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBuZXR3b3JrIG1hbmlwdWxhdGlvbnMgc3VjaCBhcyBpbXBhY3RzIHRvIG5ldHdvcmsgYXZhaWxhYmlsaXR5LCB0cmFmZmljIGZpbHRlcmluZywgZGVncmFkZWQgc3BlZWRzLCBldGMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNyI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMCI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM2Ij5FeGZpbHRyYXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzQiPkltcGFjdDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZXhmaWx0cmF0ZSBkYXRhLCB0aGVpciBkYXRhIGFyZSB2dWxuZXJhYmxlIHRvIG9ic2VydmF0aW9uIG9yIG1hbmlwdWxhdGlvbiB2aWEgTWFuLWluLXRoZS1NaWRkbGUgYWN0aXZpdGllcy4gPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNyI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMCI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM2Ij5FeGZpbHRyYXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzQiPkltcGFjdDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXNlIGVhc2lseSBpZGVudGlmaWFibGUgdGVjaG5pcXVlcywgb3IgZ2VuZXJhdGUgc2lnbmF0dXJhYmxlIHBhdHRlcm5zIGluIGRhdGEgb3IgdHJhZmZpYywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBkZXRlY3Rpb24gb2YgdGhlaXIgYWN0aXZpdHkuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5JQ1M8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAzIj5FdmFzaW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBhIGRpdmVyc2Ugc2V0IG9mIGFjY2Vzc2libGUgcmVzb3VyY2VzIGFuZCBkZWNveSBhcnRpZmFjdHMgb24gdGhlIHRhcmdldCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzIGFuZCBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMCI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNSI+SW1wYWN0PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBleGZpbHRyYXRlIGRhdGEsIHRoZWlyIGRhdGEgYXJlIHZ1bG5lcmFibGUgdG8gb2JzZXJ2YXRpb24gb3IgbWFuaXB1bGF0aW9uIHZpYSBNYW4taW4tdGhlLU1pZGRsZSBhY3Rpdml0aWVzLiA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAxIj5Db21tYW5kIGFuZCBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA0Ij5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDUiPkltcGFjdDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNyI+SW5oaWJpdCBSZXNwb25zZSBGdW5jdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXNlIGVhc2lseSBpZGVudGlmaWFibGUgdGVjaG5pcXVlcywgb3IgZ2VuZXJhdGUgc2lnbmF0dXJhYmxlIHBhdHRlcm5zIGluIGRhdGEgb3IgdHJhZmZpYywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBkZXRlY3Rpb24gb2YgdGhlaXIgYWN0aXZpdHkuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMyI+RXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNCI+RXhlY3V0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA1Ij5JbXBhY3Q8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDYiPkltcGFpciBQcm9jZXNzIENvbnRyb2w8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDciPkluaGliaXQgUmVzcG9uc2UgRnVuY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMTAiPlBlcnNpc3RlbmNlPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBhdHRlbXB0IHRvIHJlbW90ZWx5IG1hbmlwdWxhdGUsIGRhbWFnZSBvciBlZmZlY3Qgc29tZSBjaGFuZ2UgaW4gdGhlIHBoeXNpY2FsIGVudmlyb25tZW50LCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIE1hbi1pbi10aGUtTWlkZGxlIG1hbmlwdWxhdGlvbnMuIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgIDwvZGl2Pgo8L2Rpdj4KPGRpdiBjbGFzcz0iZXRfcGJfcm93IGV0X3BiX3Jvd18yIHN5c3RlbS1hY3Rpdml0eS1tb25pdG9yaW5nLWRldGFpbCBtYXRyaXgtZGV0YWlscyBldF9wYl9ndXR0ZXJzMSBldF9oYWRfYW5pbWF0aW9uIiBzdHlsZT0iZGlzcGxheTogbm9uZTsiPgogICAgPGRpdiBjbGFzcz0iZXRfcGJfY29sdW1uIGV0X3BiX2NvbHVtbl80XzQgZXRfcGJfY29sdW1uXzUgZXRfcGJfY3NzX21peF9ibGVuZF9tb2RlX3Bhc3N0aHJvdWdoIGV0LWxhc3QtY2hpbGQiPgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8wIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGg0IGNsYXNzPSJldF9wYl9tb2R1bGVfaGVhZGVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4gc3R5bGU9ImZvbnQtc2l6ZTogMjBweCAhaW1wb3J0YW50O2xpbmUtaGVpZ2h0OiAxICFpbXBvcnRhbnQ7Zm9udC13ZWlnaHQ6IDYwMCAhaW1wb3J0YW50Ij5TeXN0ZW0gQWN0aXZpdHkgTW9uaXRvcmluZzwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBFQUMwMDAzPC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+Q29sbGVjdCBzeXN0ZW0gYWN0aXZpdHkgbG9ncyB0aGF0IGNhbiByZXZlYWwgYWR2ZXJzYXJ5IGFjdGl2aXR5LjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBzeXN0ZW0tYWN0aXZpdHktbW9uaXRvcmluZy1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+Q2FwdHVyaW5nIHN5c3RlbSBsb2dzIGNhbiBzaG93IGxvZ2lucywgdXNlciBhbmQgc3lzdGVtIGV2ZW50cywgZXRjLiBBIGRlZmVuZGVyIGNhbiB1c2Ugc3VjaCBpbmhlcmVudCBzeXN0ZW0gbG9nZ2luZyB0byBzdHVkeSBhbmQgY29sbGVjdCBmaXJzdC1oYW5kIG9ic2VydmF0aW9ucyBhYm91dCB0aGUgYWR2ZXJzYXJ54oCZcyBhY3Rpb25zIGFuZCB0b29scy4gIFRoaXMgZGF0YSBjYW4gYmUgc2VudCB0byBhIGNlbnRyYWxpemVkIGNvbGxlY3Rpb24gbG9jYXRpb24gZm9yIGZ1cnRoZXIgYW5hbHlzaXMuIENhcmVmdWwgcGxhbm5pbmcgc2hvdWxkIGJlIHVzZWQgdG8gZ3VpZGUgd2hpY2ggc3lzdGVtIGxvZ3MgYXJlIGNvbGxlY3RlZCBhbmQgYXQgd2hhdCBsZXZlbC4gSWYgdGhlIGxvZ2dpbmcgbGV2ZWwgaXMgc2V0IHRvbyBoaWdoIG9yIHRvbyBtYW55IHN5c3RlbSBsb2dzIGFyZSBjb2xsZWN0ZWQsIHRoZSBkZWZlbmRlciBtYXkgYmUgYmxpbmRlZCBieSB0aGUgZXhjZXNzIGRhdGEuIEZvciBleGFtcGxlLCB1bmRlcnN0YW5kaW5nIHRoZSBhZHZlcnNhcnnigJlzIGtub3duIFRUUHMgd2lsbCBoaWdobGlnaHQgcmVzb3VyY2VzIHRoZSBhZHZlcnNhcnkgaXMgbGlrZWx5IHRvIHRvdWNoIGFuZCB0aGVyZWZvcmUgd2hpY2ggc3lzdGVtIGxvZ3MgYXJlIGxpa2VseSB0byBjYXB0dXJlIGFkdmVyc2FyeSBhY3Rpdml0eS4gIE92ZXJhbGwsIFN5c3RlbSBBY3Rpdml0eSBNb25pdG9yaW5nIGlzIGVzc2VudGlhbCB0byBtYWludGFpbiBzaXR1YXRpb25hbCBhd2FyZW5lc3Mgb2YgYWR2ZXJzYXJpYWwgYWN0aXZpdGllcyBpbiBvcmRlciB0byBlbnN1cmUgb3BlcmF0aW9uYWwgc2FmZXR5IGFuZCBwcm9ncmVzcyB0b3dhcmRzIG9wZXJhdGlvbmFsIGdvYWxzLiBDYXJlZnVsIHByZS1vcGVyYXRpb25hbCBwbGFubmluZyBzaG91bGQgYmUgZG9uZSB0byBwcm9wZXJseSBpbnN0cnVtZW50IHRoZSBlbmdhZ2VtZW50IGVudmlyb25tZW50LiBUaGlzIHdpbGwgZW5zdXJlIHRoYXQgYWxsIGtleSBuZXR3b3JrIHRyYWZmaWMgaXMgY29sbGVjdGVkLjwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgc3lzdGVtLWFjdGl2aXR5LW1vbml0b3JpbmctcmVmZXJlbmNlcyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InR0YWJsZSB0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBSZWZlcmVuY2UgTGlua3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vY2l0ZXNlZXJ4LmlzdC5wc3UuZWR1L3ZpZXdkb2MvZG93bmxvYWQ/ZG9pPTEwLjEuMS40NjIuMTUwOCZhbXA7cmVwPXJlcDEmYW1wO3R5cGU9cGRmIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+U2lnbmF0dXJlIEJhc2VkIEludHJ1c2lvbiBEZXRlY3Rpb24gU3lzdGVtIFVzaW5nIFNOT1JUPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2llZWV4cGxvcmUuaWVlZS5vcmcvYWJzdHJhY3QvZG9jdW1lbnQvODcxNzg5MiIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPk1hY2hpbmUgTGVhcm5pbmcgQmFzZWQgSW5zaWRlciBUaHJlYXQgTW9kZWxsaW5nIEFuZCBEZXRlY3Rpb248L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vaWVlZXhwbG9yZS5pZWVlLm9yZy9kb2N1bWVudC84OTY4Njk3IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+UmVhbC1UaW1lIERldGVjdGlvbiBTeXN0ZW0gQWdhaW5zdCBNYWxpY2lvdXMgVG9vbHMgQnkgTW9uaXRvcmluZyBEbGwgT24gQ2xpZW50IENvbXB1dGVyczwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cHM6Ly9pZWVleHBsb3JlLmllZWUub3JnL2RvY3VtZW50LzcxNjMyNzkiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5EZXRlY3RpbmcgQVBUIE1hbHdhcmUgSW5mZWN0aW9ucyBCYXNlZCBPbiBNYWxpY2lvdXMgRE5TIEFuZCBUcmFmZmljIEFuYWx5c2lzPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIHN5c3RlbS1hY3Rpdml0eS1tb25pdG9yaW5nLWF0dGFjay1tYXBwaW5ncyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5FbnRlcnByaXNlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOCI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCB0aGUgZW52aXJvbm1lbnQgb3IgcGVyc29uYXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgd2hlbiB0aGV5IGNvbGxlY3QsIG9ic2VydmUsIG9yIG1hbmlwdWxhdGUgc3lzdGVtIGFydGlmYWN0cyBvciBpbmZvcm1hdGlvbi4gTWFuaXB1bGF0ZWQgZGF0YSBtYXkgY2F1c2UgdGhlbSB0byByZXZlYWwgYmVoYXZpb3JzLCB1c2UgYWRkaXRpb25hbCBvciBtb3JlIGFkdmFuY2VkIGNhcGFiaWxpdGllcyBhZ2FpbnN0IHRoZSB0YXJnZXQsIGFuZC9vciBpbXBhY3QgdGhlaXIgZHdlbGwgdGltZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA2Ij5DcmVkZW50aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNSI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAyIj5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwNDAiPkltcGFjdDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMSI+SW5pdGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDgiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDMiPlBlcnNpc3RlbmNlPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA0Ij5Qcml2aWxlZ2UgRXNjYWxhdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBuZXR3b3JrIG9yIHN5c3RlbSByZXNvdXJjZXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdHJpZ2dlcmluZyB0cmlwd2lyZXMgb3IgZW5nYWdpbmcgaW4gZWFzaWx5IGRldGVjdGFibGUsIGFub21hbG91cyBiZWhhdmlvci48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA2Ij5DcmVkZW50aWFsIEFjY2VzczwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXNlIHByZXZpb3VzbHkgc3RvbGVuIGluZm9ybWF0aW9uIHRvIGFjY2VzcyBvciBtb3ZlIGxhdGVyYWxseSB3aXRoaW4gYW4gZW52aXJvbm1lbnQsIHRoZXkgbWF5IHJldmVhbCBwcmV2aW91cyBjb2xsZWN0aW9uIGFjdGl2aXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAxMSI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNSI+RGVmZW5zZSBFdmFzaW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyB1dGlsaXplIG9yIGFidXNlIHN5c3RlbSBmZWF0dXJlcywgc29mdHdhcmUsIG9yIG90aGVyIHJlc291cmNlcywgdGhleSBtYXkgYmUgdnVsbmVyYWJsZSB0byBtb25pdG9yaW5nIG9yIE1hbi1pbi10aGUtTWlkZGxlIG1hbmlwdWxhdGlvbi48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAzIj5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXNlIGVhc2lseSBpZGVudGlmaWFibGUgdGVjaG5pcXVlcywgb3IgZ2VuZXJhdGUgc2lnbmF0dXJhYmxlIHBhdHRlcm5zIGluIGRhdGEgb3IgdHJhZmZpYywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBkZXRlY3Rpb24gb2YgdGhlaXIgYWN0aXZpdHkuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDQiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBjb2xsZWN0IG1hbmlwdWxhdGVkIGFydGlmYWN0cywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgcHJlc2VuY2Ugd2hlbiB1c2luZyBvciBtb3ZpbmcgdGhlIGFydGlmYWN0cyBlbHNld2hlcmUgaW4gdGhlIGVuZ2FnZW1lbnQgZW52aXJvbm1lbnQuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5Nb2JpbGU8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM1Ij5Db2xsZWN0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIHRoZSBlbnZpcm9ubWVudCBvciBwZXJzb25hcywgdGhleSBhcmUgdnVsbmVyYWJsZSB3aGVuIHRoZXkgY29sbGVjdCwgb2JzZXJ2ZSwgb3IgbWFuaXB1bGF0ZSBzeXN0ZW0gYXJ0aWZhY3RzIG9yIGluZm9ybWF0aW9uLiBNYW5pcHVsYXRlZCBkYXRhIG1heSBjYXVzZSB0aGVtIHRvIHJldmVhbCBiZWhhdmlvcnMsIHVzZSBhZGRpdGlvbmFsIG9yIG1vcmUgYWR2YW5jZWQgY2FwYWJpbGl0aWVzIGFnYWluc3QgdGhlIHRhcmdldCwgYW5kL29yIGltcGFjdCB0aGVpciBkd2VsbCB0aW1lLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzUiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzAiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MSI+RXhlY3V0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM0Ij5JbXBhY3Q8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMjciPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMzIj5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDI4Ij5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBuZXR3b3JrIG9yIHN5c3RlbSByZXNvdXJjZXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdHJpZ2dlcmluZyB0cmlwd2lyZXMgb3IgZW5nYWdpbmcgaW4gZWFzaWx5IGRldGVjdGFibGUsIGFub21hbG91cyBiZWhhdmlvci48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMwIj5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzQiPkltcGFjdDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXRpbGl6ZSBvciBhYnVzZSBzeXN0ZW0gZmVhdHVyZXMsIHNvZnR3YXJlLCBvciBvdGhlciByZXNvdXJjZXMsIHRoZXkgbWF5IGJlIHZ1bG5lcmFibGUgdG8gbW9uaXRvcmluZyBvciBNYW4taW4tdGhlLU1pZGRsZSBtYW5pcHVsYXRpb24uPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5JQ1M8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA1Ij5JbXBhY3Q8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDciPkluaGliaXQgUmVzcG9uc2UgRnVuY3Rpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggZW5nYWdlbWVudCBlbnZpcm9ubWVudHMgYW5kIHBlcnNvbmFzLCB0aGVpciBmdXR1cmUgY2FwYWJpbGl0eSwgdGFyZ2V0aW5nLCBhbmQvb3IgaW5mcmFzdHJ1Y3R1cmUgcmVxdWlyZW1lbnRzIGFyZSB2dWxuZXJhYmxlIHRvIGluZmx1ZW5jZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA5Ij5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTEwIj5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBuZXR3b3JrIG9yIHN5c3RlbSByZXNvdXJjZXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdHJpZ2dlcmluZyB0cmlwd2lyZXMgb3IgZW5nYWdpbmcgaW4gZWFzaWx5IGRldGVjdGFibGUsIGFub21hbG91cyBiZWhhdmlvci48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICA8L2Rpdj4KPC9kaXY+CjxkaXYgY2xhc3M9ImV0X3BiX3JvdyBldF9wYl9yb3dfMiBuZXR3b3JrLWFuYWx5c2lzLWRldGFpbCBtYXRyaXgtZGV0YWlscyBldF9wYl9ndXR0ZXJzMSBldF9oYWRfYW5pbWF0aW9uIiBzdHlsZT0iZGlzcGxheTogbm9uZTsiPgogICAgPGRpdiBjbGFzcz0iZXRfcGJfY29sdW1uIGV0X3BiX2NvbHVtbl80XzQgZXRfcGJfY29sdW1uXzUgZXRfcGJfY3NzX21peF9ibGVuZF9tb2RlX3Bhc3N0aHJvdWdoIGV0LWxhc3QtY2hpbGQiPgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8wIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGg0IGNsYXNzPSJldF9wYl9tb2R1bGVfaGVhZGVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4gc3R5bGU9ImZvbnQtc2l6ZTogMjBweCAhaW1wb3J0YW50O2xpbmUtaGVpZ2h0OiAxICFpbXBvcnRhbnQ7Zm9udC13ZWlnaHQ6IDYwMCAhaW1wb3J0YW50Ij5OZXR3b3JrIEFuYWx5c2lzPC9zcGFuPgogICAgICAgICAgICAgICAgICAgIDwvaDQ+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8aDU+SUQ6IEVBQzAwMDQ8L2g1PgogICAgICAgICAgICAgICAgICAgICAgICA8cD5BbmFseXplIG5ldHdvcmsgdHJhZmZpYyB0byBnYWluIGludGVsbGlnZW5jZSBvbiBjb21tdW5pY2F0aW9ucyBiZXR3ZWVuIHN5c3RlbXMuPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIG5ldHdvcmstYW5hbHlzaXMtbG9uZy1kZXNjcmlwdGlvbiBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPk5ldHdvcmsgYW5hbHlzaXMgY2FuIGJlIGFuIGF1dG9tYXRlZCBvciBtYW51YWwgdGFzayB0byByZXZpZXcgY29tbXVuaWNhdGlvbnMgYmV0d2VlbiBzeXN0ZW1zIHRvIGV4cG9zZSBhZHZlcnNhcnkgYWN0aXZpdHksIHN1Y2ggYXMgQzIgb3IgZGF0YSBleGZpbHRyYXRpb24gdHJhZmZpYy4gVGhpcyBhbmFseXNpcyBpcyBub3JtYWxseSBkb25lIGJ5IGNhcHR1cmluZyBhbmQgYW5hbHl6aW5nIHRyYWZmaWMgb24gdGhlIHdpcmUgb3IgZnJvbSBwcmV2aW91c2x5IGNvbGxlY3RlZCBwYWNrZXQgY2FwdHVyZS4gIFdoZW4gY3VzdG9tIHByb3RvY29scyBhcmUgaW4gdXNlLCBkZWZlbmRlcnMgY2FuIGxldmVyYWdlIHByb3RvY29sIGRlY29kZXIgZnJhbWV3b3Jrcy4gVGhlc2UgYXJlIGN1c3RvbWl6ZWQgY29kZSBtb2R1bGVzIHRoYXQgY2FuIHJlYWQgbmV0d29yayB0cmFmZmljIGFuZCBjb250ZXh0dWFsaXplIGFjdGl2aXR5IGJldHdlZW4gdGhlIEMyIG9wZXJhdG9yIGFuZCB0aGUgaW1wbGFudC4gVGhlc2UgZnJhbWV3b3JrcyBhcmUgb2Z0ZW4gcmVxdWlyZWQgdG8gcHJvY2VzcyBjb21wbGV4IGVuY3J5cHRpb24gY2lwaGVycyBhbmQgY3VzdG9tIHByb3RvY29scyBpbnRvIGEgaHVtYW4tcmVhZGFibGUgZm9ybWF0IGZvciBhbiBhbmFseXN0IHRvIGludGVycHJldC4gRGVjb2RlciBjcmVhdGlvbiByZXF1aXJlcyBtYWx3YXJlIGFuYWx5c2lzIG9mIHRoZSBpbXBsYW50IHRvIHVuZGVyc3RhbmQgdGhlIGRlc2lnbiBvZiB0aGUgcHJvdG9jb2wuIFdoaWxlIGEgaGlnaCBsZXZlbCBvZiB0ZWNobmljYWwgbWF0dXJpdHkgaXMgcmVxdWlyZWQgdG8gY3JlYXRlIHN1Y2ggYSBkZWNvZGVyLCBvbmNlIGNyZWF0ZWQgdGhleSBhcmUgaW52YWx1YWJsZSB0byB0aGUgZGVmZW5kZXIuICBGb3IgZXhhbXBsZSwgYSBkZWZlbmRlciBjYW4gdXNlIGEgcHJvdG9jb2wgZGVjb2RlIHRvIGRlY3J5cHQgbmV0d29yayBjYXB0dXJlIGRhdGEgYW5kIGV4cG9zZSBhbiBhZHZlcnNhcnnigJlzIEMyIG9yIGV4ZmlsdHJhdGlvbiBhY3Rpdml0eS4gTm90IG9ubHkgZG9lcyB0aGlzIGRhdGEgcHJvdmlkZSBleHF1aXNpdGUgaW50ZWxsaWdlbmNlIGluIHJlZ2FyZCB0byB0aGUgYWR2ZXJzYXJ54oCZcyBjb21tdW5pY2F0aW9ucyBjaGFubmVscyBhbmQgdGFyZ2V0aW5nIHByZWZlcmVuY2VzLCBidXQgaXQgYWxzbyBwcm92aWRlcyBmdXR1cmUgb3Bwb3J0dW5pdGllcyBmb3IgZGF0YSBtYW5pcHVsYXRpb24gdG8gZnVydGhlciBvcGVyYXRpb25hbCBnb2Fscy48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIG5ldHdvcmstYW5hbHlzaXMtcmVmZXJlbmNlcyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InR0YWJsZSB0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBSZWZlcmVuY2UgTGlua3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vc2VmY29tLmFzdS5lZHUvcHVibGljYXRpb25zL3V0aWxpemluZy1uZXR3b3JrLXNjaWVuY2UtaGljc3MyMDE1LnBkZiIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPlV0aWxpemluZyBOZXR3b3JrIFNjaWVuY2UgQW5kIEhvbmV5bmV0cyBGb3IgU29mdHdhcmUgSW5kdWNlZCBDeWJlciBJbmNpZGVudCBBbmFseXNpczwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cDovL3d3dy50aHVjc25ldC5vcmcvdXBsb2Fkcy8yLzUvMi84LzI1Mjg5Nzk1L2d1b2Rvbmdfemhhb19pZWVlX2FjY2Vzc18yMDE1LnBkZiIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPkRldGVjdGluZyBBUFQgTWFsd2FyZSBJbmZlY3Rpb25zIEJhc2VkIE9uIE1hbGljaW91cyBETlMgQW5kIFRyYWZmaWMgQW5hbHlzaXM8L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgbmV0d29yay1hbmFseXNpcy1hdHRhY2stbWFwcGluZ3MgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+RW50ZXJwcmlzZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMTAiPkV4ZmlsdHJhdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBuZXR3b3JrIG9yIHN5c3RlbSByZXNvdXJjZXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdHJpZ2dlcmluZyB0cmlwd2lyZXMgb3IgZW5nYWdpbmcgaW4gZWFzaWx5IGRldGVjdGFibGUsIGFub21hbG91cyBiZWhhdmlvci48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDExIj5Db21tYW5kIGFuZCBDb250cm9sPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBleGZpbHRyYXRlIGRhdGEsIHRoZWlyIGRhdGEgYXJlIHZ1bG5lcmFibGUgdG8gb2JzZXJ2YXRpb24gb3IgbWFuaXB1bGF0aW9uIHZpYSBNYW4taW4tdGhlLU1pZGRsZSBhY3Rpdml0aWVzLiA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDExIj5Db21tYW5kIGFuZCBDb250cm9sPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyB1c2UgZWFzaWx5IGlkZW50aWZpYWJsZSB0ZWNobmlxdWVzLCBvciBnZW5lcmF0ZSBzaWduYXR1cmFibGUgcGF0dGVybnMgaW4gZGF0YSBvciB0cmFmZmljLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIGRldGVjdGlvbiBvZiB0aGVpciBhY3Rpdml0eS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA5Ij5Db2xsZWN0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBhdHRlbXB0IHRvIGV4ZmlsdHJhdGUsIG1hbmlwdWxhdGUsIG9yIG1vdmUgbWFzc2l2ZSBkYXRhIG9iamVjdHMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gd2FzdGluZyByZXNvdXJjZXMgdG8gYWNjb21wbGlzaCB0aGUgdGFzay48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPk1vYmlsZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzciPkNvbW1hbmQgYW5kIENvbnRyb2w8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzAiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMiI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM2Ij5FeGZpbHRyYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggbmV0d29yayBvciBzeXN0ZW0gcmVzb3VyY2VzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRyaWdnZXJpbmcgdHJpcHdpcmVzIG9yIGVuZ2FnaW5nIGluIGVhc2lseSBkZXRlY3RhYmxlLCBhbm9tYWxvdXMgYmVoYXZpb3IuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMyI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZGlzY292ZXIgYSBkaXZlcnNlIHNldCBvZiBhY2Nlc3NpYmxlIHJlc291cmNlcyBhbmQgZGVjb3kgYXJ0aWZhY3RzIG9uIHRoZSB0YXJnZXQsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gcmV2ZWFsaW5nIHRoZWlyIHRhcmdldGluZyBwcmVmZXJlbmNlcyBhbmQgY2FwYWJpbGl0aWVzLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzciPkNvbW1hbmQgYW5kIENvbnRyb2w8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzAiPkRlZmVuc2UgRXZhc2lvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZXhmaWx0cmF0ZSBkYXRhLCB0aGVpciBkYXRhIGFyZSB2dWxuZXJhYmxlIHRvIG9ic2VydmF0aW9uIG9yIG1hbmlwdWxhdGlvbiB2aWEgTWFuLWluLXRoZS1NaWRkbGUgYWN0aXZpdGllcy4gPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgbHVyZXMtZGV0YWlsIG1hdHJpeC1kZXRhaWxzIGV0X3BiX2d1dHRlcnMxIGV0X2hhZF9hbmltYXRpb24iIHN0eWxlPSJkaXNwbGF5OiBub25lOyI+CiAgICA8ZGl2IGNsYXNzPSJldF9wYl9jb2x1bW4gZXRfcGJfY29sdW1uXzRfNCBldF9wYl9jb2x1bW5fNSBldF9wYl9jc3NfbWl4X2JsZW5kX21vZGVfcGFzc3Rocm91Z2ggZXQtbGFzdC1jaGlsZCI+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzAgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8aDQgY2xhc3M9ImV0X3BiX21vZHVsZV9oZWFkZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8c3BhbiBzdHlsZT0iZm9udC1zaXplOiAyMHB4ICFpbXBvcnRhbnQ7bGluZS1oZWlnaHQ6IDEgIWltcG9ydGFudDtmb250LXdlaWdodDogNjAwICFpbXBvcnRhbnQiPkx1cmVzPC9zcGFuPgogICAgICAgICAgICAgICAgICAgIDwvaDQ+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8aDU+SUQ6IEVBQzAwMDU8L2g1PgogICAgICAgICAgICAgICAgICAgICAgICA8cD5EZWNlcHRpdmUgc3lzdGVtcyBhbmQgYXJ0aWZhY3RzIGludGVuZGVkIHRvIHNlcnZlIGFzIGRlY295cywgYnJlYWRjcnVtYnMsIG9yIGJhaXQgdG8gZWxpY2l0IGEgc3BlY2lmaWMgcmVzcG9uc2UgZnJvbSB0aGUgYWR2ZXJzYXJ5LjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBsdXJlcy1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+THVyZXMgYXJlIGludGVuZGVkIHRvIGVsaWNpdCBhIHBhcnRpY3VsYXIgcmVzcG9uc2UgZnJvbSB0aGUgYWR2ZXJzYXJ5LiBGb3IgZXhhbXBsZSwgdGhlIGRlZmVuZGVyIG1heSB1dGlsaXplIEx1cmVzIHRvIGVuYWJsZSBvciBibG9jayB0aGUgYWR2ZXJzYXJ54oCZcyBpbnRlbmRlZCBhY3Rpb25zIG9yIGVuY291cmFnZSBvciBkaXNjb3VyYWdlIGEgc3BlY2lmaWMgYWN0aW9uIG9yIHJlc3BvbnNlLiBMdXJlcyBjYW4gdGFrZSBhIHZhcmlldHkgb2YgZm9ybXMgaW5jbHVkaW5nIGNyZWRlbnRpYWxzLCBhY2NvdW50cywgZmlsZXMvZGlyZWN0b3JpZXMsIGJyb3dzZXIgZXh0ZW5zaW9ucy9ib29rbWFya3MsIHN5c3RlbSBwcm9jZXNzZXMsIGV0Yy4gUmVnYXJkbGVzcyBvZiBmb3JtLCBMdXJlcyBwcm92aWRlIG9wcG9ydHVuaXRpZXMgdG8gdGhlIGRlZmVuZGVyIHRvIGRyaXZlIGFkdmVyc2FyeSBiZWhhdmlvciBpbiB3YXlzIHRoYXQgYWxpZ24gd2l0aCBvcGVyYXRpb25hbCBvdXRjb21lcy48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIGx1cmVzLXJlZmVyZW5jZXMgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0dGFibGUgdGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgUmVmZXJlbmNlIExpbmtzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2RvaS5vcmcvMTAuMTE0NS8zNDc4OTA1LjM0Nzg5MzAiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5Db21wYXJpc29uIE9mIERlZmVuc2UgRWZmZWN0aXZlbmVzcyBCZXR3ZWVuIE1vdmluZyBUYXJnZXQgRGVmZW5zZSBBbmQgQ3liZXIgRGVjZXB0aW9uIERlZmVuc2U8L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vZG9pLm9yZy8xMC4xMTQ1LzMzMzg0NjguMzM1NjgyNiIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPkEgU2NhbGFibGUgSGlnaCBGaWRlbGl0eSBEZWNveSBGcmFtZXdvcmsgQWdhaW5zdCBTb3BoaXN0aWNhdGVkIEN5YmVyIEF0dGFja3M8L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHA6Ly93d3cuY3MuY29sdW1iaWEuZWR1L35ibWJvd2VuL3BhcGVycy9EZWNveURvY3VtZW50c0NhbWVyYVJlYWR5U0VDQ09NMDkucGRmIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+QmFpdGluZyBJbnNpZGUgQXR0YWNrZXJzIFVzaW5nIERlY295IERvY3VtZW50czwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cHM6Ly9kbC5hY20ub3JnL2RvaS9hYnMvMTAuMTE0NS8zMzM4NDY4LjMzNTY4MjYiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5BIFNjYWxhYmxlIEhpZ2ggRmlkZWxpdHkgRGVjb3kgRnJhbWV3b3JrIEFnYWluc3QgU29waGlzdGljYXRlZCBDeWJlciBBdHRhY2tzPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2RsLmFjbS5vcmcvZG9pL2Ficy8xMC4xMTQ1LzMxMjk3OTAuMzEyOTgwNSIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPkNhdGVnb3JpemF0aW9uIE9mIEN5YmVyIFNlY3VyaXR5IERlY2VwdGlvbiBFdmVudHMgRm9yIE1lYXN1cmluZyBUaGUgU2V2ZXJpdHkgTGV2ZWwgT2YgQWR2YW5jZWQgVGFyZ2V0ZWQgQnJlYWNoZXM8L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHA6Ly93d3cucGVvcGxlLnZjdS5lZHUvfm1tYW5pYy9wYXBlcnMvMjAxNC9USUkxNF9Wb2xNYW5pY19DUFNTZWN1cml0eVZpcnR1YWxIb3N0LnBkZiIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPkN5YmVyLVBoeXNpY2FsIFN5c3RlbSBTZWN1cml0eSBXaXRoIERlY2VwdGl2ZSBWaXJ0dWFsIEhvc3RzIEZvciBJbmR1c3RyaWFsIENvbnRyb2wgTmV0d29ya3M8L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vc2Nob2xhcnNwYWNlLm1hbm9hLmhhd2FpaS5lZHUvaGFuZGxlLzEwMTI1LzQxODk3IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+QXV0b21hdGluZyBUaGUgR2VuZXJhdGlvbiBPZiBFbnRpY2luZyBUZXh0IENvbnRlbnQgRm9yIEhpZ2gtSW50ZXJhY3Rpb24gSG9uZXlmaWxlczwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cHM6Ly9mYWN1bHR5Lm5wcy5lZHUvZGVkZW5uaW4vcHVibGljYXRpb25zL2hvbmV5ZmlsZXMucGRmIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+SG9uZXlmaWxlczogRGVjZXB0aXZlIEZpbGVzIEZvciBJbnRydXNpb24gRGV0ZWN0aW9uPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL3d3dy5hY2FkZW1pYS5lZHUvNDk1MTkyNzUvREVDRVBUSVZFX0RFQ09ZU19DT01CSU5JTkdfQkVMSUVWQUJMRV9VU0VSX0FORF9ORVRXT1JLX0FDVElWSVRJRVNfQU5EX0RFQ0VQVElWRV9ORVRXT1JLX1NFVFVQX0lOX0VOSEFOQ0lOR19FRkZFQ1RJVkVORVNTP2Zyb209Y292ZXJfcGFnZSIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPkRlY2VwdGl2ZSBEZWNveXM6IENvbWJpbmluZyBCZWxpZXZhYmxlIFVzZXIgYW5kIE5ldHdvcmsgQWN0aXZpdGllcyBhbmQgRGVjZXB0aXZlIE5ldHdvcmsgU2V0dXAgaW4gRW5oYW5jaW5nIEVmZmVjdGl2ZW5lc3M8L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vd3d3Lm55dGltZXMuY29tLzIwMTcvMDUvMDkvd29ybGQvZXVyb3BlL2hhY2tlcnMtY2FtZS1idXQtdGhlLWZyZW5jaC13ZXJlLXByZXBhcmVkLmh0bWwiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5IYWNrZXJzIENhbWUgYnV0IHRoZSBGcmVuY2ggV2VyZSBQcmVwYXJlZDwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMiBsdXJlcy1hdHRhY2stbWFwcGluZ3MgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+RW50ZXJwcmlzZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDkiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMTEiPkNvbW1hbmQgYW5kIENvbnRyb2w8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDYiPkNyZWRlbnRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA1Ij5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDciPkRpc2NvdmVyeTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMiI+RXhlY3V0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQwIj5JbXBhY3Q8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDEiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA4Ij5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAzIj5QZXJzaXN0ZW5jZTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNCI+UHJpdmlsZWdlIEVzY2FsYXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwNDMiPlJlY29ubmFpc3NhbmNlPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIHRoZSBlbnZpcm9ubWVudCBvciBwZXJzb25hcywgdGhleSBhcmUgdnVsbmVyYWJsZSB3aGVuIHRoZXkgY29sbGVjdCwgb2JzZXJ2ZSwgb3IgbWFuaXB1bGF0ZSBzeXN0ZW0gYXJ0aWZhY3RzIG9yIGluZm9ybWF0aW9uLiBNYW5pcHVsYXRlZCBkYXRhIG1heSBjYXVzZSB0aGVtIHRvIHJldmVhbCBiZWhhdmlvcnMsIHVzZSBhZGRpdGlvbmFsIG9yIG1vcmUgYWR2YW5jZWQgY2FwYWJpbGl0aWVzIGFnYWluc3QgdGhlIHRhcmdldCwgYW5kL29yIGltcGFjdCB0aGVpciBkd2VsbCB0aW1lLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDEiPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBleHBsb2l0IGEgdHJ1c3RlZCByZWxhdGlvbnNoaXAsIHN1Y2ggYXMgdXNpbmcgYW4gYWNjb3VudCB0byBhY2Nlc3Mgb3IgbW92ZSBpbiB0aGUgZW52aXJvbm1lbnQsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdHJpZ2dlcmluZyB0cmlwd2lyZXMgb3IgZW5nYWdpbmcgaW4gYW5vbWFsb3VzIGJlaGF2aW9yLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDkiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMTEiPkNvbW1hbmQgYW5kIENvbnRyb2w8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDYiPkNyZWRlbnRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA1Ij5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDciPkRpc2NvdmVyeTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MCI+SW1wYWN0PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOCI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDQiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQzIj5SZWNvbm5haXNzYW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBlbmdhZ2VtZW50IGVudmlyb25tZW50cyBhbmQgcGVyc29uYXMsIHRoZWlyIGZ1dHVyZSBjYXBhYmlsaXR5LCB0YXJnZXRpbmcsIGFuZC9vciBpbmZyYXN0cnVjdHVyZSByZXF1aXJlbWVudHMgYXJlIHZ1bG5lcmFibGUgdG8gaW5mbHVlbmNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDEiPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBtYWludGFpbiBkcml2ZS1ieSBzaXRlcywgdGhleSBwcm92aWRlIGEgcGF0aHdheSBmb3IgYmVnaW5uaW5nIGVuZ2FnZW1lbnRzIGFuZCBtYXkgYmUgdW5hYmxlIHRvIGRpZmZlcmVudGlhdGUgcmVhbCBmcm9tIGRlY2VwdGl2ZSB2aWN0aW1zLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDEiPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBtYWludGFpbiBkcml2ZS1ieSBzaXRlcyBhbmQgY29sbGVjdCBpbmZvcm1hdGlvbiBhYm91dCBwb3RlbnRpYWwgdmljdGltcywgdGhleSBtYXkgcmV2ZWFsIGluZm9ybWF0aW9uIGFib3V0IHRoZWlyIHRhcmdldGluZyBwcmVmZXJlbmNlcyBieSBzZWxlY3Rpbmcgb3IgcmVqZWN0aW5nIGFuIGFyYml0cmFyeSB2aWN0aW0uPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNyI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQwIj5JbXBhY3Q8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDEiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAzIj5QZXJzaXN0ZW5jZTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MyI+UmVjb25uYWlzc2FuY2U8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggbmV0d29yayBvciBzeXN0ZW0gcmVzb3VyY2VzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRyaWdnZXJpbmcgdHJpcHdpcmVzIG9yIGVuZ2FnaW5nIGluIGVhc2lseSBkZXRlY3RhYmxlLCBhbm9tYWxvdXMgYmVoYXZpb3IuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNiI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDUiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNyI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAyIj5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDEiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA4Ij5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAzIj5QZXJzaXN0ZW5jZTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNCI+UHJpdmlsZWdlIEVzY2FsYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHVzZSBwcmV2aW91c2x5IHN0b2xlbiBpbmZvcm1hdGlvbiB0byBhY2Nlc3Mgb3IgbW92ZSBsYXRlcmFsbHkgd2l0aGluIGFuIGVudmlyb25tZW50LCB0aGV5IG1heSByZXZlYWwgcHJldmlvdXMgY29sbGVjdGlvbiBhY3Rpdml0aWVzLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDYiPkNyZWRlbnRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA1Ij5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDMiPlBlcnNpc3RlbmNlPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyByZWx5IG9uIHNwZWNpZmljIHJlc291cmNlcyB0byBiZSBlbmFibGVkLCBhY2Nlc3NpYmxlLCBhbmQvb3IgdnVsbmVyYWJsZSwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB0aGVpciBvcGVyYXRpb25zIGJlaW5nIGRpc3J1cHRlZCBpZiB0aGUgcmVzb3VyY2VzIGFyZSBkaXNhYmxlZCwgcmVtb3ZlZCwgb3Igb3RoZXJ3aXNlIG1hZGUgaW52dWxuZXJhYmxlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDEiPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBleHBsb2l0IGEgdHJ1c3RlZCByZWxhdGlvbnNoaXAsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gY29sbGVjdGluZyBhbmQgYWN0aW5nIG9uIG1hbmlwdWxhdGVkIGRhdGEgcHJvdmlkZWQgYnkgdGhlIHRydXN0ZWQgcGFydHkuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNiI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDUiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNyI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAyIj5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDEiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA4Ij5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAzIj5QZXJzaXN0ZW5jZTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNCI+UHJpdmlsZWdlIEVzY2FsYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGVuYWJsZWQsIGFjY2Vzc2libGUsIG9yIGludGVudGlvbmFsbHkgd2Vha2VuZWQvb3Zlcmx5IHBlcm1pc3NpdmUgcmVzb3VyY2VzIGluIHRoZSBlbnZpcm9ubWVudCAocHJvZHVjdGlvbiBvciBpc29sYXRlZCksIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gcmV2ZWFsaW5nIGFkZGl0aW9uYWwgb3IgbW9yZSBhZHZhbmNlZCBjYXBhYmlsaXRpZXMgd2hlbiBleHBsb2l0aW5nIG9yIHVzaW5nIHNhaWQgcmVzb3VyY2UuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAxMSI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZXhmaWx0cmF0ZSBkYXRhLCB0aGVpciBkYXRhIGFyZSB2dWxuZXJhYmxlIHRvIG9ic2VydmF0aW9uIG9yIG1hbmlwdWxhdGlvbiB2aWEgTWFuLWluLXRoZS1NaWRkbGUgYWN0aXZpdGllcy4gPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNiI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHVzZSBicnV0ZS1mb3JjZSB0ZWNobmlxdWVzIHRvIGFjY2VzcyBhY2NvdW50cyBvciBlbmNyeXB0ZWQgZGF0YSwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB3YXN0aW5nIHJlc291cmNlcyBpZiB0aGUgYXJ0aWZhY3QgaGFzIG5vIHZhbGlkIGNyZWRlbnRpYWxzIG9yIGlzIGxvY2tlZCBpbiBzb21lIG90aGVyIHdheS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgbWFpbnRhaW4gZHJpdmUtYnkgc2l0ZXMsIHRoZXkgcmV2ZWFsIGluZm9ybWF0aW9uIGFib3V0IHRoZWlyIHRhcmdldGluZyBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAxMSI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNiI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMTAiPkV4ZmlsdHJhdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgY29sbGVjdCBtYW5pcHVsYXRlZCBhcnRpZmFjdHMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gcmV2ZWFsaW5nIHRoZWlyIHByZXNlbmNlIHdoZW4gdXNpbmcgb3IgbW92aW5nIHRoZSBhcnRpZmFjdHMgZWxzZXdoZXJlIGluIHRoZSBlbmdhZ2VtZW50IGVudmlyb25tZW50LjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDkiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMTEiPkNvbW1hbmQgYW5kIENvbnRyb2w8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMTAiPkV4ZmlsdHJhdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgYXR0ZW1wdCB0byBleGZpbHRyYXRlLCBtYW5pcHVsYXRlLCBvciBtb3ZlIG1hc3NpdmUgZGF0YSBvYmplY3RzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHdhc3RpbmcgcmVzb3VyY2VzIHRvIGFjY29tcGxpc2ggdGhlIHRhc2suPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5Nb2JpbGU8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM1Ij5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMxIj5DcmVkZW50aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMCI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMyIj5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzQiPkltcGFjdDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMyI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAyOSI+UHJpdmlsZWdlIEVzY2FsYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggdGhlIGVudmlyb25tZW50IG9yIHBlcnNvbmFzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHdoZW4gdGhleSBjb2xsZWN0LCBvYnNlcnZlLCBvciBtYW5pcHVsYXRlIHN5c3RlbSBhcnRpZmFjdHMgb3IgaW5mb3JtYXRpb24uIE1hbmlwdWxhdGVkIGRhdGEgbWF5IGNhdXNlIHRoZW0gdG8gcmV2ZWFsIGJlaGF2aW9ycywgdXNlIGFkZGl0aW9uYWwgb3IgbW9yZSBhZHZhbmNlZCBjYXBhYmlsaXRpZXMgYWdhaW5zdCB0aGUgdGFyZ2V0LCBhbmQvb3IgaW1wYWN0IHRoZWlyIGR3ZWxsIHRpbWUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMSI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggdGhlIGVudmlyb25tZW50IG9yIHBlcnNvbmFzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIGNvbGxlY3RpbmcsIG9yIGluIHNvbWUgd2F5IGludGVyYWN0aW5nIHdpdGgsIG1hbmlwdWxhdGVkIG9yIGRlY295IGRhdGEuIEluIHRob3NlIGNhc2VzIHRoZSBkYXRhIG1heSBpbmNyZWFzZSB0aGVpciB0b2xlcmFuY2UgZm9yIGltcGVyZmVjdGlvbnMgaW4gdGhlIGVudmlyb25tZW50IGFuZCBpbXByb3ZlIHRoZSBvdmVyYWxsIGJlbGlldmFiaWxpdHkgb2YgdGhlIHJ1c2UuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMSI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzIiPkRpc2NvdmVyeTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBlbmdhZ2VtZW50IGVudmlyb25tZW50cyBhbmQgcGVyc29uYXMsIHRoZWlyIGZ1dHVyZSBjYXBhYmlsaXR5LCB0YXJnZXRpbmcsIGFuZC9vciBpbmZyYXN0cnVjdHVyZSByZXF1aXJlbWVudHMgYXJlIHZ1bG5lcmFibGUgdG8gaW5mbHVlbmNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMjciPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBtYWludGFpbiBkcml2ZS1ieSBzaXRlcywgdGhleSBwcm92aWRlIGEgcGF0aHdheSBmb3IgYmVnaW5uaW5nIGVuZ2FnZW1lbnRzIGFuZCBtYXkgYmUgdW5hYmxlIHRvIGRpZmZlcmVudGlhdGUgcmVhbCBmcm9tIGRlY2VwdGl2ZSB2aWN0aW1zLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMjciPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBtYWludGFpbiBkcml2ZS1ieSBzaXRlcyBhbmQgY29sbGVjdCBpbmZvcm1hdGlvbiBhYm91dCBwb3RlbnRpYWwgdmljdGltcywgdGhleSBtYXkgcmV2ZWFsIGluZm9ybWF0aW9uIGFib3V0IHRoZWlyIHRhcmdldGluZyBwcmVmZXJlbmNlcyBieSBzZWxlY3Rpbmcgb3IgcmVqZWN0aW5nIGFuIGFyYml0cmFyeSB2aWN0aW0uPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAyOCI+UGVyc2lzdGVuY2U8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggbmV0d29yayBvciBzeXN0ZW0gcmVzb3VyY2VzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRyaWdnZXJpbmcgdHJpcHdpcmVzIG9yIGVuZ2FnaW5nIGluIGVhc2lseSBkZXRlY3RhYmxlLCBhbm9tYWxvdXMgYmVoYXZpb3IuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMSI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHVzZSBwcmV2aW91c2x5IHN0b2xlbiBpbmZvcm1hdGlvbiB0byBhY2Nlc3Mgb3IgbW92ZSBsYXRlcmFsbHkgd2l0aGluIGFuIGVudmlyb25tZW50LCB0aGV5IG1heSByZXZlYWwgcHJldmlvdXMgY29sbGVjdGlvbiBhY3Rpdml0aWVzLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzUiPkNvbGxlY3Rpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHJlbHkgb24gc3BlY2lmaWMgcmVzb3VyY2VzIHRvIGJlIGVuYWJsZWQsIGFjY2Vzc2libGUsIGFuZC9vciB2dWxuZXJhYmxlLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRoZWlyIG9wZXJhdGlvbnMgYmVpbmcgZGlzcnVwdGVkIGlmIHRoZSByZXNvdXJjZXMgYXJlIGRpc2FibGVkLCByZW1vdmVkLCBvciBvdGhlcndpc2UgbWFkZSBpbnZ1bG5lcmFibGUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNyI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNCI+SW1wYWN0PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBleGZpbHRyYXRlIGRhdGEsIHRoZWlyIGRhdGEgYXJlIHZ1bG5lcmFibGUgdG8gb2JzZXJ2YXRpb24gb3IgbWFuaXB1bGF0aW9uIHZpYSBNYW4taW4tdGhlLU1pZGRsZSBhY3Rpdml0aWVzLiA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDI3Ij5Jbml0aWFsIEFjY2VzczwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgbWFpbnRhaW4gZHJpdmUtYnkgc2l0ZXMsIHRoZXkgcmV2ZWFsIGluZm9ybWF0aW9uIGFib3V0IHRoZWlyIHRhcmdldGluZyBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNyI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNiI+RXhmaWx0cmF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBjb2xsZWN0IG1hbmlwdWxhdGVkIGFydGlmYWN0cywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgcHJlc2VuY2Ugd2hlbiB1c2luZyBvciBtb3ZpbmcgdGhlIGFydGlmYWN0cyBlbHNld2hlcmUgaW4gdGhlIGVuZ2FnZW1lbnQgZW52aXJvbm1lbnQuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNyI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNiI+RXhmaWx0cmF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBhdHRlbXB0IHRvIGV4ZmlsdHJhdGUsIG1hbmlwdWxhdGUsIG9yIG1vdmUgbWFzc2l2ZSBkYXRhIG9iamVjdHMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gd2FzdGluZyByZXNvdXJjZXMgdG8gYWNjb21wbGlzaCB0aGUgdGFzay48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPklDUzwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDAiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDIiPkRpc2NvdmVyeTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMyI+RXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNSI+SW1wYWN0PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA4Ij5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwOSI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDExMSI+UHJpdmlsZWdlIEVzY2FsYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggdGhlIGVudmlyb25tZW50IG9yIHBlcnNvbmFzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHdoZW4gdGhleSBjb2xsZWN0LCBvYnNlcnZlLCBvciBtYW5pcHVsYXRlIHN5c3RlbSBhcnRpZmFjdHMgb3IgaW5mb3JtYXRpb24uIE1hbmlwdWxhdGVkIGRhdGEgbWF5IGNhdXNlIHRoZW0gdG8gcmV2ZWFsIGJlaGF2aW9ycywgdXNlIGFkZGl0aW9uYWwgb3IgbW9yZSBhZHZhbmNlZCBjYXBhYmlsaXRpZXMgYWdhaW5zdCB0aGUgdGFyZ2V0LCBhbmQvb3IgaW1wYWN0IHRoZWlyIGR3ZWxsIHRpbWUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMCI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMiI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA1Ij5JbXBhY3Q8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDYiPkltcGFpciBQcm9jZXNzIENvbnRyb2w8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDciPkluaGliaXQgUmVzcG9uc2UgRnVuY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDgiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA5Ij5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTEwIj5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBlbmdhZ2VtZW50IGVudmlyb25tZW50cyBhbmQgcGVyc29uYXMsIHRoZWlyIGZ1dHVyZSBjYXBhYmlsaXR5LCB0YXJnZXRpbmcsIGFuZC9vciBpbmZyYXN0cnVjdHVyZSByZXF1aXJlbWVudHMgYXJlIHZ1bG5lcmFibGUgdG8gaW5mbHVlbmNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDgiPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBtYWludGFpbiBkcml2ZS1ieSBzaXRlcywgdGhleSBwcm92aWRlIGEgcGF0aHdheSBmb3IgYmVnaW5uaW5nIGVuZ2FnZW1lbnRzIGFuZCBtYXkgYmUgdW5hYmxlIHRvIGRpZmZlcmVudGlhdGUgcmVhbCBmcm9tIGRlY2VwdGl2ZSB2aWN0aW1zLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDgiPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBtYWludGFpbiBkcml2ZS1ieSBzaXRlcyBhbmQgY29sbGVjdCBpbmZvcm1hdGlvbiBhYm91dCBwb3RlbnRpYWwgdmljdGltcywgdGhleSBtYXkgcmV2ZWFsIGluZm9ybWF0aW9uIGFib3V0IHRoZWlyIHRhcmdldGluZyBwcmVmZXJlbmNlcyBieSBzZWxlY3Rpbmcgb3IgcmVqZWN0aW5nIGFuIGFyYml0cmFyeSB2aWN0aW0uPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMCI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMiI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAzIj5FdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA0Ij5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDYiPkltcGFpciBQcm9jZXNzIENvbnRyb2w8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDciPkluaGliaXQgUmVzcG9uc2UgRnVuY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDgiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTEwIj5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBuZXR3b3JrIG9yIHN5c3RlbSByZXNvdXJjZXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdHJpZ2dlcmluZyB0cmlwd2lyZXMgb3IgZW5nYWdpbmcgaW4gZWFzaWx5IGRldGVjdGFibGUsIGFub21hbG91cyBiZWhhdmlvci48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA4Ij5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwOSI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDExMCI+UGVyc2lzdGVuY2U8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHVzZSBwcmV2aW91c2x5IHN0b2xlbiBpbmZvcm1hdGlvbiB0byBhY2Nlc3Mgb3IgbW92ZSBsYXRlcmFsbHkgd2l0aGluIGFuIGVudmlyb25tZW50LCB0aGV5IG1heSByZXZlYWwgcHJldmlvdXMgY29sbGVjdGlvbiBhY3Rpdml0aWVzLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDgiPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyB1c2UgaGFyZHdhcmUgcGVyaXBoZXJhbHMsIHJlbW92YWJsZSBtZWRpYSwgb3IgY29ubmVjdGVkIHRyYW5zaWVudCBjeWJlciBhc3NldHMsIHRoZXkgbXVzdCByZWx5IG9uIHBoeXNpY2FsIGFjY2VzcyBvciBoYXZlIGxpbWl0ZWQgY29udHJvbCBvdmVyIHdoZW4gYW5kIHdoZXJlIGhhcmR3YXJlIGFkZGl0aW9ucyBhcmUgY29ubmVjdGVkIGluIHRoZSB0YXJnZXQgbmV0d29yay48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA4Ij5Jbml0aWFsIEFjY2VzczwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgcmVseSBvbiBzcGVjaWZpYyByZXNvdXJjZXMgdG8gYmUgZW5hYmxlZCwgYWNjZXNzaWJsZSwgYW5kL29yIHZ1bG5lcmFibGUsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdGhlaXIgb3BlcmF0aW9ucyBiZWluZyBkaXNydXB0ZWQgaWYgdGhlIHJlc291cmNlcyBhcmUgZGlzYWJsZWQsIHJlbW92ZWQsIG9yIG90aGVyd2lzZSBtYWRlIGludnVsbmVyYWJsZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAwIj5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAyIj5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDMiPkV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDciPkluaGliaXQgUmVzcG9uc2UgRnVuY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDgiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA5Ij5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTEwIj5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZGlzY292ZXIgZW5hYmxlZCwgYWNjZXNzaWJsZSwgb3IgaW50ZW50aW9uYWxseSB3ZWFrZW5lZC9vdmVybHkgcGVybWlzc2l2ZSByZXNvdXJjZXMgaW4gdGhlIGVudmlyb25tZW50IChwcm9kdWN0aW9uIG9yIGlzb2xhdGVkKSwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgYWRkaXRpb25hbCBvciBtb3JlIGFkdmFuY2VkIGNhcGFiaWxpdGllcyB3aGVuIGV4cGxvaXRpbmcgb3IgdXNpbmcgc2FpZCByZXNvdXJjZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAwIj5Db2xsZWN0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBhIGRpdmVyc2Ugc2V0IG9mIGFjY2Vzc2libGUgcmVzb3VyY2VzIGFuZCBkZWNveSBhcnRpZmFjdHMgb24gdGhlIHRhcmdldCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzIGFuZCBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMCI+Q29sbGVjdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgY29sbGVjdCB0YXJnZXRpbmcgaW5mb3JtYXRpb24gZnJvbSBvcGVuIG9yIGNsb3NlZCBkYXRhIHNvdXJjZXMsIHRoZXkgbWF5IHJldmVhbCB0aGVpciB0YXJnZXRpbmcgcHJlZmVyZW5jZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwOCI+SW5pdGlhbCBBY2Nlc3M8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIG1haW50YWluIGRyaXZlLWJ5IHNpdGVzLCB0aGV5IHJldmVhbCBpbmZvcm1hdGlvbiBhYm91dCB0aGVpciB0YXJnZXRpbmcgY2FwYWJpbGl0aWVzLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMTAiPlBlcnNpc3RlbmNlPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllc+KAmSBtYWx3YXJlIGlzIGRldG9uYXRlZCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBkeW5hbWljIGFuYWx5c2lzLCB3aGljaCBjYW4gcmV2ZWFsIGhvdyB0aGUgbWFsd2FyZSBpbnRlcmFjdHMgd2l0aCBzeXN0ZW0gcmVzb3VyY2VzLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDAiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDUiPkltcGFjdDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgY29sbGVjdCBtYW5pcHVsYXRlZCBhcnRpZmFjdHMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gcmV2ZWFsaW5nIHRoZWlyIHByZXNlbmNlIHdoZW4gdXNpbmcgb3IgbW92aW5nIHRoZSBhcnRpZmFjdHMgZWxzZXdoZXJlIGluIHRoZSBlbmdhZ2VtZW50IGVudmlyb25tZW50LjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDAiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDUiPkltcGFjdDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgYXR0ZW1wdCB0byBleGZpbHRyYXRlLCBtYW5pcHVsYXRlLCBvciBtb3ZlIG1hc3NpdmUgZGF0YSBvYmplY3RzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHdhc3RpbmcgcmVzb3VyY2VzIHRvIGFjY29tcGxpc2ggdGhlIHRhc2suPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMCI+Q29sbGVjdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZGlzY292ZXIgaW5hY2Nlc3NpYmxlIChidXQgcG9zc2libHkgdmFsdWFibGUpIGRhdGEgb3IgZGF0YSBzdHJlYW1zLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHdhc3RpbmcgcmVzb3VyY2VzIG9yIHJldmVhbGluZyBhZGRpdGlvbmFsIGNhcGFiaWxpdGllcyBpbiBhbiBlZmZvcnQgdG8gYWNjZXNzIHRoZSBjb250ZW50LjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgIDwvZGl2Pgo8L2Rpdj4KPGRpdiBjbGFzcz0iZXRfcGJfcm93IGV0X3BiX3Jvd18yIGFwcGxpY2F0aW9uLWRpdmVyc2l0eS1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+QXBwbGljYXRpb24gRGl2ZXJzaXR5PC9zcGFuPgogICAgICAgICAgICAgICAgICAgIDwvaDQ+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8aDU+SUQ6IEVBQzAwMDY8L2g1PgogICAgICAgICAgICAgICAgICAgICAgICA8cD5QcmVzZW50IHRoZSBhZHZlcnNhcnkgd2l0aCBhIHZhcmlldHkgb2YgaW5zdGFsbGVkIGFwcGxpY2F0aW9ucyBhbmQgc2VydmljZXMuPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIGFwcGxpY2F0aW9uLWRpdmVyc2l0eS1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+QXBwbGljYXRpb24gRGl2ZXJzaXR5IHByZXNlbnRzIGFuIGFycmF5IG9mIHNvZnR3YXJlIHRhcmdldHMgdG8gdGhlIGFkdmVyc2FyeS4gT24gYSBzaW5nbGUgdGFyZ2V0IHN5c3RlbSwgZGVmZW5kZXJzIGNhbiBjb25maWd1cmUgbXVsdGlwbGUgc2VydmljZXMgb3Igc29mdHdhcmUgYXBwbGljYXRpb25zLiBUaGlzIGRpdmVyc2l0eSBtYXkgaW5jbHVkZSBub3Qgb25seSBhIHZhcmlldHkgb2YgZGlmZmVyZW50IHR5cGVzIG9mIGFwcGxpY2F0aW9ucywgYnV0IGFsc28gdmFyaW91cyB2ZXJzaW9ucyBvZiB0aGUgc2FtZSBhcHBsaWNhdGlvbi4gQXBwbGljYXRpb24gRGl2ZXJzaXR5IGNhbiBiZSB1c2VkIHRvIGVuY291cmFnZSBlbmdhZ2VtZW50IGJ5IG9mZmVyaW5nIGEgYnJvYWQgYXR0YWNrIHN1cmZhY2UuIEJ5IG1vbml0b3JpbmcgYWR2ZXJzYXJ5IGFjdGl2aXR5IGluIGEgZGl2ZXJzZSBlbnZpcm9ubWVudCwgdGhlIGRlZmVuZGVyIGNhbiBnYWluIGluZm9ybWF0aW9uIG9uIHRoZSBhZHZlcnNhcnnigJlzIGNhcGFiaWxpdGllcyBhbmQgdGFyZ2V0aW5nIHByZWZlcmVuY2VzLiBGb3IgZXhhbXBsZSwgYSBkZWZlbmRlciBjYW4gaW5zdGFsbCBvbmUgb3IgbW9yZSBhcHBsaWNhdGlvbnMgd2l0aCBhIHZhcmlldHkgb2YgcGF0Y2ggbGV2ZWxzIHRvIHNlZSBob3cgdGhlIGFkdmVyc2FyeeKAmXMgcmVzcG9uc2UgZGlmZmVycyBhY3Jvc3MgdmVyc2lvbnMuICBBZGRpdGlvbmFsbHksIGEgZGl2ZXJzZSBzZXQgb2YgYXBwbGljYXRpb25zIHByb3ZpZGVzIGEgdmFyaWV0eSBvZiBhdmVudWVzIGZvciB0aGUgZGVmZW5kZXIgdG8gcHJlc2VudCBhZGRpdGlvbmFsIGluZm9ybWF0aW9uIHRocm91Z2hvdXQgYW4gb3BlcmF0aW9uLiBUaGlzIGluZm9ybWF0aW9uIGNhbiBiZSB1c2VkIHRvIGludHJvZHVjZSBhZGRpdGlvbmFsIGF0dGFjayBzdXJmYWNlcywgbW90aXZhdGUgb3IgZGVtb3RpdmF0ZSB0aGUgYWR2ZXJzYXJ5LCBvciBmdXJ0aGVyIHRoZSBlbmdhZ2VtZW50IG5hcnJhdGl2ZS4gRm9yIGV4YW1wbGUsIGlmIHRoZSBhZHZlcnNhcnkgaXMgY2xvc2UgdG8gdW5jb3ZlcmluZyBzb21ldGhpbmcgdGhhdCBtaWdodCByYWlzZSBzdXNwaWNpb24gYXJvdW5kIGEgdGFyZ2V0LCB0aGUgZGVmZW5kZXIgY2FuIGFkZCBhbiBldmVudCB0byBhIHNoYXJlZCBjYWxlbmRhciBhcHBsaWNhdGlvbiBvciBhIG1lc3NhZ2UgaW4gYSBub3RlcyBhcHBsaWNhdGlvbiB0aGF0IHRoZSBzeXN0ZW0gd2lsbCBiZSBvZmZsaW5lIGZvciBzY2hlZHVsZWQgbWFpbnRlbmFuY2UuIEhhdmluZyBhIHZhcmlldHkgb2YgYXBwbGljYXRpb25zIG9uIHRoZSBzeXN0ZW0gcHJvdmlkZXMgdGhlIGRlZmVuZGVyIHdpdGggbXVsdGlwbGUgZW5nYWdlbWVudCBhdmVudWVzIHRvIGhhbmRsZSB3aGF0ZXZlciBldmVudHMgaGFwcGVuIGR1cmluZyB0aGUgb3BlcmF0aW9uLiBGaW5hbGx5LCBkaXZlcnNpdHkgY2FuIGluY3JlYXNlIHRoZSBhZHZlcnNhcnnigJlzIG92ZXJhbGwgY29tZm9ydCBsZXZlbCBieSBhZGRpbmcgdG8gdGhlIGJlbGlldmFiaWxpdHkgb2YgdGhlIGVudmlyb25tZW50LiA8L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIGFwcGxpY2F0aW9uLWRpdmVyc2l0eS1yZWZlcmVuY2VzIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idHRhYmxlIHRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIFJlZmVyZW5jZSBMaW5rcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cHM6Ly9kbC5hY20ub3JnL2RvaS9hYnMvMTAuMTE0NS8yOTkzNDEyLjI5OTM0MTciIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5BbiBJbnRlcmZhY2UgRGl2ZXJzaWZpZWQgSG9uZXlwb3QgRm9yIE1hbHdhcmUgQW5hbHlzaXM8L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vY29yZS5hYy51ay9kb3dubG9hZC9wZGYvMzY3Mjg5NDgucGRmIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+RGVmZW5kaW5nIEN5YmVyc3BhY2UgV2l0aCBGYWtlIEhvbmV5cG90czwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cHM6Ly9pZWVleHBsb3JlLmllZWUub3JnL2Fic3RyYWN0L2RvY3VtZW50LzkzNDgxMjIiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5Tb2Z0d2FyZSBEaXZlcnNpdHkgRm9yIEN5YmVyIERlY2VwdGlvbjwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cHM6Ly9pZWVleHBsb3JlLmllZWUub3JnL2llbDcvOTMyMjA1NS85MzIxOTczLzA5MzQ4MTIyLnBkZiIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPlNvZnR3YXJlIERpdmVyc2l0eSBGb3IgQ3liZXIgRGVjZXB0aW9uPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIGFwcGxpY2F0aW9uLWRpdmVyc2l0eS1hdHRhY2stbWFwcGluZ3MgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+RW50ZXJwcmlzZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDkiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMTEiPkNvbW1hbmQgYW5kIENvbnRyb2w8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDYiPkNyZWRlbnRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA1Ij5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDciPkRpc2NvdmVyeTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMiI+RXhlY3V0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQwIj5JbXBhY3Q8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDEiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA4Ij5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAzIj5QZXJzaXN0ZW5jZTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNCI+UHJpdmlsZWdlIEVzY2FsYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGEgZGl2ZXJzZSBzZXQgb2YgYWNjZXNzaWJsZSByZXNvdXJjZXMgYW5kIGRlY295IGFydGlmYWN0cyBvbiB0aGUgdGFyZ2V0LCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHJldmVhbGluZyB0aGVpciB0YXJnZXRpbmcgcHJlZmVyZW5jZXMgYW5kIGNhcGFiaWxpdGllcy48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPk1vYmlsZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzEiPkNyZWRlbnRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDI4Ij5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgcmVseSBvbiBzcGVjaWZpYyByZXNvdXJjZXMgdG8gYmUgZW5hYmxlZCwgYWNjZXNzaWJsZSwgYW5kL29yIHZ1bG5lcmFibGUsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdGhlaXIgb3BlcmF0aW9ucyBiZWluZyBkaXNydXB0ZWQgaWYgdGhlIHJlc291cmNlcyBhcmUgZGlzYWJsZWQsIHJlbW92ZWQsIG9yIG90aGVyd2lzZSBtYWRlIGludnVsbmVyYWJsZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM1Ij5Db2xsZWN0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBlbmFibGVkLCBhY2Nlc3NpYmxlLCBvciBpbnRlbnRpb25hbGx5IHdlYWtlbmVkL292ZXJseSBwZXJtaXNzaXZlIHJlc291cmNlcyBpbiB0aGUgZW52aXJvbm1lbnQgKHByb2R1Y3Rpb24gb3IgaXNvbGF0ZWQpLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHJldmVhbGluZyBhZGRpdGlvbmFsIG9yIG1vcmUgYWR2YW5jZWQgY2FwYWJpbGl0aWVzIHdoZW4gZXhwbG9pdGluZyBvciB1c2luZyBzYWlkIHJlc291cmNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzUiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzEiPkNyZWRlbnRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMwIj5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzIiPkRpc2NvdmVyeTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNCI+SW1wYWN0PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMzIj5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDI4Ij5QZXJzaXN0ZW5jZTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAyOSI+UHJpdmlsZWdlIEVzY2FsYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGEgZGl2ZXJzZSBzZXQgb2YgYWNjZXNzaWJsZSByZXNvdXJjZXMgYW5kIGRlY295IGFydGlmYWN0cyBvbiB0aGUgdGFyZ2V0LCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHJldmVhbGluZyB0aGVpciB0YXJnZXRpbmcgcHJlZmVyZW5jZXMgYW5kIGNhcGFiaWxpdGllcy48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPklDUzwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDgiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA5Ij5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTExIj5Qcml2aWxlZ2UgRXNjYWxhdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZGlzY292ZXIgYSBkaXZlcnNlIHNldCBvZiBhY2Nlc3NpYmxlIHJlc291cmNlcyBhbmQgZGVjb3kgYXJ0aWZhY3RzIG9uIHRoZSB0YXJnZXQsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gcmV2ZWFsaW5nIHRoZWlyIHRhcmdldGluZyBwcmVmZXJlbmNlcyBhbmQgY2FwYWJpbGl0aWVzLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgIDwvZGl2Pgo8L2Rpdj4KPGRpdiBjbGFzcz0iZXRfcGJfcm93IGV0X3BiX3Jvd18yIG5ldHdvcmstZGl2ZXJzaXR5LWRldGFpbCBtYXRyaXgtZGV0YWlscyBldF9wYl9ndXR0ZXJzMSBldF9oYWRfYW5pbWF0aW9uIiBzdHlsZT0iZGlzcGxheTogbm9uZTsiPgogICAgPGRpdiBjbGFzcz0iZXRfcGJfY29sdW1uIGV0X3BiX2NvbHVtbl80XzQgZXRfcGJfY29sdW1uXzUgZXRfcGJfY3NzX21peF9ibGVuZF9tb2RlX3Bhc3N0aHJvdWdoIGV0LWxhc3QtY2hpbGQiPgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8wIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGg0IGNsYXNzPSJldF9wYl9tb2R1bGVfaGVhZGVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4gc3R5bGU9ImZvbnQtc2l6ZTogMjBweCAhaW1wb3J0YW50O2xpbmUtaGVpZ2h0OiAxICFpbXBvcnRhbnQ7Zm9udC13ZWlnaHQ6IDYwMCAhaW1wb3J0YW50Ij5OZXR3b3JrIERpdmVyc2l0eTwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBFQUMwMDA3PC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+VXNlIGEgZGl2ZXJzZSBzZXQgb2YgZGV2aWNlcyBvbiB0aGUgbmV0d29yayB0byBoZWxwIGVzdGFibGlzaCB0aGUgbGVnaXRpbWFjeSBvZiBhIGRlY2VwdGl2ZSBuZXR3b3JrLjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBuZXR3b3JrLWRpdmVyc2l0eS1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+TmV0d29yayBEaXZlcnNpdHkgaW52b2x2ZXMgdGhlIHVzZSBvZiBhbiBhc3NvcnRlZCBjb2xsZWN0aW9uIG9mIG5ldHdvcmsgcmVzb3VyY2VzIHN1Y2ggYXMgbmV0d29ya2luZyBkZXZpY2VzLCBmaXJld2FsbHMsIHByaW50ZXJzLCBwaG9uZXMsIGV0Yy4gTmV0d29yayBEaXZlcnNpdHkgY2FuIGJlIHVzZWQgdG8gZW5jb3VyYWdlIGFkdmVyc2FyaWVzIHRvIGVuZ2FnZSBieSBvZmZlcmluZyBhIGJyb2FkIGF0dGFjayBzdXJmYWNlLiBBZGRpdGlvbmFsbHksIGRpdmVyc2l0eSBjYW4gaW5jcmVhc2UgdGhlIGFkdmVyc2FyeeKAmXMgb3ZlcmFsbCBjb21mb3J0IGxldmVsIGJ5IGFkZGluZyB0byB0aGUgYmVsaWV2YWJpbGl0eSBvZiB0aGUgZW52aXJvbm1lbnQuIEJ5IG1vbml0b3JpbmcgYWR2ZXJzYXJ5IGFjdGl2aXR5IGluIGEgZGl2ZXJzZSBlbnZpcm9ubWVudCwgdGhlIGRlZmVuZGVyIGNhbiBnYWluIGluZm9ybWF0aW9uIG9uIHRoZSBhZHZlcnNhcnnigJlzIGNhcGFiaWxpdGllcyBhbmQgdGFyZ2V0aW5nIHByZWZlcmVuY2VzLiBGb3IgZXhhbXBsZSwgYSBkZWZlbmRlciBjYW4gZGVwbG95IGEgdmFyaWV0eSBvZiBuZXR3b3JrIHJlc291cmNlcyB0byBpZGVudGlmeSB3aGljaCBkZXZpY2VzIGFyZSB0YXJnZXRlZCBieSB0aGUgYWR2ZXJzYXJ5LjwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgbmV0d29yay1kaXZlcnNpdHktcmVmZXJlbmNlcyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InR0YWJsZSB0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBSZWZlcmVuY2UgTGlua3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vY29yZS5hYy51ay9kb3dubG9hZC9wZGYvMzY3MjkwMDIucGRmIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+QSBUZWNobmlxdWUgRm9yIE5ldHdvcmsgVG9wb2xvZ3kgRGVjZXB0aW9uPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIG5ldHdvcmstZGl2ZXJzaXR5LWF0dGFjay1tYXBwaW5ncyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5FbnRlcnByaXNlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNiI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDciPkRpc2NvdmVyeTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MCI+SW1wYWN0PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwNDMiPlJlY29ubmFpc3NhbmNlPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBhIGRpdmVyc2Ugc2V0IG9mIGFjY2Vzc2libGUgcmVzb3VyY2VzIGFuZCBkZWNveSBhcnRpZmFjdHMgb24gdGhlIHRhcmdldCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzIGFuZCBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5Nb2JpbGU8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMwIj5EZWZlbnNlIEV2YXNpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggbmV0d29yayBvciBzeXN0ZW0gcmVzb3VyY2VzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRyaWdnZXJpbmcgdHJpcHdpcmVzIG9yIGVuZ2FnaW5nIGluIGVhc2lseSBkZXRlY3RhYmxlLCBhbm9tYWxvdXMgYmVoYXZpb3IuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNCI+SW1wYWN0PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBhIGRpdmVyc2Ugc2V0IG9mIGFjY2Vzc2libGUgcmVzb3VyY2VzIGFuZCBkZWNveSBhcnRpZmFjdHMgb24gdGhlIHRhcmdldCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzIGFuZCBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5JQ1M8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAwIj5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAyIj5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDgiPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBhIGRpdmVyc2Ugc2V0IG9mIGFjY2Vzc2libGUgcmVzb3VyY2VzIGFuZCBkZWNveSBhcnRpZmFjdHMgb24gdGhlIHRhcmdldCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzIGFuZCBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgYnVybi1pbi1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+QnVybi1Jbjwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBFQUMwMDA4PC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+RXhlcmNpc2UgYSB0YXJnZXQgc3lzdGVtIGluIGEgbWFubmVyIHdoZXJlIGl0IHdpbGwgZ2VuZXJhdGUgZGVzaXJhYmxlIHN5c3RlbSBhcnRpZmFjdHMuPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIGJ1cm4taW4tbG9uZy1kZXNjcmlwdGlvbiBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPkJ1cm4tSW4gaW52b2x2ZXMgZXhlcmNpc2luZyB0aGUgc3lzdGVtIHRvIGNyZWF0ZSBkZXNpcmFibGUgc3lzdGVtIGFydGlmYWN0cyBzdWNoIGFzIHdlYiBicm93c2luZyBoaXN0b3J5LCBmaWxlIHN5c3RlbSB1c2FnZSwgb3IgdGhlIHJ1bm5pbmcgb2YgdXNlciBhcHBsaWNhdGlvbnMuIEF0IHRpbWVzLCBCdXJuLUluIGNhbiBiZSBhY2NvbXBsaXNoZWQgYnkgc2ltcGx5IGxldHRpbmcgYSBzeXN0ZW0gb3IgYXBwbGljYXRpb24gcnVuIGZvciBhbiBleHRlbmRlZCBwZXJpb2Qgb2YgdGltZS4gT3RoZXIgdGltZXMsIHRoZSBkZWZlbmRlciBlbmdhZ2VzIHdpdGggdGhlIGVudmlyb25tZW50IHRvIHByb2R1Y2UgdGhlIEJ1cm4tSW4gYXJ0aWZhY3RzLCBzdWNoIGFzIHdoZW4gdGhlIGRlZmVuZGVyIGxvZ3MgaW50byBhIGRlY295IGFjY291bnQgb3IgYWNjZXNzZXMgYSBkZWNveSB3ZWJzaXRlIHRvIGdlbmVyYXRlIHNlc3Npb24gY29va2llcyBhbmQgYnJvd3NlciBoaXN0b3J5LiBUaGVzZSB0YXNrcyBjYW4gYmUgYWNjb21wbGlzaGVkIG1hbnVhbGx5IG9yIHZpYSBhdXRvbWF0ZWQgdG9vbGluZy4gIEJ1cm4tSW4gc2hvdWxkIG9jY3VyIHByZS1vcGVyYXRpb24gYW5kIGNvbnRpbnVlIGFzIGFwcHJvcHJpYXRlIGR1cmluZyB0aGUgb3BlcmF0aW9uLiBUaGUgYXJ0aWZhY3RzIGdlbmVyYXRlZCBkdXJpbmcgdGhlIEJ1cm4tSW4gcHJvY2VzcyBjYW4gcmVhc3N1cmUgdGhlIGFkdmVyc2FyeSBvZiB0aGUgZW52aXJvbm1lbnTigJlzIGxlZ2l0aW1hY3kgYnkgY3JlYXRpbmcgYW4gZW52aXJvbm1lbnQgdGhhdCBtb3JlIGNsb3NlbHkgcmVzZW1ibGVzIGEgcmVhbCwgbGl2ZWQgaW4sIHN5c3RlbSBvciBuZXR3b3JrLjwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgYnVybi1pbi1hdHRhY2stbWFwcGluZ3MgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+RW50ZXJwcmlzZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDkiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDUiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNyI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDQiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQzIj5SZWNvbm5haXNzYW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCB0aGUgZW52aXJvbm1lbnQgb3IgcGVyc29uYXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gY29sbGVjdGluZywgb3IgaW4gc29tZSB3YXkgaW50ZXJhY3Rpbmcgd2l0aCwgbWFuaXB1bGF0ZWQgb3IgZGVjb3kgZGF0YS4gSW4gdGhvc2UgY2FzZXMgdGhlIGRhdGEgbWF5IGluY3JlYXNlIHRoZWlyIHRvbGVyYW5jZSBmb3IgaW1wZXJmZWN0aW9ucyBpbiB0aGUgZW52aXJvbm1lbnQgYW5kIGltcHJvdmUgdGhlIG92ZXJhbGwgYmVsaWV2YWJpbGl0eSBvZiB0aGUgcnVzZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA5Ij5Db2xsZWN0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBhIGRpdmVyc2Ugc2V0IG9mIGFjY2Vzc2libGUgcmVzb3VyY2VzIGFuZCBkZWNveSBhcnRpZmFjdHMgb24gdGhlIHRhcmdldCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzIGFuZCBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5Nb2JpbGU8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM1Ij5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMyIj5EaXNjb3Zlcnk8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggdGhlIGVudmlyb25tZW50IG9yIHBlcnNvbmFzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIGNvbGxlY3RpbmcsIG9yIGluIHNvbWUgd2F5IGludGVyYWN0aW5nIHdpdGgsIG1hbmlwdWxhdGVkIG9yIGRlY295IGRhdGEuIEluIHRob3NlIGNhc2VzIHRoZSBkYXRhIG1heSBpbmNyZWFzZSB0aGVpciB0b2xlcmFuY2UgZm9yIGltcGVyZmVjdGlvbnMgaW4gdGhlIGVudmlyb25tZW50IGFuZCBpbXByb3ZlIHRoZSBvdmVyYWxsIGJlbGlldmFiaWxpdHkgb2YgdGhlIHJ1c2UuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMiI+RGlzY292ZXJ5PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIGVuZ2FnZW1lbnQgZW52aXJvbm1lbnRzIGFuZCBwZXJzb25hcywgdGhlaXIgZnV0dXJlIGNhcGFiaWxpdHksIHRhcmdldGluZywgYW5kL29yIGluZnJhc3RydWN0dXJlIHJlcXVpcmVtZW50cyBhcmUgdnVsbmVyYWJsZSB0byBpbmZsdWVuY2UuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5JQ1M8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAyIj5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDgiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA5Ij5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTEwIj5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCB0aGUgZW52aXJvbm1lbnQgb3IgcGVyc29uYXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gY29sbGVjdGluZywgb3IgaW4gc29tZSB3YXkgaW50ZXJhY3Rpbmcgd2l0aCwgbWFuaXB1bGF0ZWQgb3IgZGVjb3kgZGF0YS4gSW4gdGhvc2UgY2FzZXMgdGhlIGRhdGEgbWF5IGluY3JlYXNlIHRoZWlyIHRvbGVyYW5jZSBmb3IgaW1wZXJmZWN0aW9ucyBpbiB0aGUgZW52aXJvbm1lbnQgYW5kIGltcHJvdmUgdGhlIG92ZXJhbGwgYmVsaWV2YWJpbGl0eSBvZiB0aGUgcnVzZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICA8L2Rpdj4KPC9kaXY+CjxkaXYgY2xhc3M9ImV0X3BiX3JvdyBldF9wYl9yb3dfMiBlbWFpbC1tYW5pcHVsYXRpb24tZGV0YWlsIG1hdHJpeC1kZXRhaWxzIGV0X3BiX2d1dHRlcnMxIGV0X2hhZF9hbmltYXRpb24iIHN0eWxlPSJkaXNwbGF5OiBub25lOyI+CiAgICA8ZGl2IGNsYXNzPSJldF9wYl9jb2x1bW4gZXRfcGJfY29sdW1uXzRfNCBldF9wYl9jb2x1bW5fNSBldF9wYl9jc3NfbWl4X2JsZW5kX21vZGVfcGFzc3Rocm91Z2ggZXQtbGFzdC1jaGlsZCI+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzAgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8aDQgY2xhc3M9ImV0X3BiX21vZHVsZV9oZWFkZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8c3BhbiBzdHlsZT0iZm9udC1zaXplOiAyMHB4ICFpbXBvcnRhbnQ7bGluZS1oZWlnaHQ6IDEgIWltcG9ydGFudDtmb250LXdlaWdodDogNjAwICFpbXBvcnRhbnQiPkVtYWlsIE1hbmlwdWxhdGlvbjwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBFQUMwMDA5PC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+TW9kaWZ5IHRoZSBmbG93IG9mIGVtYWlsIGluIHRoZSBlbnZpcm9ubWVudC48L3A+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzEgZW1haWwtbWFuaXB1bGF0aW9uLWxvbmctZGVzY3JpcHRpb24gZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5FbWFpbCBNYW5pcHVsYXRpb24gY292ZXJzIHRoZSB2YXJpb3VzIHdheXMgZW1haWwgZmxvd3MgaW4gdGhlIGVudmlyb25tZW50IGNhbiBiZSBhZmZlY3RlZC4gRW1haWwgTWFuaXB1bGF0aW9uIGNhbiBhZmZlY3Qgd2hpY2ggbWFpbCBhcHBsaWFuY2VzIHByb2Nlc3MgbWFpbCBmbG93cywgd2hlcmUgbWFpbCBpcyBmb3J3YXJkZWQsIG9yIHdoYXQgbWFpbCBpcyBwcmVzZW50IGluIGFuIGluYm94LiBBIGNvbW1vbiB1c2UgY2FzZSBmb3IgZW1haWwgbWFuaXB1bGF0aW9uIGlzIGFzIGEgdmVjdG9yIHRvIGludHJvZHVjZSBtYWx3YXJlIGludG8gdGhlIGVuZ2FnZW1lbnQgZW52aXJvbm1lbnQuICBTdXNwaWNpb3VzIGVtYWlscyBtYXkgYmUgcmVtb3ZlZCBmcm9tIHByb2R1Y3Rpb24gbWFpbGJveCBhbmQgcGxhY2VkIGludG8gYW4gaW5ib3ggaW4gYW4gZW5nYWdlbWVudCBlbnZpcm9ubWVudC4gVGhlbiwgYW55IHN1c3BpY2lvdXMgYXR0YWNobWVudHMgb3IgbGlua3MgY291bGQgYmUgZGV0b25hdGVkIGZyb20gd2l0aGluIHRoZSBlbnZpcm9ubWVudC4gQXMgYW5vdGhlciBleGFtcGxlLCBlbWFpbHMgY29sbGVjdGVkIG92ZXIgYSBsb25nIHBlcmlvZCBvZiB0aW1lIGZyb20gYSBsZWdpdGltYXRlIGluYm94IG91dHNpZGUgdGhlIGVudmlyb25tZW50IG1heSBiZSBtb3ZlZCBpbnRvIHRoZSBlbnZpcm9ubWVudCB0byByZWFzc3VyZSB0aGUgYWR2ZXJzYXJ5IG9mIHRoZSBlbnZpcm9ubWVudOKAmXMgbGVnaXRpbWFjeSBieSBjcmVhdGluZyBhIG1haWxib3ggdGhhdCBtb3JlIGNsb3NlbHkgcmVzZW1ibGVzIGEgcmVhbCwgbGl2ZWQtaW4gaW5ib3guPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMiBlbWFpbC1tYW5pcHVsYXRpb24tcmVmZXJlbmNlcyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InR0YWJsZSB0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBSZWZlcmVuY2UgTGlua3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vd3d3Lm55dGltZXMuY29tLzIwMTcvMDUvMDkvd29ybGQvZXVyb3BlL2hhY2tlcnMtY2FtZS1idXQtdGhlLWZyZW5jaC13ZXJlLXByZXBhcmVkLmh0bWwiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5IYWNrZXJzIENhbWUgYnV0IHRoZSBGcmVuY2ggV2VyZSBQcmVwYXJlZDwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMiBlbWFpbC1tYW5pcHVsYXRpb24tYXR0YWNrLW1hcHBpbmdzIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPkVudGVycHJpc2U8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA5Ij5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCB0aGUgZW52aXJvbm1lbnQgb3IgcGVyc29uYXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgd2hlbiB0aGV5IGNvbGxlY3QsIG9ic2VydmUsIG9yIG1hbmlwdWxhdGUgc3lzdGVtIGFydGlmYWN0cyBvciBpbmZvcm1hdGlvbi4gTWFuaXB1bGF0ZWQgZGF0YSBtYXkgY2F1c2UgdGhlbSB0byByZXZlYWwgYmVoYXZpb3JzLCB1c2UgYWRkaXRpb25hbCBvciBtb3JlIGFkdmFuY2VkIGNhcGFiaWxpdGllcyBhZ2FpbnN0IHRoZSB0YXJnZXQsIGFuZC9vciBpbXBhY3QgdGhlaXIgZHdlbGwgdGltZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA5Ij5Db2xsZWN0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIHRoZSBlbnZpcm9ubWVudCBvciBwZXJzb25hcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBjb2xsZWN0aW5nLCBvciBpbiBzb21lIHdheSBpbnRlcmFjdGluZyB3aXRoLCBtYW5pcHVsYXRlZCBvciBkZWNveSBkYXRhLiBJbiB0aG9zZSBjYXNlcyB0aGUgZGF0YSBtYXkgaW5jcmVhc2UgdGhlaXIgdG9sZXJhbmNlIGZvciBpbXBlcmZlY3Rpb25zIGluIHRoZSBlbnZpcm9ubWVudCBhbmQgaW1wcm92ZSB0aGUgb3ZlcmFsbCBiZWxpZXZhYmlsaXR5IG9mIHRoZSBydXNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDEiPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyB1c2UgcGhpc2hpbmcgZW1haWxzIHRvIGdhaW4gYWNjZXNzIHRvIHZpY3RpbSBzeXN0ZW1zLCB0aGV5IGhhdmUgbm8gY29udHJvbCBvdmVyIHdoZXJlIGEgbWFsaWNpb3VzIGF0dGFjaG1lbnQgaXMgZGV0b25hdGVkIGZyb20sIG9yIHdoZXJlIGEgbGluayBpcyBjbGlja2VkLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDkiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDEiPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIGVuZ2FnZW1lbnQgZW52aXJvbm1lbnRzIGFuZCBwZXJzb25hcywgdGhlaXIgZnV0dXJlIGNhcGFiaWxpdHksIHRhcmdldGluZywgYW5kL29yIGluZnJhc3RydWN0dXJlIHJlcXVpcmVtZW50cyBhcmUgdnVsbmVyYWJsZSB0byBpbmZsdWVuY2UuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgcGVyaXBoZXJhbC1tYW5hZ2VtZW50LWRldGFpbCBtYXRyaXgtZGV0YWlscyBldF9wYl9ndXR0ZXJzMSBldF9oYWRfYW5pbWF0aW9uIiBzdHlsZT0iZGlzcGxheTogbm9uZTsiPgogICAgPGRpdiBjbGFzcz0iZXRfcGJfY29sdW1uIGV0X3BiX2NvbHVtbl80XzQgZXRfcGJfY29sdW1uXzUgZXRfcGJfY3NzX21peF9ibGVuZF9tb2RlX3Bhc3N0aHJvdWdoIGV0LWxhc3QtY2hpbGQiPgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8wIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGg0IGNsYXNzPSJldF9wYl9tb2R1bGVfaGVhZGVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4gc3R5bGU9ImZvbnQtc2l6ZTogMjBweCAhaW1wb3J0YW50O2xpbmUtaGVpZ2h0OiAxICFpbXBvcnRhbnQ7Zm9udC13ZWlnaHQ6IDYwMCAhaW1wb3J0YW50Ij5QZXJpcGhlcmFsIE1hbmFnZW1lbnQ8L3NwYW4+CiAgICAgICAgICAgICAgICAgICAgPC9oND4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxoNT5JRDogRUFDMDAxMDwvaDU+CiAgICAgICAgICAgICAgICAgICAgICAgIDxwPk1hbmFnZSBwZXJpcGhlcmFsIGRldmljZXMgdXNlZCBvbiBzeXN0ZW1zIHdpdGhpbiB0aGUgbmV0d29yayBmb3IgZW5nYWdlbWVudCBwdXJwb3Nlcy48L3A+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzEgcGVyaXBoZXJhbC1tYW5hZ2VtZW50LWxvbmctZGVzY3JpcHRpb24gZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5QZXJpcGhlcmFsIE1hbmFnZW1lbnQgaXMgdGhlIGFkbWluaXN0cmF0aW9uIG9mIHBlcmlwaGVyYWwgZGV2aWNlcyB1c2VkIG9uIHN5c3RlbXMgd2l0aGluIHRoZSBlbmdhZ2VtZW50IGVudmlyb25tZW50LiBBIGRlZmVuZGVyIGNhbiBjaG9vc2UgdG8gYWxsb3cgb3IgZGVueSBjZXJ0YWluIHR5cGVzIG9mIHBlcmlwaGVyYWxzIGZyb20gYmVpbmcgdXNlZCBvbiBzeXN0ZW1zIHRvIGVpdGhlciBtb3RpdmF0ZSBvciBkZW1vdGl2YXRlIGFkdmVyc2FyeSBhY3Rpdml0eSBvciB0byBkaXJlY3QgdGhlIGFkdmVyc2FyeSB0b3dhcmRzIHNwZWNpZmljIHRhcmdldHMuIERlZmVuZGVycyBjYW4gYWxzbyBpbnRyb2R1Y2UgcGVyaXBoZXJhbHMgdG8gYW4gYWR2ZXJzYXJ5LWNvbnRyb2xsZWQgc3lzdGVtIHRvIHNlZSBob3cgdGhlIGFkdmVyc2FyeSByZWFjdHMuIEZvciBleGFtcGxlLCB0aGUgZGVmZW5kZXIgY2FuIGludHJvZHVjZSBleHRlcm5hbCBXaS1GaSBhZGFwdGVycywgVVNCIGRldmljZXMsIGV0Yy4gdG8gZGV0ZXJtaW5lIGlmIGFkdmVyc2FyaWVzIGF0dGVtcHQgdG8gdXNlIHRoZW0gZm9yIGV4ZmlsdHJhdGlvbiBwdXJwb3Nlcy4gIEFkZGl0aW9uYWxseSwgcGVyaXBoZXJhbHMgcHJvdmlkZSBhbiBhdmVudWUgZm9yIHRoZSBkZWZlbmRlciB0byBwcmVzZW50IG5ldyBvciBhZGRpdGlvbmFsIGluZm9ybWF0aW9uIHRvIHRoZSBhZHZlcnNhcnkuIFRoaXMgaW5mb3JtYXRpb24gY2FuIGJlIHVzZWQgdG8gaW50cm9kdWNlIGFuIGFkZGl0aW9uYWwgYXR0YWNrIHN1cmZhY2UsIG1vdGl2YXRlIG9yIGRlbW90aXZhdGUgYWR2ZXJzYXJ5IGFjdGl2aXR5LCBvciB0byBmdXJ0aGVyIHRoZSBkZWNlcHRpb24gc3RvcnkuIEZvciBleGFtcGxlLCB0aGUgZGVmZW5kZXIgbWF5IGluY2x1ZGUgZGF0YSBvbiBhIGNvbm5lY3RlZCBVU0IgZGV2aWNlIG9yIHN0YWdlIGFuIGltcG9ydGFudCBjb252ZXJzYXRpb24gbmVhciBhbiBleHRlcm5hbGx5IGNvbm5lY3RlZCBjYW1lcmEgb3IgbWljcm9waG9uZS4gRGVwZW5kaW5nIG9uIHRoZSBjb250ZW50cyBvZiB0aGlzIGRhdGEsIHRoZSBhZHZlcnNhcnkgbWF5IGJlIGVuY291cmFnZWQgdG8gdGFrZSBhIHNwZWNpZmljIGFjdGlvbiBhbmQvb3IgcmVhc3N1cmVkIGFib3V0IHRoZSBsZWdpdGltYWN5IG9mIHRoZSBlbnZpcm9ubWVudC48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIHBlcmlwaGVyYWwtbWFuYWdlbWVudC1hdHRhY2stbWFwcGluZ3MgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+RW50ZXJwcmlzZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMTEiPkNvbW1hbmQgYW5kIENvbnRyb2w8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDciPkRpc2NvdmVyeTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCB0aGUgZW52aXJvbm1lbnQgb3IgcGVyc29uYXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgd2hlbiB0aGV5IGNvbGxlY3QsIG9ic2VydmUsIG9yIG1hbmlwdWxhdGUgc3lzdGVtIGFydGlmYWN0cyBvciBpbmZvcm1hdGlvbi4gTWFuaXB1bGF0ZWQgZGF0YSBtYXkgY2F1c2UgdGhlbSB0byByZXZlYWwgYmVoYXZpb3JzLCB1c2UgYWRkaXRpb25hbCBvciBtb3JlIGFkdmFuY2VkIGNhcGFiaWxpdGllcyBhZ2FpbnN0IHRoZSB0YXJnZXQsIGFuZC9vciBpbXBhY3QgdGhlaXIgZHdlbGwgdGltZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA3Ij5EaXNjb3Zlcnk8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggZW5nYWdlbWVudCBlbnZpcm9ubWVudHMgYW5kIHBlcnNvbmFzLCB0aGVpciBmdXR1cmUgY2FwYWJpbGl0eSwgdGFyZ2V0aW5nLCBhbmQvb3IgaW5mcmFzdHJ1Y3R1cmUgcmVxdWlyZW1lbnRzIGFyZSB2dWxuZXJhYmxlIHRvIGluZmx1ZW5jZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOCI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBuZXR3b3JrIG9yIHN5c3RlbSByZXNvdXJjZXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdHJpZ2dlcmluZyB0cmlwd2lyZXMgb3IgZW5nYWdpbmcgaW4gZWFzaWx5IGRldGVjdGFibGUsIGFub21hbG91cyBiZWhhdmlvci48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDExIj5Db21tYW5kIGFuZCBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA3Ij5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMTAiPkV4ZmlsdHJhdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMSI+SW5pdGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDgiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHVzZSBoYXJkd2FyZSBwZXJpcGhlcmFscywgcmVtb3ZhYmxlIG1lZGlhLCBvciBjb25uZWN0ZWQgdHJhbnNpZW50IGN5YmVyIGFzc2V0cywgdGhleSBtdXN0IHJlbHkgb24gcGh5c2ljYWwgYWNjZXNzIG9yIGhhdmUgbGltaXRlZCBjb250cm9sIG92ZXIgd2hlbiBhbmQgd2hlcmUgaGFyZHdhcmUgYWRkaXRpb25zIGFyZSBjb25uZWN0ZWQgaW4gdGhlIHRhcmdldCBuZXR3b3JrLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDkiPkNvbGxlY3Rpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHJlbHkgb24gc3BlY2lmaWMgcmVzb3VyY2VzIHRvIGJlIGVuYWJsZWQsIGFjY2Vzc2libGUsIGFuZC9vciB2dWxuZXJhYmxlLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRoZWlyIG9wZXJhdGlvbnMgYmVpbmcgZGlzcnVwdGVkIGlmIHRoZSByZXNvdXJjZXMgYXJlIGRpc2FibGVkLCByZW1vdmVkLCBvciBvdGhlcndpc2UgbWFkZSBpbnZ1bG5lcmFibGUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAxMCI+RXhmaWx0cmF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBlbmFibGVkLCBhY2Nlc3NpYmxlLCBvciBpbnRlbnRpb25hbGx5IHdlYWtlbmVkL292ZXJseSBwZXJtaXNzaXZlIHJlc291cmNlcyBpbiB0aGUgZW52aXJvbm1lbnQgKHByb2R1Y3Rpb24gb3IgaXNvbGF0ZWQpLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHJldmVhbGluZyBhZGRpdGlvbmFsIG9yIG1vcmUgYWR2YW5jZWQgY2FwYWJpbGl0aWVzIHdoZW4gZXhwbG9pdGluZyBvciB1c2luZyBzYWlkIHJlc291cmNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDciPkRpc2NvdmVyeTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgbW92ZSBkYXRhIGFjcm9zcyB0aGUgbmV0d29yayBvciBpbnRlcmFjdCB3aXRoIHJlbW90ZSByZXNvdXJjZXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gbmV0d29yayBtYW5pcHVsYXRpb25zIHN1Y2ggYXMgaW1wYWN0cyB0byBuZXR3b3JrIGF2YWlsYWJpbGl0eSwgdHJhZmZpYyBmaWx0ZXJpbmcsIGRlZ3JhZGVkIHNwZWVkcywgZXRjLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+TW9iaWxlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAyNyI+SW5pdGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzMiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggbmV0d29yayBvciBzeXN0ZW0gcmVzb3VyY2VzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRyaWdnZXJpbmcgdHJpcHdpcmVzIG9yIGVuZ2FnaW5nIGluIGVhc2lseSBkZXRlY3RhYmxlLCBhbm9tYWxvdXMgYmVoYXZpb3IuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAyNyI+SW5pdGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzMiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHVzZSBoYXJkd2FyZSBwZXJpcGhlcmFscywgcmVtb3ZhYmxlIG1lZGlhLCBvciBjb25uZWN0ZWQgdHJhbnNpZW50IGN5YmVyIGFzc2V0cywgdGhleSBtdXN0IHJlbHkgb24gcGh5c2ljYWwgYWNjZXNzIG9yIGhhdmUgbGltaXRlZCBjb250cm9sIG92ZXIgd2hlbiBhbmQgd2hlcmUgaGFyZHdhcmUgYWRkaXRpb25zIGFyZSBjb25uZWN0ZWQgaW4gdGhlIHRhcmdldCBuZXR3b3JrLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzUiPkNvbGxlY3Rpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHJlbHkgb24gc3BlY2lmaWMgcmVzb3VyY2VzIHRvIGJlIGVuYWJsZWQsIGFjY2Vzc2libGUsIGFuZC9vciB2dWxuZXJhYmxlLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRoZWlyIG9wZXJhdGlvbnMgYmVpbmcgZGlzcnVwdGVkIGlmIHRoZSByZXNvdXJjZXMgYXJlIGRpc2FibGVkLCByZW1vdmVkLCBvciBvdGhlcndpc2UgbWFkZSBpbnZ1bG5lcmFibGUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5JQ1M8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA4Ij5Jbml0aWFsIEFjY2VzczwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXNlIGhhcmR3YXJlIHBlcmlwaGVyYWxzLCByZW1vdmFibGUgbWVkaWEsIG9yIGNvbm5lY3RlZCB0cmFuc2llbnQgY3liZXIgYXNzZXRzLCB0aGV5IG11c3QgcmVseSBvbiBwaHlzaWNhbCBhY2Nlc3Mgb3IgaGF2ZSBsaW1pdGVkIGNvbnRyb2wgb3ZlciB3aGVuIGFuZCB3aGVyZSBoYXJkd2FyZSBhZGRpdGlvbnMgYXJlIGNvbm5lY3RlZCBpbiB0aGUgdGFyZ2V0IG5ldHdvcmsuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgcG9ja2V0LWxpdHRlci1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+UG9ja2V0IExpdHRlcjwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBFQUMwMDExPC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+RGF0YSB1c2VkIHRvIHN1cHBvcnQgdGhlIGVuZ2FnZW1lbnQgbmFycmF0aXZlLjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBwb2NrZXQtbGl0dGVyLWxvbmctZGVzY3JpcHRpb24gZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5Qb2NrZXQgTGl0dGVyIGlzIGRhdGEgcGxhY2VkIG9uIGEgc3lzdGVtIHRvIGhlbHAgdGVsbCB0aGUgZW5nYWdlbWVudCBuYXJyYXRpdmUsIHRvIGluY3JlYXNlIHRoZSBjcmVkaWJpbGl0eSBvZiBhbiBlbnZpcm9ubWVudCwgYW5kL29yIHRvIGVzdGFibGlzaCBhIGNvZ25pdGl2ZSBiaWFzIHRvIHJhaXNlIHRoZSBhZHZlcnNhcnnigJlzIHRvbGVyYW5jZSB0byB3ZWFrbmVzc2VzIGluIHRoZSBlbnZpcm9ubWVudC4gVW5saWtlIEx1cmVzLCBQb2NrZXQgTGl0dGVyIGRvZXMgbm90IG5lY2Vzc2FyaWx5IGFpbSB0byBlbmNvdXJhZ2UgdGhlIGFkdmVyc2FyeSB0byB0YWtlIGEgc3BlY2lmaWMgYWN0aW9uLCBidXQgcmF0aGVyIGl0IHN1cHBvcnRzIHRoZSBvdmVyYWxsIGRlY2VwdGlvbiBzdG9yeS4gIFBvY2tldCBMaXR0ZXIgY2FuIGluY2x1ZGUgZG9jdW1lbnRzLCBwaWN0dXJlcywgcmVnaXN0cnkgZW50cmllcywgaW5zdGFsbGVkIHNvZnR3YXJlLCBsb2cgaGlzdG9yeSwgYnJvd3NpbmcgaGlzdG9yeSwgY29ubmVjdGlvbiBoaXN0b3J5LCBhbmQgb3RoZXIgdXNlciBkYXRhIHRoYXQgYW4gYWR2ZXJzYXJ5IHdvdWxkIGV4cGVjdCB0byBleGlzdCBvbiBhIHVzZXLigJlzIGNvbXB1dGVyLiBGb3IgZXhhbXBsZSwgYSBkZWZlbmRlciBtaWdodCBjb25kdWN0IGEgc2VyaWVzIG9mIHdlYiBzZWFyY2hlcyB0byBnZW5lcmF0ZSBicm93c2VyIGFydGlmYWN0cywgb3Igc2NhdHRlciBhIHZhcmlldHkgb2YgcGhvdG9zIGFuZCBkb2N1bWVudHMgYWNyb3NzIHRoZSBkZXNrdG9wIHRvIG1ha2UgdGhlIGNvbXB1dGVyIGZlZWwgbGl2ZWQgaW4uPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMiBwb2NrZXQtbGl0dGVyLXJlZmVyZW5jZXMgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0dGFibGUgdGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgUmVmZXJlbmNlIExpbmtzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2FjbGFudGhvbG9neS5vcmcvVzE4LTQxMDQucGRmIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+RW5oYW5jaW5nIENvaGVzaW9uIEFuZCBDb2hlcmVuY2UgT2YgRmFrZSBUZXh0IFRvIEltcHJvdmUgQmVsaWV2YWJpbGl0eSBGb3IgRGVjZWl2aW5nIEN5YmVyIEF0dGFja2VyczwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cHM6Ly9pZWVleHBsb3JlLmllZWUub3JnL2Fic3RyYWN0L2RvY3VtZW50Lzg5OTgyNTYiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5QaGFudG9tZnM6IEZpbGUtQmFzZWQgRGVjZXB0aW9uIFRlY2hub2xvZ3kgRm9yIFRod2FydGluZyBNYWxpY2lvdXMgVXNlcnM8L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgcG9ja2V0LWxpdHRlci1hdHRhY2stbWFwcGluZ3MgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+RW50ZXJwcmlzZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDciPkRpc2NvdmVyeTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCB0aGUgZW52aXJvbm1lbnQgb3IgcGVyc29uYXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgd2hlbiB0aGV5IGNvbGxlY3QsIG9ic2VydmUsIG9yIG1hbmlwdWxhdGUgc3lzdGVtIGFydGlmYWN0cyBvciBpbmZvcm1hdGlvbi4gTWFuaXB1bGF0ZWQgZGF0YSBtYXkgY2F1c2UgdGhlbSB0byByZXZlYWwgYmVoYXZpb3JzLCB1c2UgYWRkaXRpb25hbCBvciBtb3JlIGFkdmFuY2VkIGNhcGFiaWxpdGllcyBhZ2FpbnN0IHRoZSB0YXJnZXQsIGFuZC9vciBpbXBhY3QgdGhlaXIgZHdlbGwgdGltZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA5Ij5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDExIj5Db21tYW5kIGFuZCBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA2Ij5DcmVkZW50aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNSI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA3Ij5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDIiPkV4ZWN1dGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MCI+SW1wYWN0PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOCI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDQiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQzIj5SZWNvbm5haXNzYW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCB0aGUgZW52aXJvbm1lbnQgb3IgcGVyc29uYXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gY29sbGVjdGluZywgb3IgaW4gc29tZSB3YXkgaW50ZXJhY3Rpbmcgd2l0aCwgbWFuaXB1bGF0ZWQgb3IgZGVjb3kgZGF0YS4gSW4gdGhvc2UgY2FzZXMgdGhlIGRhdGEgbWF5IGluY3JlYXNlIHRoZWlyIHRvbGVyYW5jZSBmb3IgaW1wZXJmZWN0aW9ucyBpbiB0aGUgZW52aXJvbm1lbnQgYW5kIGltcHJvdmUgdGhlIG92ZXJhbGwgYmVsaWV2YWJpbGl0eSBvZiB0aGUgcnVzZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQwIj5JbXBhY3Q8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGEgZGl2ZXJzZSBzZXQgb2YgYWNjZXNzaWJsZSByZXNvdXJjZXMgYW5kIGRlY295IGFydGlmYWN0cyBvbiB0aGUgdGFyZ2V0LCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHJldmVhbGluZyB0aGVpciB0YXJnZXRpbmcgcHJlZmVyZW5jZXMgYW5kIGNhcGFiaWxpdGllcy48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDEwIj5FeGZpbHRyYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGNvbGxlY3QgbWFuaXB1bGF0ZWQgYXJ0aWZhY3RzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHJldmVhbGluZyB0aGVpciBwcmVzZW5jZSB3aGVuIHVzaW5nIG9yIG1vdmluZyB0aGUgYXJ0aWZhY3RzIGVsc2V3aGVyZSBpbiB0aGUgZW5nYWdlbWVudCBlbnZpcm9ubWVudC48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPk1vYmlsZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzIiPkRpc2NvdmVyeTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCB0aGUgZW52aXJvbm1lbnQgb3IgcGVyc29uYXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgd2hlbiB0aGV5IGNvbGxlY3QsIG9ic2VydmUsIG9yIG1hbmlwdWxhdGUgc3lzdGVtIGFydGlmYWN0cyBvciBpbmZvcm1hdGlvbi4gTWFuaXB1bGF0ZWQgZGF0YSBtYXkgY2F1c2UgdGhlbSB0byByZXZlYWwgYmVoYXZpb3JzLCB1c2UgYWRkaXRpb25hbCBvciBtb3JlIGFkdmFuY2VkIGNhcGFiaWxpdGllcyBhZ2FpbnN0IHRoZSB0YXJnZXQsIGFuZC9vciBpbXBhY3QgdGhlaXIgZHdlbGwgdGltZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM1Ij5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMxIj5DcmVkZW50aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMCI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMyIj5EaXNjb3Zlcnk8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggdGhlIGVudmlyb25tZW50IG9yIHBlcnNvbmFzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIGNvbGxlY3RpbmcsIG9yIGluIHNvbWUgd2F5IGludGVyYWN0aW5nIHdpdGgsIG1hbmlwdWxhdGVkIG9yIGRlY295IGRhdGEuIEluIHRob3NlIGNhc2VzIHRoZSBkYXRhIG1heSBpbmNyZWFzZSB0aGVpciB0b2xlcmFuY2UgZm9yIGltcGVyZmVjdGlvbnMgaW4gdGhlIGVudmlyb25tZW50IGFuZCBpbXByb3ZlIHRoZSBvdmVyYWxsIGJlbGlldmFiaWxpdHkgb2YgdGhlIHJ1c2UuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNCI+SW1wYWN0PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBhIGRpdmVyc2Ugc2V0IG9mIGFjY2Vzc2libGUgcmVzb3VyY2VzIGFuZCBkZWNveSBhcnRpZmFjdHMgb24gdGhlIHRhcmdldCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzIGFuZCBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5JQ1M8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAwIj5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAyIj5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDUiPkltcGFjdDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNyI+SW5oaWJpdCBSZXNwb25zZSBGdW5jdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwOCI+SW5pdGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDkiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMTAiPlBlcnNpc3RlbmNlPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIHRoZSBlbnZpcm9ubWVudCBvciBwZXJzb25hcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBjb2xsZWN0aW5nLCBvciBpbiBzb21lIHdheSBpbnRlcmFjdGluZyB3aXRoLCBtYW5pcHVsYXRlZCBvciBkZWNveSBkYXRhLiBJbiB0aG9zZSBjYXNlcyB0aGUgZGF0YSBtYXkgaW5jcmVhc2UgdGhlaXIgdG9sZXJhbmNlIGZvciBpbXBlcmZlY3Rpb25zIGluIHRoZSBlbnZpcm9ubWVudCBhbmQgaW1wcm92ZSB0aGUgb3ZlcmFsbCBiZWxpZXZhYmlsaXR5IG9mIHRoZSBydXNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDMiPkV2YXNpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHJlbHkgb24gc3BlY2lmaWMgcmVzb3VyY2VzIHRvIGJlIGVuYWJsZWQsIGFjY2Vzc2libGUsIGFuZC9vciB2dWxuZXJhYmxlLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRoZWlyIG9wZXJhdGlvbnMgYmVpbmcgZGlzcnVwdGVkIGlmIHRoZSByZXNvdXJjZXMgYXJlIGRpc2FibGVkLCByZW1vdmVkLCBvciBvdGhlcndpc2UgbWFkZSBpbnZ1bG5lcmFibGUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNyI+SW5oaWJpdCBSZXNwb25zZSBGdW5jdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXRpbGl6ZSBvciBhYnVzZSBzeXN0ZW0gZmVhdHVyZXMsIHNvZnR3YXJlLCBvciBvdGhlciByZXNvdXJjZXMsIHRoZXkgbWF5IGJlIHZ1bG5lcmFibGUgdG8gbW9uaXRvcmluZyBvciBNYW4taW4tdGhlLU1pZGRsZSBtYW5pcHVsYXRpb24uPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMCI+Q29sbGVjdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZGlzY292ZXIgYSBkaXZlcnNlIHNldCBvZiBhY2Nlc3NpYmxlIHJlc291cmNlcyBhbmQgZGVjb3kgYXJ0aWZhY3RzIG9uIHRoZSB0YXJnZXQsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gcmV2ZWFsaW5nIHRoZWlyIHRhcmdldGluZyBwcmVmZXJlbmNlcyBhbmQgY2FwYWJpbGl0aWVzLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDAiPkNvbGxlY3Rpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGluYWNjZXNzaWJsZSAoYnV0IHBvc3NpYmx5IHZhbHVhYmxlKSBkYXRhIG9yIGRhdGEgc3RyZWFtcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB3YXN0aW5nIHJlc291cmNlcyBvciByZXZlYWxpbmcgYWRkaXRpb25hbCBjYXBhYmlsaXRpZXMgaW4gYW4gZWZmb3J0IHRvIGFjY2VzcyB0aGUgY29udGVudC48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICA8L2Rpdj4KPC9kaXY+CjxkaXYgY2xhc3M9ImV0X3BiX3JvdyBldF9wYl9yb3dfMiBwZXJzb25hcy1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+UGVyc29uYXM8L3NwYW4+CiAgICAgICAgICAgICAgICAgICAgPC9oND4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxoNT5JRDogRUFDMDAxMjwvaDU+CiAgICAgICAgICAgICAgICAgICAgICAgIDxwPkNyZWF0ZSBmaWN0aXRpb3VzIGh1bWFuIHVzZXIocykgdGhyb3VnaCBhIGNvbWJpbmF0aW9uIG9mIHBsYW50ZWQgZGF0YSBhbmQgcmV2ZWFsZWQgYmVoYXZpb3IgcGF0dGVybnMuPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIHBlcnNvbmFzLWxvbmctZGVzY3JpcHRpb24gZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5BIFBlcnNvbmEgaXMgdXNlZCB0byBlc3RhYmxpc2ggYmFja2dyb3VuZCBpbmZvcm1hdGlvbiBhYm91dCBhIHZpY3RpbSB0byBpbmNyZWFzZSB0aGUgYmVsaWV2YWJpbGl0eSBvZiB0aGUgdGFyZ2V0LiBUbyBjcmVhdGUgYSBQZXJzb25hLCB0aGUgZGVmZW5kZXIgbXVzdCBkZXZlbG9wIGEgYmFja3N0b3J5IGFuZCBzZWVkIHRoZSBlbnZpcm9ubWVudCB3aXRoIHZhcnlpbmcgZGF0YSBpbiBzdXBwb3J0IG9mIHRoaXMgc3RvcnkuIERlcGVuZGluZyBvbiB0aGUgbmVlZCBmb3IgcmVhbGlzbSwgdGhlIGNvbnN0cnVjdGVkIHBlcnNvbmEgY2FuIGJlIHN1cHBvcnRlZCBieSBldmlkZW5jZSBvZiBob2JiaWVzLCBzb2NpYWwgYW5kIHByb2Zlc3Npb25hbCBpbnRlcmFjdGlvbnMsIGNvbnN1bWVyIHRyYW5zYWN0aW9ucywgZW1wbG95bWVudCwgYnJvd3NpbmcgaGFiaXRzLCBldGMuICBJbiBhZGRpdGlvbiB0byBsZW5kaW5nIGxlZ2l0aW1hY3kgdG8gdGhlIGVudmlyb25tZW50LCBwZXJzb25hcyBjYW4gYmUgdXNlZCB0byBlbmdhZ2UgZGlyZWN0bHkgd2l0aCBhZHZlcnNhcmllcywgc3VjaCBhcyBkdXJpbmcgcGhpc2hpbmcgZW1haWwgZXhjaGFuZ2VzLiBBZGRpdGlvbmFsbHksIHBlcnNvbmFzIGNhbiBtYWtlIGNoYW5nZXMgdG8gdGhlIGVudmlyb25tZW50IGR1cmluZyB0aGUgb3BlcmF0aW9uLCBzdWNoIGFzIGFkZGluZyBvciByZW1vdmluZyBhIFVTQiBkZXZpY2Ugb3IgaW50cm9kdWNpbmcgbmV3IGRlY295IGRvY3VtZW50cyBvciBjcmVkZW50aWFscy48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIHBlcnNvbmFzLWF0dGFjay1tYXBwaW5ncyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5FbnRlcnByaXNlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNyI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQzIj5SZWNvbm5haXNzYW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCB0aGUgZW52aXJvbm1lbnQgb3IgcGVyc29uYXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgd2hlbiB0aGV5IGNvbGxlY3QsIG9ic2VydmUsIG9yIG1hbmlwdWxhdGUgc3lzdGVtIGFydGlmYWN0cyBvciBpbmZvcm1hdGlvbi4gTWFuaXB1bGF0ZWQgZGF0YSBtYXkgY2F1c2UgdGhlbSB0byByZXZlYWwgYmVoYXZpb3JzLCB1c2UgYWRkaXRpb25hbCBvciBtb3JlIGFkdmFuY2VkIGNhcGFiaWxpdGllcyBhZ2FpbnN0IHRoZSB0YXJnZXQsIGFuZC9vciBpbXBhY3QgdGhlaXIgZHdlbGwgdGltZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA5Ij5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA1Ij5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDciPkRpc2NvdmVyeTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMSI+SW5pdGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDMiPlBlcnNpc3RlbmNlPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA0Ij5Qcml2aWxlZ2UgRXNjYWxhdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCB0aGUgZW52aXJvbm1lbnQgb3IgcGVyc29uYXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gY29sbGVjdGluZywgb3IgaW4gc29tZSB3YXkgaW50ZXJhY3Rpbmcgd2l0aCwgbWFuaXB1bGF0ZWQgb3IgZGVjb3kgZGF0YS4gSW4gdGhvc2UgY2FzZXMgdGhlIGRhdGEgbWF5IGluY3JlYXNlIHRoZWlyIHRvbGVyYW5jZSBmb3IgaW1wZXJmZWN0aW9ucyBpbiB0aGUgZW52aXJvbm1lbnQgYW5kIGltcHJvdmUgdGhlIG92ZXJhbGwgYmVsaWV2YWJpbGl0eSBvZiB0aGUgcnVzZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQzIj5SZWNvbm5haXNzYW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgY29sbGVjdCB0YXJnZXRpbmcgaW5mb3JtYXRpb24gZnJvbSBvcGVuIG9yIGNsb3NlZCBkYXRhIHNvdXJjZXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gYmVpbmcgaW5mbHVlbmNlZCBieSBtYW5pcHVsYXRlZCBvciBtaXNsZWFkaW5nIGRhdGEuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNiI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHJlbHkgb24gc3BlY2lmaWMgcmVzb3VyY2VzIHRvIGJlIGVuYWJsZWQsIGFjY2Vzc2libGUsIGFuZC9vciB2dWxuZXJhYmxlLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRoZWlyIG9wZXJhdGlvbnMgYmVpbmcgZGlzcnVwdGVkIGlmIHRoZSByZXNvdXJjZXMgYXJlIGRpc2FibGVkLCByZW1vdmVkLCBvciBvdGhlcndpc2UgbWFkZSBpbnZ1bG5lcmFibGUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNSI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA3Ij5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwNDAiPkltcGFjdDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMSI+SW5pdGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDMiPlBlcnNpc3RlbmNlPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA0Ij5Qcml2aWxlZ2UgRXNjYWxhdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZGlzY292ZXIgZW5hYmxlZCwgYWNjZXNzaWJsZSwgb3IgaW50ZW50aW9uYWxseSB3ZWFrZW5lZC9vdmVybHkgcGVybWlzc2l2ZSByZXNvdXJjZXMgaW4gdGhlIGVudmlyb25tZW50IChwcm9kdWN0aW9uIG9yIGlzb2xhdGVkKSwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgYWRkaXRpb25hbCBvciBtb3JlIGFkdmFuY2VkIGNhcGFiaWxpdGllcyB3aGVuIGV4cGxvaXRpbmcgb3IgdXNpbmcgc2FpZCByZXNvdXJjZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDExIj5Db21tYW5kIGFuZCBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAyIj5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDEiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQzIj5SZWNvbm5haXNzYW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3QgZGlyZWN0bHkgd2l0aCB2aWN0aW1zLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIGJlaW5nIHNvY2lhbGx5IGVuZ2luZWVyZWQgb3Igb3RoZXJ3aXNlIG1hbmlwdWxhdGVkIGJ5IGFuIGF3YXJlIHVzZXIuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAxMSI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNSI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDQiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBhIGRpdmVyc2Ugc2V0IG9mIGFjY2Vzc2libGUgcmVzb3VyY2VzIGFuZCBkZWNveSBhcnRpZmFjdHMgb24gdGhlIHRhcmdldCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzIGFuZCBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MyI+UmVjb25uYWlzc2FuY2U8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGNvbGxlY3QgdGFyZ2V0aW5nIGluZm9ybWF0aW9uIGZyb20gb3BlbiBvciBjbG9zZWQgZGF0YSBzb3VyY2VzLCB0aGV5IG1heSByZXZlYWwgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDYiPkNyZWRlbnRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBjb2xsZWN0IG1hbmlwdWxhdGVkIGFydGlmYWN0cywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgcHJlc2VuY2Ugd2hlbiB1c2luZyBvciBtb3ZpbmcgdGhlIGFydGlmYWN0cyBlbHNld2hlcmUgaW4gdGhlIGVuZ2FnZW1lbnQgZW52aXJvbm1lbnQuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5Nb2JpbGU8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM1Ij5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMyIj5EaXNjb3Zlcnk8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggdGhlIGVudmlyb25tZW50IG9yIHBlcnNvbmFzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHdoZW4gdGhleSBjb2xsZWN0LCBvYnNlcnZlLCBvciBtYW5pcHVsYXRlIHN5c3RlbSBhcnRpZmFjdHMgb3IgaW5mb3JtYXRpb24uIE1hbmlwdWxhdGVkIGRhdGEgbWF5IGNhdXNlIHRoZW0gdG8gcmV2ZWFsIGJlaGF2aW9ycywgdXNlIGFkZGl0aW9uYWwgb3IgbW9yZSBhZHZhbmNlZCBjYXBhYmlsaXRpZXMgYWdhaW5zdCB0aGUgdGFyZ2V0LCBhbmQvb3IgaW1wYWN0IHRoZWlyIGR3ZWxsIHRpbWUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMSI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggdGhlIGVudmlyb25tZW50IG9yIHBlcnNvbmFzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIGNvbGxlY3RpbmcsIG9yIGluIHNvbWUgd2F5IGludGVyYWN0aW5nIHdpdGgsIG1hbmlwdWxhdGVkIG9yIGRlY295IGRhdGEuIEluIHRob3NlIGNhc2VzIHRoZSBkYXRhIG1heSBpbmNyZWFzZSB0aGVpciB0b2xlcmFuY2UgZm9yIGltcGVyZmVjdGlvbnMgaW4gdGhlIGVudmlyb25tZW50IGFuZCBpbXByb3ZlIHRoZSBvdmVyYWxsIGJlbGlldmFiaWxpdHkgb2YgdGhlIHJ1c2UuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMSI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHJlbHkgb24gc3BlY2lmaWMgcmVzb3VyY2VzIHRvIGJlIGVuYWJsZWQsIGFjY2Vzc2libGUsIGFuZC9vciB2dWxuZXJhYmxlLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRoZWlyIG9wZXJhdGlvbnMgYmVpbmcgZGlzcnVwdGVkIGlmIHRoZSByZXNvdXJjZXMgYXJlIGRpc2FibGVkLCByZW1vdmVkLCBvciBvdGhlcndpc2UgbWFkZSBpbnZ1bG5lcmFibGUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNCI+SW1wYWN0PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBlbmFibGVkLCBhY2Nlc3NpYmxlLCBvciBpbnRlbnRpb25hbGx5IHdlYWtlbmVkL292ZXJseSBwZXJtaXNzaXZlIHJlc291cmNlcyBpbiB0aGUgZW52aXJvbm1lbnQgKHByb2R1Y3Rpb24gb3IgaXNvbGF0ZWQpLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHJldmVhbGluZyBhZGRpdGlvbmFsIG9yIG1vcmUgYWR2YW5jZWQgY2FwYWJpbGl0aWVzIHdoZW4gZXhwbG9pdGluZyBvciB1c2luZyBzYWlkIHJlc291cmNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzUiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzciPkNvbW1hbmQgYW5kIENvbnRyb2w8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzEiPkNyZWRlbnRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM0Ij5JbXBhY3Q8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMjciPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCBkaXJlY3RseSB3aXRoIHZpY3RpbXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gYmVpbmcgc29jaWFsbHkgZW5naW5lZXJlZCBvciBvdGhlcndpc2UgbWFuaXB1bGF0ZWQgYnkgYW4gYXdhcmUgdXNlci48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM1Ij5Db2xsZWN0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBhIGRpdmVyc2Ugc2V0IG9mIGFjY2Vzc2libGUgcmVzb3VyY2VzIGFuZCBkZWNveSBhcnRpZmFjdHMgb24gdGhlIHRhcmdldCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzIGFuZCBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5JQ1M8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAwIj5Db2xsZWN0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIHRoZSBlbnZpcm9ubWVudCBvciBwZXJzb25hcywgdGhleSBhcmUgdnVsbmVyYWJsZSB3aGVuIHRoZXkgY29sbGVjdCwgb2JzZXJ2ZSwgb3IgbWFuaXB1bGF0ZSBzeXN0ZW0gYXJ0aWZhY3RzIG9yIGluZm9ybWF0aW9uLiBNYW5pcHVsYXRlZCBkYXRhIG1heSBjYXVzZSB0aGVtIHRvIHJldmVhbCBiZWhhdmlvcnMsIHVzZSBhZGRpdGlvbmFsIG9yIG1vcmUgYWR2YW5jZWQgY2FwYWJpbGl0aWVzIGFnYWluc3QgdGhlIHRhcmdldCwgYW5kL29yIGltcGFjdCB0aGVpciBkd2VsbCB0aW1lLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDAiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDkiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMTAiPlBlcnNpc3RlbmNlPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIHRoZSBlbnZpcm9ubWVudCBvciBwZXJzb25hcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBjb2xsZWN0aW5nLCBvciBpbiBzb21lIHdheSBpbnRlcmFjdGluZyB3aXRoLCBtYW5pcHVsYXRlZCBvciBkZWNveSBkYXRhLiBJbiB0aG9zZSBjYXNlcyB0aGUgZGF0YSBtYXkgaW5jcmVhc2UgdGhlaXIgdG9sZXJhbmNlIGZvciBpbXBlcmZlY3Rpb25zIGluIHRoZSBlbnZpcm9ubWVudCBhbmQgaW1wcm92ZSB0aGUgb3ZlcmFsbCBiZWxpZXZhYmlsaXR5IG9mIHRoZSBydXNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDgiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA5Ij5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTEwIj5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZGlzY292ZXIgZW5hYmxlZCwgYWNjZXNzaWJsZSwgb3IgaW50ZW50aW9uYWxseSB3ZWFrZW5lZC9vdmVybHkgcGVybWlzc2l2ZSByZXNvdXJjZXMgaW4gdGhlIGVudmlyb25tZW50IChwcm9kdWN0aW9uIG9yIGlzb2xhdGVkKSwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgYWRkaXRpb25hbCBvciBtb3JlIGFkdmFuY2VkIGNhcGFiaWxpdGllcyB3aGVuIGV4cGxvaXRpbmcgb3IgdXNpbmcgc2FpZCByZXNvdXJjZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA0Ij5FeGVjdXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IGRpcmVjdGx5IHdpdGggdmljdGltcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBiZWluZyBzb2NpYWxseSBlbmdpbmVlcmVkIG9yIG90aGVyd2lzZSBtYW5pcHVsYXRlZCBieSBhbiBhd2FyZSB1c2VyLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDkiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMTAiPlBlcnNpc3RlbmNlPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBhIGRpdmVyc2Ugc2V0IG9mIGFjY2Vzc2libGUgcmVzb3VyY2VzIGFuZCBkZWNveSBhcnRpZmFjdHMgb24gdGhlIHRhcmdldCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzIGFuZCBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMCI+Q29sbGVjdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgY29sbGVjdCB0YXJnZXRpbmcgaW5mb3JtYXRpb24gZnJvbSBvcGVuIG9yIGNsb3NlZCBkYXRhIHNvdXJjZXMsIHRoZXkgbWF5IHJldmVhbCB0aGVpciB0YXJnZXRpbmcgcHJlZmVyZW5jZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgbWFsd2FyZS1kZXRvbmF0aW9uLWRldGFpbCBtYXRyaXgtZGV0YWlscyBldF9wYl9ndXR0ZXJzMSBldF9oYWRfYW5pbWF0aW9uIiBzdHlsZT0iZGlzcGxheTogbm9uZTsiPgogICAgPGRpdiBjbGFzcz0iZXRfcGJfY29sdW1uIGV0X3BiX2NvbHVtbl80XzQgZXRfcGJfY29sdW1uXzUgZXRfcGJfY3NzX21peF9ibGVuZF9tb2RlX3Bhc3N0aHJvdWdoIGV0LWxhc3QtY2hpbGQiPgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8wIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGg0IGNsYXNzPSJldF9wYl9tb2R1bGVfaGVhZGVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4gc3R5bGU9ImZvbnQtc2l6ZTogMjBweCAhaW1wb3J0YW50O2xpbmUtaGVpZ2h0OiAxICFpbXBvcnRhbnQ7Zm9udC13ZWlnaHQ6IDYwMCAhaW1wb3J0YW50Ij5NYWx3YXJlIERldG9uYXRpb248L3NwYW4+CiAgICAgICAgICAgICAgICAgICAgPC9oND4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxoNT5JRDogRUFDMDAxMzwvaDU+CiAgICAgICAgICAgICAgICAgICAgICAgIDxwPkV4ZWN1dGUgbWFsd2FyZSB1bmRlciBjb250cm9sbGVkIGNvbmRpdGlvbnMgdG8gYW5hbHl6ZSBpdHMgZnVuY3Rpb25hbGl0eS48L3A+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzEgbWFsd2FyZS1kZXRvbmF0aW9uLWxvbmctZGVzY3JpcHRpb24gZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5NYWx3YXJlIGNhbiBiZSBkZXRvbmF0ZWQgaW4gYSBjb250cm9sbGVkIGFuZCBzYWZlIGVudmlyb25tZW50LiBDbGVhciBnb2FscyBhbmQgc2FmZXR5IHByb2NlZHVyZXMgc2hvdWxkIGFsd2F5cyBiZSBlc3RhYmxpc2hlZCBiZWZvcmUgZGV0b25hdGlvbiB0byBlbnN1cmUgdGhhdCB0aGUgb3BlcmF0aW9uIGlzIGZvY3VzZWQgYW5kIHNhZmUuIFRoZSBtYWx3YXJlIGNhbiBiZSBkZXRvbmF0ZWQgaW4gYW4gZXhlY3V0aW9uIGVudmlyb25tZW50IHJhbmdpbmcgZnJvbSBhIHNvbWV3aGF0IHN0ZXJpbGUgY29tbWVyY2lhbCBtYWx3YXJlIGV4ZWN1dGlvbiBhcHBsaWFuY2UgdG8gYSBiZXNwb2tlIGVuZ2FnZW1lbnQgZW52aXJvbm1lbnQgY3JhZnRlZCB0byBzdXBwb3J0IGFuIGV4dGVuZGVkIGVuZ2FnZW1lbnQuICBEZXBlbmRpbmcgb24gb3BlcmF0aW9uYWwgb2JqZWN0aXZlcywgdGhlIG91dGNvbWUgb2YgYSBtYWx3YXJlIGRldG9uYXRpb24gb3BlcmF0aW9uIGNhbiBpbmNsdWRlOiBjb2xsZWN0aW5nIG5ldyBJT0NzIGR1cmluZyBkeW5hbWljIGFuYWx5c2lzLCAgb2JzZXJ2aW5nIGFkZGl0aW9uYWwgVFRQcyBieSBkZXRvbmF0aW5nIHRoZSBtYWx3YXJlIGluIGEgdGFyZ2V0IHJpY2ggZW52aXJvbm1lbnQsIGFuZC9vciBuZWdhdGl2ZWx5IGltcGFjdGluZyB0aGUgYWR2ZXJzYXJ5IGFuZCB0aGVpciBvcGVyYXRpb24uIDwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgbWFsd2FyZS1kZXRvbmF0aW9uLXJlZmVyZW5jZXMgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0dGFibGUgdGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgUmVmZXJlbmNlIExpbmtzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL3NlZmNvbS5hc3UuZWR1L3B1YmxpY2F0aW9ucy91dGlsaXppbmctbmV0d29yay1zY2llbmNlLWhpY3NzMjAxNS5wZGYiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5VdGlsaXppbmcgTmV0d29yayBTY2llbmNlIEFuZCBIb25leW5ldHMgRm9yIFNvZnR3YXJlIEluZHVjZWQgQ3liZXIgSW5jaWRlbnQgQW5hbHlzaXM8L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vYXBwcy5kdGljLm1pbC9zdGkvcGRmcy9BREE1MjczMjgucGRmIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+RHVwaW5nIFRoZSBTb3ZpZXRzOiBUaGUgRmFyZXdlbGwgRG9zc2llcjwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMiBtYWx3YXJlLWRldG9uYXRpb24tYXR0YWNrLW1hcHBpbmdzIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPkVudGVycHJpc2U8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDExIj5Db21tYW5kIGFuZCBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA1Ij5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDIiPkV4ZWN1dGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MCI+SW1wYWN0PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllc+KAmSBtYWx3YXJlIGlzIGRldG9uYXRlZCwgdGhleSBtYXkgYmUgZW5jb3VyYWdlZCB0byBvcGVyYXRlIGluIGFuIHVuaW50ZW5kZWQgZW52aXJvbm1lbnQuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAxMSI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZGlzY292ZXIgYSBkaXZlcnNlIHNldCBvZiBhY2Nlc3NpYmxlIHJlc291cmNlcyBhbmQgZGVjb3kgYXJ0aWZhY3RzIG9uIHRoZSB0YXJnZXQsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gcmV2ZWFsaW5nIHRoZWlyIHRhcmdldGluZyBwcmVmZXJlbmNlcyBhbmQgY2FwYWJpbGl0aWVzLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDUiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMiI+RXhlY3V0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllc+KAmSBtYWx3YXJlIGlzIGRldG9uYXRlZCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBkeW5hbWljIGFuYWx5c2lzLCB3aGljaCBjYW4gcmV2ZWFsIGhvdyB0aGUgbWFsd2FyZSBpbnRlcmFjdHMgd2l0aCBzeXN0ZW0gcmVzb3VyY2VzLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+TW9iaWxlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMCI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM0Ij5JbXBhY3Q8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVz4oCZIG1hbHdhcmUgaXMgZGV0b25hdGVkLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIGR5bmFtaWMgYW5hbHlzaXMsIHdoaWNoIGNhbiByZXZlYWwgaG93IHRoZSBtYWx3YXJlIGludGVyYWN0cyB3aXRoIHN5c3RlbSByZXNvdXJjZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5JQ1M8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA0Ij5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDgiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTEwIj5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXPigJkgbWFsd2FyZSBpcyBkZXRvbmF0ZWQsIHRoZXkgbWF5IGJlIGVuY291cmFnZWQgdG8gb3BlcmF0ZSBpbiBhbiB1bmludGVuZGVkIGVudmlyb25tZW50LjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDQiPkV4ZWN1dGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwOCI+SW5pdGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMTAiPlBlcnNpc3RlbmNlPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllc+KAmSBtYWx3YXJlIGlzIGRldG9uYXRlZCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBkeW5hbWljIGFuYWx5c2lzLCB3aGljaCBjYW4gcmV2ZWFsIGhvdyB0aGUgbWFsd2FyZSBpbnRlcmFjdHMgd2l0aCBzeXN0ZW0gcmVzb3VyY2VzLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgIDwvZGl2Pgo8L2Rpdj4KPGRpdiBjbGFzcz0iZXRfcGJfcm93IGV0X3BiX3Jvd18yIHNvZnR3YXJlLW1hbmlwdWxhdGlvbi1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+U29mdHdhcmUgTWFuaXB1bGF0aW9uPC9zcGFuPgogICAgICAgICAgICAgICAgICAgIDwvaDQ+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8aDU+SUQ6IEVBQzAwMTQ8L2g1PgogICAgICAgICAgICAgICAgICAgICAgICA8cD5NYWtlIGNoYW5nZXMgdG8gYSBzeXN0ZW3igJlzIHNvZnR3YXJlIHByb3BlcnRpZXMgYW5kIGZ1bmN0aW9ucyB0byBhY2hpZXZlIGEgZGVzaXJlZCBlZmZlY3QuPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIHNvZnR3YXJlLW1hbmlwdWxhdGlvbi1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+U29mdHdhcmUgTWFuaXB1bGF0aW9uIGFsbG93cyBhIGRlZmVuZGVyIHRvIGFsdGVyIG9yIHJlcGxhY2UgZWxlbWVudHMgb2YgdGhlIE9TLCBmaWxlIHN5c3RlbSwgb3Igb3RoZXIgc29mdHdhcmUgaW5zdGFsbGVkIGFuZCBleGVjdXRlZCBvbiBhIHN5c3RlbS4gVGhlc2UgYWx0ZXJhdGlvbnMgY2FuIGFmZmVjdCBvdXRwdXRzLCBkZWdyYWRlIGVmZmVjdGl2ZW5lc3MsIGFuZC9vciBwcmV2ZW50IHRoZSBzb2Z0d2FyZSBmcm9tIGZ1bmN0aW9uaW5nIGFsdG9nZXRoZXIuIEZvciBleGFtcGxlLCB0aGUgZGVmZW5kZXIgY2FuIG1hbmlwdWxhdGUgc29mdHdhcmUgYnkgY2hhbmdpbmcgdGhlIG91dHB1dCBvZiBjb21tb25seSB1c2VkIGRpc2NvdmVyeSBjb21tYW5kcyB0byBoaWRlIGxlZ2l0aW1hdGUgc3lzdGVtcyBhbmQgYXJ0aWZhY3RzIGFuZC9vciByZXZlYWwgZGVjZXB0aXZlIGFydGlmYWN0cyBhbmQgc3lzdGVtcy4gIEFsdGVybmF0aXZlbHksIHRoZSBkZWZlbmRlciBjYW4gY2hhbmdlIHRoZSBvdXRwdXQgb2YgdGhlIHBhc3N3b3JkIHBvbGljeSBkZXNjcmlwdGlvbiBmb3IgYW4gYWR2ZXJzYXJ5IGF0dGVtcHRpbmcgdG8gYnJ1dGUtZm9yY2UgY3JlZGVudGlhbHMuIFRoaXMgbWFuaXB1bGF0aW9uIG1heSBjYXVzZSB0aGUgYWR2ZXJzYXJ5IHRvIHdhc3RlIHJlc291cmNlcyBicnV0ZS1mb3JjaW5nIHBhc3N3b3JkcyB3aXRoIGluYWNjdXJhdGUgY29tcGxleGl0eSByZXF1aXJlbWVudHMuIElmIHRoZSBkZWZlbmRlciB3YW50ZWQgdG8gZGVncmFkZSBzb2Z0d2FyZSBlZmZlY3RpdmVuZXNzLCB0aGV5IG1pZ2h0IHdlYWtlbiBhbGdvcml0aG1zIHRvIGV4cG9zZSBkYXRhIHRoYXQgaXMgYmVpbmcgYXJjaGl2ZWQsIGVuY29kZWQsIGFuZC9vciBlbmNyeXB0ZWQuICBGaW5hbGx5LCB0byBwcmV2ZW50IHNvZnR3YXJlIGZyb20gZnVuY3Rpb25pbmcgYWx0b2dldGhlciwgdGhlIGRlZmVuZGVyIG1heSBjYXVzZSBmYWlsdXJlcyBpbiBzb2Z0d2FyZSB0eXBpY2FsbHkgdXNlZCB0byBkZWxldGUgZGF0YSBvciBoaWRlIGFkdmVyc2FyeSBhcnRpZmFjdHMuIEZvciBzb21lIFNvZnR3YXJlIE1hbmlwdWxhdGlvbiB1c2UgY2FzZXMsIGl0IG1heSBiZSBwb3NzaWJsZSB0byBtYWtlIGNoYW5nZXMgaW4gc3VjaCBhIHdheSB0aGF0IGFkdmVyc2FyeSBhY3Rpb25zIGFuZCBsZWdpdGltYXRlIHVzZXIgYWN0aW9ucyBhcmUgaGFuZGxlZCBkaWZmZXJlbnRseS4gRm9yIGV4YW1wbGUsIHRoZSBkZWZlbmRlciBjb3VsZCBzaG93IGFsbCBmaWxlcyB3aGVuIHZpZXdlZCBpbiBhIGdyYXBoaWNhbCBhcHBsaWNhdGlvbiBidXQgaGlkZSBmaWxlcyBvciBpbnRyb2R1Y2UgZGVjb3kgZmlsZXMgd2hlbiB2aWV3ZWQgdmlhIGEgdGVybWluYWwgY29tbWFuZC4gVGhpcyBzZXR1cCB3b3VsZCBhbGxvdyBsZWdpdGltYXRlIHVzZXJzIGZ1bGwgYWNjZXNzIHRvIHRoZSBmaWxlIHN5c3RlbSwgd2hpbGUgbWFuaXB1bGF0aW5nIGFjY2VzcyBmb3IgYWR2ZXJzYXJpZXMgdXNpbmcgYSByZXZlcnNlIHNoZWxsLjwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgc29mdHdhcmUtbWFuaXB1bGF0aW9uLXJlZmVyZW5jZXMgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0dGFibGUgdGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgUmVmZXJlbmNlIExpbmtzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2llZWV4cGxvcmUuaWVlZS5vcmcvYWJzdHJhY3QvZG9jdW1lbnQvNzM0Njg0Mi8iIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5BIERlY2VwdGlvbiBCYXNlZCBBcHByb2FjaCBGb3IgRGVmZWF0aW5nIE9TIEFuZCBTZXJ2aWNlIEZpbmdlcnByaW50aW5nPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2NpdGVzZWVyeC5pc3QucHN1LmVkdS92aWV3ZG9jL2Rvd25sb2FkP2RvaT0xMC4xLjEuNjk2LjI4MDMmYW1wO3JlcD1yZXAxJmFtcDt0eXBlPXBkZiIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPkZyb20gUGF0Y2hlcyBUbyBIb25leS1QYXRjaGVzOiBMaWdodHdlaWdodCBBdHRhY2tlciBNaXNkaXJlY3Rpb24sIERlY2VwdGlvbiwgQW5kIERpc2luZm9ybWF0aW9uPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2FwcHMuZHRpYy5taWwvc3RpL3BkZnMvQURBNDg1MDAzLnBkZiIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPlVzaW5nIERlY2VwdGlvbiBUbyBIaWRlIFRoaW5ncyBGcm9tIEhhY2tlcnM6IFByb2Nlc3NlcywgUHJpbmNpcGxlcywgQW5kIFRlY2huaXF1ZXM8L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgc29mdHdhcmUtbWFuaXB1bGF0aW9uLWF0dGFjay1tYXBwaW5ncyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5FbnRlcnByaXNlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNyI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAyIj5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwNDAiPkltcGFjdDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDQiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIHRoZSBlbnZpcm9ubWVudCBvciBwZXJzb25hcywgdGhleSBhcmUgdnVsbmVyYWJsZSB3aGVuIHRoZXkgY29sbGVjdCwgb2JzZXJ2ZSwgb3IgbWFuaXB1bGF0ZSBzeXN0ZW0gYXJ0aWZhY3RzIG9yIGluZm9ybWF0aW9uLiBNYW5pcHVsYXRlZCBkYXRhIG1heSBjYXVzZSB0aGVtIHRvIHJldmVhbCBiZWhhdmlvcnMsIHVzZSBhZGRpdGlvbmFsIG9yIG1vcmUgYWR2YW5jZWQgY2FwYWJpbGl0aWVzIGFnYWluc3QgdGhlIHRhcmdldCwgYW5kL29yIGltcGFjdCB0aGVpciBkd2VsbCB0aW1lLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDciPkRpc2NvdmVyeTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBlbmdhZ2VtZW50IGVudmlyb25tZW50cyBhbmQgcGVyc29uYXMsIHRoZWlyIGZ1dHVyZSBjYXBhYmlsaXR5LCB0YXJnZXRpbmcsIGFuZC9vciBpbmZyYXN0cnVjdHVyZSByZXF1aXJlbWVudHMgYXJlIHZ1bG5lcmFibGUgdG8gaW5mbHVlbmNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDEiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA4Ij5MYXRlcmFsIE1vdmVtZW50PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIG5ldHdvcmsgb3Igc3lzdGVtIHJlc291cmNlcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB0cmlnZ2VyaW5nIHRyaXB3aXJlcyBvciBlbmdhZ2luZyBpbiBlYXNpbHkgZGV0ZWN0YWJsZSwgYW5vbWFsb3VzIGJlaGF2aW9yLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDUiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHJlbHkgb24gc3BlY2lmaWMgcmVzb3VyY2VzIHRvIGJlIGVuYWJsZWQsIGFjY2Vzc2libGUsIGFuZC9vciB2dWxuZXJhYmxlLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRoZWlyIG9wZXJhdGlvbnMgYmVpbmcgZGlzcnVwdGVkIGlmIHRoZSByZXNvdXJjZXMgYXJlIGRpc2FibGVkLCByZW1vdmVkLCBvciBvdGhlcndpc2UgbWFkZSBpbnZ1bG5lcmFibGUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAxMSI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNiI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDUiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNyI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAyIj5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwNDAiPkltcGFjdDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOCI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDQiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyB1dGlsaXplIG9yIGFidXNlIHN5c3RlbSBmZWF0dXJlcywgc29mdHdhcmUsIG9yIG90aGVyIHJlc291cmNlcywgdGhleSBtYXkgYmUgdnVsbmVyYWJsZSB0byBtb25pdG9yaW5nIG9yIE1hbi1pbi10aGUtTWlkZGxlIG1hbmlwdWxhdGlvbi48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA3Ij5EaXNjb3Zlcnk8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGEgZGl2ZXJzZSBzZXQgb2YgYWNjZXNzaWJsZSByZXNvdXJjZXMgYW5kIGRlY295IGFydGlmYWN0cyBvbiB0aGUgdGFyZ2V0LCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHJldmVhbGluZyB0aGVpciB0YXJnZXRpbmcgcHJlZmVyZW5jZXMgYW5kIGNhcGFiaWxpdGllcy48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA2Ij5DcmVkZW50aWFsIEFjY2VzczwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXNlIGJydXRlLWZvcmNlIHRlY2huaXF1ZXMgdG8gYWNjZXNzIGFjY291bnRzIG9yIGVuY3J5cHRlZCBkYXRhLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHdhc3RpbmcgcmVzb3VyY2VzIGlmIHRoZSBhcnRpZmFjdCBoYXMgbm8gdmFsaWQgY3JlZGVudGlhbHMgb3IgaXMgbG9ja2VkIGluIHNvbWUgb3RoZXIgd2F5LjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+TW9iaWxlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MSI+RXhlY3V0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM0Ij5JbXBhY3Q8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMjgiPlBlcnNpc3RlbmNlPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIHRoZSBlbnZpcm9ubWVudCBvciBwZXJzb25hcywgdGhleSBhcmUgdnVsbmVyYWJsZSB3aGVuIHRoZXkgY29sbGVjdCwgb2JzZXJ2ZSwgb3IgbWFuaXB1bGF0ZSBzeXN0ZW0gYXJ0aWZhY3RzIG9yIGluZm9ybWF0aW9uLiBNYW5pcHVsYXRlZCBkYXRhIG1heSBjYXVzZSB0aGVtIHRvIHJldmVhbCBiZWhhdmlvcnMsIHVzZSBhZGRpdGlvbmFsIG9yIG1vcmUgYWR2YW5jZWQgY2FwYWJpbGl0aWVzIGFnYWluc3QgdGhlIHRhcmdldCwgYW5kL29yIGltcGFjdCB0aGVpciBkd2VsbCB0aW1lLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzEiPkNyZWRlbnRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIHRoZSBlbnZpcm9ubWVudCBvciBwZXJzb25hcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBjb2xsZWN0aW5nLCBvciBpbiBzb21lIHdheSBpbnRlcmFjdGluZyB3aXRoLCBtYW5pcHVsYXRlZCBvciBkZWNveSBkYXRhLiBJbiB0aG9zZSBjYXNlcyB0aGUgZGF0YSBtYXkgaW5jcmVhc2UgdGhlaXIgdG9sZXJhbmNlIGZvciBpbXBlcmZlY3Rpb25zIGluIHRoZSBlbnZpcm9ubWVudCBhbmQgaW1wcm92ZSB0aGUgb3ZlcmFsbCBiZWxpZXZhYmlsaXR5IG9mIHRoZSBydXNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzAiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNCI+SW1wYWN0PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIGVuZ2FnZW1lbnQgZW52aXJvbm1lbnRzIGFuZCBwZXJzb25hcywgdGhlaXIgZnV0dXJlIGNhcGFiaWxpdHksIHRhcmdldGluZywgYW5kL29yIGluZnJhc3RydWN0dXJlIHJlcXVpcmVtZW50cyBhcmUgdnVsbmVyYWJsZSB0byBpbmZsdWVuY2UuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAyNyI+SW5pdGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzMiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggbmV0d29yayBvciBzeXN0ZW0gcmVzb3VyY2VzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRyaWdnZXJpbmcgdHJpcHdpcmVzIG9yIGVuZ2FnaW5nIGluIGVhc2lseSBkZXRlY3RhYmxlLCBhbm9tYWxvdXMgYmVoYXZpb3IuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAyOCI+UGVyc2lzdGVuY2U8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHJlbHkgb24gc3BlY2lmaWMgcmVzb3VyY2VzIHRvIGJlIGVuYWJsZWQsIGFjY2Vzc2libGUsIGFuZC9vciB2dWxuZXJhYmxlLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRoZWlyIG9wZXJhdGlvbnMgYmVpbmcgZGlzcnVwdGVkIGlmIHRoZSByZXNvdXJjZXMgYXJlIGRpc2FibGVkLCByZW1vdmVkLCBvciBvdGhlcndpc2UgbWFkZSBpbnZ1bG5lcmFibGUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNyI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMCI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMyIj5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwNDEiPkV4ZWN1dGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNCI+SW1wYWN0PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDI4Ij5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXRpbGl6ZSBvciBhYnVzZSBzeXN0ZW0gZmVhdHVyZXMsIHNvZnR3YXJlLCBvciBvdGhlciByZXNvdXJjZXMsIHRoZXkgbWF5IGJlIHZ1bG5lcmFibGUgdG8gbW9uaXRvcmluZyBvciBNYW4taW4tdGhlLU1pZGRsZSBtYW5pcHVsYXRpb24uPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAyOSI+UHJpdmlsZWdlIEVzY2FsYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGVuYWJsZWQsIGFjY2Vzc2libGUsIG9yIGludGVudGlvbmFsbHkgd2Vha2VuZWQvb3Zlcmx5IHBlcm1pc3NpdmUgcmVzb3VyY2VzIGluIHRoZSBlbnZpcm9ubWVudCAocHJvZHVjdGlvbiBvciBpc29sYXRlZCksIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gcmV2ZWFsaW5nIGFkZGl0aW9uYWwgb3IgbW9yZSBhZHZhbmNlZCBjYXBhYmlsaXRpZXMgd2hlbiBleHBsb2l0aW5nIG9yIHVzaW5nIHNhaWQgcmVzb3VyY2UuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMiI+RGlzY292ZXJ5PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBhIGRpdmVyc2Ugc2V0IG9mIGFjY2Vzc2libGUgcmVzb3VyY2VzIGFuZCBkZWNveSBhcnRpZmFjdHMgb24gdGhlIHRhcmdldCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzIGFuZCBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5JQ1M8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAwIj5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAyIj5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDMiPkV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDQiPkV4ZWN1dGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNiI+SW1wYWlyIFByb2Nlc3MgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNyI+SW5oaWJpdCBSZXNwb25zZSBGdW5jdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwOCI+SW5pdGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDkiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMTAiPlBlcnNpc3RlbmNlPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTExIj5Qcml2aWxlZ2UgRXNjYWxhdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXRpbGl6ZSBvciBhYnVzZSBzeXN0ZW0gZmVhdHVyZXMsIHNvZnR3YXJlLCBvciBvdGhlciByZXNvdXJjZXMsIHRoZXkgbWF5IGJlIHZ1bG5lcmFibGUgdG8gbW9uaXRvcmluZyBvciBNYW4taW4tdGhlLU1pZGRsZSBtYW5pcHVsYXRpb24uPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwOCI+SW5pdGlhbCBBY2Nlc3M8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIG1vdmUgZGF0YSBhY3Jvc3MgdGhlIG5ldHdvcmsgb3IgaW50ZXJhY3Qgd2l0aCByZW1vdGUgcmVzb3VyY2VzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIG5ldHdvcmsgbWFuaXB1bGF0aW9ucyBzdWNoIGFzIGltcGFjdHMgdG8gbmV0d29yayBhdmFpbGFiaWxpdHksIHRyYWZmaWMgZmlsdGVyaW5nLCBkZWdyYWRlZCBzcGVlZHMsIGV0Yy48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA3Ij5JbmhpYml0IFJlc3BvbnNlIEZ1bmN0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBpbmFjY2Vzc2libGUgYnV0IHBlcmNlaXZlZCBhcyBpbnRlcmVzdGluZyBkYXRhIG9yIGRhdGEgc3RyZWFtcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB3YXN0aW5nIHJlc291cmNlcyBvciByZXZlYWxpbmcgYWRkaXRpb25hbCBjYXBhYmlsaXRpZXMgaW4gYW4gZWZmb3J0IHRvIGFjY2VzcyB0aGUgY29udGVudC48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAwIj5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAyIj5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDciPkluaGliaXQgUmVzcG9uc2UgRnVuY3Rpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGluYWNjZXNzaWJsZSAoYnV0IHBvc3NpYmx5IHZhbHVhYmxlKSBkYXRhIG9yIGRhdGEgc3RyZWFtcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB3YXN0aW5nIHJlc291cmNlcyBvciByZXZlYWxpbmcgYWRkaXRpb25hbCBjYXBhYmlsaXRpZXMgaW4gYW4gZWZmb3J0IHRvIGFjY2VzcyB0aGUgY29udGVudC48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICA8L2Rpdj4KPC9kaXY+CjxkaXYgY2xhc3M9ImV0X3BiX3JvdyBldF9wYl9yb3dfMiBpbmZvcm1hdGlvbi1tYW5pcHVsYXRpb24tZGV0YWlsIG1hdHJpeC1kZXRhaWxzIGV0X3BiX2d1dHRlcnMxIGV0X2hhZF9hbmltYXRpb24iIHN0eWxlPSJkaXNwbGF5OiBub25lOyI+CiAgICA8ZGl2IGNsYXNzPSJldF9wYl9jb2x1bW4gZXRfcGJfY29sdW1uXzRfNCBldF9wYl9jb2x1bW5fNSBldF9wYl9jc3NfbWl4X2JsZW5kX21vZGVfcGFzc3Rocm91Z2ggZXQtbGFzdC1jaGlsZCI+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzAgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8aDQgY2xhc3M9ImV0X3BiX21vZHVsZV9oZWFkZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8c3BhbiBzdHlsZT0iZm9udC1zaXplOiAyMHB4ICFpbXBvcnRhbnQ7bGluZS1oZWlnaHQ6IDEgIWltcG9ydGFudDtmb250LXdlaWdodDogNjAwICFpbXBvcnRhbnQiPkluZm9ybWF0aW9uIE1hbmlwdWxhdGlvbjwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBFQUMwMDE1PC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+Q29uY2VhbCBhbmQgcmV2ZWFsIGJvdGggZmFjdHMgYW5kIGZpY3Rpb25zIHRvIHN1cHBvcnQgYSBkZWNlcHRpb24gc3Rvcnk8L3A+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzEgaW5mb3JtYXRpb24tbWFuaXB1bGF0aW9uLWxvbmctZGVzY3JpcHRpb24gZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5JbmZvcm1hdGlvbiBNYW5pcHVsYXRpb24gaXMgdXNlZCB0byBzdXBwb3J0IHRoZSBlbmdhZ2VtZW50IG5hcnJhdGl2ZSBhbmQgZGlyZWN0bHkgaW1wYWN0IGFkdmVyc2FyeSBhY3Rpdml0aWVzLiBSZXZlYWxlZCBmYWN0cyBhbmQgZmljdGlvbnMgY2FuIGJlIHVzZWQgdG8gYWRqdXN0IHRoZSBhZHZlcnNhcnnigJlzIHRydXN0IGluIHRoZSBlbnZpcm9ubWVudC4gQ29uY2VhbGVkIGZhY3RzIGFuZCBmaWN0aW9uIGNhbiBiZSB1c2VkIHRvIGFkanVzdCB0aGUgYWR2ZXJzYXJ54oCZcyBzZW5zZSBvZiB1bmNlcnRhaW50eSB0b3dhcmRzIHRoZSBlbnZpcm9ubWVudC4gUmV2ZWFsZWQgZmFjdHMgbWF5IGluY2x1ZGUgT1MgdHlwZSBhbmQgdmVyc2lvbiwgZ2VvZ3JhcGhpYyBsb2NhdGlvbiwgaGFyZHdhcmUgdHlwZSBhbmQgdmVyc2lvbiwgYWNjb3VudHMsIGNyZWRlbnRpYWxzLCBldGMuIFJldmVhbGVkIGZpY3Rpb25zIG1heSBpbmNsdWRlIHRoZSBjb250ZW50IG9mIGRlY295IGZpbGVzLCBlbWFpbHMsIG1lc3NhZ2VzLCBldGMuIFJldmVhbGVkIGZhY3RzIGFuZCBmaWN0aW9ucyBtYXkgb3IgbWF5IG5vdCBiZSBiZWxpZXZlZCBieSB0aGUgYWR2ZXJzYXJ5LiAgSWYgYW4gYWR2ZXJzYXJ5IGJlbGlldmVzIGEgcmV2ZWFsZWQgZmFjdCBvciBmaWN0aW9uLCBpdCBtYXkgbGVuZCBjcmVkaWJpbGl0eSB0byB0aGUgZW52aXJvbm1lbnQgb3IgZW5jb3VyYWdlIGEgc3BlY2lmaWMgYWN0aW9uLiBJZiBhbiBhZHZlcnNhcnkgaXMgc3VzcGljaW91cyBvciBkb2VzIG5vdCBiZWxpZXZlIGEgcmV2ZWFsZWQgZmFjdCBvciBmaWN0aW9uLCBpdCBtYXkgZXJvZGUgYWR2ZXJzYXJ5IHRydXN0IGluIHRoZSBlbnZpcm9ubWVudCBvciBkaXNjb3VyYWdlIGEgc3BlY2lmaWMgYWN0aW9uLiBUaGVyZWZvcmUsIHJldmVhbGVkIGZhY3RzIGFuZCBmaWN0aW9ucyBjYW4gYmUgdXNlZCB0byBhZGp1c3QgdGhlIGFkdmVyc2FyeeKAmXMgdHJ1c3QgaW4gdGhlIGVudmlyb25tZW50IGluIHdheXMgdGhhdCBzdXBwb3J0IHRoZSBvcGVyYXRpb25hbCBvYmplY3RpdmVzLiAgPC9wPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+Q29uY2VhbGVkIGZhY3RzIG1heSBpbmNsdWRlIHZpcnR1YWxpemVkIHN5c3RlbXMgZGlzZ3Vpc2VkIGFzIHBoeXNpY2FsIHN5c3RlbXMsIG1vbml0b3Jpbmcgc29mdHdhcmUsIG9yIGNvbGxlY3Rpb24gZWZmb3J0cy4gQ29uY2VhbGVkIGZpY3Rpb25zIG1heSBpbmNsdWRlIGFuIGVuY3J5cHRlZCwgaW50ZXJlc3RpbmdseSBuYW1lZCwgZGVjb3kgZmlsZSBvciBhIHBhcnRpYWxseSBkZWxldGVkIGVtYWlsIHRocmVhZCByZWZlcmVuY2luZyBoaWdoIHZhbHVlLCBidXQgZGVjb3ksIGFzc2V0cy4gQ29uY2VhbGVkIGZhY3RzIGFuZCBmaWN0aW9ucyBtYXkgb3IgbWF5IG5vdCBiZSBkaXNjb3ZlcmVkIGJ5IHRoZSBhZHZlcnNhcnkuIElmIHRoZSBhZHZlcnNhcnkgZGlzY292ZXJzIGEgY29uY2VhbGVkIGZhY3Qgb3IgZmljdGlvbiwgaXQgbWF5IGluY3JlYXNlIHRoZSBhbWJpZ3VpdHkgb2YgdGhlIGVudmlyb25tZW50IGFuZCBhZmZlY3QgdGhlIGFkdmVyc2FyeeKAmXMgc2Vuc2Ugb2YgdW5jZXJ0YWludHkuICBJbiB0aGlzIHdheSwgY29uY2VhbGVkIGZhY3RzIGFuZCBmaWN0aW9ucyBjYW4gYmUgdXNlZCB0byBhZGp1c3QgdGhlIGFtYmlndWl0eSBhbmQgYWZmZWN0IHRoZSBhZHZlcnNhcnnigJlzIHNlbnNlIG9mIHVuY2VydGFpbnR5IGluIHdheXMgdGhhdCBzdXBwb3J0IHRoZSBvcGVyYXRpb25hbCBvYmplY3RpdmVzPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMiBpbmZvcm1hdGlvbi1tYW5pcHVsYXRpb24tcmVmZXJlbmNlcyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InR0YWJsZSB0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBSZWZlcmVuY2UgTGlua3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vZGwuYWNtLm9yZy9kb2kvYWJzLzEwLjExNDUvMzQxODI4OSIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPlVzaW5nIFdvcmQgRW1iZWRkaW5ncyBUbyBEZXRlciBJbnRlbGxlY3R1YWwgUHJvcGVydHkgVGhlZnQgVGhyb3VnaCBBdXRvbWF0ZWQgR2VuZXJhdGlvbiBPZiBGYWtlIERvY3VtZW50czwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cHM6Ly9hcHBzLmR0aWMubWlsL3N0aS9wZGZzL0FEQTUyNzMyOC5wZGYiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5EdXBpbmcgVGhlIFNvdmlldHM6IFRoZSBGYXJld2VsbCBEb3NzaWVyPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL3d3dy5ueXRpbWVzLmNvbS8yMDE3LzA1LzA5L3dvcmxkL2V1cm9wZS9oYWNrZXJzLWNhbWUtYnV0LXRoZS1mcmVuY2gtd2VyZS1wcmVwYXJlZC5odG1sIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+SGFja2VycyBDYW1lIGJ1dCB0aGUgRnJlbmNoIFdlcmUgUHJlcGFyZWQ8L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgaW5mb3JtYXRpb24tbWFuaXB1bGF0aW9uLWF0dGFjay1tYXBwaW5ncyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5FbnRlcnByaXNlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNSI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA3Ij5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDIiPkV4ZWN1dGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MCI+SW1wYWN0PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQzIj5SZWNvbm5haXNzYW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCB0aGUgZW52aXJvbm1lbnQgb3IgcGVyc29uYXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgd2hlbiB0aGV5IGNvbGxlY3QsIG9ic2VydmUsIG9yIG1hbmlwdWxhdGUgc3lzdGVtIGFydGlmYWN0cyBvciBpbmZvcm1hdGlvbi4gTWFuaXB1bGF0ZWQgZGF0YSBtYXkgY2F1c2UgdGhlbSB0byByZXZlYWwgYmVoYXZpb3JzLCB1c2UgYWRkaXRpb25hbCBvciBtb3JlIGFkdmFuY2VkIGNhcGFiaWxpdGllcyBhZ2FpbnN0IHRoZSB0YXJnZXQsIGFuZC9vciBpbXBhY3QgdGhlaXIgZHdlbGwgdGltZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQzIj5SZWNvbm5haXNzYW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgY29sbGVjdCB0YXJnZXRpbmcgaW5mb3JtYXRpb24gZnJvbSBvcGVuIG9yIGNsb3NlZCBkYXRhIHNvdXJjZXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gYmVpbmcgaW5mbHVlbmNlZCBieSBtYW5pcHVsYXRlZCBvciBtaXNsZWFkaW5nIGRhdGEuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNSI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA3Ij5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDIiPkV4ZWN1dGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBlbmdhZ2VtZW50IGVudmlyb25tZW50cyBhbmQgcGVyc29uYXMsIHRoZWlyIGZ1dHVyZSBjYXBhYmlsaXR5LCB0YXJnZXRpbmcsIGFuZC9vciBpbmZyYXN0cnVjdHVyZSByZXF1aXJlbWVudHMgYXJlIHZ1bG5lcmFibGUgdG8gaW5mbHVlbmNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDUiPkRlZmVuc2UgRXZhc2lvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZGlzY292ZXIgZW5hYmxlZCwgYWNjZXNzaWJsZSwgb3IgaW50ZW50aW9uYWxseSB3ZWFrZW5lZC9vdmVybHkgcGVybWlzc2l2ZSByZXNvdXJjZXMgaW4gdGhlIGVudmlyb25tZW50IChwcm9kdWN0aW9uIG9yIGlzb2xhdGVkKSwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgYWRkaXRpb25hbCBvciBtb3JlIGFkdmFuY2VkIGNhcGFiaWxpdGllcyB3aGVuIGV4cGxvaXRpbmcgb3IgdXNpbmcgc2FpZCByZXNvdXJjZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAyIj5FeGVjdXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IGRpcmVjdGx5IHdpdGggdmljdGltcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBiZWluZyBzb2NpYWxseSBlbmdpbmVlcmVkIG9yIG90aGVyd2lzZSBtYW5pcHVsYXRlZCBieSBhbiBhd2FyZSB1c2VyLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDkiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMTEiPkNvbW1hbmQgYW5kIENvbnRyb2w8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDciPkRpc2NvdmVyeTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAxMCI+RXhmaWx0cmF0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQwIj5JbXBhY3Q8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDgiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGEgZGl2ZXJzZSBzZXQgb2YgYWNjZXNzaWJsZSByZXNvdXJjZXMgYW5kIGRlY295IGFydGlmYWN0cyBvbiB0aGUgdGFyZ2V0LCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHJldmVhbGluZyB0aGVpciB0YXJnZXRpbmcgcHJlZmVyZW5jZXMgYW5kIGNhcGFiaWxpdGllcy48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQzIj5SZWNvbm5haXNzYW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgY29sbGVjdCB0YXJnZXRpbmcgaW5mb3JtYXRpb24gZnJvbSBvcGVuIG9yIGNsb3NlZCBkYXRhIHNvdXJjZXMsIHRoZXkgbWF5IHJldmVhbCB0aGVpciB0YXJnZXRpbmcgcHJlZmVyZW5jZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOSI+Q29sbGVjdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgY29sbGVjdCBtYW5pcHVsYXRlZCBhcnRpZmFjdHMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gcmV2ZWFsaW5nIHRoZWlyIHByZXNlbmNlIHdoZW4gdXNpbmcgb3IgbW92aW5nIHRoZSBhcnRpZmFjdHMgZWxzZXdoZXJlIGluIHRoZSBlbmdhZ2VtZW50IGVudmlyb25tZW50LjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+TW9iaWxlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMSI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzAiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMiI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM0Ij5JbXBhY3Q8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggdGhlIGVudmlyb25tZW50IG9yIHBlcnNvbmFzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHdoZW4gdGhleSBjb2xsZWN0LCBvYnNlcnZlLCBvciBtYW5pcHVsYXRlIHN5c3RlbSBhcnRpZmFjdHMgb3IgaW5mb3JtYXRpb24uIE1hbmlwdWxhdGVkIGRhdGEgbWF5IGNhdXNlIHRoZW0gdG8gcmV2ZWFsIGJlaGF2aW9ycywgdXNlIGFkZGl0aW9uYWwgb3IgbW9yZSBhZHZhbmNlZCBjYXBhYmlsaXRpZXMgYWdhaW5zdCB0aGUgdGFyZ2V0LCBhbmQvb3IgaW1wYWN0IHRoZWlyIGR3ZWxsIHRpbWUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMSI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzAiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNCI+SW1wYWN0PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIHRoZSBlbnZpcm9ubWVudCBvciBwZXJzb25hcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBjb2xsZWN0aW5nLCBvciBpbiBzb21lIHdheSBpbnRlcmFjdGluZyB3aXRoLCBtYW5pcHVsYXRlZCBvciBkZWNveSBkYXRhLiBJbiB0aG9zZSBjYXNlcyB0aGUgZGF0YSBtYXkgaW5jcmVhc2UgdGhlaXIgdG9sZXJhbmNlIGZvciBpbXBlcmZlY3Rpb25zIGluIHRoZSBlbnZpcm9ubWVudCBhbmQgaW1wcm92ZSB0aGUgb3ZlcmFsbCBiZWxpZXZhYmlsaXR5IG9mIHRoZSBydXNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzUiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzEiPkNyZWRlbnRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMwIj5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzIiPkRpc2NvdmVyeTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBlbmdhZ2VtZW50IGVudmlyb25tZW50cyBhbmQgcGVyc29uYXMsIHRoZWlyIGZ1dHVyZSBjYXBhYmlsaXR5LCB0YXJnZXRpbmcsIGFuZC9vciBpbmZyYXN0cnVjdHVyZSByZXF1aXJlbWVudHMgYXJlIHZ1bG5lcmFibGUgdG8gaW5mbHVlbmNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzEiPkNyZWRlbnRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyByZWx5IG9uIHNwZWNpZmljIHJlc291cmNlcyB0byBiZSBlbmFibGVkLCBhY2Nlc3NpYmxlLCBhbmQvb3IgdnVsbmVyYWJsZSwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB0aGVpciBvcGVyYXRpb25zIGJlaW5nIGRpc3J1cHRlZCBpZiB0aGUgcmVzb3VyY2VzIGFyZSBkaXNhYmxlZCwgcmVtb3ZlZCwgb3Igb3RoZXJ3aXNlIG1hZGUgaW52dWxuZXJhYmxlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzUiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzIiPkRpc2NvdmVyeTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXRpbGl6ZSBvciBhYnVzZSBzeXN0ZW0gZmVhdHVyZXMsIHNvZnR3YXJlLCBvciBvdGhlciByZXNvdXJjZXMsIHRoZXkgbWF5IGJlIHZ1bG5lcmFibGUgdG8gbW9uaXRvcmluZyBvciBNYW4taW4tdGhlLU1pZGRsZSBtYW5pcHVsYXRpb24uPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNyI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNCI+SW1wYWN0PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCBkaXJlY3RseSB3aXRoIHZpY3RpbXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gYmVpbmcgc29jaWFsbHkgZW5naW5lZXJlZCBvciBvdGhlcndpc2UgbWFuaXB1bGF0ZWQgYnkgYW4gYXdhcmUgdXNlci48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM1Ij5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMyIj5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzYiPkV4ZmlsdHJhdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNCI+SW1wYWN0PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBhIGRpdmVyc2Ugc2V0IG9mIGFjY2Vzc2libGUgcmVzb3VyY2VzIGFuZCBkZWNveSBhcnRpZmFjdHMgb24gdGhlIHRhcmdldCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzIGFuZCBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMSI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGNvbGxlY3QgbWFuaXB1bGF0ZWQgYXJ0aWZhY3RzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHJldmVhbGluZyB0aGVpciBwcmVzZW5jZSB3aGVuIHVzaW5nIG9yIG1vdmluZyB0aGUgYXJ0aWZhY3RzIGVsc2V3aGVyZSBpbiB0aGUgZW5nYWdlbWVudCBlbnZpcm9ubWVudC48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPklDUzwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDAiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDIiPkRpc2NvdmVyeTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNCI+RXhlY3V0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA3Ij5JbmhpYml0IFJlc3BvbnNlIEZ1bmN0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIHRoZSBlbnZpcm9ubWVudCBvciBwZXJzb25hcywgdGhleSBhcmUgdnVsbmVyYWJsZSB3aGVuIHRoZXkgY29sbGVjdCwgb2JzZXJ2ZSwgb3IgbWFuaXB1bGF0ZSBzeXN0ZW0gYXJ0aWZhY3RzIG9yIGluZm9ybWF0aW9uLiBNYW5pcHVsYXRlZCBkYXRhIG1heSBjYXVzZSB0aGVtIHRvIHJldmVhbCBiZWhhdmlvcnMsIHVzZSBhZGRpdGlvbmFsIG9yIG1vcmUgYWR2YW5jZWQgY2FwYWJpbGl0aWVzIGFnYWluc3QgdGhlIHRhcmdldCwgYW5kL29yIGltcGFjdCB0aGVpciBkd2VsbCB0aW1lLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDAiPkNvbGxlY3Rpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGNvbGxlY3QgdGFyZ2V0aW5nIGluZm9ybWF0aW9uIGZyb20gb3BlbiBvciBjbG9zZWQgZGF0YSBzb3VyY2VzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIGJlaW5nIGluZmx1ZW5jZWQgYnkgbWFuaXB1bGF0ZWQgb3IgbWlzbGVhZGluZyBkYXRhLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDAiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDIiPkRpc2NvdmVyeTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNCI+RXhlY3V0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA2Ij5JbXBhaXIgUHJvY2VzcyBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA3Ij5JbmhpYml0IFJlc3BvbnNlIEZ1bmN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA4Ij5Jbml0aWFsIEFjY2VzczwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBlbmdhZ2VtZW50IGVudmlyb25tZW50cyBhbmQgcGVyc29uYXMsIHRoZWlyIGZ1dHVyZSBjYXBhYmlsaXR5LCB0YXJnZXRpbmcsIGFuZC9vciBpbmZyYXN0cnVjdHVyZSByZXF1aXJlbWVudHMgYXJlIHZ1bG5lcmFibGUgdG8gaW5mbHVlbmNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDQiPkV4ZWN1dGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3QgZGlyZWN0bHkgd2l0aCB2aWN0aW1zLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIGJlaW5nIHNvY2lhbGx5IGVuZ2luZWVyZWQgb3Igb3RoZXJ3aXNlIG1hbmlwdWxhdGVkIGJ5IGFuIGF3YXJlIHVzZXIuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMCI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNSI+SW1wYWN0PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA3Ij5JbmhpYml0IFJlc3BvbnNlIEZ1bmN0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBhIGRpdmVyc2Ugc2V0IG9mIGFjY2Vzc2libGUgcmVzb3VyY2VzIGFuZCBkZWNveSBhcnRpZmFjdHMgb24gdGhlIHRhcmdldCwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgdGhlaXIgdGFyZ2V0aW5nIHByZWZlcmVuY2VzIGFuZCBjYXBhYmlsaXRpZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMCI+Q29sbGVjdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgY29sbGVjdCB0YXJnZXRpbmcgaW5mb3JtYXRpb24gZnJvbSBvcGVuIG9yIGNsb3NlZCBkYXRhIHNvdXJjZXMsIHRoZXkgbWF5IHJldmVhbCB0aGVpciB0YXJnZXRpbmcgcHJlZmVyZW5jZXMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgbmV0d29yay1tYW5pcHVsYXRpb24tZGV0YWlsIG1hdHJpeC1kZXRhaWxzIGV0X3BiX2d1dHRlcnMxIGV0X2hhZF9hbmltYXRpb24iIHN0eWxlPSJkaXNwbGF5OiBub25lOyI+CiAgICA8ZGl2IGNsYXNzPSJldF9wYl9jb2x1bW4gZXRfcGJfY29sdW1uXzRfNCBldF9wYl9jb2x1bW5fNSBldF9wYl9jc3NfbWl4X2JsZW5kX21vZGVfcGFzc3Rocm91Z2ggZXQtbGFzdC1jaGlsZCI+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzAgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8aDQgY2xhc3M9ImV0X3BiX21vZHVsZV9oZWFkZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8c3BhbiBzdHlsZT0iZm9udC1zaXplOiAyMHB4ICFpbXBvcnRhbnQ7bGluZS1oZWlnaHQ6IDEgIWltcG9ydGFudDtmb250LXdlaWdodDogNjAwICFpbXBvcnRhbnQiPk5ldHdvcmsgTWFuaXB1bGF0aW9uPC9zcGFuPgogICAgICAgICAgICAgICAgICAgIDwvaDQ+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8aDU+SUQ6IEVBQzAwMTY8L2g1PgogICAgICAgICAgICAgICAgICAgICAgICA8cD5NYWtlIGNoYW5nZXMgdG8gbmV0d29yayBwcm9wZXJ0aWVzIGFuZCBmdW5jdGlvbnMgdG8gYWNoaWV2ZSBhIGRlc2lyZWQgZWZmZWN0LjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBuZXR3b3JrLW1hbmlwdWxhdGlvbi1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+TmV0d29yayBNYW5pcHVsYXRpb24gYWxsb3dzIGEgZGVmZW5kZXIgdG8gdGhyb3R0bGUgbmV0d29yayBzcGVlZHMsIHNlZ21lbnQgdGhlIG5ldHdvcmssIG1haW50YWluIGEgdW5pcXVlIElQIGFkZHJlc3Npbmcgc2NoZW1lLCBhZGQgYSBraWxsIHN3aXRjaCB0byBjdXQgb2ZmIG5ldHdvcmsgYWNjZXNzLCBldGMuIFRoZXNlIHR5cGVzIG9mIG1hbmlwdWxhdGlvbnMgY2FuIGFmZmVjdCB0aGUgYWR2ZXJzYXJ54oCZcyBhYmlsaXR5IHRvIGFjaGlldmUgdGhlaXIgb3BlcmF0aW9uYWwgb2JqZWN0aXZlcyBieSBpbmN1cnJpbmcgYW4gaW5jcmVhc2VkIHJlc291cmNlIGNvc3QsIGZvcmNpbmcgdGhlbSB0byBjaGFuZ2UgdGFjdGljcywgb3Igc3RvcHBpbmcgdGhlbSBhbHRvZ2V0aGVyLiAgRm9yIGV4YW1wbGUsIGEgZGVmZW5kZXIgY2FuIGxpbWl0IHRoZSBhbGxvd2VkIHBvcnRzIG9yIG5ldHdvcmsgcmVxdWVzdHMgdG8gZm9yY2UgdGhlIGFkdmVyc2FyeSB0byBhbHRlciB0aGVpciBwbGFubmVkIEMyIG9yIGV4ZmlsdHJhdGlvbiBjaGFubmVscy4gQXMgYW5vdGhlciBleGFtcGxlLCBhIGRlZmVuZGVyIGNvdWxkIGFsbG93IG9yIGRlbnkgb3V0Ym91bmQgU01CIHJlcXVlc3RzIGZyb20gYSBuZXR3b3JrIHRvIGFmZmVjdCB0aGUgc3VjY2VzcyBvZiBmb3JjZWQgYXV0aGVudGljYXRpb24uIEFkZGl0aW9uYWxseSwgdGhlIGRlZmVuZGVyIGNhbiBkZWdyYWRlIG5ldHdvcmsgc3BlZWRzIGFuZCByZWxpYWJpbGl0eSB0byBpbXBvc2UgYSByZXNvdXJjZSBjb3N0IGFzIGFkdmVyc2FyaWVzIGV4ZmlsdHJhdGUgbGFyZ2UgcXVhbnRpdGllcyBvZiBkYXRhLiBGaW5hbGx5LCBhIGRlZmVuZGVyIGNhbiBibG9jayBwcmltYXJ5IEMyIGRvbWFpbnMgYW5kIElQcyB0byBkZXRlcm1pbmUgaWYgdGhlIGFkdmVyc2FyeSBoYXMgYWRkaXRpb25hbCBpbmZyYXN0cnVjdHVyZS4gV2hpbGUgdGhlcmUgYXJlIGEgcmFuZ2Ugb2YgbmV0d29yayBtYW5pcHVsYXRpb24gb3B0aW9ucywgaW4gYWxsIGNhc2VzLCB0aGUgZGVmZW5kZXIgaGFzIGFuIG9wcG9ydHVuaXR5IHRvIGxlYXJuIGFib3V0IG9yIGluZmx1ZW5jZSB0aGUgYWR2ZXJzYXJpZXMgb3BlcmF0aW5nIGluIHRoZSBlbnZpcm9ubWVudC48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIG5ldHdvcmstbWFuaXB1bGF0aW9uLXJlZmVyZW5jZXMgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0dGFibGUgdGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgUmVmZXJlbmNlIExpbmtzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2RvaS5vcmcvMTAuMTE0NS8zMjY4OTY2LjMyNjg5NzEiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5FbnN1cmluZyBEZWNlcHRpb24gQ29uc2lzdGVuY3kgRm9yIEZUUCBTZXJ2aWNlcyBIYXJkZW5lZCBBZ2FpbnN0IEFkdmFuY2VkIFBlcnNpc3RlbnQgVGhyZWF0czwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cHM6Ly93d3cuYWNhZGVtaWEuZWR1LzQ5NTE5Mjc1L0RFQ0VQVElWRV9ERUNPWVNfQ09NQklOSU5HX0JFTElFVkFCTEVfVVNFUl9BTkRfTkVUV09SS19BQ1RJVklUSUVTX0FORF9ERUNFUFRJVkVfTkVUV09SS19TRVRVUF9JTl9FTkhBTkNJTkdfRUZGRUNUSVZFTkVTUz9mcm9tPWNvdmVyX3BhZ2UiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5EZWNlcHRpdmUgRGVjb3lzOiBDb21iaW5pbmcgQmVsaWV2YWJsZSBVc2VyIGFuZCBOZXR3b3JrIEFjdGl2aXRpZXMgYW5kIERlY2VwdGl2ZSBOZXR3b3JrIFNldHVwIGluIEVuaGFuY2luZyBFZmZlY3RpdmVuZXNzPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2RsLmFjbS5vcmcvZG9pL2Ficy8xMC4xMTQ1LzI5OTU5NTkuMjk5NTk2MiIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPkN5YmVyIERlY2VwdGlvbjogVmlydHVhbCBOZXR3b3JrcyBUbyBEZWZlbmQgSW5zaWRlciBSZWNvbm5haXNzYW5jZTwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cHM6Ly9pZWVleHBsb3JlLmllZWUub3JnL2Fic3RyYWN0L2RvY3VtZW50Lzc5NzE5NDMiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5EZWNlaXZpbmcgTmV0d29yayBSZWNvbm5haXNzYW5jZSBVc2luZyBTRE4tQmFzZWQgVmlydHVhbCBUb3BvbG9naWVzPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2llZWV4cGxvcmUuaWVlZS5vcmcvYWJzdHJhY3QvZG9jdW1lbnQvOTA0NTE2NCIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPkRlY2VwdG9yLUluLVRoZS1NaWRkbGUgKERpdG0pOiBDeWJlciBEZWNlcHRpb24gRm9yIFNlY3VyaXR5IEluIFdpcmVsZXNzIE5ldHdvcmsgVmlydHVhbGl6YXRpb248L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vY2FsaG91bi5ucHMuZWR1L2hhbmRsZS8xMDk0NS80NjM1OCIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPlVuY292ZXJpbmcgTmV0d29yayBUYXJwaXRzIFdpdGggRGVncmVhc2VyPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwOi8vY2V1ci13cy5vcmcvVm9sLTIwODEvcGFwZXIxOS5wZGYiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5IaWRpbmcgQ29tcHV0ZXIgTmV0d29yayBQcm9hY3RpdmUgU2VjdXJpdHkgVG9vbHMgVW5tYXNraW5nIEZlYXR1cmVzPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL3d3dy5vc3RpLmdvdi9iaWJsaW8vMTQ2NjQ4MCIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPk5vdyBZb3UgU2VlIE1lIE5vdyBZb3UgRG9uJiMzOTt0OiBBZHZhbmNpbmcgTmV0d29yayBEZWZlbnNlIFRocm91Z2ggTmV0d29yayBEZWNlcHRpb248L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vY29yZS5hYy51ay9kb3dubG9hZC9wZGYvMzY3MjkwMDIucGRmIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+QSBUZWNobmlxdWUgRm9yIE5ldHdvcmsgVG9wb2xvZ3kgRGVjZXB0aW9uPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIG5ldHdvcmstbWFuaXB1bGF0aW9uLWF0dGFjay1tYXBwaW5ncyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5FbnRlcnByaXNlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOCI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCB0aGUgZW52aXJvbm1lbnQgb3IgcGVyc29uYXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgd2hlbiB0aGV5IGNvbGxlY3QsIG9ic2VydmUsIG9yIG1hbmlwdWxhdGUgc3lzdGVtIGFydGlmYWN0cyBvciBpbmZvcm1hdGlvbi4gTWFuaXB1bGF0ZWQgZGF0YSBtYXkgY2F1c2UgdGhlbSB0byByZXZlYWwgYmVoYXZpb3JzLCB1c2UgYWRkaXRpb25hbCBvciBtb3JlIGFkdmFuY2VkIGNhcGFiaWxpdGllcyBhZ2FpbnN0IHRoZSB0YXJnZXQsIGFuZC9vciBpbXBhY3QgdGhlaXIgZHdlbGwgdGltZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDExIj5Db21tYW5kIGFuZCBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA1Ij5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDIiPkV4ZWN1dGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgcmVseSBvbiBzcGVjaWZpYyByZXNvdXJjZXMgdG8gYmUgZW5hYmxlZCwgYWNjZXNzaWJsZSwgYW5kL29yIHZ1bG5lcmFibGUsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdGhlaXIgb3BlcmF0aW9ucyBiZWluZyBkaXNydXB0ZWQgaWYgdGhlIHJlc291cmNlcyBhcmUgZGlzYWJsZWQsIHJlbW92ZWQsIG9yIG90aGVyd2lzZSBtYWRlIGludnVsbmVyYWJsZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA5Ij5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDExIj5Db21tYW5kIGFuZCBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA2Ij5DcmVkZW50aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNSI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA3Ij5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMTAiPkV4ZmlsdHJhdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MCI+SW1wYWN0PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOCI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwNDMiPlJlY29ubmFpc3NhbmNlPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBtb3ZlIGRhdGEgYWNyb3NzIHRoZSBuZXR3b3JrIG9yIGludGVyYWN0IHdpdGggcmVtb3RlIHJlc291cmNlcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBuZXR3b3JrIG1hbmlwdWxhdGlvbnMgc3VjaCBhcyBpbXBhY3RzIHRvIG5ldHdvcmsgYXZhaWxhYmlsaXR5LCB0cmFmZmljIGZpbHRlcmluZywgZGVncmFkZWQgc3BlZWRzLCBldGMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAxMSI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAxMCI+RXhmaWx0cmF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBleGZpbHRyYXRlIGRhdGEsIHRoZWlyIGRhdGEgYXJlIHZ1bG5lcmFibGUgdG8gb2JzZXJ2YXRpb24gb3IgbWFuaXB1bGF0aW9uIHZpYSBNYW4taW4tdGhlLU1pZGRsZSBhY3Rpdml0aWVzLiA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDExIj5Db21tYW5kIGFuZCBDb250cm9sPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyB1c2UgZWFzaWx5IGlkZW50aWZpYWJsZSB0ZWNobmlxdWVzLCBvciBnZW5lcmF0ZSBzaWduYXR1cmFibGUgcGF0dGVybnMgaW4gZGF0YSBvciB0cmFmZmljLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIGRldGVjdGlvbiBvZiB0aGVpciBhY3Rpdml0eS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDExIj5Db21tYW5kIGFuZCBDb250cm9sPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBhdHRlbXB0IHRvIGV4ZmlsdHJhdGUsIG1hbmlwdWxhdGUsIG9yIG1vdmUgbWFzc2l2ZSBkYXRhIG9iamVjdHMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gd2FzdGluZyByZXNvdXJjZXMgdG8gYWNjb21wbGlzaCB0aGUgdGFzay48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPk1vYmlsZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzIiPkRpc2NvdmVyeTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXRpbGl6ZSBvciBhYnVzZSBzeXN0ZW0gZmVhdHVyZXMsIHNvZnR3YXJlLCBvciBvdGhlciByZXNvdXJjZXMsIHRoZXkgbWF5IGJlIHZ1bG5lcmFibGUgdG8gbW9uaXRvcmluZyBvciBNYW4taW4tdGhlLU1pZGRsZSBtYW5pcHVsYXRpb24uPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMyI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZGlzY292ZXIgZW5hYmxlZCwgYWNjZXNzaWJsZSwgb3IgaW50ZW50aW9uYWxseSB3ZWFrZW5lZC9vdmVybHkgcGVybWlzc2l2ZSByZXNvdXJjZXMgaW4gdGhlIGVudmlyb25tZW50IChwcm9kdWN0aW9uIG9yIGlzb2xhdGVkKSwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgYWRkaXRpb25hbCBvciBtb3JlIGFkdmFuY2VkIGNhcGFiaWxpdGllcyB3aGVuIGV4cGxvaXRpbmcgb3IgdXNpbmcgc2FpZCByZXNvdXJjZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMyIj5EaXNjb3Zlcnk8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGEgZGl2ZXJzZSBzZXQgb2YgYWNjZXNzaWJsZSByZXNvdXJjZXMgYW5kIGRlY295IGFydGlmYWN0cyBvbiB0aGUgdGFyZ2V0LCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHJldmVhbGluZyB0aGVpciB0YXJnZXRpbmcgcHJlZmVyZW5jZXMgYW5kIGNhcGFiaWxpdGllcy48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM1Ij5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM3Ij5Db21tYW5kIGFuZCBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMwIj5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzYiPkV4ZmlsdHJhdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNCI+SW1wYWN0PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBtb3ZlIGRhdGEgYWNyb3NzIHRoZSBuZXR3b3JrIG9yIGludGVyYWN0IHdpdGggcmVtb3RlIHJlc291cmNlcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBuZXR3b3JrIG1hbmlwdWxhdGlvbnMgc3VjaCBhcyBpbXBhY3RzIHRvIG5ldHdvcmsgYXZhaWxhYmlsaXR5LCB0cmFmZmljIGZpbHRlcmluZywgZGVncmFkZWQgc3BlZWRzLCBldGMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNyI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNiI+RXhmaWx0cmF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBleGZpbHRyYXRlIGRhdGEsIHRoZWlyIGRhdGEgYXJlIHZ1bG5lcmFibGUgdG8gb2JzZXJ2YXRpb24gb3IgbWFuaXB1bGF0aW9uIHZpYSBNYW4taW4tdGhlLU1pZGRsZSBhY3Rpdml0aWVzLiA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM3Ij5Db21tYW5kIGFuZCBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMwIj5EZWZlbnNlIEV2YXNpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHVzZSBlYXNpbHkgaWRlbnRpZmlhYmxlIHRlY2huaXF1ZXMsIG9yIGdlbmVyYXRlIHNpZ25hdHVyYWJsZSBwYXR0ZXJucyBpbiBkYXRhIG9yIHRyYWZmaWMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gZGV0ZWN0aW9uIG9mIHRoZWlyIGFjdGl2aXR5LjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzciPkNvbW1hbmQgYW5kIENvbnRyb2w8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGF0dGVtcHQgdG8gZXhmaWx0cmF0ZSwgbWFuaXB1bGF0ZSwgb3IgbW92ZSBtYXNzaXZlIGRhdGEgb2JqZWN0cywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB3YXN0aW5nIHJlc291cmNlcyB0byBhY2NvbXBsaXNoIHRoZSB0YXNrLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+SUNTPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMCI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMSI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMiI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAzIj5FdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA0Ij5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDUiPkltcGFjdDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNiI+SW1wYWlyIFByb2Nlc3MgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNyI+SW5oaWJpdCBSZXNwb25zZSBGdW5jdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwOCI+SW5pdGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDkiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMTAiPlBlcnNpc3RlbmNlPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBtb3ZlIGRhdGEgYWNyb3NzIHRoZSBuZXR3b3JrIG9yIGludGVyYWN0IHdpdGggcmVtb3RlIHJlc291cmNlcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBuZXR3b3JrIG1hbmlwdWxhdGlvbnMgc3VjaCBhcyBpbXBhY3RzIHRvIG5ldHdvcmsgYXZhaWxhYmlsaXR5LCB0cmFmZmljIGZpbHRlcmluZywgZGVncmFkZWQgc3BlZWRzLCBldGMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNSI+SW1wYWN0PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBleGZpbHRyYXRlIGRhdGEsIHRoZWlyIGRhdGEgYXJlIHZ1bG5lcmFibGUgdG8gb2JzZXJ2YXRpb24gb3IgbWFuaXB1bGF0aW9uIHZpYSBNYW4taW4tdGhlLU1pZGRsZSBhY3Rpdml0aWVzLiA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAzIj5FdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA0Ij5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDUiPkltcGFjdDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNiI+SW1wYWlyIFByb2Nlc3MgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNyI+SW5oaWJpdCBSZXNwb25zZSBGdW5jdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwOCI+SW5pdGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMTAiPlBlcnNpc3RlbmNlPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBhdHRlbXB0IHRvIHJlbW90ZWx5IG1hbmlwdWxhdGUsIGRhbWFnZSBvciBlZmZlY3Qgc29tZSBjaGFuZ2UgaW4gdGhlIHBoeXNpY2FsIGVudmlyb25tZW50LCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIE1hbi1pbi10aGUtTWlkZGxlIG1hbmlwdWxhdGlvbnMuIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgIDwvZGl2Pgo8L2Rpdj4KPGRpdiBjbGFzcz0iZXRfcGJfcm93IGV0X3BiX3Jvd18yIGhhcmR3YXJlLW1hbmlwdWxhdGlvbi1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+SGFyZHdhcmUgTWFuaXB1bGF0aW9uPC9zcGFuPgogICAgICAgICAgICAgICAgICAgIDwvaDQ+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8aDU+SUQ6IEVBQzAwMTc8L2g1PgogICAgICAgICAgICAgICAgICAgICAgICA8cD5BbHRlciB0aGUgaGFyZHdhcmUgY29uZmlndXJhdGlvbiBvZiBhIHN5c3RlbSB0byBsaW1pdCB3aGF0IGFuIGFkdmVyc2FyeSBjYW4gZG8gd2l0aCB0aGUgZGV2aWNlLjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBoYXJkd2FyZS1tYW5pcHVsYXRpb24tbG9uZy1kZXNjcmlwdGlvbiBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPkhhcmR3YXJlIE1hbmlwdWxhdGlvbiBjYW4gaW5jbHVkZSBwaHlzaWNhbCBhZGp1c3RtZW50cyBvciBjb25maWd1cmF0aW9uIGNoYW5nZXMgdG8gdGhlIGhhcmR3YXJlIGluIHRoZSBlbnZpcm9ubWVudC4gVGhpcyBtYW5pcHVsYXRpb24gY2FuIGluY2x1ZGUgcGh5c2ljYWxseSByZW1vdmluZyBhIHN5c3RlbeKAmXMgbWljcm9waG9uZSwgY2FtZXJhLCBvbi1ib2FyZCBXaS1GaSBhZGFwdGVyLCBldGMuIG9yIHVzaW5nIHNvZnR3YXJlIGNvbnRyb2xzIHRvIGRpc2FibGUgdGhvc2UgZGV2aWNlcy4gVGhlc2UgdHlwZXMgb2YgbWFuaXB1bGF0aW9ucyBjYW4gYWZmZWN0IHRoZSBhZHZlcnNhcnnigJlzIGFiaWxpdHkgdG8gYWNoaWV2ZSB0aGVpciBvcGVyYXRpb25hbCBvYmplY3RpdmVzIGJ5IGluY3VycmluZyBhbiBpbmNyZWFzZWQgcmVzb3VyY2UgY29zdCwgZm9yY2luZyB0aGVtIHRvIGNoYW5nZSB0YWN0aWNzLCBvciBzdG9wcGluZyB0aGVtIGFsdG9nZXRoZXIuICBIYXJkd2FyZSBNYW5pcHVsYXRpb24gaXMgb2Z0ZW4gcmVxdWlyZWQgdG8gbWFpbnRhaW4gb3BlcmF0aW9uYWwgc2FmZXR5LiBGb3IgZXhhbXBsZSwgaWYgdGhlIG9wZXJhdGlvbiBpbmNsdWRlcyBNYWx3YXJlIERldG9uYXRpb24gdXNpbmcgYSBsYXB0b3AgcGh5c2ljYWxseSBsb2NhdGVkIGluIGEgc2hhcmVkIHNwYWNlLCBpdCBpcyBsaWtlbHkgdGhhdCB0aGUgZGVmZW5kZXIgd2lsbCBub3QgaGF2ZSB0aGUgYWJpbGl0eSB0byBoaWRlIHRoZSBsZWdpdGltYXRlIGNvbnZlcnNhdGlvbnMgYW5kIGluZGl2aWR1YWxzIHByZXNlbnQgaW4gdGhlIHNwYWNlLiBVbmxlc3MgdGhlIGRlZmVuZGVyIGNhbiBjb250cm9sIHRoZSBiYWNrZ3JvdW5kIHNvdW5kcyBhbmQgdmlzdWFscywgaXQgaXMgbGlrZWx5IHRvbyByaXNreSB0byBsZWF2ZSB0aGUgY2FtZXJhIGFuZCBtaWNyb3Bob25lIGNvbm5lY3RlZCB0byB0aGUgbWFjaGluZS48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIGhhcmR3YXJlLW1hbmlwdWxhdGlvbi1yZWZlcmVuY2VzIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idHRhYmxlIHRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIFJlZmVyZW5jZSBMaW5rcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cHM6Ly9ib29rcy5nb29nbGUuY29tL2Jvb2tzP2hsPWVuJmFtcDtscj0mYW1wO2lkPXVZaVJEZ0FBUUJBSiZhbXA7b2k9Zm5kJmFtcDtwZz1QQTE5NCZhbXA7b3RzPWdMUl9HLTlkYkEmYW1wO3NpZz1RU0oyTnhjV3FCZmhaWHB1TTh4MjNyMUFBZzgjdj1vbmVwYWdlJmFtcDtxJmFtcDtmPWZhbHNlIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+Q3liZXIgRGVjZXB0aW9uIFZpYSBTeXN0ZW0gTWFuaXB1bGF0aW9uPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIGhhcmR3YXJlLW1hbmlwdWxhdGlvbi1hdHRhY2stbWFwcGluZ3MgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+RW50ZXJwcmlzZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDkiPkNvbGxlY3Rpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHJlbHkgb24gc3BlY2lmaWMgcmVzb3VyY2VzIHRvIGJlIGVuYWJsZWQsIGFjY2Vzc2libGUsIGFuZC9vciB2dWxuZXJhYmxlLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRoZWlyIG9wZXJhdGlvbnMgYmVpbmcgZGlzcnVwdGVkIGlmIHRoZSByZXNvdXJjZXMgYXJlIGRpc2FibGVkLCByZW1vdmVkLCBvciBvdGhlcndpc2UgbWFkZSBpbnZ1bG5lcmFibGUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5Nb2JpbGU8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM1Ij5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDI4Ij5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgcmVseSBvbiBzcGVjaWZpYyByZXNvdXJjZXMgdG8gYmUgZW5hYmxlZCwgYWNjZXNzaWJsZSwgYW5kL29yIHZ1bG5lcmFibGUsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdGhlaXIgb3BlcmF0aW9ucyBiZWluZyBkaXNydXB0ZWQgaWYgdGhlIHJlc291cmNlcyBhcmUgZGlzYWJsZWQsIHJlbW92ZWQsIG9yIG90aGVyd2lzZSBtYWRlIGludnVsbmVyYWJsZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPklDUzwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDAiPkNvbGxlY3Rpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHJlbHkgb24gc3BlY2lmaWMgcmVzb3VyY2VzIHRvIGJlIGVuYWJsZWQsIGFjY2Vzc2libGUsIGFuZC9vciB2dWxuZXJhYmxlLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRoZWlyIG9wZXJhdGlvbnMgYmVpbmcgZGlzcnVwdGVkIGlmIHRoZSByZXNvdXJjZXMgYXJlIGRpc2FibGVkLCByZW1vdmVkLCBvciBvdGhlcndpc2UgbWFkZSBpbnZ1bG5lcmFibGUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgc2VjdXJpdHktY29udHJvbHMtZGV0YWlsIG1hdHJpeC1kZXRhaWxzIGV0X3BiX2d1dHRlcnMxIGV0X2hhZF9hbmltYXRpb24iIHN0eWxlPSJkaXNwbGF5OiBub25lOyI+CiAgICA8ZGl2IGNsYXNzPSJldF9wYl9jb2x1bW4gZXRfcGJfY29sdW1uXzRfNCBldF9wYl9jb2x1bW5fNSBldF9wYl9jc3NfbWl4X2JsZW5kX21vZGVfcGFzc3Rocm91Z2ggZXQtbGFzdC1jaGlsZCI+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzAgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8aDQgY2xhc3M9ImV0X3BiX21vZHVsZV9oZWFkZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8c3BhbiBzdHlsZT0iZm9udC1zaXplOiAyMHB4ICFpbXBvcnRhbnQ7bGluZS1oZWlnaHQ6IDEgIWltcG9ydGFudDtmb250LXdlaWdodDogNjAwICFpbXBvcnRhbnQiPlNlY3VyaXR5IENvbnRyb2xzPC9zcGFuPgogICAgICAgICAgICAgICAgICAgIDwvaDQ+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8aDU+SUQ6IEVBQzAwMTg8L2g1PgogICAgICAgICAgICAgICAgICAgICAgICA8cD5BbHRlciBzZWN1cml0eSBjb250cm9scyB0byBtYWtlIHRoZSBzeXN0ZW0gbW9yZSBvciBsZXNzIHZ1bG5lcmFibGUgdG8gYXR0YWNrLjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBzZWN1cml0eS1jb250cm9scy1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+TWFuaXB1bGF0aW5nIFNlY3VyaXR5IENvbnRyb2xzIGludm9sdmVzIG1ha2luZyBjb25maWd1cmF0aW9uIGNoYW5nZXMgdG8gYSBzeXN0ZW3igJlzIHNlY3VyaXR5IHNldHRpbmdzIGluY2x1ZGluZyBtb2RpZnlpbmcgR3JvdXAgUG9saWNpZXMsIGRpc2FibGluZy9lbmFibGluZyBhdXRvcnVuIGZvciByZW1vdmFibGUgbWVkaWEsIHRpZ2h0ZW5pbmcgb3IgcmVsYXhpbmcgc3lzdGVtIGZpcmV3YWxscywgZXRjLiBTdWNoIHNlY3VyaXR5IGNvbnRyb2xzIGNhbiBiZSB0aWdodGVuZWQgdG8gZGlzc3VhZGUgb3IgcHJldmVudCBhZHZlcnNhcnkgYWN0aXZpdHkuIENvbnZlcnNlbHksIHNlY3VyaXR5IGNvbnRyb2xzIGNhbiBiZSB3ZWFrZW5lZCBvciBsZWZ0IG92ZXJseSBwZXJtaXNzaXZlIHRvIGVuY291cmFnZSBvciBlbmFibGUgYWR2ZXJzYXJ5IGFjdGl2aXR5LiAgVGlnaHRlbmluZyBzZWN1cml0eSBjb250cm9scyBjYW4gdHlwaWNhbGx5IGJlIGRvbmUgYnkgaW1wbGVtZW50aW5nIGFueSBvZiB0aGUgbWl0aWdhdGlvbnMgZGVzY3JpYmVkIGluIE1JVFJFIEFUVCZhbXA7Q0suIFNlZSBodHRwczovL2F0dGFjay5taXRyZS5vcmcvbWl0aWdhdGlvbnMvZW50ZXJwcmlzZS8gZm9yIGEgZnVsbCBsaXN0IG9mIG1pdGlnYXRpb24gc3RyYXRlZ2llcy4gV2hpbGUgbG9vc2VuaW5nIHNlY3VyaXR5IGNvbnRyb2xzIG1heSBzZWVtIG9idmlvdXMgKGkuZS4sIHNpbXBseSBkb27igJl0IGVtcGxveSBhIGdpdmVuIG1pdGlnYXRpb24gc3RyYXRlZ3kpLCB0aGVyZSBpcyBhbiBhZGRpdGlvbmFsIGxldmVsIG9mIG51YW5jZSB0aGF0IG11c3QgYmUgY29uc2lkZXJlZC4gU29tZSBzZWN1cml0eSBjb250cm9scyBhcmUgY29uc2lkZXJlZCBzbyByb3V0aW5lIHRoYXQgaXRzIGFic2VuY2UgbWF5IGJlIHN1c3BpY2lvdXMuICBGb3IgZXhhbXBsZSwgY29tcGxldGVseSB0dXJuaW5nIG9mZiBXaW5kb3dzIERlZmVuZGVyIHdvdWxkIGxpa2VseSByYWlzZSB0aGUgYWR2ZXJzYXJ54oCZcyBzdXNwaWNpb24uIEhvd2V2ZXIsIGl0IGlzIHBvc3NpYmxlIHRvIHR1cm4gb2ZmIFdpbmRvd3MgRGVmZW5kZXIgaW4gY2VydGFpbiBzaGFyZWQgZHJpdmVzIHRvIGVuY291cmFnZSBhZHZlcnNhcnkgYWN0aXZpdHkgaW4gcHJlZGV0ZXJtaW5lZCBsb2NhdGlvbnMuIFRoZXJlZm9yZSwgaXQgd2lsbCBsaWtlbHkgYmUgZmFyIGxlc3Mgc3VzcGljaW91cyB0byB0dXJuIG9mZiBXaW5kb3dzIERlZmVuZGVyIGluIGEgc2luZ2xlIGRpcmVjdG9yeSBvciBzaGFyZS4gV2hlbiBhc3Nlc3NpbmcgdGhlIGxpa2VsaWhvb2QgdGhhdCByZW1vdmluZyBhIGdpdmVuIHNlY3VyaXR5IGNvbnRyb2wgaXMgb3Zlcmx5IHN1c3BpY2lvdXMsIGl0IGlzIGltcG9ydGFudCB0byBjb25zaWRlciBob3cgcHJldmFsZW50IHRoYXQgc2VjdXJpdHkgY29udHJvbCBpcywgdGhlIHRhcmdldCBhZHZlcnNhcnnigJlzIHNvcGhpc3RpY2F0aW9uLCBhbmQgdGhlIGVuZ2FnZW1lbnQgbmFycmF0aXZlLjwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgc2VjdXJpdHktY29udHJvbHMtcmVmZXJlbmNlcyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InR0YWJsZSB0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBSZWZlcmVuY2UgTGlua3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vZGwuYWNtLm9yZy9kb2kvYWJzLzEwLjExNDUvMjgxODAwMC4yODE4MDE1IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+RXJzYXR6cGFzc3dvcmRzOiBFbmRpbmcgUGFzc3dvcmQgQ3JhY2tpbmcgQW5kIERldGVjdGluZyBQYXNzd29yZCBMZWFrYWdlPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2RsLmFjbS5vcmcvZG9pL2Ficy8xMC4xMTQ1LzI2NjAyNjcuMjY2MDMyOSIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPkZyb20gUGF0Y2hlcyBUbyBIb25leS1QYXRjaGVzOiBMaWdodHdlaWdodCBBdHRhY2tlciBNaXNkaXJlY3Rpb24sIERlY2VwdGlvbiwgQW5kIERpc2luZm9ybWF0aW9uPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwOi8vaXN5b3UuaW5mby9qaXNpcy92b2w1L25vMy9qaXNpcy0yMDE1LXZvbDUtbm8zLTAyLnBkZiIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPlRvd2FyZCBBbiBJbnNpZGVyIFRocmVhdCBEZXRlY3Rpb24gRnJhbWV3b3JrIFVzaW5nIEhvbmV5IFBlcm1pc3Npb25zPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIHNlY3VyaXR5LWNvbnRyb2xzLWF0dGFjay1tYXBwaW5ncyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5FbnRlcnByaXNlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNCI+UHJpdmlsZWdlIEVzY2FsYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggdGhlIGVudmlyb25tZW50IG9yIHBlcnNvbmFzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHdoZW4gdGhleSBjb2xsZWN0LCBvYnNlcnZlLCBvciBtYW5pcHVsYXRlIHN5c3RlbSBhcnRpZmFjdHMgb3IgaW5mb3JtYXRpb24uIE1hbmlwdWxhdGVkIGRhdGEgbWF5IGNhdXNlIHRoZW0gdG8gcmV2ZWFsIGJlaGF2aW9ycywgdXNlIGFkZGl0aW9uYWwgb3IgbW9yZSBhZHZhbmNlZCBjYXBhYmlsaXRpZXMgYWdhaW5zdCB0aGUgdGFyZ2V0LCBhbmQvb3IgaW1wYWN0IHRoZWlyIGR3ZWxsIHRpbWUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAxMSI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNiI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDUiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMiI+RXhlY3V0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOCI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDQiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyByZWx5IG9uIHNwZWNpZmljIHJlc291cmNlcyB0byBiZSBlbmFibGVkLCBhY2Nlc3NpYmxlLCBhbmQvb3IgdnVsbmVyYWJsZSwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB0aGVpciBvcGVyYXRpb25zIGJlaW5nIGRpc3J1cHRlZCBpZiB0aGUgcmVzb3VyY2VzIGFyZSBkaXNhYmxlZCwgcmVtb3ZlZCwgb3Igb3RoZXJ3aXNlIG1hZGUgaW52dWxuZXJhYmxlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDIiPkV4ZWN1dGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDQiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyB1dGlsaXplIG9yIGFidXNlIHN5c3RlbSBmZWF0dXJlcywgc29mdHdhcmUsIG9yIG90aGVyIHJlc291cmNlcywgdGhleSBtYXkgYmUgdnVsbmVyYWJsZSB0byBtb25pdG9yaW5nIG9yIE1hbi1pbi10aGUtTWlkZGxlIG1hbmlwdWxhdGlvbi48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA5Ij5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA2Ij5DcmVkZW50aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNSI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA3Ij5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDIiPkV4ZWN1dGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MCI+SW1wYWN0PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOCI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDQiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBlbmFibGVkLCBhY2Nlc3NpYmxlLCBvciBpbnRlbnRpb25hbGx5IHdlYWtlbmVkL292ZXJseSBwZXJtaXNzaXZlIHJlc291cmNlcyBpbiB0aGUgZW52aXJvbm1lbnQgKHByb2R1Y3Rpb24gb3IgaXNvbGF0ZWQpLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHJldmVhbGluZyBhZGRpdGlvbmFsIG9yIG1vcmUgYWR2YW5jZWQgY2FwYWJpbGl0aWVzIHdoZW4gZXhwbG9pdGluZyBvciB1c2luZyBzYWlkIHJlc291cmNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDYiPkNyZWRlbnRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBtb3ZlIGRhdGEgYWNyb3NzIHRoZSBuZXR3b3JrIG9yIGludGVyYWN0IHdpdGggcmVtb3RlIHJlc291cmNlcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byBuZXR3b3JrIG1hbmlwdWxhdGlvbnMgc3VjaCBhcyBpbXBhY3RzIHRvIG5ldHdvcmsgYXZhaWxhYmlsaXR5LCB0cmFmZmljIGZpbHRlcmluZywgZGVncmFkZWQgc3BlZWRzLCBldGMuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNSI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDEwIj5FeGZpbHRyYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGluYWNjZXNzaWJsZSBidXQgcGVyY2VpdmVkIGFzIGludGVyZXN0aW5nIGRhdGEgb3IgZGF0YSBzdHJlYW1zLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHdhc3RpbmcgcmVzb3VyY2VzIG9yIHJldmVhbGluZyBhZGRpdGlvbmFsIGNhcGFiaWxpdGllcyBpbiBhbiBlZmZvcnQgdG8gYWNjZXNzIHRoZSBjb250ZW50LjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+TW9iaWxlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMCI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM0Ij5JbXBhY3Q8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggdGhlIGVudmlyb25tZW50IG9yIHBlcnNvbmFzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHdoZW4gdGhleSBjb2xsZWN0LCBvYnNlcnZlLCBvciBtYW5pcHVsYXRlIHN5c3RlbSBhcnRpZmFjdHMgb3IgaW5mb3JtYXRpb24uIE1hbmlwdWxhdGVkIGRhdGEgbWF5IGNhdXNlIHRoZW0gdG8gcmV2ZWFsIGJlaGF2aW9ycywgdXNlIGFkZGl0aW9uYWwgb3IgbW9yZSBhZHZhbmNlZCBjYXBhYmlsaXRpZXMgYWdhaW5zdCB0aGUgdGFyZ2V0LCBhbmQvb3IgaW1wYWN0IHRoZWlyIGR3ZWxsIHRpbWUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNSI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNyI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMSI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzAiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MSI+RXhlY3V0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM0Ij5JbXBhY3Q8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMjciPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMzIj5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDI4Ij5QZXJzaXN0ZW5jZTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAyOSI+UHJpdmlsZWdlIEVzY2FsYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHJlbHkgb24gc3BlY2lmaWMgcmVzb3VyY2VzIHRvIGJlIGVuYWJsZWQsIGFjY2Vzc2libGUsIGFuZC9vciB2dWxuZXJhYmxlLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRoZWlyIG9wZXJhdGlvbnMgYmVpbmcgZGlzcnVwdGVkIGlmIHRoZSByZXNvdXJjZXMgYXJlIGRpc2FibGVkLCByZW1vdmVkLCBvciBvdGhlcndpc2UgbWFkZSBpbnZ1bG5lcmFibGUuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MSI+RXhlY3V0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyB1dGlsaXplIG9yIGFidXNlIHN5c3RlbSBmZWF0dXJlcywgc29mdHdhcmUsIG9yIG90aGVyIHJlc291cmNlcywgdGhleSBtYXkgYmUgdnVsbmVyYWJsZSB0byBtb25pdG9yaW5nIG9yIE1hbi1pbi10aGUtTWlkZGxlIG1hbmlwdWxhdGlvbi48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM1Ij5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM3Ij5Db21tYW5kIGFuZCBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMwIj5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwNDEiPkV4ZWN1dGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNCI+SW1wYWN0PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMzIj5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDI4Ij5QZXJzaXN0ZW5jZTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAyOSI+UHJpdmlsZWdlIEVzY2FsYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGVuYWJsZWQsIGFjY2Vzc2libGUsIG9yIGludGVudGlvbmFsbHkgd2Vha2VuZWQvb3Zlcmx5IHBlcm1pc3NpdmUgcmVzb3VyY2VzIGluIHRoZSBlbnZpcm9ubWVudCAocHJvZHVjdGlvbiBvciBpc29sYXRlZCksIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gcmV2ZWFsaW5nIGFkZGl0aW9uYWwgb3IgbW9yZSBhZHZhbmNlZCBjYXBhYmlsaXRpZXMgd2hlbiBleHBsb2l0aW5nIG9yIHVzaW5nIHNhaWQgcmVzb3VyY2UuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNiI+RXhmaWx0cmF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBpbmFjY2Vzc2libGUgYnV0IHBlcmNlaXZlZCBhcyBpbnRlcmVzdGluZyBkYXRhIG9yIGRhdGEgc3RyZWFtcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB3YXN0aW5nIHJlc291cmNlcyBvciByZXZlYWxpbmcgYWRkaXRpb25hbCBjYXBhYmlsaXRpZXMgaW4gYW4gZWZmb3J0IHRvIGFjY2VzcyB0aGUgY29udGVudC48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPklDUzwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDciPkluaGliaXQgUmVzcG9uc2UgRnVuY3Rpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggbmV0d29yayBvciBzeXN0ZW0gcmVzb3VyY2VzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRyaWdnZXJpbmcgdHJpcHdpcmVzIG9yIGVuZ2FnaW5nIGluIGVhc2lseSBkZXRlY3RhYmxlLCBhbm9tYWxvdXMgYmVoYXZpb3IuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMCI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMyI+RXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNCI+RXhlY3V0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA2Ij5JbXBhaXIgUHJvY2VzcyBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA3Ij5JbmhpYml0IFJlc3BvbnNlIEZ1bmN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA4Ij5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwOSI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDExMCI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMTEiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyByZWx5IG9uIHNwZWNpZmljIHJlc291cmNlcyB0byBiZSBlbmFibGVkLCBhY2Nlc3NpYmxlLCBhbmQvb3IgdnVsbmVyYWJsZSwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB0aGVpciBvcGVyYXRpb25zIGJlaW5nIGRpc3J1cHRlZCBpZiB0aGUgcmVzb3VyY2VzIGFyZSBkaXNhYmxlZCwgcmVtb3ZlZCwgb3Igb3RoZXJ3aXNlIG1hZGUgaW52dWxuZXJhYmxlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDAiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDMiPkV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDQiPkV4ZWN1dGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNSI+SW1wYWN0PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA2Ij5JbXBhaXIgUHJvY2VzcyBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA3Ij5JbmhpYml0IFJlc3BvbnNlIEZ1bmN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA4Ij5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwOSI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDExMCI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMTEiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBlbmFibGVkLCBhY2Nlc3NpYmxlLCBvciBpbnRlbnRpb25hbGx5IHdlYWtlbmVkL292ZXJseSBwZXJtaXNzaXZlIHJlc291cmNlcyBpbiB0aGUgZW52aXJvbm1lbnQgKHByb2R1Y3Rpb24gb3IgaXNvbGF0ZWQpLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHJldmVhbGluZyBhZGRpdGlvbmFsIG9yIG1vcmUgYWR2YW5jZWQgY2FwYWJpbGl0aWVzIHdoZW4gZXhwbG9pdGluZyBvciB1c2luZyBzYWlkIHJlc291cmNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDAiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDUiPkltcGFjdDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZGlzY292ZXIgaW5hY2Nlc3NpYmxlIGJ1dCBwZXJjZWl2ZWQgYXMgaW50ZXJlc3RpbmcgZGF0YSBvciBkYXRhIHN0cmVhbXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gd2FzdGluZyByZXNvdXJjZXMgb3IgcmV2ZWFsaW5nIGFkZGl0aW9uYWwgY2FwYWJpbGl0aWVzIGluIGFuIGVmZm9ydCB0byBhY2Nlc3MgdGhlIGNvbnRlbnQuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgYmFzZWxpbmUtZGV0YWlsIG1hdHJpeC1kZXRhaWxzIGV0X3BiX2d1dHRlcnMxIGV0X2hhZF9hbmltYXRpb24iIHN0eWxlPSJkaXNwbGF5OiBub25lOyI+CiAgICA8ZGl2IGNsYXNzPSJldF9wYl9jb2x1bW4gZXRfcGJfY29sdW1uXzRfNCBldF9wYl9jb2x1bW5fNSBldF9wYl9jc3NfbWl4X2JsZW5kX21vZGVfcGFzc3Rocm91Z2ggZXQtbGFzdC1jaGlsZCI+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzAgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8aDQgY2xhc3M9ImV0X3BiX21vZHVsZV9oZWFkZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8c3BhbiBzdHlsZT0iZm9udC1zaXplOiAyMHB4ICFpbXBvcnRhbnQ7bGluZS1oZWlnaHQ6IDEgIWltcG9ydGFudDtmb250LXdlaWdodDogNjAwICFpbXBvcnRhbnQiPkJhc2VsaW5lPC9zcGFuPgogICAgICAgICAgICAgICAgICAgIDwvaDQ+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8aDU+SUQ6IEVBQzAwMTk8L2g1PgogICAgICAgICAgICAgICAgICAgICAgICA8cD5JZGVudGlmeSBrZXkgc3lzdGVtIGVsZW1lbnRzIHRvIGVzdGFibGlzaCBhIGJhc2VsaW5lIGFuZCBiZSBwcmVwYXJlZCB0byByZXNldCBhIHN5c3RlbSB0byB0aGF0IGJhc2VsaW5lIHdoZW4gbmVjZXNzYXJ5LjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBiYXNlbGluZS1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+VG8gZGV0ZXJtaW5lIHRoZSBzeXN0ZW0gQmFzZWxpbmUsIHRoZSBkZWZlbmRlciBtdXN0IGlkZW50aWZ5IHNvZnR3YXJlIGFuZCBjb25maWd1cmF0aW9uIGVsZW1lbnRzIHRoYXQgYXJlIGNyaXRpY2FsIHRvIGEgc2V0IG9mIG9iamVjdGl2ZXMuIFRoZSBkZWZlbmRlciBtdXN0IGRlZmluZSB0aGUgcHJvcGVyIHZhbHVlcyBhbmQgYmUgcHJlcGFyZWQgdG8gcmVzZXQgYSBydW5uaW5nIHN5c3RlbSB0byBpdHMgaW50ZW5kZWQgc3RhdGUuIFJldmVydGluZyB0byBhIEJhc2VsaW5lIGNvbmZpZ3VyYXRpb24gY2FuIGJlIGVzc2VudGlhbCB3aGVuIHJlc3RvcmluZyBhbiBvcGVyYXRpb25hbCBlbnZpcm9ubWVudCB0byBhIHNhZmUgc3RhdGUgb3Igd2hlbiBsb29raW5nIHRvIGltcG9zZSBhIGNvc3Qgb24gYWR2ZXJzYXJpZXMgYnkgcHJldmVudGluZyB0aGVpciBhY3Rpdml0eS4gIEZvciBleGFtcGxlLCB0aGUgZGVmZW5kZXIgY2FuIHdhdGNoIGZvciBhbiBhZHZlcnNhcnkgdG8gbWFrZSBjaGFuZ2VzIGluIHRoZSBlbnZpcm9ubWVudCBhbmQgdGhlbiByZXZlcnQgdGhlIGVudmlyb25tZW50IHdpdGggdGhlIGdvYWwgb2YgZWl0aGVyIGZvcmNpbmcgdGhlIGFkdmVyc2FyeSB0byB0YXJnZXQgZWxzZXdoZXJlIGluIHRoZSBuZXR3b3JrIG9yIHRvIGRpc3BsYXkgYSBuZXcsIHBvc3NpYmx5IG1vcmUgYWR2YW5jZWQsIFRUUC4gVGhlIEJhc2VsaW5lIHZhbHVlcyB3aWxsIGFsc28gYmUgY3J1Y2lhbCBwb3N0LW9wZXJhdGlvbiB3aGVuIGFuYWx5emluZyBjaGFuZ2VzIHRvIHRoZSBlbnZpcm9ubWVudCBvdmVyIHRpbWUuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMiBiYXNlbGluZS1hdHRhY2stbWFwcGluZ3MgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+RW50ZXJwcmlzZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwNDAiPkltcGFjdDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXPigJkgbWFsd2FyZSBpcyBkZXRvbmF0ZWQsIHRoZXkgbWF5IGJlIGVuY291cmFnZWQgdG8gb3BlcmF0ZSBpbiBhbiB1bmludGVuZGVkIGVudmlyb25tZW50LjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDUiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MCI+SW1wYWN0PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIG5ldHdvcmsgb3Igc3lzdGVtIHJlc291cmNlcywgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB0cmlnZ2VyaW5nIHRyaXB3aXJlcyBvciBlbmdhZ2luZyBpbiBlYXNpbHkgZGV0ZWN0YWJsZSwgYW5vbWFsb3VzIGJlaGF2aW9yLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDUiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDQiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyByZWx5IG9uIHNwZWNpZmljIHJlc291cmNlcyB0byBiZSBlbmFibGVkLCBhY2Nlc3NpYmxlLCBhbmQvb3IgdnVsbmVyYWJsZSwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB0aGVpciBvcGVyYXRpb25zIGJlaW5nIGRpc3J1cHRlZCBpZiB0aGUgcmVzb3VyY2VzIGFyZSBkaXNhYmxlZCwgcmVtb3ZlZCwgb3Igb3RoZXJ3aXNlIG1hZGUgaW52dWxuZXJhYmxlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwNDAiPkltcGFjdDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXRpbGl6ZSBvciBhYnVzZSBzeXN0ZW0gZmVhdHVyZXMsIHNvZnR3YXJlLCBvciBvdGhlciByZXNvdXJjZXMsIHRoZXkgbWF5IGJlIHZ1bG5lcmFibGUgdG8gbW9uaXRvcmluZyBvciBNYW4taW4tdGhlLU1pZGRsZSBtYW5pcHVsYXRpb24uPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5Nb2JpbGU8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMwIj5EZWZlbnNlIEV2YXNpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMjgiPlBlcnNpc3RlbmNlPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyByZWx5IG9uIHNwZWNpZmljIHJlc291cmNlcyB0byBiZSBlbmFibGVkLCBhY2Nlc3NpYmxlLCBhbmQvb3IgdnVsbmVyYWJsZSwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB0aGVpciBvcGVyYXRpb25zIGJlaW5nIGRpc3J1cHRlZCBpZiB0aGUgcmVzb3VyY2VzIGFyZSBkaXNhYmxlZCwgcmVtb3ZlZCwgb3Igb3RoZXJ3aXNlIG1hZGUgaW52dWxuZXJhYmxlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+SUNTPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMyI+RXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNyI+SW5oaWJpdCBSZXNwb25zZSBGdW5jdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgcmVseSBvbiBzcGVjaWZpYyByZXNvdXJjZXMgdG8gYmUgZW5hYmxlZCwgYWNjZXNzaWJsZSwgYW5kL29yIHZ1bG5lcmFibGUsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdGhlaXIgb3BlcmF0aW9ucyBiZWluZyBkaXNydXB0ZWQgaWYgdGhlIHJlc291cmNlcyBhcmUgZGlzYWJsZWQsIHJlbW92ZWQsIG9yIG90aGVyd2lzZSBtYWRlIGludnVsbmVyYWJsZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICA8L2Rpdj4KPC9kaXY+CjxkaXYgY2xhc3M9ImV0X3BiX3JvdyBldF9wYl9yb3dfMiBpc29sYXRpb24tZGV0YWlsIG1hdHJpeC1kZXRhaWxzIGV0X3BiX2d1dHRlcnMxIGV0X2hhZF9hbmltYXRpb24iIHN0eWxlPSJkaXNwbGF5OiBub25lOyI+CiAgICA8ZGl2IGNsYXNzPSJldF9wYl9jb2x1bW4gZXRfcGJfY29sdW1uXzRfNCBldF9wYl9jb2x1bW5fNSBldF9wYl9jc3NfbWl4X2JsZW5kX21vZGVfcGFzc3Rocm91Z2ggZXQtbGFzdC1jaGlsZCI+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzAgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8aDQgY2xhc3M9ImV0X3BiX21vZHVsZV9oZWFkZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8c3BhbiBzdHlsZT0iZm9udC1zaXplOiAyMHB4ICFpbXBvcnRhbnQ7bGluZS1oZWlnaHQ6IDEgIWltcG9ydGFudDtmb250LXdlaWdodDogNjAwICFpbXBvcnRhbnQiPklzb2xhdGlvbjwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBFQUMwMDIwPC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+Q29uZmlndXJlIGRldmljZXMsIHN5c3RlbXMsIG5ldHdvcmtzLCBldGMuIHRvIGNvbnRhaW4gYWN0aXZpdHkgYW5kIGRhdGEsIHRodXMgcHJldmVudGluZyB0aGUgZXhwYW5zaW9uIG9mIGFuIGVuZ2FnZW1lbnQgYmV5b25kIGRlc2lyZWQgbGltaXRzLjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBpc29sYXRpb24tbG9uZy1kZXNjcmlwdGlvbiBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPlVzaW5nIElzb2xhdGlvbiwgYSBkZWZlbmRlciBjYW4gbGltaXQgdGhlIGVmZmVjdGl2ZW5lc3MgYW5kIHNjb3BlIG9mIG1hbGljaW91cyBhY3Rpdml0eSBhbmQvb3IgbG93ZXIgZXhwb3N1cmUgdG8gdW5pbnRlbmRlZCByaXNrcy4gV2hlbiBhIHN5c3RlbSBvciByZXNvdXJjZSBpcyBpc29sYXRlZCwgYSBkZWZlbmRlciBjYW4gb2JzZXJ2ZSBhZHZlcnNhcnkgYmVoYXZpb3JzIG9yIHRvb2xzIHdpdGggbGltaXRlZCwgb3Igbm8sIGxhdGVyYWwgbW92ZW1lbnQgYWxsb3dlZC4gRm9yIGV4YW1wbGUsIGEgZGVmZW5kZXIgbWF5IGRldG9uYXRlIGEgcGllY2Ugb2YgbWFsd2FyZSBvbiBhbiBpc29sYXRlZCBzeXN0ZW0gdG8gcGVyZm9ybSBkeW5hbWljIGFuYWx5c2lzIHdpdGhvdXQgcmlzayB0byBvdGhlciBuZXR3b3JrIHJlc291cmNlcy4gIERldGVybWluaW5nIHdoaWNoIHN5c3RlbXMgc2hvdWxkIGJlIGlzb2xhdGVkIGluIGFuIG9wZXJhdGlvbiBpcyBhIGNyaXRpY2FsIGRlY2lzaW9uIHdoZW4gY2FsY3VsYXRpbmcgYWNjZXB0YWJsZSBvcGVyYXRpb25hbCByaXNrLiBIb3dldmVyLCBpZiB0aGUgYWR2ZXJzYXJ5IGV4cGVjdHMgdG8gZmluZCBhbiBlbnRpcmUgY29ycG9yYXRlIG5ldHdvcmsgYnV0IGluc3RlYWQgZmluZHMgb25seSBhbiBpc29sYXRlZCBzeXN0ZW0sIHRoZXkgbWF5IG5vdCBiZSBpbnRlcmVzdGVkIGluIGVuZ2FnaW5nIHdpdGggdGhlIHRhcmdldC4gQmFsYW5jaW5nIGFjY2VwdGFibGUgcmlzaywgYmVsaWV2YWJpbGl0eSwgYW5kIG9wZXJhdGlvbmFsIG9iamVjdGl2ZXMgaXMgZXNzZW50aWFsIHdoZW4gZGV0ZXJtaW5pbmcgaWYgb3Igd2hlbiBhIHN5c3RlbSBzaG91bGQgYmUgaXNvbGF0ZWQuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMiBpc29sYXRpb24tYXR0YWNrLW1hcHBpbmdzIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPkVudGVycHJpc2U8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAyIj5FeGVjdXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVz4oCZIG1hbHdhcmUgaXMgZGV0b25hdGVkLCB0aGV5IG1heSBiZSBlbmNvdXJhZ2VkIHRvIG9wZXJhdGUgaW4gYW4gdW5pbnRlbmRlZCBlbnZpcm9ubWVudC48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDExIj5Db21tYW5kIGFuZCBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwOCI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXNlIGhhcmR3YXJlIHBlcmlwaGVyYWxzLCByZW1vdmFibGUgbWVkaWEsIG9yIGNvbm5lY3RlZCB0cmFuc2llbnQgY3liZXIgYXNzZXRzLCB0aGV5IG11c3QgcmVseSBvbiBwaHlzaWNhbCBhY2Nlc3Mgb3IgaGF2ZSBsaW1pdGVkIGNvbnRyb2wgb3ZlciB3aGVuIGFuZCB3aGVyZSBoYXJkd2FyZSBhZGRpdGlvbnMgYXJlIGNvbm5lY3RlZCBpbiB0aGUgdGFyZ2V0IG5ldHdvcmsuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAxMSI+Q29tbWFuZCBhbmQgQ29udHJvbDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgcmVseSBvbiBzcGVjaWZpYyByZXNvdXJjZXMgdG8gYmUgZW5hYmxlZCwgYWNjZXNzaWJsZSwgYW5kL29yIHZ1bG5lcmFibGUsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdGhlaXIgb3BlcmF0aW9ucyBiZWluZyBkaXNydXB0ZWQgaWYgdGhlIHJlc291cmNlcyBhcmUgZGlzYWJsZWQsIHJlbW92ZWQsIG9yIG90aGVyd2lzZSBtYWRlIGludnVsbmVyYWJsZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgbWFuaXB1bGF0ZSBzdXBwbHkgY2hhaW4gbWVjaGFuaXNtcyBwcmlvciB0byByZWNlaXB0IGJ5IGEgZmluYWwgY29uc3VtZXIsIHRoZXkgZm9yZmVpdCBjb250cm9sIG92ZXIgd2hlbiBhbmQgd2hlcmUgdGhlIHByb2R1Y3QgaXMgY29ubmVjdGVkIGluIHRoZSB0YXJnZXQgbmV0d29yay48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPk1vYmlsZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMjciPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMzIj5MYXRlcmFsIE1vdmVtZW50PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyB1c2UgaGFyZHdhcmUgcGVyaXBoZXJhbHMsIHJlbW92YWJsZSBtZWRpYSwgb3IgY29ubmVjdGVkIHRyYW5zaWVudCBjeWJlciBhc3NldHMsIHRoZXkgbXVzdCByZWx5IG9uIHBoeXNpY2FsIGFjY2VzcyBvciBoYXZlIGxpbWl0ZWQgY29udHJvbCBvdmVyIHdoZW4gYW5kIHdoZXJlIGhhcmR3YXJlIGFkZGl0aW9ucyBhcmUgY29ubmVjdGVkIGluIHRoZSB0YXJnZXQgbmV0d29yay48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDM3Ij5Db21tYW5kIGFuZCBDb250cm9sPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyByZWx5IG9uIHNwZWNpZmljIHJlc291cmNlcyB0byBiZSBlbmFibGVkLCBhY2Nlc3NpYmxlLCBhbmQvb3IgdnVsbmVyYWJsZSwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byB0aGVpciBvcGVyYXRpb25zIGJlaW5nIGRpc3J1cHRlZCBpZiB0aGUgcmVzb3VyY2VzIGFyZSBkaXNhYmxlZCwgcmVtb3ZlZCwgb3Igb3RoZXJ3aXNlIG1hZGUgaW52dWxuZXJhYmxlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMjciPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBtYW5pcHVsYXRlIHN1cHBseSBjaGFpbiBtZWNoYW5pc21zIHByaW9yIHRvIHJlY2VpcHQgYnkgYSBmaW5hbCBjb25zdW1lciwgdGhleSBmb3JmZWl0IGNvbnRyb2wgb3ZlciB3aGVuIGFuZCB3aGVyZSB0aGUgcHJvZHVjdCBpcyBjb25uZWN0ZWQgaW4gdGhlIHRhcmdldCBuZXR3b3JrLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+SUNTPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNCI+RXhlY3V0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTEwIj5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXPigJkgbWFsd2FyZSBpcyBkZXRvbmF0ZWQsIHRoZXkgbWF5IGJlIGVuY291cmFnZWQgdG8gb3BlcmF0ZSBpbiBhbiB1bmludGVuZGVkIGVudmlyb25tZW50LjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDgiPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyB1c2UgaGFyZHdhcmUgcGVyaXBoZXJhbHMsIHJlbW92YWJsZSBtZWRpYSwgb3IgY29ubmVjdGVkIHRyYW5zaWVudCBjeWJlciBhc3NldHMsIHRoZXkgbXVzdCByZWx5IG9uIHBoeXNpY2FsIGFjY2VzcyBvciBoYXZlIGxpbWl0ZWQgY29udHJvbCBvdmVyIHdoZW4gYW5kIHdoZXJlIGhhcmR3YXJlIGFkZGl0aW9ucyBhcmUgY29ubmVjdGVkIGluIHRoZSB0YXJnZXQgbmV0d29yay48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA4Ij5Jbml0aWFsIEFjY2VzczwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgbWFuaXB1bGF0ZSBzdXBwbHkgY2hhaW4gbWVjaGFuaXNtcyBwcmlvciB0byByZWNlaXB0IGJ5IGEgZmluYWwgY29uc3VtZXIsIHRoZXkgZm9yZmVpdCBjb250cm9sIG92ZXIgd2hlbiBhbmQgd2hlcmUgdGhlIHByb2R1Y3QgaXMgY29ubmVjdGVkIGluIHRoZSB0YXJnZXQgbmV0d29yay48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICA8L2Rpdj4KPC9kaXY+CjxkaXYgY2xhc3M9ImV0X3BiX3JvdyBldF9wYl9yb3dfMiBhdHRhY2stdmVjdG9yLW1pZ3JhdGlvbi1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+QXR0YWNrIFZlY3RvciBNaWdyYXRpb248L3NwYW4+CiAgICAgICAgICAgICAgICAgICAgPC9oND4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxoNT5JRDogRUFDMDAyMTwvaDU+CiAgICAgICAgICAgICAgICAgICAgICAgIDxwPk1vdmUgYSBtYWxpY2lvdXMgbGluaywgZmlsZSwgb3IgZGV2aWNlIGZyb20gaXRzIGludGVuZGVkIGxvY2F0aW9uIHRvIGFuIGVuZ2FnZW1lbnQgc3lzdGVtIG9yIG5ldHdvcmsgZm9yIGV4ZWN1dGlvbi91c2UuPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIGF0dGFjay12ZWN0b3ItbWlncmF0aW9uLWxvbmctZGVzY3JpcHRpb24gZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5XaGVuIGEgZGVmZW5kZXIgTWlncmF0ZXMgYW4gQXR0YWNrIFZlY3RvciwgdGhlIGRlZmVuZGVyIGludGVyY2VwdHMgYSBtYWxpY2lvdXMgZWxlbWVudCBhbmQgbW92ZXMgaXQgdG8gYSBzYWZlIGVudmlyb25tZW50LCBzdWNoIGFzIGEgZGVjb3kgc3lzdGVtIHdpdGhpbiBhIGRlY295IG5ldHdvcmssIGZvciBjb250aW51ZWQgZW5nYWdlbWVudCBvciBhbmFseXNpcy4gQSBkZWZlbmRlciBtYXkgY2hvb3NlIHRvIEF0dGFjayBWZWN0b3IgTWlncmF0aW9ucywgd2hpY2ggbWF5IGFwcGVhciBpbiB0aGUgZm9ybSBvZiBwaGlzaGluZyBlbWFpbHMsIHN1c3BpY2lvdXMgZW1haWwgYXR0YWNobWVudHMsIG9yIG1hbGljaW91cyBVU0JzLiBGb3IgZXhhbXBsZSwgYSBkZWZlbmRlciBtaWdodCBtb3ZlIGEgc3VzcGljaW91cyBhdHRhY2htZW50IGZyb20gYSBjb3Jwb3JhdGUgaW5ib3ggdG8gYW4gaW5ib3ggb24gYSBzeXN0ZW0gdGhhdCwgd2hpbGUgaW4gdGhlIGNvcnBvcmF0ZSBJUCBzcGFjZSwgaXMgY29tcGxldGVseSBzZWdtZW50ZWQgZnJvbSB0aGUgZW50ZXJwcmlzZSBuZXR3b3JrLiBUaGlzIHNlZ3JlZ2F0ZWQgZW52aXJvbm1lbnQgd2lsbCBhbGxvdyB0aGUgYWR2ZXJzYXJ5IHRvIG1vdmUgbGF0ZXJhbGx5IHRocm91Z2hvdXQgdGhlIGVudmlyb25tZW50IHdpdGhvdXQgcmlzayB0byBlbnRlcnByaXNlIHJlc291cmNlcy4gIERldGVybWluaW5nIHdoZW4gYW4gZW5nYWdlbWVudCBzaG91bGQgYmUgbW92ZWQgdG8gYW4gZW5nYWdlbWVudCBlbnZpcm9ubWVudCBpcyBhIGNyaXRpY2FsIGRlY2lzaW9uIHdoZW4gY2FsY3VsYXRpbmcgYWNjZXB0YWJsZSBvcGVyYXRpb25hbCByaXNrLiBIb3dldmVyLCBpZiB0aGUgYWR2ZXJzYXJ5IHNlbnQgYSBjdXN0b20gbWFsd2FyZSBzYW1wbGUgdG8gYSBwaGlzaGluZyB2aWN0aW0sIGJ1dCB1bHRpbWF0ZWx5IGZpbmQgdGhlbXNlbHZlcyBvbiBhbiB1bnJlbGF0ZWQgdmljdGltLCB0aGV5IG1heSBiZSBzdXNwaWNpb3VzLiBCYWxhbmNpbmcgdGhpcyBhY2NlcHRhYmxlIHJpc2ssIGJlbGlldmFiaWxpdHksIGFuZCBvcGVyYXRpb25hbCBnb2FscyBpcyBlc3NlbnRpYWwgd2hlbiBkZXRlcm1pbmluZyBpZiBvciB3aGVuIHRvIG1pZ3JhdGUgYW4gYXR0YWNrIHZlY3Rvci48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIGF0dGFjay12ZWN0b3ItbWlncmF0aW9uLXJlZmVyZW5jZXMgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0dGFibGUgdGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgUmVmZXJlbmNlIExpbmtzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2RvaS5vcmcvMTAuMTE0NS8zMjY4OTY2LjMyNjg5NzEiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5FbnN1cmluZyBEZWNlcHRpb24gQ29uc2lzdGVuY3kgRm9yIEZUUCBTZXJ2aWNlcyBIYXJkZW5lZCBBZ2FpbnN0IEFkdmFuY2VkIFBlcnNpc3RlbnQgVGhyZWF0czwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cHM6Ly9jaXRlc2VlcnguaXN0LnBzdS5lZHUvdmlld2RvYy9kb3dubG9hZD9kb2k9MTAuMS4xLjMxMC4yNTE0JmFtcDtyZXA9cmVwMSZhbXA7dHlwZT1wZGYiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5Ib25leXdvcmRzOiBNYWtpbmcgUGFzc3dvcmQtQ3JhY2tpbmcgRGV0ZWN0YWJsZTwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMiBhdHRhY2stdmVjdG9yLW1pZ3JhdGlvbi1hdHRhY2stbWFwcGluZ3MgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+RW50ZXJwcmlzZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDEiPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyB1c2UgcGhpc2hpbmcgZW1haWxzIHRvIGdhaW4gYWNjZXNzIHRvIHZpY3RpbSBzeXN0ZW1zLCB0aGV5IGhhdmUgbm8gY29udHJvbCBvdmVyIHdoZXJlIGEgbWFsaWNpb3VzIGF0dGFjaG1lbnQgaXMgZGV0b25hdGVkIGZyb20sIG9yIHdoZXJlIGEgbGluayBpcyBjbGlja2VkLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDIiPkV4ZWN1dGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXPigJkgbWFsd2FyZSBpcyBkZXRvbmF0ZWQsIHRoZXkgbWF5IGJlIGVuY291cmFnZWQgdG8gb3BlcmF0ZSBpbiBhbiB1bmludGVuZGVkIGVudmlyb25tZW50LjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMTEiPkNvbW1hbmQgYW5kIENvbnRyb2w8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDEiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA4Ij5MYXRlcmFsIE1vdmVtZW50PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyB1c2UgaGFyZHdhcmUgcGVyaXBoZXJhbHMsIHJlbW92YWJsZSBtZWRpYSwgb3IgY29ubmVjdGVkIHRyYW5zaWVudCBjeWJlciBhc3NldHMsIHRoZXkgbXVzdCByZWx5IG9uIHBoeXNpY2FsIGFjY2VzcyBvciBoYXZlIGxpbWl0ZWQgY29udHJvbCBvdmVyIHdoZW4gYW5kIHdoZXJlIGhhcmR3YXJlIGFkZGl0aW9ucyBhcmUgY29ubmVjdGVkIGluIHRoZSB0YXJnZXQgbmV0d29yay48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDExIj5Db21tYW5kIGFuZCBDb250cm9sPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAzIj5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgcmVseSBvbiBzcGVjaWZpYyByZXNvdXJjZXMgdG8gYmUgZW5hYmxlZCwgYWNjZXNzaWJsZSwgYW5kL29yIHZ1bG5lcmFibGUsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdGhlaXIgb3BlcmF0aW9ucyBiZWluZyBkaXNydXB0ZWQgaWYgdGhlIHJlc291cmNlcyBhcmUgZGlzYWJsZWQsIHJlbW92ZWQsIG9yIG90aGVyd2lzZSBtYWRlIGludnVsbmVyYWJsZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgbWFuaXB1bGF0ZSBzdXBwbHkgY2hhaW4gbWVjaGFuaXNtcyBwcmlvciB0byByZWNlaXB0IGJ5IGEgZmluYWwgY29uc3VtZXIsIHRoZXkgZm9yZmVpdCBjb250cm9sIG92ZXIgd2hlbiBhbmQgd2hlcmUgdGhlIHByb2R1Y3QgaXMgY29ubmVjdGVkIGluIHRoZSB0YXJnZXQgbmV0d29yay48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPk1vYmlsZTwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMjciPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDMzIj5MYXRlcmFsIE1vdmVtZW50PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyB1c2UgaGFyZHdhcmUgcGVyaXBoZXJhbHMsIHJlbW92YWJsZSBtZWRpYSwgb3IgY29ubmVjdGVkIHRyYW5zaWVudCBjeWJlciBhc3NldHMsIHRoZXkgbXVzdCByZWx5IG9uIHBoeXNpY2FsIGFjY2VzcyBvciBoYXZlIGxpbWl0ZWQgY29udHJvbCBvdmVyIHdoZW4gYW5kIHdoZXJlIGhhcmR3YXJlIGFkZGl0aW9ucyBhcmUgY29ubmVjdGVkIGluIHRoZSB0YXJnZXQgbmV0d29yay48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDI4Ij5QZXJzaXN0ZW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgcmVseSBvbiBzcGVjaWZpYyByZXNvdXJjZXMgdG8gYmUgZW5hYmxlZCwgYWNjZXNzaWJsZSwgYW5kL29yIHZ1bG5lcmFibGUsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdGhlaXIgb3BlcmF0aW9ucyBiZWluZyBkaXNydXB0ZWQgaWYgdGhlIHJlc291cmNlcyBhcmUgZGlzYWJsZWQsIHJlbW92ZWQsIG9yIG90aGVyd2lzZSBtYWRlIGludnVsbmVyYWJsZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDI3Ij5Jbml0aWFsIEFjY2VzczwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgbWFuaXB1bGF0ZSBzdXBwbHkgY2hhaW4gbWVjaGFuaXNtcyBwcmlvciB0byByZWNlaXB0IGJ5IGEgZmluYWwgY29uc3VtZXIsIHRoZXkgZm9yZmVpdCBjb250cm9sIG92ZXIgd2hlbiBhbmQgd2hlcmUgdGhlIHByb2R1Y3QgaXMgY29ubmVjdGVkIGluIHRoZSB0YXJnZXQgbmV0d29yay48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPklDUzwvc3Bhbj48YnI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBVFQmYW1wO0NLJnJlZzsgVGFjdGljcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogNjQ3Ljk2OXB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQWR2ZXJzYXJ5IFZ1bG5lcmFiaWxpdHkgUHJlc2VudGVkCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDQiPkV4ZWN1dGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwOCI+SW5pdGlhbCBBY2Nlc3M8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHVzZSBwaGlzaGluZyBlbWFpbHMgdG8gZ2FpbiBhY2Nlc3MgdG8gdmljdGltIHN5c3RlbXMsIHRoZXkgaGF2ZSBubyBjb250cm9sIG92ZXIgd2hlcmUgYSBtYWxpY2lvdXMgYXR0YWNobWVudCBpcyBkZXRvbmF0ZWQgZnJvbSwgb3Igd2hlcmUgYSBsaW5rIGlzIGNsaWNrZWQuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNCI+RXhlY3V0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllc+KAmSBtYWx3YXJlIGlzIGRldG9uYXRlZCwgdGhleSBtYXkgYmUgZW5jb3VyYWdlZCB0byBvcGVyYXRlIGluIGFuIHVuaW50ZW5kZWQgZW52aXJvbm1lbnQuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwOCI+SW5pdGlhbCBBY2Nlc3M8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIHVzZSBoYXJkd2FyZSBwZXJpcGhlcmFscywgcmVtb3ZhYmxlIG1lZGlhLCBvciBjb25uZWN0ZWQgdHJhbnNpZW50IGN5YmVyIGFzc2V0cywgdGhleSBtdXN0IHJlbHkgb24gcGh5c2ljYWwgYWNjZXNzIG9yIGhhdmUgbGltaXRlZCBjb250cm9sIG92ZXIgd2hlbiBhbmQgd2hlcmUgaGFyZHdhcmUgYWRkaXRpb25zIGFyZSBjb25uZWN0ZWQgaW4gdGhlIHRhcmdldCBuZXR3b3JrLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDgiPkluaXRpYWwgQWNjZXNzPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBtYW5pcHVsYXRlIHN1cHBseSBjaGFpbiBtZWNoYW5pc21zIHByaW9yIHRvIHJlY2VpcHQgYnkgYSBmaW5hbCBjb25zdW1lciwgdGhleSBmb3JmZWl0IGNvbnRyb2wgb3ZlciB3aGVuIGFuZCB3aGVyZSB0aGUgcHJvZHVjdCBpcyBjb25uZWN0ZWQgaW4gdGhlIHRhcmdldCBuZXR3b3JrLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgIDwvZGl2Pgo8L2Rpdj4KPGRpdiBjbGFzcz0iZXRfcGJfcm93IGV0X3BiX3Jvd18yIGFydGlmYWN0LWRpdmVyc2l0eS1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+QXJ0aWZhY3QgRGl2ZXJzaXR5PC9zcGFuPgogICAgICAgICAgICAgICAgICAgIDwvaDQ+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8aDU+SUQ6IEVBQzAwMjI8L2g1PgogICAgICAgICAgICAgICAgICAgICAgICA8cD5QcmVzZW50IHRoZSBhZHZlcnNhcnkgd2l0aCBhIHZhcmlldHkgb2YgbmV0d29yayBhbmQgc3lzdGVtIGFydGlmYWN0cy48L3A+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzEgYXJ0aWZhY3QtZGl2ZXJzaXR5LWxvbmctZGVzY3JpcHRpb24gZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5BcnRpZmFjdCBEaXZlcnNpdHkgbWVhbnMgcHJlc2VudGluZyBtdWx0aXBsZSBuZXR3b3JrIGFuZCBzeXN0ZW0gYXJ0aWZhY3RzIHRvIHRoZSBhZHZlcnNhcnkgaW5jbHVkaW5nIGFjY291bnRzLCBmaWxlcy9kaXJlY3RvcmllcywgY3JlZGVudGlhbHMsIGxvZ3MsIHdlYiBicm93c2luZyBoaXN0b3J5LCBicm93c2VyIGNvb2tpZXMsIGV0Yy4gVGhlc2UgYXJ0aWZhY3RzIGNhbiBiZSBsZWdpdGltYXRlIGFydGlmYWN0cyBjcmVhdGVkIGFzIHRoZSByZXN1bHQgb2YgbmF0dXJhbCB1c2FnZSBvdmVyIHRpbWUgb3IgbWFudWFsbHkgYWRkZWQgdG8gdGhlIGVudmlyb25tZW50IGJ5IHRoZSBkZWZlbmRlci4gQXJ0aWZhY3QgRGl2ZXJzaXR5IGNhbiBiZSB1c2VkIHRvIGVuY291cmFnZSB0aGUgYWR2ZXJzYXJ5IHRvIGVuZ2FnZSBieSBvZmZlcmluZyBhIGJyb2FkIGF0dGFjayBzdXJmYWNlIG9yIGNhbiBpbmNyZWFzZSB0aGUgYWR2ZXJzYXJ54oCZcyBvdmVyYWxsIGNvbWZvcnQgbGV2ZWwgYnkgYWRkaW5nIHRvIHRoZSBiZWxpZXZhYmlsaXR5IG9mIHRoZSBlbnZpcm9ubWVudC4gIEFkZGl0aW9uYWxseSwgdGhlc2UgYXJ0aWZhY3RzIG1heSBiZSBMdXJlcyBpbnRlbmRlZCB0byBlbGljaXQgYSBzcGVjaWZpYyByZXNwb25zZSBmcm9tIHRoZSBhZHZlcnNhcnkuIEluIGFueSBjYXNlLCBieSBtb25pdG9yaW5nIGFkdmVyc2FyeSBhY3Rpdml0eSBpbiBhIGRpdmVyc2UgZW52aXJvbm1lbnQsIHRoZSBkZWZlbmRlciBjYW4gZ2FpbiBpbmZvcm1hdGlvbiBvbiB0aGUgYWR2ZXJzYXJ54oCZcyBjYXBhYmlsaXRpZXMgYW5kIHRhcmdldGluZyBwcmVmZXJlbmNlcy4gRm9yIGV4YW1wbGUsIGEgZGVmZW5kZXIgY2FuIGluY2x1ZGUgYSBkaXZlcnNlIHNldCBvZiBhY2NvdW50cyBhbmQgY3JlZGVudGlhbHMgYW5kIHRoZW4gbW9uaXRvciB0byBkZXRlcm1pbmUgd2hpY2ggYWNjb3VudHMgdGhlIGFkdmVyc2FyeSB0YXJnZXRzIGluIHRoZSBmdXR1cmUuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMiBhcnRpZmFjdC1kaXZlcnNpdHktYXR0YWNrLW1hcHBpbmdzIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPkVudGVycHJpc2U8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA5Ij5Db2xsZWN0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA2Ij5DcmVkZW50aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNSI+RGVmZW5zZSBFdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA3Ij5EaXNjb3Zlcnk8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDIiPkV4ZWN1dGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDA0MCI+SW1wYWN0PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAxIj5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMyI+UGVyc2lzdGVuY2U8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDQiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQzIj5SZWNvbm5haXNzYW5jZTwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZGlzY292ZXIgYSBkaXZlcnNlIHNldCBvZiBhY2Nlc3NpYmxlIHJlc291cmNlcyBhbmQgZGVjb3kgYXJ0aWZhY3RzIG9uIHRoZSB0YXJnZXQsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gcmV2ZWFsaW5nIHRoZWlyIHRhcmdldGluZyBwcmVmZXJlbmNlcyBhbmQgY2FwYWJpbGl0aWVzLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+TW9iaWxlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzNCI+SW1wYWN0PC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIHRoZSBlbnZpcm9ubWVudCBvciBwZXJzb25hcywgdGhleSBhcmUgdnVsbmVyYWJsZSB3aGVuIHRoZXkgY29sbGVjdCwgb2JzZXJ2ZSwgb3IgbWFuaXB1bGF0ZSBzeXN0ZW0gYXJ0aWZhY3RzIG9yIGluZm9ybWF0aW9uLiBNYW5pcHVsYXRlZCBkYXRhIG1heSBjYXVzZSB0aGVtIHRvIHJldmVhbCBiZWhhdmlvcnMsIHVzZSBhZGRpdGlvbmFsIG9yIG1vcmUgYWR2YW5jZWQgY2FwYWJpbGl0aWVzIGFnYWluc3QgdGhlIHRhcmdldCwgYW5kL29yIGltcGFjdCB0aGVpciBkd2VsbCB0aW1lLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzUiPkNvbGxlY3Rpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzAiPkRlZmVuc2UgRXZhc2lvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAzMiI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDQxIj5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMzQiPkltcGFjdDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZGlzY292ZXIgYSBkaXZlcnNlIHNldCBvZiBhY2Nlc3NpYmxlIHJlc291cmNlcyBhbmQgZGVjb3kgYXJ0aWZhY3RzIG9uIHRoZSB0YXJnZXQsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gcmV2ZWFsaW5nIHRoZWlyIHRhcmdldGluZyBwcmVmZXJlbmNlcyBhbmQgY2FwYWJpbGl0aWVzLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+SUNTPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwMCI+Q29sbGVjdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwNyI+SW5oaWJpdCBSZXNwb25zZSBGdW5jdGlvbjwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwOSI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDExMCI+UGVyc2lzdGVuY2U8L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGEgZGl2ZXJzZSBzZXQgb2YgYWNjZXNzaWJsZSByZXNvdXJjZXMgYW5kIGRlY295IGFydGlmYWN0cyBvbiB0aGUgdGFyZ2V0LCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHJldmVhbGluZyB0aGVpciB0YXJnZXRpbmcgcHJlZmVyZW5jZXMgYW5kIGNhcGFiaWxpdGllcy48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICA8L2Rpdj4KPC9kaXY+CjxkaXYgY2xhc3M9ImV0X3BiX3JvdyBldF9wYl9yb3dfMiBpbnRyb2R1Y2VkLXZ1bG5lcmFiaWxpdGllcy1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+SW50cm9kdWNlZCBWdWxuZXJhYmlsaXRpZXM8L3NwYW4+CiAgICAgICAgICAgICAgICAgICAgPC9oND4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxoNT5JRDogRUFDMDAyMzwvaDU+CiAgICAgICAgICAgICAgICAgICAgICAgIDxwPkludGVudGlvbmFsbHkgaW50cm9kdWNlIHZ1bG5lcmFiaWxpdGllcyBpbnRvIHRoZSBlbnZpcm9ubWVudCBmb3IgdGhlIGFkdmVyc2FyeSB0byBleHBsb2l0LjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBpbnRyb2R1Y2VkLXZ1bG5lcmFiaWxpdGllcy1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+QnkgaW50ZW50aW9uYWxseSBJbnRyb2R1Y2luZyBWdWxuZXJhYmlsaXRpZXMgaW50byB0aGUgZW5nYWdlbWVudCBlbnZpcm9ubWVudCwgdGhlIGRlZmVuZGVyIGNhbiBhdHRlbXB0IHRvIG1vdGl2YXRlIHRoZSBhZHZlcnNhcnkgdG8gdGFyZ2V0IHNwZWNpZmljIHJlc291cmNlcy4gVGhpcyB0YXJnZXRpbmcgbWF5IHNlcnZlIHRvIG1vdmUgdGhlIGFkdmVyc2FyeSB0b3dhcmRzIGEgcGFydGljdWxhciByZXNvdXJjZSwgb3IgYXdheSBmcm9tIGFub3RoZXIgcmVzb3VyY2UuIEF0IG90aGVyIHRpbWVzLCB0aGUgZGVmZW5kZXIgbWF5IEludHJvZHVjZSBWdWxuZXJhYmlsaXRpZXMgYXMgYSBtZWFuIG9mIGVuY291cmFnaW5nIHRoZSBhZHZlcnNhcnkgdG8gcmV2ZWFsIHRhcmdldGluZyBwcmVmZXJlbmNlcywgYXZhaWxhYmxlIGNhcGFiaWxpdGllcywgb3IgZXZlbiB0byBpbmZsdWVuY2UgZnV0dXJlIHRhcmdldGluZyBkZWNpc2lvbnMuIFRoZSBvcGVyYXRpb25hbCBvYmplY3RpdmVzIHdpbGwgZHJpdmUgaG93IGFuZCB3aHkgdGhlIGRlZmVuZGVyIEludHJvZHVjZXMgVnVsbmVyYWJpbGl0aWVzIGluIHRoZSBlbmdhZ2VtZW50IGVudmlyb25tZW50LjwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgaW50cm9kdWNlZC12dWxuZXJhYmlsaXRpZXMtYXR0YWNrLW1hcHBpbmdzIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuPkVudGVycHJpc2U8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA2Ij5DcmVkZW50aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNyI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAyIj5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDgiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDQiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBpbnRlcmFjdCB3aXRoIGVuZ2FnZW1lbnQgZW52aXJvbm1lbnRzIGFuZCBwZXJzb25hcywgdGhlaXIgZnV0dXJlIGNhcGFiaWxpdHksIHRhcmdldGluZywgYW5kL29yIGluZnJhc3RydWN0dXJlIHJlcXVpcmVtZW50cyBhcmUgdnVsbmVyYWJsZSB0byBpbmZsdWVuY2UuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNiI+Q3JlZGVudGlhbCBBY2Nlc3M8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDciPkRpc2NvdmVyeTwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwMiI+RXhlY3V0aW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA4Ij5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA0Ij5Qcml2aWxlZ2UgRXNjYWxhdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBuZXR3b3JrIG9yIHN5c3RlbSByZXNvdXJjZXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdHJpZ2dlcmluZyB0cmlwd2lyZXMgb3IgZW5nYWdpbmcgaW4gZWFzaWx5IGRldGVjdGFibGUsIGFub21hbG91cyBiZWhhdmlvci48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA2Ij5DcmVkZW50aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNyI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAyIj5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDgiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDQiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyB1dGlsaXplIG9yIGFidXNlIHN5c3RlbSBmZWF0dXJlcywgc29mdHdhcmUsIG9yIG90aGVyIHJlc291cmNlcywgdGhleSBtYXkgYmUgdnVsbmVyYWJsZSB0byBtb25pdG9yaW5nIG9yIE1hbi1pbi10aGUtTWlkZGxlIG1hbmlwdWxhdGlvbi48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDA2Ij5DcmVkZW50aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAwNyI+RGlzY292ZXJ5PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDAyIj5FeGVjdXRpb248L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDgiPkxhdGVyYWwgTW92ZW1lbnQ8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAwMDQiPlByaXZpbGVnZSBFc2NhbGF0aW9uPC9hPiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDY0Ny45NjlweCI+V2hlbiBhZHZlcnNhcmllcyBkaXNjb3ZlciBlbmFibGVkLCBhY2Nlc3NpYmxlLCBvciBpbnRlbnRpb25hbGx5IHdlYWtlbmVkL292ZXJseSBwZXJtaXNzaXZlIHJlc291cmNlcyBpbiB0aGUgZW52aXJvbm1lbnQgKHByb2R1Y3Rpb24gb3IgaXNvbGF0ZWQpLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHJldmVhbGluZyBhZGRpdGlvbmFsIG9yIG1vcmUgYWR2YW5jZWQgY2FwYWJpbGl0aWVzIHdoZW4gZXhwbG9pdGluZyBvciB1c2luZyBzYWlkIHJlc291cmNlLjwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4+TW9iaWxlPC9zcGFuPjxicj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFUVCZhbXA7Q0smcmVnOyBUYWN0aWNzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiA2NDcuOTY5cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBBZHZlcnNhcnkgVnVsbmVyYWJpbGl0eSBQcmVzZW50ZWQKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAyOSI+UHJpdmlsZWdlIEVzY2FsYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGludGVyYWN0IHdpdGggZW5nYWdlbWVudCBlbnZpcm9ubWVudHMgYW5kIHBlcnNvbmFzLCB0aGVpciBmdXR1cmUgY2FwYWJpbGl0eSwgdGFyZ2V0aW5nLCBhbmQvb3IgaW5mcmFzdHJ1Y3R1cmUgcmVxdWlyZW1lbnRzIGFyZSB2dWxuZXJhYmxlIHRvIGluZmx1ZW5jZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDI5Ij5Qcml2aWxlZ2UgRXNjYWxhdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBuZXR3b3JrIG9yIHN5c3RlbSByZXNvdXJjZXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdHJpZ2dlcmluZyB0cmlwd2lyZXMgb3IgZW5nYWdpbmcgaW4gZWFzaWx5IGRldGVjdGFibGUsIGFub21hbG91cyBiZWhhdmlvci48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMDI5Ij5Qcml2aWxlZ2UgRXNjYWxhdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgdXRpbGl6ZSBvciBhYnVzZSBzeXN0ZW0gZmVhdHVyZXMsIHNvZnR3YXJlLCBvciBvdGhlciByZXNvdXJjZXMsIHRoZXkgbWF5IGJlIHZ1bG5lcmFibGUgdG8gbW9uaXRvcmluZyBvciBNYW4taW4tdGhlLU1pZGRsZSBtYW5pcHVsYXRpb24uPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDAyOSI+UHJpdmlsZWdlIEVzY2FsYXRpb248L2E+ICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogNjQ3Ljk2OXB4Ij5XaGVuIGFkdmVyc2FyaWVzIGRpc2NvdmVyIGVuYWJsZWQsIGFjY2Vzc2libGUsIG9yIGludGVudGlvbmFsbHkgd2Vha2VuZWQvb3Zlcmx5IHBlcm1pc3NpdmUgcmVzb3VyY2VzIGluIHRoZSBlbnZpcm9ubWVudCAocHJvZHVjdGlvbiBvciBpc29sYXRlZCksIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gcmV2ZWFsaW5nIGFkZGl0aW9uYWwgb3IgbW9yZSBhZHZhbmNlZCBjYXBhYmlsaXRpZXMgd2hlbiBleHBsb2l0aW5nIG9yIHVzaW5nIHNhaWQgcmVzb3VyY2UuPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGFibGU+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8c3Bhbj5JQ1M8L3NwYW4+PGJyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgQVRUJmFtcDtDSyZyZWc7IFRhY3RpY3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDY0Ny45NjlweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIEFkdmVyc2FyeSBWdWxuZXJhYmlsaXR5IFByZXNlbnRlZAogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAzIj5FdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA4Ij5Jbml0aWFsIEFjY2VzczwvYT4sICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIHN0eWxlPSJjb2xvcjogIzAxNjNDQiAhaW1wb3J0YW50OyBmb250LXdlaWdodDogYm9sZDsgdGV4dC1kZWNvcmF0aW9uOiBub25lOyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiIGhyZWY9Imh0dHBzOi8vYXR0YWNrLm1pdHJlLm9yZy90YWN0aWNzL1RBMDEwOSI+TGF0ZXJhbCBNb3ZlbWVudDwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgaW50ZXJhY3Qgd2l0aCBuZXR3b3JrIG9yIHN5c3RlbSByZXNvdXJjZXMsIHRoZXkgYXJlIHZ1bG5lcmFibGUgdG8gdHJpZ2dlcmluZyB0cmlwd2lyZXMgb3IgZW5nYWdpbmcgaW4gZWFzaWx5IGRldGVjdGFibGUsIGFub21hbG91cyBiZWhhdmlvci48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTAzIj5FdmFzaW9uPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA1Ij5JbXBhY3Q8L2E+LCAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBzdHlsZT0iY29sb3I6ICMwMTYzQ0IgIWltcG9ydGFudDsgZm9udC13ZWlnaHQ6IGJvbGQ7IHRleHQtZGVjb3JhdGlvbjogbm9uZTsiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIiBocmVmPSJodHRwczovL2F0dGFjay5taXRyZS5vcmcvdGFjdGljcy9UQTAxMDgiPkluaXRpYWwgQWNjZXNzPC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTA5Ij5MYXRlcmFsIE1vdmVtZW50PC9hPiwgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgc3R5bGU9ImNvbG9yOiAjMDE2M0NCICFpbXBvcnRhbnQ7IGZvbnQtd2VpZ2h0OiBib2xkOyB0ZXh0LWRlY29yYXRpb246IG5vbmU7IiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciIgaHJlZj0iaHR0cHM6Ly9hdHRhY2subWl0cmUub3JnL3RhY3RpY3MvVEEwMTExIj5Qcml2aWxlZ2UgRXNjYWxhdGlvbjwvYT4gICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiA2NDcuOTY5cHgiPldoZW4gYWR2ZXJzYXJpZXMgZGlzY292ZXIgZW5hYmxlZCwgYWNjZXNzaWJsZSwgb3IgaW50ZW50aW9uYWxseSB3ZWFrZW5lZC9vdmVybHkgcGVybWlzc2l2ZSByZXNvdXJjZXMgaW4gdGhlIGVudmlyb25tZW50IChwcm9kdWN0aW9uIG9yIGlzb2xhdGVkKSwgdGhleSBhcmUgdnVsbmVyYWJsZSB0byByZXZlYWxpbmcgYWRkaXRpb25hbCBvciBtb3JlIGFkdmFuY2VkIGNhcGFiaWxpdGllcyB3aGVuIGV4cGxvaXRpbmcgb3IgdXNpbmcgc2FpZCByZXNvdXJjZS48L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICA8L2Rpdj4KPC9kaXY+CjxkaXYgY2xhc3M9ImV0X3BiX3JvdyBldF9wYl9yb3dfMiBjb2xsZWN0LWRldGFpbCBtYXRyaXgtZGV0YWlscyBldF9wYl9ndXR0ZXJzMSBldF9oYWRfYW5pbWF0aW9uIiBzdHlsZT0iZGlzcGxheTogbm9uZTsiPgogICAgPGRpdiBjbGFzcz0iZXRfcGJfY29sdW1uIGV0X3BiX2NvbHVtbl80XzQgZXRfcGJfY29sdW1uXzUgZXRfcGJfY3NzX21peF9ibGVuZF9tb2RlX3Bhc3N0aHJvdWdoIGV0LWxhc3QtY2hpbGQiPgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8wIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGg0IGNsYXNzPSJldF9wYl9tb2R1bGVfaGVhZGVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4gc3R5bGU9ImZvbnQtc2l6ZTogMjBweCAhaW1wb3J0YW50O2xpbmUtaGVpZ2h0OiAxICFpbXBvcnRhbnQ7Zm9udC13ZWlnaHQ6IDYwMCAhaW1wb3J0YW50Ij5Db2xsZWN0PC9zcGFuPgogICAgICAgICAgICAgICAgICAgIDwvaDQ+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8aDU+SUQ6IEVBUDAwMDE8L2g1PgogICAgICAgICAgICAgICAgICAgICAgICA8cD5HYXRoZXIgYWR2ZXJzYXJ5IHRvb2xzLCBvYnNlcnZlIHRhY3RpY3MsIGFuZCBjb2xsZWN0IG90aGVyIHJhdyBpbnRlbGxpZ2VuY2UgYWJvdXQgdGhlIGFkdmVyc2FyeeKAmXMgYWN0aXZpdHkuPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIGNvbGxlY3QtbG9uZy1kZXNjcmlwdGlvbiBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPkNvbGxlY3Rpb24gYWN0aXZpdGllcyBhcmUgdXNlZCB0byBnYXRoZXIgaW5mb3JtYXRpb24gYWJvdXQgYW4gYWR2ZXJzYXJ5IG9yIHRoZWlyIGFjdGl2aXRpZXMuIFRoaXMgY29sbGVjdGlvbiBjYW4gaW5jbHVkZSBnYXRoZXJpbmcgc3lzdGVtIGxvZ3MsIG5ldHdvcmsgdHJhZmZpYywgYWR2ZXJzYXJ5IGFydGlmYWN0cywgb3Igb3RoZXIgZGF0YSB0aGF0IGNhbiBiZSB1c2VkIHRvIGV4cG9zZSBhZHZlcnNhcnkgYWN0aXZpdHkuIEluIG1hbnkgY2FzZXMsIGNvbGxlY3Rpb24gYWN0aXZpdGllcyBhcmUgYWxzbyBnb29kIGN5YmVyc2VjdXJpdHkgcHJhY3RpY2VzLiBIb3dldmVyLCBpbiBFbmdhZ2UsIHRoZXNlIGFjdGl2aXRpZXMgd2lsbCBmb2N1cyBleGNsdXNpdmVseSBvbiB0aGUgaW50ZXJzZWN0aW9uIG9mIGRlbmlhbCwgZGVjZXB0aW9uLCBhbmQgYWR2ZXJzYXJ5IGVuZ2FnZW1lbnQgdGVjaG5vbG9naWVzIGFuZCB0aGUgZGVmZW5kZXLigJlzIGFiaWxpdHkgdG8gRXhwb3NlIHRoZSBhZHZlcnNhcnkuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgZGV0ZWN0LWRldGFpbCBtYXRyaXgtZGV0YWlscyBldF9wYl9ndXR0ZXJzMSBldF9oYWRfYW5pbWF0aW9uIiBzdHlsZT0iZGlzcGxheTogbm9uZTsiPgogICAgPGRpdiBjbGFzcz0iZXRfcGJfY29sdW1uIGV0X3BiX2NvbHVtbl80XzQgZXRfcGJfY29sdW1uXzUgZXRfcGJfY3NzX21peF9ibGVuZF9tb2RlX3Bhc3N0aHJvdWdoIGV0LWxhc3QtY2hpbGQiPgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8wIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGg0IGNsYXNzPSJldF9wYl9tb2R1bGVfaGVhZGVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4gc3R5bGU9ImZvbnQtc2l6ZTogMjBweCAhaW1wb3J0YW50O2xpbmUtaGVpZ2h0OiAxICFpbXBvcnRhbnQ7Zm9udC13ZWlnaHQ6IDYwMCAhaW1wb3J0YW50Ij5EZXRlY3Q8L3NwYW4+CiAgICAgICAgICAgICAgICAgICAgPC9oND4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxoNT5JRDogRUFQMDAwMjwvaDU+CiAgICAgICAgICAgICAgICAgICAgICAgIDxwPkVzdGFibGlzaCBvciBtYWludGFpbiBhd2FyZW5lc3MgcmVnYXJkaW5nIGFkdmVyc2FyeSBhY3Rpdml0eS48L3A+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzEgZGV0ZWN0LWxvbmctZGVzY3JpcHRpb24gZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5EZXRlY3Rpb24gYWN0aXZpdGllcyBmb2N1cyBvbiB0aGUgZGVmZW5kZXLigJlzIGFiaWxpdHkgdG8gbW9uaXRvciBhZHZlcnNhcnkgYWN0aXZpdHkgdGhyb3VnaG91dCBhbiBlbnZpcm9ubWVudCwgb2Z0ZW4gYnkgY3JlYXRpbmcgaGlnaC1maWRlbGl0eSBkZXRlY3Rpb25zLiBUaGVzZSBkZXRlY3Rpb25zIGNhbiBiZSBwcm9kdWNlZCBpbiBzZXZlcmFsIHdheXMuIEZvciBleGFtcGxlLCBhIGRlZmVuZGVyIGNhbiBkZXBsb3kgbHVyZXMgYXMgdHJpcHdpcmVzIGluIHRoZSBlbnZpcm9ubWVudC4gVGhlIGRlZmVuZGVyIG1heSBjcmVhdGUgY3VzdG9tIGFsZXJ0cyBiYXNlZCBvbiBUVFBzIG9yIElPQ3Mgb2JzZXJ2ZWQgZHVyaW5nIGEgbWFsd2FyZSBkZXRvbmF0aW9uIG9wZXJhdGlvbi4gRmluYWxseSwgdGhlIGRlZmVuZGVyIG1heSB3cml0ZSBjdXN0b21lciBkZWNvZGVycyB0byBhbmFseXplIGFuZCBhbGVydCBvbiBtYWxpY2lvdXMgdHJhZmZpYy48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5JbiBhbGwgdGhlc2UgY2FzZXMsIGRldGVjdGlvbiBhY3Rpdml0aWVzIGFsbG93IHRoZSBkZWZlbmRlciB0byBwcm9kdWNlIGEgaGlnaC1maWRlbGl0eSBhbGVydCB0byBtb25pdG9yIGFkdmVyc2FyeSBhY3Rpdml0aWVzLiBPZnRlbiBEZXRlY3Rpb24gYWN0aXZpdGllcyBhcmUgYWxzbyBnb29kIGN5YmVyc2VjdXJpdHkgcHJhY3RpY2VzLiBIb3dldmVyLCBpbiBFbmdhZ2UsIHRoZXNlIGFjdGl2aXRpZXMgd2lsbCBmb2N1cyBleGNsdXNpdmVseSBvbiB0aGUgaW50ZXJzZWN0aW9uIG9mIGRlbmlhbCwgZGVjZXB0aW9uLCBhbmQgYWR2ZXJzYXJ5IGVuZ2FnZW1lbnQgdGVjaG5vbG9naWVzIGFuZCB0aGUgZGVmZW5kZXLigJlzIGFiaWxpdHkgdG8gRXhwb3NlIHRoZSBhZHZlcnNhcnkuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgcHJldmVudC1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+UHJldmVudDwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBFQVAwMDAzPC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+U3RvcCBhbGwgb3IgcGFydCBvZiB0aGUgYWR2ZXJzYXJ54oCZcyBhYmlsaXR5IHRvIGNvbmR1Y3QgdGhlaXIgb3BlcmF0aW9uIGFzIGludGVuZGVkLjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBwcmV2ZW50LWxvbmctZGVzY3JpcHRpb24gZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5QcmV2ZW50aW9uIGFjdGl2aXRpZXMgZm9jdXMgb24gc3RvcHBpbmcgdGhlIGFkdmVyc2FyeeKAmXMgYWJpbGl0eSB0byBjb25kdWN0IHRoZWlyIG9wZXJhdGlvbnMgYXMgaW50ZW5kZWQuIFRoZSBkZWZlbmRlciBjYW4gcGh5c2ljYWxseSBvciB2aXJ0dWFsbHkgcmVtb3ZlIG9yIGRpc2FibGUgcmVzb3VyY2VzLCB0aWdodGVuIHNlY3VyaXR5IGNvbnRyb2xzLCBvciBvdGhlcndpc2UgaW1wYWlyIHRoZSBhZHZlcnNhcnnigJlzIGFiaWxpdHkgdG8gb3BlcmF0ZS4gQSBkZWZlbmRlciBtaWdodCBwcmV2ZW50IGFuIGFkdmVyc2FyeSBmcm9tIG9wZXJhdGluZyB0byBmb3JjZSB0aGVtIHRvIHJldmVhbCBkaWZmZXJlbnQsIHBvc3NpYmx5IG1vcmUgYWR2YW5jZWQsIGNhcGFiaWxpdGllcy4gQWRkaXRpb25hbGx5LCBhIGRlZmVuZGVyIGNhbiB1c2UgcHJldmVudGlvbiBhY3Rpdml0aWVzIHRvIGRpc2NvdXJhZ2UgdGhlIGFkdmVyc2FyeSBmcm9tIG9wZXJhdGluZyBhZ2FpbnN0IGEgc3BlY2lmaWMgdGFyZ2V0LiBJbiB0aGlzIGNhc2UsIHRoZSBkZWZlbmRlciBtYXkgYmUgYXR0ZW1wdGluZyB0byBlbmNvdXJhZ2UgdGhlIGFkdmVyc2FyeSB0byBmb2N1cyBlbHNld2hlcmUgaW4gdGhlIGVuZ2FnZW1lbnQgZW52aXJvbm1lbnQuICBUaGVyZSBhcmUgbWFueSBtb3JlIHByZXZlbnRpb24gYWN0aXZpdGllcyB0aGF0IGFyZSBhbHNvIGdvb2QgY3liZXJzZWN1cml0eSBwcmFjdGljZXMuIEhvd2V2ZXIsIGluIEVuZ2FnZSwgd2UgYXJlIGZvY3VzZWQgb24gYSBzdWJzZXQgb2YgYWN0aXZpdGllcy4gVGhvc2UgYXJlIGZvY3VzZWQgZXhjbHVzaXZlbHkgb24gdGhlIGludGVyc2VjdGlvbiBvZiBkZW5pYWwsIGRlY2VwdGlvbiwgYW5kIGFkdmVyc2FyeSBlbmdhZ2VtZW50IHRlY2hub2xvZ2llcyBhbmQgdGhlIGRlZmVuZGVy4oCZcyBhYmlsaXR5IHRvIEFmZmVjdCB0aGUgYWR2ZXJzYXJ5LjwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgIDwvZGl2Pgo8L2Rpdj4KPGRpdiBjbGFzcz0iZXRfcGJfcm93IGV0X3BiX3Jvd18yIGRpcmVjdC1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+RGlyZWN0PC9zcGFuPgogICAgICAgICAgICAgICAgICAgIDwvaDQ+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8aDU+SUQ6IEVBUDAwMDQ8L2g1PgogICAgICAgICAgICAgICAgICAgICAgICA8cD5FbmNvdXJhZ2Ugb3IgZGlzY291cmFnZSB0aGUgYWR2ZXJzYXJ5IGZyb20gY29uZHVjdGluZyB0aGVpciBvcGVyYXRpb24gYXMgaW50ZW5kZWQuPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIGRpcmVjdC1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+RGlyZWN0aW9uIGFjdGl2aXRpZXMgZm9jdXMgb24gbW92aW5nIHRoZSBhZHZlcnNhcnkgdG93YXJkcyBvciBhd2F5IGZyb20gYW4gaW50ZW5kZWQgcGF0aC4gVGhpcyBmb3JjZWQgZGlyZWN0aW9uIGNhbiBiZSBhY2NvbXBsaXNoZWQgYnkgcmVtb3Zpbmcgb3IgZGlzYWJsaW5nIHNvbWUgcmVzb3VyY2VzLCB3aGlsZSBhZGRpbmcgb3IgZW5hYmxpbmcgb3RoZXJzLiBUaGUgZGVmZW5kZXIgY2FuIGFkZCBsdXJlcyBvciBvdGhlcndpc2UgbWFuaXB1bGF0ZSB0aGUgZW52aXJvbm1lbnQgdG8gYXR0ZW1wdCB0byBlbGljaXQgc3BlY2lmaWMgcmVzcG9uc2VzIGZyb20gdGhlIGFkdmVyc2FyeS4gQWRkaXRpb25hbGx5LCB0aGUgZGVmZW5kZXIgY2FuIHRpZ2h0ZW4gc29tZSBzZWN1cml0eSBjb250cm9scyB3aGlsZSBsZWF2aW5nIG90aGVycyBvdmVybHkgcGVybWlzc2l2ZSBvciB3ZWFrZW5lZC4gRmluYWxseSwgdGhlIGRlZmVuZGVyIGNhbiBwaHlzaWNhbGx5IG1vdmUgdGhlIGFkdmVyc2FyeSBieSBtb3ZpbmcgdGhyZWF0cyBmcm9tIHRoZWlyIGludGVuZGVkIGVudmlyb25tZW50IGFuZCBpbnRvIGEgc2FmZSBlbmdhZ2VtZW50IGVudmlyb25tZW50LiAgRm9yIGV4YW1wbGUsIGEgc3VzcGljaW91cyBlbWFpbCBhdHRhY2htZW50IGNhbiBiZSBtb3ZlZCBmcm9tIHRoZSBpbnRlbmRlZCB0YXJnZXQgdG8gYW4gZW5nYWdlbWVudCBlbnZpcm9ubWVudCBmb3IgYW5hbHlzaXMuIE5vIG1hdHRlciBob3cgdGhlIGRpcmVjdGlvbiBpcyBhY2hpZXZlZCwgdGhlIGRlZmVuZGVyIGhvcGVzIHRvIGZvcmNlIHRoZSBhZHZlcnNhcnkgdG8gdGFrZSB1bmludGVuZGVkIGFjdGlvbnMgb3Igc3RvcCBpbnRlbmRlZCBhY3Rpb25zLjwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgIDwvZGl2Pgo8L2Rpdj4KPGRpdiBjbGFzcz0iZXRfcGJfcm93IGV0X3BiX3Jvd18yIGRpc3J1cHQtZGV0YWlsIG1hdHJpeC1kZXRhaWxzIGV0X3BiX2d1dHRlcnMxIGV0X2hhZF9hbmltYXRpb24iIHN0eWxlPSJkaXNwbGF5OiBub25lOyI+CiAgICA8ZGl2IGNsYXNzPSJldF9wYl9jb2x1bW4gZXRfcGJfY29sdW1uXzRfNCBldF9wYl9jb2x1bW5fNSBldF9wYl9jc3NfbWl4X2JsZW5kX21vZGVfcGFzc3Rocm91Z2ggZXQtbGFzdC1jaGlsZCI+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzAgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8aDQgY2xhc3M9ImV0X3BiX21vZHVsZV9oZWFkZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8c3BhbiBzdHlsZT0iZm9udC1zaXplOiAyMHB4ICFpbXBvcnRhbnQ7bGluZS1oZWlnaHQ6IDEgIWltcG9ydGFudDtmb250LXdlaWdodDogNjAwICFpbXBvcnRhbnQiPkRpc3J1cHQ8L3NwYW4+CiAgICAgICAgICAgICAgICAgICAgPC9oND4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxoNT5JRDogRUFQMDAwNTwvaDU+CiAgICAgICAgICAgICAgICAgICAgICAgIDxwPkltcGFpciBhbiBhZHZlcnNhcnnigJlzIGFiaWxpdHkgdG8gY29uZHVjdCB0aGVpciBvcGVyYXRpb24gYXMgaW50ZW5kZWQuPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIGRpc3J1cHQtbG9uZy1kZXNjcmlwdGlvbiBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPkRpc3J1cHRpb24gYWN0aXZpdGllcyBhcmUgdXNlZCB0byBzdG9wIG9yIGRpc2NvdXJhZ2UgYW4gYWR2ZXJzYXJ5IGZyb20gY29uZHVjdGluZyBwYXJ0IG9yIGFsbCBvZiB0aGVpciBtaXNzaW9uLiBUaGlzIGRpc3J1cHRpb24gbWF5IGluY3JlYXNlIHRoZSB0aW1lLCBza2lsbHMsIG9yIHJlc291cmNlcyBuZWVkZWQgZm9yIHRoZSBhZHZlcnNhcnkgdG8gYWNjb21wbGlzaCBhIHNwZWNpZmljIHRhc2suIEZvciBleGFtcGxlLCBhIGRlZmVuZGVyIG1heSBkZWdyYWRlIG5ldHdvcmsgc3BlZWRzIGFzIHRoZSBhZHZlcnNhcnkgYXR0ZW1wdHMgdG8gZXhmaWx0cmF0ZSBsYXJnZSBibG9ja3Mgb2YgZGF0YS4gQXMgYSBzZWNvbmQgZXhhbXBsZSwgdGhlIGRlZmVuZGVyIG1heSBtYW5pcHVsYXRlIHRoZSBvdXRwdXQgb2YgY29tbW9ubHkgdXNlZCBkaXNjb3ZlcnkgY29tbWFuZHMgdG8gc2hvdyB0YXJnZXRzIHRoYXQgZG8gbm90IGV4aXN0IG9yIHRvIGhpZGUgcmVhbCB0YXJnZXRzLiBJbiBlaXRoZXIgY2FzZSwgdGhlIGFkdmVyc2FyeSBtYXkgd2FzdGUgcmVzb3VyY2VzIGFjdGluZyBvbiBwYXJ0aWFsIG9yIGZhbHNpZmllZCBkYXRhLiAgRGlzcnVwdGlvbnMgbWF5IGFsc28gaW5jbHVkZSBwbGFudGluZyBtaXNpbmZvcm1hdGlvbiBkZXNpZ25lZCB0byBpbmZsdWVuY2UgdGhlIGFkdmVyc2FyeeKAmXMgZGVjaXNpb24tbWFrZXJzIHRvIG1ha2UgdGhlIHdyb25nIGRlY2lzaW9ucyBvciB0byB3YXN0ZSByZXNvdXJjZXMuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgcmVhc3N1cmUtZGV0YWlsIG1hdHJpeC1kZXRhaWxzIGV0X3BiX2d1dHRlcnMxIGV0X2hhZF9hbmltYXRpb24iIHN0eWxlPSJkaXNwbGF5OiBub25lOyI+CiAgICA8ZGl2IGNsYXNzPSJldF9wYl9jb2x1bW4gZXRfcGJfY29sdW1uXzRfNCBldF9wYl9jb2x1bW5fNSBldF9wYl9jc3NfbWl4X2JsZW5kX21vZGVfcGFzc3Rocm91Z2ggZXQtbGFzdC1jaGlsZCI+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzAgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8aDQgY2xhc3M9ImV0X3BiX21vZHVsZV9oZWFkZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8c3BhbiBzdHlsZT0iZm9udC1zaXplOiAyMHB4ICFpbXBvcnRhbnQ7bGluZS1oZWlnaHQ6IDEgIWltcG9ydGFudDtmb250LXdlaWdodDogNjAwICFpbXBvcnRhbnQiPlJlYXNzdXJlPC9zcGFuPgogICAgICAgICAgICAgICAgICAgIDwvaDQ+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8aDU+SUQ6IEVBUDAwMDY8L2g1PgogICAgICAgICAgICAgICAgICAgICAgICA8cD5BZGQgYXV0aGVudGljaXR5IHRvIGRlY2VwdGl2ZSBjb21wb25lbnRzIHRvIGNvbnZpbmNlIGFuIGFkdmVyc2FyeSB0aGF0IGFuIGVudmlyb25tZW50IGlzIHJlYWwuPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIHJlYXNzdXJlLWxvbmctZGVzY3JpcHRpb24gZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5SZWFzc3VyYW5jZSBhY3Rpdml0aWVzIGFyZSB1c2VkIHRvIGFkZCBhdXRoZW50aWNpdHkgdG8gZGVjZXB0aXZlIGNvbXBvbmVudHMgdG8gcmVkdWNlIGFkdmVyc2FyeSBzdXNwaWNpb24gYWJvdXQgdGhlIGxlZ2l0aW1hY3kgb2YgdGhlIGVudmlyb25tZW50LiBBY3Rpdml0aWVzIGluY2x1ZGUgYWRkaW5nIHJlYWxpc3RpYyB1c2VyIGFjY291bnRzLCBmaWxlcywgc3lzdGVtIGFjdGl2aXR5LCBhbmQgYW55IG90aGVyIGNvbnRlbnQgdGhhdCBhbiBhZHZlcnNhcnkgbWlnaHQgZXhwZWN0IHRvIGZpbmQgb24gdGhlIHN5c3RlbS4gVGhlc2UgYWN0aXZpdGllcyBtYXkgYWRkIG5ldyBhcnRpZmFjdHMsIHN1Y2ggYXMgcGVyaXBoZXJhbHMgYW5kIHBvY2tldCBsaXR0ZXIsIHdoaWxlIGNvbmNlYWxpbmcgb3RoZXJzLCBzdWNoIGFzIGhvdyByZWNlbnRseSBhbiBlbnZpcm9ubWVudCB3YXMgc3Rvb2QgdXAuIElmIGRvbmUgY29ycmVjdGx5LCByZWFzc3VyaW5nIGFuIGFkdmVyc2FyeSBtYXkgaGVscCB0byBtYWtlIHRoZW0gIGZlZWwgbW9yZSBjb21mb3J0YWJsZSB1cG9uIGxhbmRpbmcgaW4gYSBuZXcgZW52aXJvbm1lbnQuIFRoaXMgaW5pdGlhbCBsZXZlbCBvZiBjb21mb3J0IGNhbiBoZWxwIGFuY2hvciB0aGUgYWR2ZXJzYXJ5IGluIHRoZSBlbnZpcm9ubWVudCwgaW5jcmVhc2luZyB0aGVpciB0b2xlcmFuY2UgdG8gZmF1bHRzIG9yIHdlYWtuZXNzZXMgZGlzY292ZXJlZCBsYXRlci48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICA8L2Rpdj4KPC9kaXY+CjxkaXYgY2xhc3M9ImV0X3BiX3JvdyBldF9wYl9yb3dfMiBtb3RpdmF0ZS1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+TW90aXZhdGU8L3NwYW4+CiAgICAgICAgICAgICAgICAgICAgPC9oND4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxoNT5JRDogRUFQMDAwNzwvaDU+CiAgICAgICAgICAgICAgICAgICAgICAgIDxwPkVuY291cmFnZSBhbiBhZHZlcnNhcnkgdG8gY29uZHVjdCBwYXJ0IG9yIGFsbCBvZiB0aGVpciBtaXNzaW9uLjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBtb3RpdmF0ZS1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+TW90aXZhdGluZyBhY3Rpdml0aWVzIGlzIHVzZWQgdG8gZW5jb3VyYWdlIGFuIGFkdmVyc2FyeSB0byBjb25kdWN0IHBhcnQgb3IgYWxsIG9mIHRoZWlyIG1pc3Npb24gYnkgcHJvdmlkaW5nIGEgdGFyZ2V0LXJpY2ggZW52aXJvbm1lbnQuIFRvIGRvIHRoaXMsIHRoZSBkZWZlbmRlciBjYW4gdXNlIHVucGF0Y2hlZCB2ZXJzaW9ucyBvZiBvcGVyYXRpbmcgc3lzdGVtcyBhbmQgc29mdHdhcmUsIHJlbW92ZSBlbmQtcG9pbnQgZGV0ZWN0aW9uIHNvZnR3YXJlLCBhbmQgdXNlIHdlYWsgcGFzc3dvcmRzLiBBZGRpdGlvbmFsbHksIHRoZSBkZWZlbmRlciBjYW4gb3BlbiBmaXJld2FsbCBwb3J0cywgYWRkIHByb3h5IGNhcGFiaWxpdGllcywgb3IgaW50cm9kdWNlIGVsZW1lbnRzIHRoYXQgYW4gYWR2ZXJzYXJ5IGNhbiBlYXNpbHkgbGV2ZXJhZ2UgdG8gYnlwYXNzIGFuIG9ic3RhY2xlIGluIHRoZWlyIG9wZXJhdGlvbnMuIEZpbmFsbHksIHRoZSBkZWZlbmRlciBjYW4gaW5jbHVkZSBlbnRpY2luZyBkYXRhIHRvIHRoZSBlbnZpcm9ubWVudCB0byBlbmNvdXJhZ2UgdGhlIGFkdmVyc2FyeSB0byBzdGVhbCB0aGUgZGF0YS48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICA8L2Rpdj4KPC9kaXY+CjxkaXYgY2xhc3M9ImV0X3BiX3JvdyBldF9wYl9yb3dfMiBleHBvc2UtZGV0YWlsIG1hdHJpeC1kZXRhaWxzIGV0X3BiX2d1dHRlcnMxIGV0X2hhZF9hbmltYXRpb24iIHN0eWxlPSJkaXNwbGF5OiBub25lOyI+CiAgICA8ZGl2IGNsYXNzPSJldF9wYl9jb2x1bW4gZXRfcGJfY29sdW1uXzRfNCBldF9wYl9jb2x1bW5fNSBldF9wYl9jc3NfbWl4X2JsZW5kX21vZGVfcGFzc3Rocm91Z2ggZXQtbGFzdC1jaGlsZCI+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzAgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8aDQgY2xhc3M9ImV0X3BiX21vZHVsZV9oZWFkZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8c3BhbiBzdHlsZT0iZm9udC1zaXplOiAyMHB4ICFpbXBvcnRhbnQ7bGluZS1oZWlnaHQ6IDEgIWltcG9ydGFudDtmb250LXdlaWdodDogNjAwICFpbXBvcnRhbnQiPkV4cG9zZTwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBFR08wMDAxPC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+UmV2ZWFsIHRoZSBwcmVzZW5jZSBvZiBvbmdvaW5nIGFkdmVyc2FyeSBvcGVyYXRpb25zLjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBleHBvc2UtbG9uZy1kZXNjcmlwdGlvbiBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPkV4cG9zZSBpcyBhYm91dCBkaXNjb3ZlcmluZyBwcmV2aW91c2x5IHVuZGV0ZWN0ZWQgYWR2ZXJzYXJpZXMgZW5nYWdpbmcgaW4gb25lIG9mIHR3byBiZWhhdmlvcnMuIEZpcnN0LCB0aGUgYWR2ZXJzYXJ5IG1heSBiZSBhdHRlbXB0aW5nIHRvIGdhaW4gYWNjZXNzIHRvIHRoZSBuZXR3b3Jrcy4gU2Vjb25kLCB0aGUgYWR2ZXJzYXJ5IG1heSBiZSBjdXJyZW50bHkgb3BlcmF0aW5nIG9uIHRoZSBuZXR3b3Jrcy4gQm90aCBjYXRlZ29yaWVzIG9mIGFkdmVyc2FyeSBiZWhhdmlvciBjb250YWluIHZ1bG5lcmFiaWxpdGllcyB0aGF0IGNhbiBiZSBhZHZhbnRhZ2VvdXMgZm9yIGEgZGVmZW5kZXIgc2Vla2luZyB0byBleHBvc2UgdGhlIGFkdmVyc2FyeS4gPC9wPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+QXMgYW4gZXhhbXBsZSBvZiBzdWNoIGEgdnVsbmVyYWJpbGl0eSwgd2hlbiBhbiBhZHZlcnNhcnkgaW50ZXJhY3RzIHdpdGggbmV0d29yayBvciBzeXN0ZW0gcmVzb3VyY2VzLCB0aGV5IGFyZSB2dWxuZXJhYmxlIHRvIHRyaWdnZXIgdHJpcHdpcmVzLiBUaGUgZGVmZW5kZXIgY2FuIG1ha2UgYW5kIGxlYWsgZmFrZSBjcmVkZW50aWFscyBib3RoIGluc2lkZSBhbmQgb3V0c2lkZSBvZiB0aGUgbmV0d29yay4gVGhlIGRlZmVuZGVyIGNhbiB0aGVuIG1vbml0b3IgZm9yIHRoZSB1c2Ugb2YgdGhlc2UgY3JlZGVudGlhbHMuIFRoZW4sIHdoZW4gYW4gYWR2ZXJzYXJ5IHVzZXMgYSBmYWtlIGNyZWRlbnRpYWwsIHRoZSBkZWZlbmRlciB3aWxsIHJlY2VpdmUgYSBoaWdoLWZpZGVsaXR5IGFsZXJ0LiBJbiBhZGRpdGlvbiwgaWYgdGhlIGNyZWRlbnRpYWxzIGFyZSB1bmlxdWUsIGEgZGVmZW5kZXIgbWF5IGJlIGFibGUgdG8gZGV0ZWN0IGhvdyBhbmQgd2hlbiBhbiBhZHZlcnNhcnkgY29sbGVjdGVkIHRoZSBjcmVkZW50aWFscy4gV2hlbmV2ZXIgYSBkZWZlbmRlciBzZWVrcyB0byBlbmdhZ2Ugd2l0aCBhbiBhZHZlcnNhcnksIG9wZXJhdGlvbmFsIHNhZmV0eSBpcyBwYXJhbW91bnQuIFRvIG1haW50YWluIHRoaXMgc2FmZXR5LCBpdCBpcyBhIGJlc3QgcHJhY3RpY2UgdG8gbW9uaXRvciBhZHZlcnNhcmllcyBhcyB0aGV5IG9wZXJhdGUgaW4gYW4gZW5nYWdlbWVudCBlbnZpcm9ubWVudC4gQWRkaXRpb25hbGx5LCB0aGUgZGVmZW5kZXIgbXVzdCBiZSBhYmxlIHRvIG9ic2VydmUgdGhlIGFkdmVyc2FyeS4gVGhlcmVmb3JlLCBjb2xsZWN0aW9uIGFuZCBkZXRlY3Rpb24gYWN0aXZpdGllcyBjYW4gb2Z0ZW4gYmUgdXRpbGl6ZWQgZXZlbiB3aGVuIGEgZGVmZW5kZXIgbWF5IGhhdmUgb3RoZXIgc3RyYXRlZ2ljIGdvYWxzIGluIG1pbmQuIDwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPkVuZ2FnZSBkZWZpbmVzIHR3byBhcHByb2FjaGVzIHRvIG1ha2UgcHJvZ3Jlc3MgdG93YXJkcyB0aGUgRXhwb3NlIGdvYWwuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+Q29sbGVjdGlvbiBhbGxvd3MgdGhlIGRlZmVuZGVyIHRvIGNhcHR1cmUgYW5kIHJldmlldyBkYXRhIHRoYXQgdGhlIGFkdmVyc2FyeSBwcm9kdWNlcyBkdXJpbmcgdGhlaXIgb3BlcmF0aW9ucy48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5EZXRlY3Rpb24gdGFrZXMgdGhpcyBjb2xsZWN0ZWQgZGF0YSBhbmQgdHVybnMgaXQgaW50byBhbiBhbGVydCB0aGF0IHRoZSBkZWZlbmRlciBjYW4gdXNlIHRvIHRoZWlyIGFkdmFudGFnZS48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5JbiBtYW55IGNhc2VzLCB0aGUgYWN0aXZpdGllcyB0aGF0IHN1cHBvcnQgc3VjaCBDb2xsZWN0aW9uIGFuZCBEZXRlY3Rpb24gYXBwcm9hY2hlcyBhcmUgYWxzbyBnb29kIGN5YmVyc2VjdXJpdHkgcHJhY3RpY2VzLiBIb3dldmVyLCBpbiBFbmdhZ2UsIHRoZXNlIGFjdGl2aXRpZXMgd2lsbCBmb2N1cyBleGNsdXNpdmVseSBvbiB0aGUgaW50ZXJzZWN0aW9uIG9mIGRlbmlhbCwgZGVjZXB0aW9uLCBhbmQgYWR2ZXJzYXJ5IGVuZ2FnZW1lbnQgdGVjaG5vbG9naWVzIGFuZCB0aGUgZGVmZW5kZXLigJlzIGFiaWxpdHkgdG8gRXhwb3NlIHRoZSBhZHZlcnNhcnkuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgYWZmZWN0LWRldGFpbCBtYXRyaXgtZGV0YWlscyBldF9wYl9ndXR0ZXJzMSBldF9oYWRfYW5pbWF0aW9uIiBzdHlsZT0iZGlzcGxheTogbm9uZTsiPgogICAgPGRpdiBjbGFzcz0iZXRfcGJfY29sdW1uIGV0X3BiX2NvbHVtbl80XzQgZXRfcGJfY29sdW1uXzUgZXRfcGJfY3NzX21peF9ibGVuZF9tb2RlX3Bhc3N0aHJvdWdoIGV0LWxhc3QtY2hpbGQiPgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8wIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGg0IGNsYXNzPSJldF9wYl9tb2R1bGVfaGVhZGVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4gc3R5bGU9ImZvbnQtc2l6ZTogMjBweCAhaW1wb3J0YW50O2xpbmUtaGVpZ2h0OiAxICFpbXBvcnRhbnQ7Zm9udC13ZWlnaHQ6IDYwMCAhaW1wb3J0YW50Ij5BZmZlY3Q8L3NwYW4+CiAgICAgICAgICAgICAgICAgICAgPC9oND4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxoNT5JRDogRUdPMDAwMjwvaDU+CiAgICAgICAgICAgICAgICAgICAgICAgIDxwPk5lZ2F0aXZlbHkgaW1wYWN0IHRoZSBhZHZlcnNhcmllcyBvcGVyYXRpb25zLjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBhZmZlY3QtbG9uZy1kZXNjcmlwdGlvbiBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPkFmZmVjdCBpcyB1bHRpbWF0ZWx5IGFib3V0IGNoYW5naW5nIHRoZSBjb3N0LXZhbHVlIHByb3Bvc2l0aW9uIGluIGN5YmVyIG9wZXJhdGlvbnMgZm9yIHRoZSBhZHZlcnNhcnkuIFRoZSBkZWZlbmRlciBtYXkgd2FudCB0byBpbmNyZWFzZSB0aGUgYWR2ZXJzYXJ54oCZcyBjb3N0IHRvIG9wZXJhdGUgb3IgZHJpdmUgZG93biB0aGUgdmFsdWUgdGhleSBkZXJpdmUgZnJvbSB0aGVpciBvcGVyYXRpb25zLiBGb3IgZXhhbXBsZSwgdGhlIGRlZmVuZGVyIGNhbiBuZWdhdGl2ZWx5IGltcGFjdCB0aGUgYWR2ZXJzYXJ54oCZcyBvbi1uZXR3b3JrIG9wZXJhdGlvbnMgdG8gZHJpdmUgdXAgdGhlIHJlc291cmNlIGNvc3Qgb2YgZG9pbmcgb3BlcmF0aW9ucyBieSBzbG93aW5nIGRvd24gb3Igc2VsZWN0aXZlbHkgcmVzZXR0aW5nIGNvbm5lY3Rpb25zIHRvIGltcGFjdCBleGZpbHRyYXRpb24uIFRoaXMgdHlwZSBvZiBhY3Rpdml0eSBpbmNyZWFzZXMgdGhlIGFkdmVyc2FyeeKAmXMgdGltZSBvbiB0YXJnZXQgYW5kIHdhc3RlcyB0aGVpciByZXNvdXJjZXMuIFRvIGRyaXZlIGRvd24gdGhlIHZhbHVlIG9mIHN0b2xlbiBkYXRhLCBhIGRlZmVuZGVyIGNvdWxkIHByb3ZpZGUgYW4gYWR2ZXJzYXJ5IGRlbGliZXJhdGVseSBjb25mbGljdGluZyBpbmZvcm1hdGlvbi4gUHJvdmlkaW5nIHN1Y2ggaW5mb3JtYXRpb24gcmVxdWlyZXMgYW4gYWR2ZXJzYXJ5IHRvIGVpdGhlciBjaG9vc2UgdG8gYmVsaWV2ZSBvbmUgcGllY2Ugb2YgZGF0YSBvdmVyIGFub3RoZXIsIGRpc3JlZ2FyZCBib3RoLCBjb2xsZWN0IG1vcmUgZGF0YSwgb3IgY29udGludWUgd2l0aCB1bmNlcnRhaW50eS4gPC9wPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+QWxsIHRoZXNlIG9wdGlvbnMgaW5jcmVhc2Ugb3BlcmF0aW9uYWwgY29zdHMgYW5kIGRlY3JlYXNlIHRoZSB2YWx1ZSBvZiBjb2xsZWN0ZWQgZGF0YS4gRW5nYWdlIGRlZmluZXMgdGhyZWUgYXBwcm9hY2hlcyB0byBtYWtlIHByb2dyZXNzIHRvd2FyZHMgdGhlIEFmZmVjdCBnb2FsLjwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPlByZXZlbnQsIGZvY3VzZXMgb24gc2V0dGluZyB1cCBtaXRpZ2F0aW9ucyB0aGF0IHN0b3Agc29tZSBwb3J0aW9uIG9mIGFuIGFkdmVyc2FyeeKAmXMgb3BlcmF0aW9u4oCZcyBmcm9tIGV2ZW4gc3RhcnRpbmcuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+RGlyZWN0LCBhdHRlbXB0cyB0byBtYW5ldXZlciBhbiBhZHZlcnNhcnkgaW50byBhIGJldHRlciBwb3NpdGlvbiBmb3IgdGhlIGRlZmVuZGVyLjwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPkRpc3J1cHQsIHNlZWtzIHRvIGNhdXNlIHByb2JsZW1zIGluIGFuIGFkdmVyc2FyeeKAmXMgb3BlcmF0aW9ucy48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICA8L2Rpdj4KPC9kaXY+CjxkaXYgY2xhc3M9ImV0X3BiX3JvdyBldF9wYl9yb3dfMiBlbGljaXQtZGV0YWlsIG1hdHJpeC1kZXRhaWxzIGV0X3BiX2d1dHRlcnMxIGV0X2hhZF9hbmltYXRpb24iIHN0eWxlPSJkaXNwbGF5OiBub25lOyI+CiAgICA8ZGl2IGNsYXNzPSJldF9wYl9jb2x1bW4gZXRfcGJfY29sdW1uXzRfNCBldF9wYl9jb2x1bW5fNSBldF9wYl9jc3NfbWl4X2JsZW5kX21vZGVfcGFzc3Rocm91Z2ggZXQtbGFzdC1jaGlsZCI+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzAgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8aDQgY2xhc3M9ImV0X3BiX21vZHVsZV9oZWFkZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8c3BhbiBzdHlsZT0iZm9udC1zaXplOiAyMHB4ICFpbXBvcnRhbnQ7bGluZS1oZWlnaHQ6IDEgIWltcG9ydGFudDtmb250LXdlaWdodDogNjAwICFpbXBvcnRhbnQiPkVsaWNpdDwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBFR08wMDAzPC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+TGVhcm4gYWJvdXQgYWR2ZXJzYXJpZXMgdGFjdGljcywgdGVjaG5pcXVlcywgYW5kIHByb2NlZHVyZXMgKFRUUHMpLjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBlbGljaXQtbG9uZy1kZXNjcmlwdGlvbiBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPkVsaWNpdCBlbmNvdXJhZ2VzIGFkdmVyc2FyaWVzIHRvIHJldmVhbCBhZGRpdGlvbmFsIG9yIG1vcmUgYWR2YW5jZWQgVFRQcyBhbmQgZ29hbHMgd2hpbGUgb3BlcmF0aW5nIGluIGRlZmVuZGVyLWNvbnRyb2xsZWQgZW5nYWdlbWVudCBlbnZpcm9ubWVudHMuIFRoZXNlIGhpZ2gtZmlkZWxpdHksIHN5bnRoZXRpYyBlbmdhZ2VtZW50IGVudmlyb25tZW50cyBhcmUgdW5pcXVlbHkgdGFpbG9yZWQgdG8gZW5nYWdlIHdpdGggc3BlY2lmaWMgYWR2ZXJzYXJpZXMuIFRoZXkgbWF5IGNvbnRhaW4gYSBjb21iaW5hdGlvbiBvZiBkb2N1bWVudHMsIGJyb3dzZXIgYXJ0aWZhY3RzLCBldGMuIHRvIHJlYXNzdXJlIGFuIGFkdmVyc2FyeSBhbmQgcmVkdWNlIHN1c3BpY2lvbi4gRnVydGhlciwgdGhleSBtYXkgb2ZmZXIgZW50aWNpbmcgZGF0YSBhbmQgZXhwbG9pdGFibGUgdnVsbmVyYWJpbGl0aWVzIHRvIG1vdGl2YXRlIGFuIGFkdmVyc2FyeSB0byBvcGVyYXRlIGluIHRoZSBkZWZlbmRlcuKAmXMgZW52aXJvbm1lbnQuIDwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPlRoZXNlIGVudmlyb25tZW50cyBjYW4gZWl0aGVyIGJlIGxlZnQgYXMgYSBkYW5nbGUsIGkuZS4sIGhvbmV5cG90LiBPdGhlciB0aW1lcywgdGhlIGRlZmVuZGVyIG1heSBzZWxmLWluZmVjdCB3aXRoIG1hbHdhcmUuIEluIGVpdGhlciBjYXNlLCBvYnNlcnZpbmcgYW4gYWR2ZXJzYXJ5IGFzIHRoZXkgb3BlcmF0ZSBjYW4gcHJvdmlkZSBvcmdhbml6YXRpb25zIHdpdGggYWN0aW9uYWJsZSBjeWJlciB0aHJlYXQgaW50ZWxsaWdlbmNlIGFuZCBwb3RlbnRpYWwgdW5kZXJzdGFuZGluZyBvZiB0aGUgYWR2ZXJzYXJ54oCZcyBnb2Fscy4gPC9wPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+RW5nYWdlIGRlZmluZXMgdHdvIGFwcHJvYWNoZXMgdG8gbWFrZSBwcm9ncmVzcyB0b3dhcmRzIHRoZSBFbGljaXQgZ29hbC48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5SZWFzc3VyYW5jZSBmb2N1c2VzIG9uIHByb3ZpZGluZyBhbiBlbnZpcm9ubWVudCB0aGF0IHJlZHVjZXMgYWR2ZXJzYXJ5IHN1c3BpY2lvbiBieSBtZWV0aW5nIGV4cGVjdGF0aW9ucyBhbmQgY3JlYXRpbmcgYW4gYXJ0aWZhY3QgcmljaCBlbnZpcm9ubWVudC48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5Nb3RpdmF0aW9uIHNlZWtzIHRvIGNyZWF0ZSBhIHRhcmdldCByaWNoIGVudmlyb25tZW50IHRoYXQgZW5jb3VyYWdlcyB0aGUgYWR2ZXJzYXJ5IHRvIGVuZ2FnZSBpbiBuZXcgVFRQcy48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICA8L2Rpdj4KPC9kaXY+CjxkaXYgY2xhc3M9ImV0X3BiX3JvdyBldF9wYl9yb3dfMiBvcGVyYXRpb25hbC1vYmplY3RpdmUtZGV0YWlsIG1hdHJpeC1kZXRhaWxzIGV0X3BiX2d1dHRlcnMxIGV0X2hhZF9hbmltYXRpb24iIHN0eWxlPSJkaXNwbGF5OiBub25lOyI+CiAgICA8ZGl2IGNsYXNzPSJldF9wYl9jb2x1bW4gZXRfcGJfY29sdW1uXzRfNCBldF9wYl9jb2x1bW5fNSBldF9wYl9jc3NfbWl4X2JsZW5kX21vZGVfcGFzc3Rocm91Z2ggZXQtbGFzdC1jaGlsZCI+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzAgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8aDQgY2xhc3M9ImV0X3BiX21vZHVsZV9oZWFkZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8c3BhbiBzdHlsZT0iZm9udC1zaXplOiAyMHB4ICFpbXBvcnRhbnQ7bGluZS1oZWlnaHQ6IDEgIWltcG9ydGFudDtmb250LXdlaWdodDogNjAwICFpbXBvcnRhbnQiPk9wZXJhdGlvbmFsIE9iamVjdGl2ZTwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBTQUMwMDAxPC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+RGVmaW5lIHRoZSBvYmplY3RpdmUgb2YgdGhlIGRlc2lyZWQgZW5kLXN0YXRlIG9mIHlvdXIgYWR2ZXJzYXJ5IGVuZ2FnZW1lbnQgb3BlcmF0aW9ucy48L3A+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzEgb3BlcmF0aW9uYWwtb2JqZWN0aXZlLWxvbmctZGVzY3JpcHRpb24gZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5UaGUgT3BlcmF0aW9uYWwgT2JqZWN0aXZlIGlzICB0aGUgZ29hbChzKSB0aGF0IGRyaXZlIGFsbCBvZiB0aGUgYXBwcm9hY2hlcyBhbmQgYWN0aXZpdGllcyB1c2VkIGluIGFuIGFkdmVyc2FyeSBlbmdhZ2VtZW50IG9wZXJhdGlvbi4gQXJ0aWN1bGF0aW5nIHRoZSBvcGVyYXRpb25hbCBvYmplY3RpdmUgYWxsb3dzIHRoZSBkZWZlbmRlciB0byBhbGlnbiB0aGVpciBhY3Rpb25zIHRvIHJlYWNoIHRoZSBkZXNpcmVkIGVuZC1zdGF0ZS4gVGhlcmUgYXJlIHRocmVlIGhpZ2gtbGV2ZWwgRW5nYWdlbWVudCBHb2FscyBpbiBhZHZlcnNhcnkgZW5nYWdlbWVudCBvcGVyYXRpb25zOiB0byBFeHBvc2UgYWR2ZXJzYXJpZXMgb24gdGhlIG5ldHdvcmssIHRvIEFmZmVjdCBhZHZlcnNhcmllcyBvbiB0aGUgbmV0d29yaywgb3IgdG8gRWxpY2l0IG5ldyBpbmZvcm1hdGlvbiBhYm91dCBhZHZlcnNhcmllcy4gIFRoZXNlIGxhcmdlciB0aGVtZXMgc2hvdWxkIGhlbHAgdGhlIGRlZmVuZGVyIGNyZWF0ZSBtb3JlIGZvY3VzZWQgb3BlcmF0aW9uYWwgb2JqZWN0aXZlcy4gRm9yIGV4YW1wbGUsIHJlYWxpc3RpYyBvcGVyYXRpb25hbCBvYmplY3RpdmVzIGluY2x1ZGU6IHByb3RlY3RpbmcgYSBzcGVjaWZpYyBoaWdoLXZhbHVlIHRlY2hub2xvZ3kgb3IgcGVyc29uIGJ5IGV4cG9zaW5nIGFkdmVyc2FyaWVzIHRhcmdldGluZyB0aGF0IHRlY2hub2xvZ3kgb3IgcGVyc29uLCBwcm90ZWN0aW5nIGFnYWluc3QgaW5zaWRlciB0aHJlYXRzIGJ5IGFmZmVjdGluZyB0aGUgYWR2ZXJzYXJ54oCZcyBhYmlsaXR5IHRvIHN0ZWFsIHNlbnNpdGl2ZSBkYXRhLCBvciBpbmNyZWFzaW5nIHRoZSBkZWZlbmRlcuKAmXMgdW5kZXJzdGFuZGluZyBvZiB0aGUgdGhyZWF0IGxhbmRzY2FwZSBieSBlbGljaXRpbmcgbmV3IGFkdmVyc2FyeSBUVFBzLCBldGMuIEV2ZXJ5IGFjdGlvbiB0YWtlbiBpbiB0aGUgcGxhbm5pbmcsIGV4ZWN1dGlvbiwgYW5kIGFuYWx5c2lzIG9mIGFuIG9wZXJhdGlvbiBzaG91bGQgYmUgYWxpZ25lZCB3aXRoIHRoZSBvcGVyYXRpb25hbCBvYmplY3RpdmUuIEl0IGlzIGltcG9ydGFudCB0byBkZWZpbmUgdGhpcyBvYmplY3RpdmUgZWFybHkgb24uIElucHV0IGZyb20gYW55IGludm9sdmVkIHN0YWtlaG9sZGVycyBzaG91bGQgYmUgY29uc2lkZXJlZCB3aGVuIGNob29zaW5nIHRoZSBvcGVyYXRpb25hbCBvYmplY3RpdmVzLiAgPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMiBvcGVyYXRpb25hbC1vYmplY3RpdmUtcmVmZXJlbmNlcyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InR0YWJsZSB0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBSZWZlcmVuY2UgTGlua3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vYXJ4aXYub3JnL3BkZi8yMTA0LjAzNTk0LnBkZiIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPlRocmVlIERlY2FkZXMgT2YgRGVjZXB0aW9uIFRlY2huaXF1ZXMgSW4gQWN0aXZlIEN5YmVyIERlZmVuc2UtUmV0cm9zcGVjdCBBbmQgT3V0bG9vazwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgcGVyc29uYS1jcmVhdGlvbi1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+UGVyc29uYSBDcmVhdGlvbjwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBTQUMwMDAyPC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+UGxhbiBhbmQgY3JlYXRlIGEgZmljdGl0aW91cyBodW1hbiB1c2VyIHRocm91Z2ggYSBjb21iaW5hdGlvbiBvZiBwbGFudGVkIGRhdGEgYW5kIHJldmVhbGVkIGJlaGF2aW9yIHBhdHRlcm5zLjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBwZXJzb25hLWNyZWF0aW9uLWxvbmctZGVzY3JpcHRpb24gZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5QZXJzb25hIENyZWF0aW9uIGlzIHRoZSBwcm9jZXNzIG9mIHBsYW5uaW5nIGZvciBhbmQgY3JlYXRpbmcgdGhlIHBlcnNvbmFzIHJlcXVpcmVkIHRvIHN1cHBvcnQgdGhlIGVuZ2FnZW1lbnQgbmFycmF0aXZlLiBUaGlzIHByb2Nlc3Mgc2hvdWxkIGJlIGluZm9ybWVkIGJ5IHRoZSBwcmV2aW91c2x5IGdlbmVyYXRlZCB0aHJlYXQgbW9kZWwgZm9yIHRoZSBkZWZlbmRlcuKAmXMgdGFyZ2V0IGFkdmVyc2FyeS4gRm9yIGV4YW1wbGUsIGlmIHRoZSBhZHZlcnNhcnkgdGFyZ2V0cyBhIHNwZWNpZmljIGluZHVzdHJ5LCB0aGUgcGVyc29uYSBtaWdodCBiZSBjcmVhdGVkIHRvIGxvb2sgbGlrZSBzb21lb25lIHdobyB3b3JrcyBpbiB0aGF0IGluZHVzdHJ5LiBUaGUgcGVyc29uYSBvdXRsaW5lIHNob3VsZCBpbmNsdWRlIGJhc2ljIGluZm9ybWF0aW9uIGFib3V0IHRoZSBwZXJzb25hIGl0c2VsZiBzdWNoIGFzIHRoZWlyIG5hbWUsIHRoZWlyIHJlbGF0aW9uc2hpcCB0byB0aGUgZW52aXJvbm1lbnQsIGFuZCBnZW9ncmFwaGljIGxvY2F0aW9uLiBPZnRlbiwgYW5kIGVzcGVjaWFsbHkgZm9yIGEgc2hvcnQtdGVybSBlbmdhZ2VtZW50IG9wZXJhdGlvbiwgdGhlc2UgcGVyc29uYSB0cmFpdHMgY2FuIGJlIGJyb2FkLiAgRm9yIGV4YW1wbGUsIGl0IGlzIHVubGlrZWx5IHRoYXQgYSBwZXJzb25hIHVzZWQgaW4gYSBzaG9ydC10ZXJtIHJhbnNvbXdhcmUgZGV0b25hdGlvbiBvcGVyYXRpb24gd291bGQgcmVxdWlyZSBhIGxvdCBvZiBkZXRhaWxzIHRvIGJlIGVmZmVjdGl2ZS4gSG93ZXZlciwgZm9yIGEgbG9uZ2VyLXRlcm0gaW5zaWRlciB0aHJlYXQgcHJvdGVjdGlvbiBvcGVyYXRpb24sIHRoZSBkZWZlbmRlciBtYXkgbmVlZCB0byBjcmVhdGUgYSBwZXJzb25hIHdpdGggdGhlIG9ubGluZSBwcmVzZW5jZSBvZiBhIGNvcnBvcmF0ZSBlbXBsb3llZSwgaW5jbHVkaW5nIG5hbWUsIGJpcnRoZGF5LCBhZGRyZXNzLCBldGMuIE1hbnkgZmFjdG9ycyBzaG91bGQgYmUgY29uc2lkZXJlZCB3aGVuIGRldGVybWluaW5nIGhvdyBpbi1kZXB0aCBhIHBlcnNvbmEgc2hvdWxkIGJlLCBpbmNsdWRpbmcgYWR2ZXJzYXJ5IHNvcGhpc3RpY2F0aW9uLCBkZWZlbmRlciByZXNvdXJjZXMsIGFuZCBlbmdhZ2VtZW50IG5hcnJhdGl2ZS4gIE9uY2UgdGhlIHBlcnNvbmEgdHJhaXRzIGhhdmUgYmVlbiBkZWNpZGVkLCB0aGUgcGxhbm5pbmcgcHJvY2VzcyBzaG91bGQgZGV0ZXJtaW5lIGhvdyB0aGVzZSB0cmFpdHMgd2lsbCBtYW5pZmVzdCBpbiB0aGUgZW52aXJvbm1lbnQuIFBlcnNvbmEgY3JlYXRpb24gaXMgaW1wb3J0YW50IHRvIHJ1bm5pbmcgYW4gb3BlcmF0aW9uLCBhcyBwZXJzb25hcyBhcmUgb2Z0ZW4gdGhlIHByZWRvbWluYW50IG1lYW5zIHRocm91Z2ggd2hpY2ggdGhlIGRlZmVuZGVyIGNhbiBlbmdhZ2Ugd2l0aCB0aGUgYWR2ZXJzYXJ5IG9yIGNoYW5nZSB0aGUgZW52aXJvbm1lbnQgZHVyaW5nIHRoZSBvcGVyYXRpb24uIENhcmVmdWwgcGxhbm5pbmcgaXMgaW1wb3J0YW50IGFzIHBlcnNvbmFzIGNhbiBiZSByZXNvdXJjZSBpbnRlbnNpdmUgdG8gY3JlYXRlIGFuZCBtYWludGFpbiBhbmQgY2FuIHJldmVhbCB0aGUgcnVzZSBpZiBkaXNjb3ZlcmVkIGFzIGZha2UgYnkgdGhlIGFkdmVyc2FyeS4gPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgc3Rvcnlib2FyZGluZy1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+U3Rvcnlib2FyZGluZzwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBTQUMwMDAzPC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+UGxhbiBhbmQgY3JlYXRlIHRoZSBkZWNlcHRpb24gc3RvcnkuPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIHN0b3J5Ym9hcmRpbmctbG9uZy1kZXNjcmlwdGlvbiBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPlN0b3J5Ym9hcmRpbmcgaXMgdGhlIHByb2Nlc3Mgb2YgY3JlYXRpbmcgdGhlIGRlY2VwdGlvbiBzdG9yeSB0aHJvdWdoIGEgc2VxdWVuY2Ugb2YgZXZlbnRzLCBpbnRlcmFjdGlvbnMsIHRoZSBwZXJzb25h4oCZcyBwYXR0ZXJuIG9mIGxpZmUsIGV0Yy4gQSBsYXJnZSBwYXJ0IG9mIFN0b3J5Ym9hcmRpbmcgaXMgY3JlYXRpbmcgdGhpcyBwYXR0ZXJuIG9mIGxpZmUgZm9yIHRoZSBwZXJzb25hKHMpIHVzaW5nIHRoZSBzeXN0ZW0ocykuIFRoZSBwYXR0ZXJuIG9mIGxpZmUgY2FuIGluY2x1ZGUgYmVoYXZpb3JzIHN1Y2ggYXMgdXNpbmcgZW1haWwgb3IgY2hhdCBzb2Z0d2FyZSwgYnJvd3NpbmcgdGhlIEludGVybmV0LCB1c2luZyBzeXN0ZW0gc29mdHdhcmUsIG9yIHBoeXNpY2FsbHkgbW92aW5nIHRoZSBkZXZpY2UgKHBhcnRpY3VsYXJseSBpbXBvcnRhbnQgZm9yIG1vYmlsZSBkZXZpY2VzIGFuZCBsYXB0b3BzKS4gIFRoZSBkZWZlbmRlciBtdXN0IGRldGVybWluZSBob3cgdGhlIFBlcnNvbmHigJlzIGJlaGF2aW9yIGFuZCBvdGhlciBldmVudHMgaW4gdGhlIGVudmlyb25tZW50IHdpbGwgYmUgZ2VuZXJhdGVkLiBQZXJzb25hcyBtYXkgYmUgZ2VuZXJhdGVkIGF1dG9tYXRpY2FsbHkgd2l0aCB0b29saW5nLCBtYW51YWxseSB3aXRoIGh1bWFuIG9wZXJhdG9ycywgb3Igc29tZSBjb21iaW5hdGlvbiBvZiBib3RoLiBUaGUgYXZhaWxhYmlsaXR5IG9mIGRlZmVuZGVyIHJlc291cmNlcyBtYXkgZ3JlYXRseSBpbXBhY3QgdGhlIGZyZXF1ZW5jeSBvZiBtYW51YWxseSBleGVjdXRpbmcgYmVoYXZpb3JzLiAgTm90IGV2ZXJ5IGFjdGlvbiB0YWtlbiBpbiB0aGUgZW52aXJvbm1lbnQgbmVlZHMgdG8gYmUgcGxhbm5lZCBpbiBhZHZhbmNlLiBIb3dldmVyLCB0aGUgZGVmZW5kZXIgc2hvdWxkIGhhdmUgYSBnZW5lcmFsIGlkZWEgb2Ygd2hhdCBhY3Rpb25zIHdpbGwgYmUgdGFrZW4uIFNldHRpbmcgdXAgYSBzdG9yeWJvYXJkIGVhcmx5IGluIHRoZSBwbGFubmluZyBwcm9jZXNzIHdpbGwgYWxsb3cgdGhlIG9wZXJhdGlvbiB0byBydW4gc21vb3RobHksIGVmZmljaWVudGx5LCBhbmQgbW9zdCBpbXBvcnRhbnRseSwgY29uc2lzdGVudGx5LCByZWdhcmRsZXNzIG9mIG9wZXJhdG9yLCBzbyBhcyBub3QgdG8gcmV2ZWFsIHRoZSBydXNlLjwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgc3Rvcnlib2FyZGluZy1yZWZlcmVuY2VzIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idHRhYmxlIHRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIFJlZmVyZW5jZSBMaW5rcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cHM6Ly9yZXBvc2l0b3J5LmxpYi5uY3N1LmVkdS9iaXRzdHJlYW0vaGFuZGxlLzE4NDAuMTYvNTY0OC9ldGQucGRmIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+RGVmZW5zaXZlIENvbXB1dGVyLVNlY3VyaXR5IERlY2VwdGlvbiBPcGVyYXRpb25zOiBQcm9jZXNzZXMsIFByaW5jaXBsZXMgQW5kIFRlY2huaXF1ZXM8L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vYXBwcy5kdGljLm1pbC9zdGkvcGRmcy9BREE1MjczMjgucGRmIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+RHVwaW5nIFRoZSBTb3ZpZXRzOiBUaGUgRmFyZXdlbGwgRG9zc2llcjwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgY3liZXItdGhyZWF0LWludGVsbGlnZW5jZS1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+Q3liZXIgVGhyZWF0IEludGVsbGlnZW5jZTwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBTQUMwMDA0PC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+VGhlIHByb2Nlc3Mgb2YgYW5hbHl6aW5nIGFjdGlvbmFibGUga25vd2xlZGdlIGFib3V0IGFkdmVyc2FyaWVzIGFuZCB0aGVpciBtYWxpY2lvdXMgYWN0aXZpdGllcywgZW5hYmxpbmcgZGVmZW5kZXJzIGFuZCB0aGVpciBvcmdhbml6YXRpb25zIHRvIHJlZHVjZSBoYXJtIHRocm91Z2ggYmV0dGVyIHNlY3VyaXR5IGRlY2lzaW9uLW1ha2luZzwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBjeWJlci10aHJlYXQtaW50ZWxsaWdlbmNlLWxvbmctZGVzY3JpcHRpb24gZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5DeWJlciBUaHJlYXQgSW50ZWxsaWdlbmNlIChDVEkpIGFsbG93cyBhbiBvcmdhbml6YXRpb24gdG8gdW5kZXJzdGFuZCB0aGUgdGhyZWF0IGxhbmRzY2FwZS4gQ1RJIGRhdGEgY2FuIGJlIGluZm9ybWVkIGJ5IGEgY29tYmluYXRpb24gb2Ygb3BlbiBhbmQgY2xvc2VkIHNvdXJjZSByZXNlYXJjaC4gQWRkaXRpb25hbGx5LCBpdCBjYW4gYmUgc3VwcGxlbWVudGVkIHdpdGggaW50ZXJuYWwgYW5kIGV4dGVybmFsIHRocmVhdCBpbnRlbGxpZ2VuY2UgZmVlZHMsIGluY2x1ZGluZyBpbmZvcm1hdGlvbiBnbGVhbmVkIGZyb20gcHJldmlvdXMgZW5nYWdlbWVudCBvcGVyYXRpb25zLiAgVGhlIHVuZGVyc3RhbmRpbmcgZ2FpbmVkIHRocm91Z2ggQ1RJIGRhdGEgYWxsb3dzIHRoZSBkZWZlbmRlciB0byBpZGVudGlmeSBhbmQgdW5kZXJzdGFuZCB0aGUgdGFyZ2V0IGFkdmVyc2FyeSBmb3IgYSBnaXZlbiBvcGVyYXRpb24uIEZvciBleGFtcGxlLCBpZiB0aGUgZGVmZW5kZXLigJlzIGludGVuZGVkIG9wZXJhdGlvbmFsIG91dGNvbWUgaXMgdG8gZXhwb3NlIGFkdmVyc2FyaWVzIG9uIHRoZSBuZXR3b3JrLCB0aGUgZGVmZW5kZXIgc2hvdWxkIHByaW9yaXRpemUgYWR2ZXJzYXJpZXMgdGhhdCBoaXN0b3JpY2FsbHkgdGFyZ2V0IHRoZWlyIG9yZ2FuaXphdGlvbiBvciBzaW1pbGFyIG9yZ2FuaXphdGlvbnMgYW5kL29yIGhhdmUgZGlzcGxheWVkIFRUUHMgdGhhdCBhcmUgbGlrZWx5IHRvIGV2YWRlIGN1cnJlbnQgZGVmZW5zZXMuIEFkZGl0aW9uYWxseSwgc3Rvcnlib2FyZGluZyBzaG91bGQgbG9vayBhdCBDVEkgZGF0YSBmb3IgdGhlIHRhcmdldCBhZHZlcnNhcnkgdG8gbWFrZSBpbmZvcm1lZCBlc3RpbWF0aW9ucyBvbiB3aGF0IHRoZSBhZHZlcnNhcnkgbWF5IGRvIGluIHRoZSBlbnZpcm9ubWVudCBhbmQgaG93IHRoZXkgbWlnaHQgcmVhY3QgdG8gd2hhdCB0aGV5IGZpbmQuICBPbmNlIG9uZSBvciBtb3JlIGFkdmVyc2FyaWVzIGhhdmUgYmVlbiBzZWxlY3RlZCBhcyB0aGUgdGFyZ2V0IGFkdmVyc2FyeSwgdGhlIHJlbGV2YW50IENUSSBkYXRhIHNob3VsZCBndWlkZSB0aGUgY3JlYXRpb24gb2YgdGhlIGVuZ2FnZW1lbnQgZW52aXJvbm1lbnQgYW5kIHN0b3J5Ym9hcmQgaW5jbHVkaW5nIGhhcmR3YXJlIGFuZCBzb2Z0d2FyZSByZXF1aXJlbWVudHMsIHRoZSByZXF1aXJlZCBsZXZlbCBvZiByZWFsaXNtIGZvciBsdXJlcyBhbmQgcG9ja2V0IExpdHRlciwgYW5kIGFjY2VwdGFibGUgb3BlcmF0aW9uYWwgcmlzay4gVGhpcyBkZWZpbml0aW9uIHdhcyBiYXNlZCBvbiB0aGUgd29yayBwcmVzZW50ZWQgYnkgTUlUUkUgQVRUJmFtcDtDSyBhcyBzZWVuIGhlcmUuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMiBjeWJlci10aHJlYXQtaW50ZWxsaWdlbmNlLXJlZmVyZW5jZXMgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0dGFibGUgdGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgUmVmZXJlbmNlIExpbmtzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwOi8vY2l0ZXNlZXJ4LmlzdC5wc3UuZWR1L3ZpZXdkb2MvZG93bmxvYWQ/ZG9pPTEwLjEuMS4xMDYuNzQ3NiZhbXA7cmVwPXJlcDEmYW1wO3R5cGU9cGRmIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+RGVjZWl2ZWQ6IFVuZGVyIFRhcmdldCBPbmxpbmU8L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vdngtdW5kZXJncm91bmQub3JnL2FyY2hpdmUvb3RoZXIvVnhIZWF2ZW5QZGZzL0EgYm9vc3RpbmcgZW5zZW1ibGUgZm9yIHRoZSByZWNvZ25pdGlvbiBvZiBjb2RlIHNoYXJpbmcgaW4gbWFsd2FyZS5wZGYiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5BIEJvb3N0aW5nIEVuc2VtYmxlIEZvciBUaGUgUmVjb2duaXRpb24gT2YgQ29kZSBTaGFyaW5nIEluIE1hbHdhcmU8L2E+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90ZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vd3d3LmFjYWRlbWlhLmVkdS9kb3dubG9hZC82NjEwODI5MC9DVElfTWF2cm9laWRpcy5wZGYiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5DeWJlciBUaHJlYXQgSW50ZWxsaWdlbmNlIE1vZGVsOiBBbiBFdmFsdWF0aW9uIE9mIFRheG9ub21pZXMsIFNoYXJpbmcgU3RhbmRhcmRzLCBBbmQgT250b2xvZ2llcyBXaXRoaW4gQ3liZXIgVGhyZWF0IEludGVsbGlnZW5jZTwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgZ2F0aW5nLWNyaXRlcmlhLWRldGFpbCBtYXRyaXgtZGV0YWlscyBldF9wYl9ndXR0ZXJzMSBldF9oYWRfYW5pbWF0aW9uIiBzdHlsZT0iZGlzcGxheTogbm9uZTsiPgogICAgPGRpdiBjbGFzcz0iZXRfcGJfY29sdW1uIGV0X3BiX2NvbHVtbl80XzQgZXRfcGJfY29sdW1uXzUgZXRfcGJfY3NzX21peF9ibGVuZF9tb2RlX3Bhc3N0aHJvdWdoIGV0LWxhc3QtY2hpbGQiPgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8wIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGg0IGNsYXNzPSJldF9wYl9tb2R1bGVfaGVhZGVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4gc3R5bGU9ImZvbnQtc2l6ZTogMjBweCAhaW1wb3J0YW50O2xpbmUtaGVpZ2h0OiAxICFpbXBvcnRhbnQ7Zm9udC13ZWlnaHQ6IDYwMCAhaW1wb3J0YW50Ij5HYXRpbmcgQ3JpdGVyaWE8L3NwYW4+CiAgICAgICAgICAgICAgICAgICAgPC9oND4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxoNT5JRDogU0FDMDAwNTwvaDU+CiAgICAgICAgICAgICAgICAgICAgICAgIDxwPkRlZmluZSB0aGUgc2V0IG9mIGV2ZW50cyB0aGF0IHdvdWxkIGxlYWQgdG8gdGhlIHVubmVnb3RpYWJsZSBwYXVzZSBvciBjb25jbHVzaW9uIHRvIHRoZSBvcGVyYXRpb24uPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIGdhdGluZy1jcml0ZXJpYS1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+R2F0aW5nIENyaXRlcmlhIGFyZSB0aGUgZXZlbnQgb3Igc2VxdWVuY2Ugb2YgZXZlbnRzIHRoYXQgYXJlIGFncmVlZCB0byBiZSB0aGUgdW5uZWdvdGlhYmxlIGltbWVkaWF0ZSBwYXVzZSBvciBlbmQgdG8gdGhlIG9wZXJhdGlvbi4gU29tZXRpbWVzLCB0aGVzZSBldmVudHMgaW5jbHVkZSB0aGUgc3VjY2Vzc2Z1bCBjb21wbGV0aW9uIG9mIHRoZSBhZ3JlZWQgdXBvbiBvcGVyYXRpb25hbCBvYmplY3RpdmVzLiBPdGhlciB0aW1lcywgdGhlc2UgZXZlbnRzIG1heSBzaWduaWZ5IHRoZSBvcGVyYXRpb24gaGFzIHJlYWNoZWQgYSBoYXJkIHN0b3AuIFRoaXMgc3RvcCBpcyBvZnRlbiBuZWNlc3NhcnkgYmVjYXVzZSBmdXR1cmUgb3BlcmF0aW9uYWwgc2FmZXR5IGNhbm5vdCBiZSBndWFyYW50ZWVkLiBBbHRlcm5hdGl2ZWx5LCB0aGUgb3BlcmF0aW9uIG1heSBuZWVkIHRvIGVuZCBiZWNhdXNlIGV2ZW50cyBoYXZlIG9jY3VycmVkIHRoYXQgb3V0d2VpZ2ggdGhlIGFncmVlZCB1cG9uIGFjY2VwdGFibGUgcmlzay4gRmluYWxseSwgaXQgbWF5IGp1c3QgYmUgdGhhdCBpZiB0aGUgYWR2ZXJzYXJ5IG9wZXJhdGVzIGFueSBsb25nZXIsIHRoZXkgbWF5IGxlYXJuIHNvbWV0aGluZyB0aGUgZGVmZW5kZXIgZG9lc27igJl0IHdhbnQgdGhlbSB0byBrbm93LiAgTXVsdGlwbGUgcGFydGllcyBmcm9tIHRoZSB0ZWNobmljYWwgb3BlcmF0aW9ucywgdGhyZWF0IGludGVsLCBsZWdhbCwgYW5kIG1hbmFnZW1lbnQgcGVyc3BlY3RpdmVzIHNob3VsZCBiZSBpbmNsdWRlZCB3aGVuIGRlZmluaW5nIEdhdGluZyBDcml0ZXJpYS4gRm9yIGV4YW1wbGUsIGlmIGFuIGFkdmVyc2FyeSBiZWdpbnMgdG8gdXNlIHRoZSBlbmdhZ2VtZW50IGVudmlyb25tZW50IGFzIGEgcGxhdGZvcm0gdG8gb3BlcmF0ZSBhZ2FpbnN0IG90aGVyIHRhcmdldHMsIHN0YWtlaG9sZGVycyBtYXkgZGVjaWRlIHRoYXQgdGhlIG9wZXJhdGlvbiBtdXN0IGJlIHN1c3BlbmRlZCB1bnRpbCB0aGUgdW5hY2NlcHRhYmxlIHRyYWZmaWMgY2FuIGJlIGJsb2NrZWQuIERlZmluaW5nIHRoZSBvcGVyYXRpb25hbCBHYXRpbmcgQ3JpdGVyaWEgaXMgYW4gZXNzZW50aWFsIHN0ZXAgdG8gZW5zdXJlIG9wZXJhdGlvbmFsIHNhZmV0eS48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICA8L2Rpdj4KPC9kaXY+CjxkaXYgY2xhc3M9ImV0X3BiX3JvdyBldF9wYl9yb3dfMiBhZnRlci1hY3Rpb24tcmV2aWV3LWRldGFpbCBtYXRyaXgtZGV0YWlscyBldF9wYl9ndXR0ZXJzMSBldF9oYWRfYW5pbWF0aW9uIiBzdHlsZT0iZGlzcGxheTogbm9uZTsiPgogICAgPGRpdiBjbGFzcz0iZXRfcGJfY29sdW1uIGV0X3BiX2NvbHVtbl80XzQgZXRfcGJfY29sdW1uXzUgZXRfcGJfY3NzX21peF9ibGVuZF9tb2RlX3Bhc3N0aHJvdWdoIGV0LWxhc3QtY2hpbGQiPgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8wIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGg0IGNsYXNzPSJldF9wYl9tb2R1bGVfaGVhZGVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4gc3R5bGU9ImZvbnQtc2l6ZTogMjBweCAhaW1wb3J0YW50O2xpbmUtaGVpZ2h0OiAxICFpbXBvcnRhbnQ7Zm9udC13ZWlnaHQ6IDYwMCAhaW1wb3J0YW50Ij5BZnRlci1BY3Rpb24gUmV2aWV3PC9zcGFuPgogICAgICAgICAgICAgICAgICAgIDwvaDQ+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8aDU+SUQ6IFNBQzAwMDY8L2g1PgogICAgICAgICAgICAgICAgICAgICAgICA8cD5SZXZpZXcgb2Ygb3BlcmF0aW9uYWwgYWN0aXZpdGllcy48L3A+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzEgYWZ0ZXItYWN0aW9uLXJldmlldy1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+VGhlIEFmdGVyIEFjdGlvbiBSZXZpZXcgKEFBUikgaXMgdGhlIG9wcG9ydHVuaXR5IGZvciB0aGUgdGVhbSB0byByZXZpZXcgdGhlIGV2ZW50cyBvZiB0aGUgb3BlcmF0aW9uIHRvIGVuc3VyZSBwcm9ncmVzcyB0b3dhcmRzIHN0cmF0ZWdpYyBvdXRjb21lcy4gVGhpcyByZXRyb3NwZWN0aXZlIGNhbiBpbmNsdWRlIGEgcmV2aWV3IG9mIHRoZSBlbnRpcmUgb3BlcmF0aW9uYWwgcHJvY2VzcyBmcm9tIHBsYW5uaW5nLCBpbXBsZW1lbnRhdGlvbiwgZXhlY3V0aW9uLCBhbmQgaW1wYWN0LiBJbiBhZGRpdGlvbiB0byB0aGUgb3BlcmF0aW9uIGl0c2VsZiwgdGhlIEFBUiBpcyBhbiBpbXBvcnRhbnQgdGltZSB0byBhc3Nlc3MgdGhlIGNvbW11bmljYXRpb24gYW5kIHRlYW13b3JrIG9mIHRoZSBvcGVyYXRpb25zIHRlYW0gYW5kIGFsbCBjb250cmlidXRpbmcgc3Rha2Vob2xkZXJzLiBXaGlsZSBhbiBBQVIgc2hvdWxkIGFsd2F5cyBvY2N1ciBhdCB0aGUgZW5kIG9mIGFuIG9wZXJhdGlvbiwgcGVyaW9kaWMgcmV2aWV3cyBkdXJpbmcgbG9uZy1ydW5uaW5nIG9wZXJhdGlvbnMgYXJlIHZpdGFsIHRvIGVuc3VyZSBhbGlnbm1lbnQgYW5kIHByb2dyZXNzIHRvd2FyZHMgdGhlIG9wZXJhdGlvbmFsIG9iamVjdGl2ZXMuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMiBhZnRlci1hY3Rpb24tcmV2aWV3LXJlZmVyZW5jZXMgZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRhYmxlIGNsYXNzPSJ0dGFibGUgdGFibGUgdGFibGUtYm9yZGVyZWQgdGFibGUtaG92ZXIiIHN0eWxlPSJoZWlnaHQ6IDI2MHB4O2JvcmRlci1zcGFjaW5nOiAwcHgiIGNlbGxwYWRkaW5nPSIwIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiAyM3B4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aCBzdHlsZT0iaGVpZ2h0OiAyM3B4O3dpZHRoOiAyNDkuMDE2cHg7dGV4dC1hbGlnbjogbGVmdCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgUmVmZXJlbmNlIExpbmtzCiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGhlYWQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwOi8vdW5kZXJzdGFuZGluZ3JlcXVpcmVtZW50cy5jb20vcmVzb3VyY2VzLzcuNCAgU3RyYXRlZ2llcyBmb3IgTGVhcm5pbmcgZnJvbSBGYWlsdXJlLnBkZiIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPlN0cmF0ZWdpZXMgRm9yIExlYXJuaW5nIEZyb20gRmFpbHVyZTwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgdGhyZWF0LW1vZGVsLWRldGFpbCBtYXRyaXgtZGV0YWlscyBldF9wYl9ndXR0ZXJzMSBldF9oYWRfYW5pbWF0aW9uIiBzdHlsZT0iZGlzcGxheTogbm9uZTsiPgogICAgPGRpdiBjbGFzcz0iZXRfcGJfY29sdW1uIGV0X3BiX2NvbHVtbl80XzQgZXRfcGJfY29sdW1uXzUgZXRfcGJfY3NzX21peF9ibGVuZF9tb2RlX3Bhc3N0aHJvdWdoIGV0LWxhc3QtY2hpbGQiPgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8wIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGg0IGNsYXNzPSJldF9wYl9tb2R1bGVfaGVhZGVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4gc3R5bGU9ImZvbnQtc2l6ZTogMjBweCAhaW1wb3J0YW50O2xpbmUtaGVpZ2h0OiAxICFpbXBvcnRhbnQ7Zm9udC13ZWlnaHQ6IDYwMCAhaW1wb3J0YW50Ij5UaHJlYXQgTW9kZWw8L3NwYW4+CiAgICAgICAgICAgICAgICAgICAgPC9oND4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxoNT5JRDogU0FDMDAwOTwvaDU+CiAgICAgICAgICAgICAgICAgICAgICAgIDxwPkEgcmlzayBhc3Nlc3NtZW50IHRoYXQgbW9kZWxzIG9yZ2FuaXphdGlvbmFsIHN0cmVuZ3RocyBhbmQgd2Vha25lc3NlcyDCoMKgPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIHRocmVhdC1tb2RlbC1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+QW1vbmcgb3RoZXIgdGhpbmdzLCB0aHJlYXQgbW9kZWxzIHJlcXVpcmUgdGhhdCB0aGUgZGVmZW5kZXIgYXNzZXNzZXMgdGhlIHN0cmVuZ3Rocywgd2Vha25lc3NlcywgYW5kIGltcG9ydGFuY2Ugb2YgdGhlIHRoZWlyIG93biBvcmdhbml6YXRpb24sIGluY2x1ZGluZyB0cnVzdGVkIHBhcnRuZXJzLCBpbmZyYXN0cnVjdHVyZSwgYW5kIGNyaXRpY2FsIGN5YmVyIGFzc2V0cy4gVGhpcyB1bmRlcnN0YW5kaW5nIHdpbGwgaW5mb3JtIG9wZXJhdGlvbmFsIG9iamVjdGl2ZXMgYnkgb3V0bGluaW5nIHRoZSBkZWZlbmRlcuKAmXMgYXR0YWNrIHN1cmZhY2UgYW5kIGhpZ2hsaWdodGluZyBhcmVhcyB0aGF0IG1heSBiZSBvZiBwYXJ0aWN1bGFyIGludGVyZXN0IHRvIGEgZ2l2ZW4gYWR2ZXJzYXJ5LiBUaGUgb3JnYW5pemF0aW9u4oCZcyB0aHJlYXQgbW9kZWwgc2hvdWxkIGJlIHVuZGVyc3Rvb2QgYXQgdGhlIG9uc2V0IG9mIGFuIG9wZXJhdGlvbiB0byBkcml2ZSBvcGVyYXRpb25hbCBvYmplY3RpdmUgZGV2ZWxvcG1lbnQgYW5kIHJldmlzaXRlZCBhdCB0aGUgY29uY2x1c2lvbiBvZiBhbiBvcGVyYXRpb24gdG8gZW5zdXJlIG9wZXJhdGlvbmFsIG91dGNvbWVzIGFyZSBjYXB0dXJlZC4gVGhlc2UgcHJvY2VzcyBvZiBkZWZpbmluZyBhbmQgaW5mb3JtaW5nIHRoZSBvcmdhbml6YXRpb27igJlzIHRocmVhdCBtb2RlbCBzaG91bGQgZW5hYmxlIGJldHRlciBzZWN1cml0eSBkZWNpc2lvbi1tYWtpbmcgYm90aCBpbiBmdXR1cmUgb3BlcmF0aW9ucyBhbmQgZWxzZXdoZXJlIGluIHRoZSBvcmdhbml6YXRpb24uPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgZW5nYWdlbWVudC1lbnZpcm9ubWVudC1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+RW5nYWdlbWVudCBFbnZpcm9ubWVudDwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBTQUMwMDEyPC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+RGVzaWduIHRoZSBzeXN0ZW1zIGFuZCBuZXR3b3JrIGZvciB0aGUgb3BlcmF0aW9uLjwvcD4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMSBlbmdhZ2VtZW50LWVudmlyb25tZW50LWxvbmctZGVzY3JpcHRpb24gZXRfcGJfdGV4dF9hbGlnbl9sZWZ0IGV0X3BiX2JsdXJiX3Bvc2l0aW9uX3RvcCBldF9wYl9iZ19sYXlvdXRfbGlnaHQiPgogICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9kZXNjcmlwdGlvbiI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5UaGUgRW5nYWdlbWVudCBFbnZpcm9ubWVudCBpcyB0aGUgc2V0IG9mIGNhcmVmdWxseSB0YWlsb3JlZCwgaGlnaGx5IGluc3RydW1lbnRlZCBzeXN0ZW1zIGRlc2lnbmVkIG9uIGFuIGVuZ2FnZW1lbnQtYnktZW5nYWdlbWVudCBiYXNpcyBhcyB0aGUgYmFja2Ryb3AgdG8gdGhlIGVuZ2FnZW1lbnQgbmFycmF0aXZlLiBJdCBpcyB0aGUgYWN0dWFsIGVudmlyb25tZW50IHRoYXQgdGhlIGFkdmVyc2FyeSB3aWxsIG9wZXJhdGUgaW4uIEl0IGlzIGltcG9ydGFudCB0byBlbnN1cmUgdGhhdCB0aGUgRW5nYWdlbWVudCBFbnZpcm9ubWVudCBjb21wbGVtZW50cywgcmF0aGVyIHRoYW4gY29tcGV0ZXMgd2l0aCwgdGhlIGVuZ2FnZW1lbnQgbmFycmF0aXZlLiBBZGRpdGlvbmFsbHksIHRoZXNlIHN5c3RlbXMgc2hvdWxkIHByb3ZpZGUgY29uZHVpdHMgdG8gYWxsb3cgdGhlIHRhcmdldCBhZHZlcnNhcnkgbmVjZXNzYXJ5IG1vdmVtZW50IHRocm91Z2hvdXQgdGhlIGVudmlyb25tZW50LCBhcyBuZWVkZWQgdG8gbWVldCBvcGVyYXRpb25hbCBvdXRjb21lcy4gPC9wPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+V2hpbGUgbm90IHN0cmljdGx5IHBhcnQgb2YgdGhlIEVuZ2FnZW1lbnQgRW52aXJvbm1lbnQsIHRoZSBjb2xsZWN0aW9uIHN5c3RlbSBpcyB0aGUgc2V0IG9mIHN5c3RlbXMgdXNlZCB0byBnYXRoZXIgYXJ0aWZhY3RzIGFuZCBvdGhlciBkYXRhIGZyb20gYW4gb3BlcmF0aW9uIHRvIG1vbml0b3IgdGhlIGVuZ2FnZW1lbnQgdG8gZW5zdXJlIG9wZXJhdGlvbmFsIHNhZmV0eS4gSXQgaXMgaW1wb3J0YW50IHRvIGNvbnNpZGVyIHRoZSBjb2xsZWN0aW9uIHN5c3RlbSB3aGlsZSBkZXNpZ25pbmcgdGhlIGVuZ2FnZW1lbnQgZW52aXJvbm1lbnQuIEJ5IGRlc2lnbmluZyB0aGVzZSBlbnZpcm9ubWVudHMgaW4gbG9ja3N0ZXAsIHRoZSBkZWZlbmRlciBndWFyYW50ZWVzIHRoYXQgYWxsIGFzcGVjdHMgb2YgdGhlIGVuZ2FnZW1lbnQgZW52aXJvbm1lbnQgY2FuIGJlIG1vbml0b3JlZC4gVGhpcyBpcyBlc3NlbnRpYWwgdG8gZW5zdXJlIG9wZXJhdGlvbnMgcmVtYWluIHdpdGhpbiB0aGUgZ3VhcmRyYWlscyBzZXQgYnkgdGhlIFJ1bGVzIG9mIEVuZ2FnZW1lbnQuIEZvciBleGFtcGxlLCBhdmFpbGFibGUgcmVzb3VyY2VzLCBjYXBhYmlsaXRpZXMsIG9yIHNraWxscyBtYXkgbGltaXQgdGhlIHR5cGUgb2YgYXNzZXRzIGluLCBvciBzaXplIG9mLCB0aGUgZW5nYWdlbWVudCBlbnZpcm9ubWVudC48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIGVuZ2FnZW1lbnQtZW52aXJvbm1lbnQtcmVmZXJlbmNlcyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InR0YWJsZSB0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBSZWZlcmVuY2UgTGlua3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vd3d3LnJlc2VhcmNoZ2F0ZS5uZXQvcHJvZmlsZS9OaWNvbGFzLVNrbGF2b3MvcHVibGljYXRpb24vMzI4NDMwMzE3X0FwcHJvYWNoZXNfZm9yX1ByZXZlbnRpbmdfSG9uZXlwb3RfRGV0ZWN0aW9uX2FuZF9Db21wcm9taXNlL2xpbmtzLzViZDg3NGRhMjk5YmYxMTI0ZmFlMWQ1Mi9BcHByb2FjaGVzLWZvci1QcmV2ZW50aW5nLUhvbmV5cG90LURldGVjdGlvbi1hbmQtQ29tcHJvbWlzZS5wZGYiIHRhcmdldD0iX2JsYW5rIiByZWw9Im5vb3BlbmVyIj5BcHByb2FjaGVzIEZvciBQcmV2ZW50aW5nIEhvbmV5cG90IERldGVjdGlvbiBBbmQgQ29tcHJvbWlzZTwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgcGxhbi1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+UGxhbjwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBTQVAwMDAxPC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+SWRlbnRpZnkgYW5kIGFsaWduIGFuIG9wZXJhdGlvbiB3aXRoIGEgZGVzaXJlZCBlbmQtc3RhdGUuPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIHBsYW4tbG9uZy1kZXNjcmlwdGlvbiBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPlBsYW5uaW5nIGlzIHVzZWQgdG8gaWRlbnRpZnkgYW5kIGFsaWduIGFuIG9wZXJhdGlvbiB3aXRoaW4gdGhlIGNvbnRleHQgb2Ygc3RyYXRlZ2ljIGdvYWxzLiBCeSBoZWxwaW5nIHRoZSBkZWZlbmRlciB0byBmaXJzdCBpZGVudGlmeSB0aGVpciBnb2FscywgUGxhbm5pbmcgZW5zdXJlcyB0aGF0IGFsbCBlbmdhZ2VtZW50IGFjdGl2aXRpZXMgYXJlIGZvY3VzZWQgYW5kIGRyaXZpbmcgZm9yd2FyZCBwcm9ncmVzcy4gQWRkaXRpb25hbGx5LCBwbGFubmluZyBlbnN1cmVzIHRoYXQgdGhlIGRlZmVuZGVyIGNhbiBpbnRlZ3JhdGUgdGhlIGlucHV0cyBvZiB0aGUgdmFyaW91cyBzdGFrZWhvbGRlcnMgYXQgdGhlIGJlZ2lubmluZyBvZiBhbiBvcGVyYXRpb24gdG8gZW5zdXJlIHRoYXQgdGhlIG9wZXJhdGlvbiBpcyBlZmZpY2llbnQsIGVmZmVjdGl2ZSwgYW5kIHNhZmUuIEZpbmFsbHksIFBsYW5uaW5nIGFjdGl2aXRpZXMgZW5zdXJlIHRoYXQgZWFjaCBvcGVyYXRpb24gaXMgaW5mb3JtZWQgYnkgdGhlIHN1Y2Nlc3NlcyBhbmQgbGVhcm5zIGZyb20gdGhlIGZhaWx1cmVzIG9mIHBhc3Qgb3BlcmF0aW9ucy48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8yIHBsYW4tcmVmZXJlbmNlcyBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250ZW50IiBzdHlsZT0ibWF4LXdpZHRoOiAxMDAlICFpbXBvcnRhbnQiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGFibGUgY2xhc3M9InR0YWJsZSB0YWJsZSB0YWJsZS1ib3JkZXJlZCB0YWJsZS1ob3ZlciIgc3R5bGU9ImhlaWdodDogMjYwcHg7Ym9yZGVyLXNwYWNpbmc6IDBweCIgY2VsbHBhZGRpbmc9IjAiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDIzcHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoIHN0eWxlPSJoZWlnaHQ6IDIzcHg7d2lkdGg6IDI0OS4wMTZweDt0ZXh0LWFsaWduOiBsZWZ0Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICBSZWZlcmVuY2UgTGlua3MKICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGg+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdHI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aGVhZD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogOTVweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRkIHN0eWxlPSJoZWlnaHQ6IDk1cHg7d2lkdGg6IDI0OS4wMTZweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxhIGhyZWY9Imh0dHBzOi8vd3d3Lm5zcHcub3JnL3BhcGVycy8yMDE0L25zcHcyMDE0LWFsbWVzaGVrYWgucGRmIiB0YXJnZXQ9Il9ibGFuayIgcmVsPSJub29wZW5lciI+UGxhbm5pbmcgQW5kIEludGVncmF0aW5nIERlY2VwdGlvbiBJbnRvIENvbXB1dGVyIFNlY3VyaXR5IERlZmVuc2VzPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2FwcHMuZHRpYy5taWwvc3RpL3BkZnMvQURBNjI0OTEwLnBkZiIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPkN5YmVyIEV4ZXJjaXNlIFBsYXlib29rPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRyIHN0eWxlPSJoZWlnaHQ6IDk1cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ZCBzdHlsZT0iaGVpZ2h0OiA5NXB4O3dpZHRoOiAyNDkuMDE2cHgiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8YSBocmVmPSJodHRwczovL2FyeGl2Lm9yZy9wZGYvMjAwNy4xNDQ5NyIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPkN5YmVyIERlY2VwdGlvbiBGb3IgQ29tcHV0ZXIgQW5kIE5ldHdvcmsgU2VjdXJpdHk6IFN1cnZleSBBbmQgQ2hhbGxlbmdlczwvYT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3Rib2R5PgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90YWJsZT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgYW5hbHl6ZS1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+QW5hbHl6ZTwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBTQVAwMDAyPC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+UmV0cm9zcGVjdGl2ZSByZXZpZXcgb2YgaW5mb3JtYXRpb24gZ2FpbmVkIGZyb20gYW4gb3BlcmF0aW9uIC48L3A+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzEgYW5hbHl6ZS1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+QW5hbHlzaXMgaXMgdXNlZCB0byBhZ2dyZWdhdGUsIGV4YW1pbmUsIGFuZCBldmFsdWF0ZSB0aGUgcmVzdWx0cyBvZiBhbiBvcGVyYXRpb24uIEFuYWx5c2lzIGlzIHVzZWZ1bCBmb3IgaW1wcm92aW5nIHRoZSBkZWZlbmRlcuKAmXMgc2VjdXJpdHkgcG9zdHVyZSB0aHJvdWdoIHRoZSBzeW50aGVzaXMgb2Ygb3BlcmF0aW9uYWwgZGF0YS4gQWRkaXRpb25hbGx5LCBhbmFseXNpcyBjYW4gYmUgdXNlZCB0byB0dXJuIGRhdGEgaW50byBhY3Rpb25hYmxlIGludGVsbGlnZW5jZSBhYm91dCBhbiBhZHZlcnNhcnnigJlzIG1vdGl2YXRvcnMsIGJlaGF2aW9ycywgdGFjdGljcywgYW5kIHRlY2huaXF1ZXMuICBEZWZlbmRlcnMgY2FuIHVzZSBhbmFseXNpcyB0byBnYWluIGluc2lnaHQgaW50byBhZHZlcnNhcnkgYWN0aXZpdHkgYW5kIHRodXMgaW5mb3JtIGRldGVjdGlvbiBhbmQgYW5hbHl0aWNzIHJlZmluZW1lbnRzLiBSZXZpZXdpbmcgdGhlIGV4ZWN1dGlvbiBvZiBhbiBvcGVyYXRpb24gYWxzbyBwcm92aWRlcyBmZWVkYmFjayBmb3IgdGhlIHRlYW0gdG8gaW1wcm92ZSB0aGUgcXVhbGl0eSBvZiBmdXR1cmUgb3BlcmF0aW9ucy4gRmluYWxseSwgQW5hbHlzaXMgYWN0aXZpdGllcyBlbnN1cmUgdGhhdCBlYWNoIG9wZXJhdGlvbiBpcyBpbmZvcm1lZCBieSB0aGUgc3VjY2Vzc2VzIGFuZCBsZWFybnMgZnJvbSB0aGUgZmFpbHVyZXMgb2YgcGFzdCBvcGVyYXRpb25zLjwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICA8L2Rpdj4KICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzIgYW5hbHl6ZS1yZWZlcmVuY2VzIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGFpbmVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0YWJsZSBjbGFzcz0idHRhYmxlIHRhYmxlIHRhYmxlLWJvcmRlcmVkIHRhYmxlLWhvdmVyIiBzdHlsZT0iaGVpZ2h0OiAyNjBweDtib3JkZXItc3BhY2luZzogMHB4IiBjZWxscGFkZGluZz0iMCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPHRoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dHIgc3R5bGU9ImhlaWdodDogMjNweCI+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGggc3R5bGU9ImhlaWdodDogMjNweDt3aWR0aDogMjQ5LjAxNnB4O3RleHQtYWxpZ246IGxlZnQiPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIFJlZmVyZW5jZSBMaW5rcwogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90aD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPC90cj4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RoZWFkPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0Ym9keT4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDx0ciBzdHlsZT0iaGVpZ2h0OiA5NXB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8dGQgc3R5bGU9ImhlaWdodDogOTVweDt3aWR0aDogMjQ5LjAxNnB4Ij4KICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgPGEgaHJlZj0iaHR0cHM6Ly93d3cuaWFsZWlhLm9yZy9kb2NzL1BzeWNob2xvZ3lfb2ZfSW50ZWxsaWdlbmNlX0FuYWx5c2lzLnBkZiIgdGFyZ2V0PSJfYmxhbmsiIHJlbD0ibm9vcGVuZXIiPlBzeWNob2xvZ3kgT2YgSW50ZWxsaWdlbmNlIEFuYWx5c2lzPC9hPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGQ+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RyPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDwvdGJvZHk+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8L3RhYmxlPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICA8L2Rpdj4KPC9kaXY+CjxkaXYgY2xhc3M9ImV0X3BiX3JvdyBldF9wYl9yb3dfMiBwcmVwYXJlLWRldGFpbCBtYXRyaXgtZGV0YWlscyBldF9wYl9ndXR0ZXJzMSBldF9oYWRfYW5pbWF0aW9uIiBzdHlsZT0iZGlzcGxheTogbm9uZTsiPgogICAgPGRpdiBjbGFzcz0iZXRfcGJfY29sdW1uIGV0X3BiX2NvbHVtbl80XzQgZXRfcGJfY29sdW1uXzUgZXRfcGJfY3NzX21peF9ibGVuZF9tb2RlX3Bhc3N0aHJvdWdoIGV0LWxhc3QtY2hpbGQiPgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8wIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGg0IGNsYXNzPSJldF9wYl9tb2R1bGVfaGVhZGVyIj4KICAgICAgICAgICAgICAgICAgICAgICAgPHNwYW4gc3R5bGU9ImZvbnQtc2l6ZTogMjBweCAhaW1wb3J0YW50O2xpbmUtaGVpZ2h0OiAxICFpbXBvcnRhbnQ7Zm9udC13ZWlnaHQ6IDYwMCAhaW1wb3J0YW50Ij5QcmVwYXJlPC9zcGFuPgogICAgICAgICAgICAgICAgICAgIDwvaDQ+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8aDU+SUQ6IFNHTzAwMDE8L2g1PgogICAgICAgICAgICAgICAgICAgICAgICA8cD5IZWxwIHRoZSBkZWZlbmRlciB0aGluayBhYm91dCB3aGF0IHRoZXkgd2FudCB0byBhY2NvbXBsaXNoIHdpdGggb3BlcmF0aW9ucy48L3A+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfbW9kdWxlIGV0X3BiX2JsdXJiIGV0X3BiX2JsdXJiXzEgcHJlcGFyZS1sb25nLWRlc2NyaXB0aW9uIGV0X3BiX3RleHRfYWxpZ25fbGVmdCBldF9wYl9ibHVyYl9wb3NpdGlvbl90b3AgZXRfcGJfYmdfbGF5b3V0X2xpZ2h0Ij4KICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfY29udGVudCIgc3R5bGU9Im1heC13aWR0aDogMTAwJSAhaW1wb3J0YW50Ij4KICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRhaW5lciI+CiAgICAgICAgICAgICAgICAgICAgPGRpdiBjbGFzcz0iZXRfcGJfYmx1cmJfZGVzY3JpcHRpb24iPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+UHJlcGFyZSBpcyB1c2VkIHRvIGVuc3VyZSB0aGUgZGVmZW5kZXIgZHJpdmVzIHByb2dyZXNzIGR1cmluZyBhZHZlcnNhcnkgZW5nYWdlbWVudCBvcGVyYXRpb25zIHRvd2FyZHMgYSBkZXNpcmVkIGVuZC1zdGF0ZSBvciBTdHJhdGVnaWMgR29hbC4gVG8gc3VwcG9ydCB0aGlzIGFpbSwgdGhlIGRlZmVuZGVyIG11c3QgZmlyc3QgZ2VuZXJhdGUgYSBjbGVhciBwaWN0dXJlIG9mIHRoZWlyIG9yZ2FuaXphdGlvbiBhbmQgdGhlIHRocmVhdCBsYW5kc2NhcGUuIFRoaXMgdW5kZXJzdGFuZGluZyBzaG91bGQgaW5jbHVkZSB0aGVpciBjdXJyZW50IHNlY3VyaXR5IHBvc3R1cmUsIGluY2x1ZGluZyBrbm93biBzdHJlbmd0aHMgYW5kIHdlYWtuZXNzZXMsIGFuZCBhbiBpbnZlbnRvcnkgb2YgcHJpb3JpdHkgY3liZXIgYXNzZXRzLCBpbmNsdWRpbmcga2V5IGludGVsbGVjdHVhbCBwcm9wZXJ0eS4gVGhlIGRlZmVuZGVyIHNob3VsZCB0aGVuIGV4YW1pbmUgYW5kIHVwZGF0ZSB0aGUgdGhyZWF0IG1vZGVscyBmb3IgYW55IGlkZW50aWZpZWQgYWR2ZXJzYXJpZXMuIDwvcD4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPlRoZXNlIHZhcmlvdXMgYXNzZXNzbWVudHMgYW5kIG1vZGVscyBzaG91bGQgZW5hYmxlIHRoZSBkZWZlbmRlciB0byBpZGVudGlmeSB0aGVpciBzdHJhdGVnaWMgZ29hbC4gQXQgdGhpcyBwb2ludCwgYWxsIGFjdGl2aXRpZXMgc2hvdWxkIGJlIGFsaWduZWQgd2l0aCB0aGlzIGdvYWwuIE9uY2UgYSBnb2FsIGhhcyBiZWVuIHNlbGVjdGVkLCB0aGUgZGVmZW5kZXIgbXVzdCB3b3JrIHRvIHBsYW4gZm9yIHRoZSBvcGVyYXRpb24gYnkgaWRlbnRpZnlpbmcgYSB0YXJnZXQgYWR2ZXJzYXJ5LCBjcmVhdGluZyB0aGUgbmVjZXNzYXJ5IFBlcnNvbmFzLCBnZW5lcmF0aW5nIGFuIG9wZXJhdGlvbmFsIHN0b3J5Ym9hcmQsIGV0Yy4gRmluYWxseSwgdGhlIGtleSBzdGFrZWhvbGRlcnMgc2hvdWxkIGJlIGNhbGxlZCBvbiB0byBlc3RhYmxpc2ggcnVsZXMgZm9yIG9wZXJhdGlvbmFsIHNhZmV0eSBhbmQgYWNjZXB0YWJsZSByaXNrLiBBdCBlYWNoIHN0ZXAgaW4gdGhlIHBsYW5uaW5nIHByb2Nlc3MsIHRoZSBkZWZlbmRlciBzaG91bGQgaW5jb3Jwb3JhdGUgaW50ZWxsaWdlbmNlIGdhaW5lZCBmcm9tIHByZXZpb3VzIG9wZXJhdGlvbnMgdG8gZW5zdXJlIHRoYXQgZnV0dXJlIG9wZXJhdGlvbnMgY2FuIHJ1biBtb3JlIGVmZmVjdGl2ZWx5IGFuZCBlZmZpY2llbnRseS4gPC9wPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+RW5nYWdlIGRlZmluZXMgYSBzaW5nbGUgYXBwcm9hY2ggdG8gbWFrZSBwcm9ncmVzcyB0b3dhcmRzIHRoZSBQcmVwYXJlIGdvYWwuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+UGxhbm5pbmcgZm9jdXNlcyBjb2xsZWN0aW5nIHRoZSB2YXJpb3VzIGV4aXN0aW5nIHNvdXJjZXMgb2YgaW50ZWxsaWdlbmNlIHRvZ2V0aGVyIHRvIGluZm9ybSB0aGUgc2VsZWN0aW9uIG9mIGEgc3RyYXRlZ2ljIGdvYWwgYW5kIHRoZW4gdG8gZHJpdmUgcHJvZ3Jlc3MgdG93YXJkcyB0aGF0IGdvYWwuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+VW5saWtlIHRoZSBFbmdhZ2VtZW50IEdvYWxzLCBQcmVwYXJlIGhhcyBvbmx5IGEgc2luZ2xlIGFwcHJvYWNoLiBUaGlzIGxhc2VyIGZvY3VzIGlzIGludGVudGlvbmFsIGZvciB0aGUgZmlyc3QgcmVsZWFzZSBvZiBFbmdhZ2UuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+RW5nYWdlIHNlZWtzIHRvIGhpZ2hsaWdodCB0aGF0IGRlbmlhbCwgZGVjZXB0aW9uLCBhbmQgYWR2ZXJzYXJ5IGVuZ2FnZW1lbnQgYWN0aXZpdGllcyBjYW5ub3QgYmUgdmlld2VkIGFzIOKAnGZpcmUgYW5kIGZvcmdldOKAnS4gVW5saWtlIG1hbnkgZGVmZW5zaXZlIHRlY2hub2xvZ2llcywgdGhlc2UgYWN0aXZpdGllcyBtdXN0IGJlIHZpZXdlZCBvbmx5IGluIGNvbnRleHQgb2YgaG93IHRoZXkgaW5mb3JtIGFuZCBkcml2ZSBwcm9ncmVzcyB0b3dhcmRzIGxhcmdlciBzdHJhdGVnaWMgZ29hbHMuIFRvIHRoaXMgZW5kLCBQcmVwYXJlIGlzIGVzc2VudGlhbCB0byBlbnN1cmUgdGhhdCBldmVyeSBhY3Rpb24gdGFrZW4gaW4gYW4gZW5nYWdlbWVudCBvcGVyYXRpb24gZHJpdmVzIHByb2dyZXNzIHRvd2FyZHMgYSB1bmlmaWVkIGdvYWwuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICA8YnIgY2xhc3M9ImNsZWFyZml4IiAvPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgPC9kaXY+CjwvZGl2Pgo8ZGl2IGNsYXNzPSJldF9wYl9yb3cgZXRfcGJfcm93XzIgdW5kZXJzdGFuZC1kZXRhaWwgbWF0cml4LWRldGFpbHMgZXRfcGJfZ3V0dGVyczEgZXRfaGFkX2FuaW1hdGlvbiIgc3R5bGU9ImRpc3BsYXk6IG5vbmU7Ij4KICAgIDxkaXYgY2xhc3M9ImV0X3BiX2NvbHVtbiBldF9wYl9jb2x1bW5fNF80IGV0X3BiX2NvbHVtbl81IGV0X3BiX2Nzc19taXhfYmxlbmRfbW9kZV9wYXNzdGhyb3VnaCBldC1sYXN0LWNoaWxkIj4KICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9tb2R1bGUgZXRfcGJfYmx1cmIgZXRfcGJfYmx1cmJfMCBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxoNCBjbGFzcz0iZXRfcGJfbW9kdWxlX2hlYWRlciI+CiAgICAgICAgICAgICAgICAgICAgICAgIDxzcGFuIHN0eWxlPSJmb250LXNpemU6IDIwcHggIWltcG9ydGFudDtsaW5lLWhlaWdodDogMSAhaW1wb3J0YW50O2ZvbnQtd2VpZ2h0OiA2MDAgIWltcG9ydGFudCI+VW5kZXJzdGFuZDwvc3Bhbj4KICAgICAgICAgICAgICAgICAgICA8L2g0PgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGg1PklEOiBTR08wMDAyPC9oNT4KICAgICAgICAgICAgICAgICAgICAgICAgPHA+TWFrZSBzdXJlIHRoYXQgdGhlIGRlZmVuZGVyIGlzIGNhcHR1cmluZywgdXRpbGl6aW5nLCBhbmQgcmVmaW5pbmcga25vd2xlZGdlIGxlYXJuZWQgdG8gaW1wcm92ZSB0aGUgZGVmZW5kZXLigJlzIHBvc3R1cmUuPC9wPgogICAgICAgICAgICAgICAgICAgIDwvZGl2PgogICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgIDwvZGl2PgogICAgICAgIDwvZGl2PgogICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX21vZHVsZSBldF9wYl9ibHVyYiBldF9wYl9ibHVyYl8xIHVuZGVyc3RhbmQtbG9uZy1kZXNjcmlwdGlvbiBldF9wYl90ZXh0X2FsaWduX2xlZnQgZXRfcGJfYmx1cmJfcG9zaXRpb25fdG9wIGV0X3BiX2JnX2xheW91dF9saWdodCI+CiAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2NvbnRlbnQiIHN0eWxlPSJtYXgtd2lkdGg6IDEwMCUgIWltcG9ydGFudCI+CiAgICAgICAgICAgICAgICA8ZGl2IGNsYXNzPSJldF9wYl9ibHVyYl9jb250YWluZXIiPgogICAgICAgICAgICAgICAgICAgIDxkaXYgY2xhc3M9ImV0X3BiX2JsdXJiX2Rlc2NyaXB0aW9uIj4KICAgICAgICAgICAgICAgICAgICAgICAgPGJyIGNsYXNzPSJjbGVhcmZpeCIgLz4KICAgICAgICAgICAgICAgICAgICAgICAgICAgIDxwPlVuZGVyc3RhbmQgZnJhbWVzIGhvdyByYXcgb3BlcmF0aW9uYWwgb3V0cHV0cyBjYW4gYmUgY29sbGVjdGVkLCBzeW50aGVzaXplZCwgYW5kIHVzZWQgdG8gaW5mb3JtIGZ1dHVyZSBvcGVyYXRpb25zIGFuZCBkZWZlbnNpdmUgc3RyYXRlZ2llcy4gVGhlIFVuZGVyc3RhbmQgZ29hbCBoZWxwcyB0aGUgZGVmZW5kZXIgdG8gYXNzZXNzIHRoZWlyIHByb2dyZXNzIHRvd2FyZHMgU3RyYXRlZ2ljIEdvYWxzLiBBdCBpdHMgY29yZSwgdGhlIFVuZGVyc3RhbmQgZ29hbCBlbnN1cmVzIHRoYXQgb3BlcmF0aW9uYWwgb3V0cHV0cyBjYW4gY29ubmVjdCB0byBhbmQgaW5mb3JtIGEgbGFyZ2VyIHN0cmF0ZWd5LiBUbyBkbyB0aGlzLCB0aGUgZGVmZW5kZXIgbXVzdCB0dXJuIHRoZSByYXcgb3V0cHV0cyBmcm9tIGFuIG9wZXJhdGlvbiBpbnRvIHVzZWZ1bCBhbmQgYWN0aW9uYWJsZSBpbnRlbGxpZ2VuY2UuIFRoZXNlIG91dHB1dHMgbWF5IGJlIGluIHRoZSBmb3JtIG9mIGNvbGxlY3RlZCBQQ0FQLCBsb2dzLCBxdWFsaXRhdGl2ZSBkZWZlbmRlciBvYnNlcnZhdGlvbnMsIGV0Yy4gQXBwbHlpbmcgYW5hbHl0aWNzIHRvIHJhdyBkYXRhIGNhbiBoZWxwIHRoZSBkZWZlbmRlciB0byBtYXAgdGhpcyBkYXRhIHRvIGFkdmVyc2FyeSBiZWhhdmlvci4gTm93IHRoZSBiZWhhdmlvciBjYW4gYmUgYW5hbHl6ZWQgdG8gY29udGV4dHVhbGl6ZSB0aGUgaW50ZWxsaWdlbmNlIGFuZCBpbmZvcm0gdGhlIGV4aXN0aW5nIHRocmVhdCBtb2RlbC4gIEZvciBleGFtcGxlLCB0aGUgZGVmZW5kZXIgbWF5IGxvb2sgYXQgcmF3IFBDQVAgZGF0YSBhbmQgaWRlbnRpZnkgYSBuZXcgSVAgYWRkcmVzcyB0aGF0IHRoZSBhZHZlcnNhcnkgdXNlcyBmb3IgZXhmaWx0cmF0aW9uLiBUaGlzIElPQyBjYW4gYmUgYWRkZWQgdG8gdGhlIGV4aXN0aW5nIHRocmVhdCBtb2RlbC4gQWZ0ZXIgYXBwbHlpbmcgYmVoYXZpb3JhbCBhbmFseXRpY3MgdG8gdGhlIGRhdGEsIHRoZSBkZWZlbmRlciBtaWdodCBzZWUgdGhhdCB0aGUgYWR2ZXJzYXJ5IHVzZWQgYSBuZXcgRGVmZW5zZSBFdmFzaW9uIHRlY2huaXF1ZS4gSW4gdGhhdCBjYXNlLCB0aGUgZGVmZW5kZXIgc2hvdWxkIHVwZGF0ZSB0aGUgdGhyZWF0IG1vZGVsIHRvIGluY2x1ZGUgdGhpcyBuZXcgaW50ZWxsaWdlbmNlLiBBdCB0aGlzIHBvaW50LCB0aGUgZGVmZW5kZXIgc2hvdWxkIGFzc2VzcyBpZiB0aGlzIG5ldyBpbnRlbGxpZ2VuY2Ugd2lsbCBhZmZlY3QgYW55IG9uZ29pbmcgb3BlcmF0aW9ucy4gRm9yIGV4YW1wbGUsIHRoZSBkZWZlbmRlciBzaG91bGQgZW5zdXJlIHRoYXQgY3VycmVudCBjb2xsZWN0aW9uIGVmZm9ydHMgd2lsbCBkZXRlY3QgdGhpcyBuZXcgVFRQLiBPdGhlciBvcHBvcnR1bml0aWVzIHRvIGluY3JlYXNlIHRoZSBkZWZlbmRlcuKAmXMgdW5kZXJzdGFuZGluZyBwb3N0LW9wZXJhdGlvbiBpbmNsdWRlIGVmZm9ydHMgdG8gcmVmaW5lIGFuZCB1cGRhdGUgaW5kaXZpZHVhbCBlbmdhZ2VtZW50IGFjdGl2aXRpZXMgYmFzZWQgb24gcXVhbGl0YXRpdmUgYW5kIHF1YW50aXRhdGl2ZSBvdXRwdXRzLiBUaGUgZGVmZW5kZXIgY2FuIHJlZmxlY3Qgb24gaG93IHRoZSBvdmVyYWxsIGVuZ2FnZW1lbnQgd2VudCBhbmQgcmVmaW5lIGZ1dHVyZSBhY3Rpdml0aWVzIHRvIG1heGltaXplIHRoZSB1c2VmdWxuZXNzLiAgRmluYWxseSwgdGhlIGRlZmVuZGVycyBzaG91bGQgYXNzZXNzIHRoZWlyIG93biBjb29yZGluYXRpb24gYW5kIGNvbW11bmljYXRpb24uIFRlYW13b3JrIGlzIGVzc2VudGlhbCBkdXJpbmcgYW4gb3BlcmF0aW9uLiBUaGUgZGVmZW5kZXIgc2hvdWxkIHNlZWsgdG8gaW1wcm92ZSBjb29yZGluYXRpb24gYW5kIHNraWxscyB3aXRoIGVhY2ggb3BlcmF0aW9uLiBFbmdhZ2UgZGVmaW5lcyBhIHNpbmdsZSBhcHByb2FjaCB0byBtYWtlIHByb2dyZXNzIHRvd2FyZHMgdGhlIFVuZGVyc3RhbmQgZ29hbC48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgICAgICA8cD5BbmFseXNpcywgZm9jdXNlcyBvbiB0dXJuaW5nIHJhdyBvdXRwdXRzIGludG8gdXNlZnVsIGludGVsbGlnZW5jZSB0aGF0IGRyaXZlcyBmdXR1cmUgcHJvZ3Jlc3MuPC9wPgogICAgICAgICAgICAgICAgICAgICAgICAgICAgPHA+VW5saWtlIHRoZSBFbmdhZ2VtZW50IEdvYWxzLCBVbmRlcnN0YW5kIGhhcyBvbmx5IGEgc2luZ2xlIGFwcHJvYWNoLiBUaGlzIGxhc2VyIGZvY3VzIGlzIGludGVudGlvbmFsIGZvciB0aGUgZmlyc3QgcmVsZWFzZSBvZiBFbmdhZ2UuICBFbmdhZ2Ugc2Vla3MgdG8gaGlnaGxpZ2h0IHRoYXQgZGVuaWFsLCBkZWNlcHRpb24sIGFuZCBhZHZlcnNhcnkgZW5nYWdlbWVudCBhY3Rpdml0aWVzIGNhbm5vdCBiZSB2aWV3ZWQgYXMg4oCc4oCcZmlyZSBhbmQgZm9yZ2V04oCd4oCcLiBVbmxpa2UgbWFueSBkZWZlbnNpdmUgdGVjaG5vbG9naWVzLCB0aGVzZSBhY3Rpdml0aWVzIG11c3QgYmUgdmlld2VkIG9ubHkgaW4gY29udGV4dCBvZiBob3cgdGhleSBpbmZvcm0gYW5kIGRyaXZlIHByb2dyZXNzIHRvd2FyZHMgbGFyZ2VyIHN0cmF0ZWdpYyBnb2Fscy4gVG8gdGhpcyBlbmQsIEFuYWx5c2lzIGlzIGVzc2VudGlhbCB0byB0dXJuIHRoZSByYXcgb3BlcmF0aW9uYWwgb3V0cHV0cyBpbnRvIGludGVsbGlnZW5jZSB0aGF0IGRyaXZlcyBwcm9ncmVzcyB0b3dhcmRzIHRoZXNlIHN0cmF0ZWdpYyBnb2Fscy48L3A+CiAgICAgICAgICAgICAgICAgICAgICAgIDxiciBjbGFzcz0iY2xlYXJmaXgiIC8+CiAgICAgICAgICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgICAgICAgICA8L2Rpdj4KICAgICAgICAgICAgPC9kaXY+CiAgICAgICAgPC9kaXY+CiAgICA8L2Rpdj4KPC9kaXY+Cg==
eyJBUEkgTW9uaXRvcmluZyI6IHsidGFjdGljcyI6IFsiVEEwMDAxIiwgIlRBMDAwMiIsICJUQTAwMDMiLCAiVEEwMDA0IiwgIlRBMDAwNSIsICJUQTAwMDYiLCAiVEEwMDA3IiwgIlRBMDAwOCIsICJUQTAwMTEiLCAiVEEwMDI3IiwgIlRBMDAyOCIsICJUQTAwMjkiLCAiVEEwMDMwIiwgIlRBMDAzMSIsICJUQTAwMzIiLCAiVEEwMDMzIiwgIlRBMDAzNCIsICJUQTAwMzUiLCAiVEEwMDM3IiwgIlRBMDA0MCIsICJUQTAwNDEiLCAiVEEwMTAwIiwgIlRBMDEwMiIsICJUQTAxMDMiLCAiVEEwMTA0IiwgIlRBMDEwNSIsICJUQTAxMDYiLCAiVEEwMTA3IiwgIlRBMDEwOSIsICJUQTAxMTAiLCAiVEEwMTExIl0sICJ0ZWNobmlxdWVzIjogWyJUMDgwOSIsICJUMDgxMyIsICJUMDgxNCIsICJUMDgxNSIsICJUMDgyMSIsICJUMDgyMyIsICJUMDgyNiIsICJUMDgyNyIsICJUMDgyOSIsICJUMDgzNCIsICJUMDgzNiIsICJUMDgzNyIsICJUMDgzOCIsICJUMDg0MCIsICJUMDg0MyIsICJUMDg0NSIsICJUMDg1OCIsICJUMDg3MSIsICJUMDg3MiIsICJUMDg3NCIsICJUMDg4MCIsICJUMDg4OCIsICJUMDg4OSIsICJUMTAwNyIsICJUMTAxNiIsICJUMTAzMyIsICJUMTA0OSIsICJUMTA3MCIsICJUMTA4MiIsICJUMTA4MyIsICJUMTA5MSIsICJUMTEwNiIsICJUMTEzMiIsICJUMTEzNCIsICJUMTIwMiIsICJUMTIxNiIsICJUMTIxOCIsICJUMTIyMCIsICJUMTQwNCIsICJUMTQxNCIsICJUMTQxOCIsICJUMTQyMCIsICJUMTQyMSIsICJUMTQyMiIsICJUMTQyNiIsICJUMTQyOSIsICJUMTQ1OCIsICJUMTQ4NSIsICJUMTQ5NiIsICJUMTUxMiIsICJUMTUxMyIsICJUMTUxNiIsICJUMTUzMyIsICJUMTU0MSIsICJUMTU1MyIsICJUMTU1NiIsICJUMTU1OSIsICJUMTU2NCIsICJUMTU2OSIsICJUMTU3NSIsICJUMTU4MiIsICJUMTYwNCIsICJUMTYxNCIsICJUMTYxNiIsICJUMTYxNyIsICJUMTYyMyIsICJUMTYyOCIsICJUMTYzMCIsICJUMTYzMiJdfSwgIkFmdGVyLUFjdGlvbiBSZXZpZXciOiB7InRhY3RpY3MiOiBbXSwgInRlY2huaXF1ZXMiOiBbXX0sICJBcHBsaWNhdGlvbiBEaXZlcnNpdHkiOiB7InRhY3RpY3MiOiBbIlRBMDAwMSIsICJUQTAwMDIiLCAiVEEwMDAzIiwgIlRBMDAwNCIsICJUQTAwMDUiLCAiVEEwMDA2IiwgIlRBMDAwNyIsICJUQTAwMDgiLCAiVEEwMDA5IiwgIlRBMDAxMSIsICJUQTAwMjgiLCAiVEEwMDI5IiwgIlRBMDAzMCIsICJUQTAwMzEiLCAiVEEwMDMyIiwgIlRBMDAzMyIsICJUQTAwMzQiLCAiVEEwMDM1IiwgIlRBMDA0MCIsICJUQTAxMDgiLCAiVEEwMTA5IiwgIlRBMDExMSJdLCAidGVjaG5pcXVlcyI6IFsiVDA4NjYiLCAiVDA4ODYiLCAiVDA4OTAiLCAiVDEwMTAiLCAiVDEwMjEiLCAiVDEwNTYiLCAiVDEwNjgiLCAiVDEwNzIiLCAiVDExMzciLCAiVDExOTAiLCAiVDEyMDMiLCAiVDEyMTAiLCAiVDEyMTEiLCAiVDEyMTIiLCAiVDEyMTkiLCAiVDE0MDQiLCAiVDE0MDkiLCAiVDE0MTciLCAiVDE0MTgiLCAiVDE0MjQiLCAiVDE0MjgiLCAiVDE0OTYiLCAiVDE1MDUiLCAiVDE1MTgiLCAiVDE1MjUiLCAiVDE1MzEiLCAiVDE1MzIiLCAiVDE1MzMiLCAiVDE1NTMiLCAiVDE1NTQiLCAiVDE1NjAiLCAiVDE1NjIiLCAiVDE1NzciLCAiVDE1NzgiLCAiVDE2MTMiLCAiVDE2MjkiLCAiVDE2MzIiLCAiVDE2MzQiLCAiVDE2NDAiLCAiVDE2NDUiXX0sICJBcnRpZmFjdCBEaXZlcnNpdHkiOiB7InRhY3RpY3MiOiBbIlRBMDAwMSIsICJUQTAwMDIiLCAiVEEwMDAzIiwgIlRBMDAwNCIsICJUQTAwMDUiLCAiVEEwMDA2IiwgIlRBMDAwNyIsICJUQTAwMDkiLCAiVEEwMDMwIiwgIlRBMDAzMiIsICJUQTAwMzQiLCAiVEEwMDM1IiwgIlRBMDA0MCIsICJUQTAwNDEiLCAiVEEwMDQzIiwgIlRBMDEwMCIsICJUQTAxMDciLCAiVEEwMTA5IiwgIlRBMDExMCJdLCAidGVjaG5pcXVlcyI6IFsiVDA4MTEiLCAiVDA4MTIiLCAiVDA4NTkiLCAiVDA4NzciLCAiVDA4ODEiLCAiVDEwNTciLCAiVDEwNTkiLCAiVDEwNjkiLCAiVDEwNzgiLCAiVDEwODMiLCAiVDEwODciLCAiVDExMjAiLCAiVDExNzYiLCAiVDEyMjEiLCAiVDEyMjIiLCAiVDE0MjAiLCAiVDE0MjQiLCAiVDE0NzEiLCAiVDE0ODIiLCAiVDE0ODYiLCAiVDE0ODkiLCAiVDE1MjYiLCAiVDE1MjkiLCAiVDE1NTIiLCAiVDE1NjQiLCAiVDE1OTIiLCAiVDE2MDEiLCAiVDE2MDIiLCAiVDE2MDYiLCAiVDE2MjMiLCAiVDE2MjgiLCAiVDE2MzYiLCAiVDE2NDAiXX0sICJBdHRhY2sgVmVjdG9yIE1pZ3JhdGlvbiI6IHsidGFjdGljcyI6IFsiVEEwMDAxIiwgIlRBMDAwMiIsICJUQTAwMDMiLCAiVEEwMDA4IiwgIlRBMDAxMSIsICJUQTAwMjciLCAiVEEwMDI4IiwgIlRBMDAzMyIsICJUQTAxMDQiLCAiVEEwMTA4Il0sICJ0ZWNobmlxdWVzIjogWyJUMDg0NyIsICJUMDg1MyIsICJUMDg2MiIsICJUMDg2MyIsICJUMDg2NCIsICJUMDg2NSIsICJUMTA5MSIsICJUMTA5MiIsICJUMTEwNCIsICJUMTE5NSIsICJUMTIwNCIsICJUMTQ1OCIsICJUMTQ3NCIsICJUMTU1NCIsICJUMTU2NiIsICJUMTY0NSJdfSwgIkJhc2VsaW5lIjogeyJ0YWN0aWNzIjogWyJUQTAwMDMiLCAiVEEwMDA0IiwgIlRBMDAwNSIsICJUQTAwMjgiLCAiVEEwMDMwIiwgIlRBMDA0MCIsICJUQTAxMDMiLCAiVEEwMTA3Il0sICJ0ZWNobmlxdWVzIjogWyJUMDg1MSIsICJUMTAxNCIsICJUMTAzNyIsICJUMTExMiIsICJUMTEzNiIsICJUMTEzNyIsICJUMTE3NiIsICJUMTM5OCIsICJUMTQ4MCIsICJUMTQ5MCIsICJUMTUwNSIsICJUMTU0MyIsICJUMTU0NiIsICJUMTU0NyIsICJUMTU2MSIsICJUMTU3NyIsICJUMTYwMSIsICJUMTYyNCIsICJUMTYyNyJdfSwgIkJ1cm4tSW4iOiB7InRhY3RpY3MiOiBbIlRBMDAwMSIsICJUQTAwMDMiLCAiVEEwMDA0IiwgIlRBMDAwNSIsICJUQTAwMDciLCAiVEEwMDA5IiwgIlRBMDAzMiIsICJUQTAwMzUiLCAiVEEwMDQzIiwgIlRBMDEwMiIsICJUQTAxMDgiLCAiVEEwMTA5IiwgIlRBMDExMCJdLCAidGVjaG5pcXVlcyI6IFsiVDA4MTIiLCAiVDA4NTkiLCAiVDA4ODMiLCAiVDA4ODgiLCAiVDEwMDUiLCAiVDEwMTIiLCAiVDEwMTYiLCAiVDEwNDkiLCAiVDEwNTciLCAiVDEwNzgiLCAiVDEwODIiLCAiVDExMTQiLCAiVDExMzMiLCAiVDExODUiLCAiVDE0MjEiLCAiVDE0MjIiLCAiVDE0MjMiLCAiVDE0MjQiLCAiVDE0MjYiLCAiVDE1MzAiLCAiVDE1MzMiLCAiVDE1OTIiLCAiVDE2MDIiXX0sICJDeWJlciBUaHJlYXQgSW50ZWxsaWdlbmNlIjogeyJ0YWN0aWNzIjogW10sICJ0ZWNobmlxdWVzIjogW119LCAiRW1haWwgTWFuaXB1bGF0aW9uIjogeyJ0YWN0aWNzIjogWyJUQTAwMDEiLCAiVEEwMDA5Il0sICJ0ZWNobmlxdWVzIjogWyJUMTExNCIsICJUMTExOSIsICJUMTU2NiJdfSwgIkVuZ2FnZW1lbnQgRW52aXJvbm1lbnQiOiB7InRhY3RpY3MiOiBbXSwgInRlY2huaXF1ZXMiOiBbXX0sICJHYXRpbmcgQ3JpdGVyaWEiOiB7InRhY3RpY3MiOiBbXSwgInRlY2huaXF1ZXMiOiBbXX0sICJIYXJkd2FyZSBNYW5pcHVsYXRpb24iOiB7InRhY3RpY3MiOiBbIlRBMDAwOSIsICJUQTAwMjgiLCAiVEEwMDM1IiwgIlRBMDEwMCJdLCAidGVjaG5pcXVlcyI6IFsiVDA4NTIiLCAiVDExMTMiLCAiVDExMjMiLCAiVDExMjUiLCAiVDEzOTgiLCAiVDE0MjkiLCAiVDE1MTIiLCAiVDE1MTMiXX0sICJJbmZvcm1hdGlvbiBNYW5pcHVsYXRpb24iOiB7InRhY3RpY3MiOiBbIlRBMDAwMiIsICJUQTAwMDUiLCAiVEEwMDA3IiwgIlRBMDAwOCIsICJUQTAwMDkiLCAiVEEwMDEwIiwgIlRBMDAxMSIsICJUQTAwMzAiLCAiVEEwMDMxIiwgIlRBMDAzMiIsICJUQTAwMzQiLCAiVEEwMDM1IiwgIlRBMDAzNiIsICJUQTAwMzciLCAiVEEwMDQwIiwgIlRBMDA0MyIsICJUQTAxMDAiLCAiVEEwMTAyIiwgIlRBMDEwNCIsICJUQTAxMDUiLCAiVEEwMTA2IiwgIlRBMDEwNyIsICJUQTAxMDgiXSwgInRlY2huaXF1ZXMiOiBbIlQwODAwIiwgIlQwODAxIiwgIlQwODAyIiwgIlQwODA2IiwgIlQwODA3IiwgIlQwODA5IiwgIlQwODExIiwgIlQwODUyIiwgIlQwODYxIiwgIlQwODYzIiwgIlQwODY0IiwgIlQwODY4IiwgIlQwODc3IiwgIlQwODgyIiwgIlQwODg4IiwgIlQxMDAxIiwgIlQxMDA1IiwgIlQxMDA3IiwgIlQxMDEwIiwgIlQxMDExIiwgIlQxMDE2IiwgIlQxMDIwIiwgIlQxMDI1IiwgIlQxMDI3IiwgIlQxMDI5IiwgIlQxMDMwIiwgIlQxMDM5IiwgIlQxMDQxIiwgIlQxMDQ3IiwgIlQxMDQ4IiwgIlQxMDQ5IiwgIlQxMDUyIiwgIlQxMDgwIiwgIlQxMDgyIiwgIlQxMDgzIiwgIlQxMDg3IiwgIlQxMTEzIiwgIlQxMTE0IiwgIlQxMTE1IiwgIlQxMTE5IiwgIlQxMTIzIiwgIlQxMTI0IiwgIlQxMTI1IiwgIlQxMTMyIiwgIlQxMTM1IiwgIlQxMjAxIiwgIlQxMjA0IiwgIlQxMjEzIiwgIlQxMjE3IiwgIlQxNDA2IiwgIlQxNDA5IiwgIlQxNDE0IiwgIlQxNDIwIiwgIlQxNDIxIiwgIlQxNDIyIiwgIlQxNDI2IiwgIlQxNDI5IiwgIlQxNDMwIiwgIlQxNDcxIiwgIlQxNDgwIiwgIlQxNDgyIiwgIlQxNDg1IiwgIlQxNDg2IiwgIlQxNDkxIiwgIlQxNDk3IiwgIlQxNTEyIiwgIlQxNTEzIiwgIlQxNTE2IiwgIlQxNTE3IiwgIlQxNTMwIiwgIlQxNTMzIiwgIlQxNTM3IiwgIlQxNTM4IiwgIlQxNTYxIiwgIlQxNTY1IiwgIlQxNTY3IiwgIlQxNTgyIiwgIlQxNTkzIiwgIlQxNTk0IiwgIlQxNTk2IiwgIlQxNTk3IiwgIlQxNTk4IiwgIlQxNjAwIiwgIlQxNjAyIiwgIlQxNjE0IiwgIlQxNjE2IiwgIlQxNjI3IiwgIlQxNjMzIiwgIlQxNjM0IiwgIlQxNjM2IiwgIlQxNjM5IiwgIlQxNjQxIiwgIlQxNjQ2Il19LCAiSW50cm9kdWNlZCBWdWxuZXJhYmlsaXRpZXMiOiB7InRhY3RpY3MiOiBbIlRBMDAwMiIsICJUQTAwMDQiLCAiVEEwMDA2IiwgIlRBMDAwNyIsICJUQTAwMDgiLCAiVEEwMDI5IiwgIlRBMDEwMyIsICJUQTAxMDUiLCAiVEEwMTA4IiwgIlRBMDEwOSIsICJUQTAxMTEiXSwgInRlY2huaXF1ZXMiOiBbIlQwODEyIiwgIlQwODE5IiwgIlQwODIwIiwgIlQwODI2IiwgIlQwODI3IiwgIlQwODI5IiwgIlQwODM3IiwgIlQwODY0IiwgIlQwODY2IiwgIlQwODgwIiwgIlQwODkwIiwgIlQxMDQwIiwgIlQxMDQ2IiwgIlQxMDY4IiwgIlQxMDcyIiwgIlQxNDA0Il19LCAiSXNvbGF0aW9uIjogeyJ0YWN0aWNzIjogWyJUQTAwMDEiLCAiVEEwMDAyIiwgIlRBMDAwOCIsICJUQTAwMTEiLCAiVEEwMDI3IiwgIlRBMDAzMyIsICJUQTAwMzciLCAiVEEwMTA0IiwgIlRBMDEwOCIsICJUQTAxMTAiXSwgInRlY2huaXF1ZXMiOiBbIlQwODQ3IiwgIlQwODYyIiwgIlQwODYzIiwgIlQwODY0IiwgIlQwODczIiwgIlQxMDkxIiwgIlQxMDkyIiwgIlQxMTA1IiwgIlQxMTk1IiwgIlQxMjAwIiwgIlQxMjA0IiwgIlQxNDU4IiwgIlQxNDc0IiwgIlQxNTQ0IiwgIlQxNjQ0Il19LCAiTHVyZXMiOiB7InRhY3RpY3MiOiBbIlRBMDAwMSIsICJUQTAwMDIiLCAiVEEwMDAzIiwgIlRBMDAwNCIsICJUQTAwMDUiLCAiVEEwMDA2IiwgIlRBMDAwNyIsICJUQTAwMDgiLCAiVEEwMDA5IiwgIlRBMDAxMCIsICJUQTAwMTEiLCAiVEEwMDI3IiwgIlRBMDAyOCIsICJUQTAwMjkiLCAiVEEwMDMwIiwgIlRBMDAzMSIsICJUQTAwMzIiLCAiVEEwMDMzIiwgIlRBMDAzNCIsICJUQTAwMzUiLCAiVEEwMDM2IiwgIlRBMDAzNyIsICJUQTAwNDAiLCAiVEEwMDQzIiwgIlRBMDEwMCIsICJUQTAxMDIiLCAiVEEwMTAzIiwgIlRBMDEwNCIsICJUQTAxMDUiLCAiVEEwMTA2IiwgIlRBMDEwNyIsICJUQTAxMDgiLCAiVEEwMTA5IiwgIlRBMDExMCIsICJUQTAxMTEiXSwgInRlY2huaXF1ZXMiOiBbIlQwODAwIiwgIlQwODAxIiwgIlQwODAyIiwgIlQwODAzIiwgIlQwODA0IiwgIlQwODA1IiwgIlQwODA2IiwgIlQwODA5IiwgIlQwODExIiwgIlQwODEyIiwgIlQwODE3IiwgIlQwODE5IiwgIlQwODIwIiwgIlQwODMwIiwgIlQwODMxIiwgIlQwODM5IiwgIlQwODQwIiwgIlQwODQyIiwgIlQwODQ2IiwgIlQwODU1IiwgIlQwODU2IiwgIlQwODU3IiwgIlQwODU5IiwgIlQwODYwIiwgIlQwODYxIiwgIlQwODYyIiwgIlQwODY0IiwgIlQwODY2IiwgIlQwODY4IiwgIlQwODcxIiwgIlQwODczIiwgIlQwODc3IiwgIlQwODc4IiwgIlQwODgyIiwgIlQwODgzIiwgIlQwODg2IiwgIlQwODg3IiwgIlQwODkwIiwgIlQwODkxIiwgIlQxMDAzIiwgIlQxMDA1IiwgIlQxMDA3IiwgIlQxMDExIiwgIlQxMDEyIiwgIlQxMDE2IiwgIlQxMDE4IiwgIlQxMDIwIiwgIlQxMDIxIiwgIlQxMDI1IiwgIlQxMDI3IiwgIlQxMDI5IiwgIlQxMDMwIiwgIlQxMDMzIiwgIlQxMDM5IiwgIlQxMDQwIiwgIlQxMDQxIiwgIlQxMDQ2IiwgIlQxMDQ3IiwgIlQxMDQ4IiwgIlQxMDQ5IiwgIlQxMDUyIiwgIlQxMDUzIiwgIlQxMDU2IiwgIlQxMDU3IiwgIlQxMDY4IiwgIlQxMDY5IiwgIlQxMDcyIiwgIlQxMDc0IiwgIlQxMDc4IiwgIlQxMDgwIiwgIlQxMDgzIiwgIlQxMDg3IiwgIlQxMDk4IiwgIlQxMTAyIiwgIlQxMTEwIiwgIlQxMTExIiwgIlQxMTE0IiwgIlQxMTE5IiwgIlQxMTIzIiwgIlQxMTI1IiwgIlQxMTMyIiwgIlQxMTMzIiwgIlQxMTM1IiwgIlQxMTM3IiwgIlQxMTc2IiwgIlQxMTg1IiwgIlQxMTg3IiwgIlQxMTg5IiwgIlQxMTkwIiwgIlQxMTk5IiwgIlQxMjAzIiwgIlQxMjEwIiwgIlQxMjExIiwgIlQxMjEyIiwgIlQxMjEzIiwgIlQxMjE5IiwgIlQxMjIwIiwgIlQxMjIxIiwgIlQxNDA0IiwgIlQxNDA2IiwgIlQxNDA5IiwgIlQxNDE3IiwgIlQxNDE4IiwgIlQxNDIwIiwgIlQxNDIxIiwgIlQxNDIyIiwgIlQxNDI0IiwgIlQxNDI4IiwgIlQxNDI5IiwgIlQxNDU2IiwgIlQxNDgwIiwgIlQxNDgxIiwgIlQxNDg1IiwgIlQxNDkxIiwgIlQxNTEyIiwgIlQxNTE3IiwgIlQxNTE4IiwgIlQxNTI2IiwgIlQxNTI4IiwgIlQxNTI5IiwgIlQxNTMwIiwgIlQxNTMxIiwgIlQxNTMyIiwgIlQxNTMzIiwgIlQxNTM1IiwgIlQxNTM3IiwgIlQxNTM4IiwgIlQxNTM5IiwgIlQxNTUwIiwgIlQxNTUyIiwgIlQxNTU0IiwgIlQxNTU1IiwgIlQxNTU3IiwgIlQxNTU4IiwgIlQxNTYwIiwgIlQxNTYzIiwgIlQxNTY3IiwgIlQxNTc3IiwgIlQxNTc4IiwgIlQxNTgwIiwgIlQxNTg5IiwgIlQxNTkwIiwgIlQxNTkxIiwgIlQxNTkyIiwgIlQxNTk0IiwgIlQxNTk1IiwgIlQxNjAxIiwgIlQxNjAyIiwgIlQxNjA2IiwgIlQxNjEzIiwgIlQxNjI3IiwgIlQxNjM0IiwgIlQxNjM1IiwgIlQxNjM4IiwgIlQxNjM5IiwgIlQxNjQwIiwgIlQxNjQzIiwgIlQxNjQ1IiwgIlQxNjQ2Il19LCAiTWFsd2FyZSBEZXRvbmF0aW9uIjogeyJ0YWN0aWNzIjogWyJUQTAwMDIiLCAiVEEwMDA1IiwgIlRBMDAxMSIsICJUQTAwMzAiLCAiVEEwMDM0IiwgIlRBMDA0MCIsICJUQTAxMDQiLCAiVEEwMTA4IiwgIlRBMDExMCJdLCAidGVjaG5pcXVlcyI6IFsiVDA4NTMiLCAiVDA4NjMiLCAiVDA4NjUiLCAiVDA4NzMiLCAiVDEwMjciLCAiVDEwNDciLCAiVDEwOTIiLCAiVDEyMDQiLCAiVDEyMTYiLCAiVDEyMTgiLCAiVDEyMTkiLCAiVDEyMjAiLCAiVDEyMjEiLCAiVDE0MDYiLCAiVDE0MDciLCAiVDE1NjEiLCAiVDE1NjkiLCAiVDE2MDQiLCAiVDE2NDMiXX0sICJOZXR3b3JrIEFuYWx5c2lzIjogeyJ0YWN0aWNzIjogWyJUQTAwMDkiLCAiVEEwMDEwIiwgIlRBMDAxMSIsICJUQTAwMzAiLCAiVEEwMDMyIiwgIlRBMDAzMyIsICJUQTAwMzYiLCAiVEEwMDM3Il0sICJ0ZWNobmlxdWVzIjogWyJUMTAwMSIsICJUMTAxMSIsICJUMTAyMCIsICJUMTAyOSIsICJUMTA0MSIsICJUMTA0OCIsICJUMTA1MiIsICJUMTA3NCIsICJUMTEzMiIsICJUMTQwNyIsICJUMTQyMyIsICJUMTQyOCIsICJUMTUyMSIsICJUMTUzNyIsICJUMTU2NyIsICJUMTU3MyIsICJUMTYzOSIsICJUMTY0NCIsICJUMTY0NiJdfSwgIk5ldHdvcmsgRGl2ZXJzaXR5IjogeyJ0YWN0aWNzIjogWyJUQTAwMDEiLCAiVEEwMDAzIiwgIlRBMDAwNiIsICJUQTAwMDciLCAiVEEwMDA5IiwgIlRBMDAzMCIsICJUQTAwMzQiLCAiVEEwMDQwIiwgIlRBMDA0MyIsICJUQTAxMDAiLCAiVEEwMTAyIiwgIlRBMDEwOCJdLCAidGVjaG5pcXVlcyI6IFsiVDA4NDIiLCAiVDA4NDYiLCAiVDA4NjAiLCAiVDA4ODMiLCAiVDA4ODciLCAiVDEwMTgiLCAiVDEwNDAiLCAiVDEwNDYiLCAiVDExMzMiLCAiVDExMzUiLCAiVDE0OTkiLCAiVDE1MzAiLCAiVDE1MzgiLCAiVDE1ODAiLCAiVDE1OTUiLCAiVDE2MDQiLCAiVDE2NDIiXX0sICJOZXR3b3JrIE1hbmlwdWxhdGlvbiI6IHsidGFjdGljcyI6IFsiVEEwMDAxIiwgIlRBMDAwMiIsICJUQTAwMDMiLCAiVEEwMDA1IiwgIlRBMDAwNiIsICJUQTAwMDciLCAiVEEwMDA4IiwgIlRBMDAwOSIsICJUQTAwMTAiLCAiVEEwMDExIiwgIlRBMDAzMCIsICJUQTAwMzIiLCAiVEEwMDMzIiwgIlRBMDAzNCIsICJUQTAwMzUiLCAiVEEwMDM2IiwgIlRBMDAzNyIsICJUQTAwNDAiLCAiVEEwMDQzIiwgIlRBMDEwMCIsICJUQTAxMDEiLCAiVEEwMTAyIiwgIlRBMDEwMyIsICJUQTAxMDQiLCAiVEEwMTA1IiwgIlRBMDEwNiIsICJUQTAxMDciLCAiVEEwMTA4IiwgIlRBMDEwOSIsICJUQTAxMTAiXSwgInRlY2huaXF1ZXMiOiBbIlQwODAwIiwgIlQwODAyIiwgIlQwODA0IiwgIlQwODA2IiwgIlQwODEzIiwgIlQwODE0IiwgIlQwODE1IiwgIlQwODIxIiwgIlQwODI2IiwgIlQwODI3IiwgIlQwODI5IiwgIlQwODM3IiwgIlQwODM4IiwgIlQwODM5IiwgIlQwODQwIiwgIlQwODQyIiwgIlQwODQ1IiwgIlQwODQ2IiwgIlQwODU1IiwgIlQwODU2IiwgIlQwODU3IiwgIlQwODU4IiwgIlQwODYwIiwgIlQwODY3IiwgIlQwODY5IiwgIlQwODc4IiwgIlQwODgwIiwgIlQwODgyIiwgIlQwODg0IiwgIlQwODg1IiwgIlQwODg2IiwgIlQwODg5IiwgIlQxMDA4IiwgIlQxMDExIiwgIlQxMDE4IiwgIlQxMDIwIiwgIlQxMDIxIiwgIlQxMDI5IiwgIlQxMDMwIiwgIlQxMDM5IiwgIlQxMDQwIiwgIlQxMDQxIiwgIlQxMDQ2IiwgIlQxMDQ4IiwgIlQxMDUyIiwgIlQxMDcxIiwgIlQxMDgwIiwgIlQxMDkwIiwgIlQxMDk1IiwgIlQxMTAyIiwgIlQxMTA0IiwgIlQxMTA1IiwgIlQxMTExIiwgIlQxMTE5IiwgIlQxMTIzIiwgIlQxMTI1IiwgIlQxMTMyIiwgIlQxMTM1IiwgIlQxMTg3IiwgIlQxMjAwIiwgIlQxMjA1IiwgIlQxMjE5IiwgIlQxNDA3IiwgIlQxNDIxIiwgIlQxNDIyIiwgIlQxNDIzIiwgIlQxNDI4IiwgIlQxNDM3IiwgIlQxNDY0IiwgIlQxNDgxIiwgIlQxNDk4IiwgIlQxNDk5IiwgIlQxNTEyIiwgIlQxNTIxIiwgIlQxNTMwIiwgIlQxNTM3IiwgIlQxNTQ0IiwgIlQxNTYzIiwgIlQxNTY3IiwgIlQxNTY4IiwgIlQxNTcwIiwgIlQxNTcxIiwgIlQxNTcyIiwgIlQxNTczIiwgIlQxNTgwIiwgIlQxNTgyIiwgIlQxNTk1IiwgIlQxNTk5IiwgIlQxNjA0IiwgIlQxNjEwIiwgIlQxNjE2IiwgIlQxNjM3IiwgIlQxNjM5IiwgIlQxNjQyIiwgIlQxNjQzIiwgIlQxNjQ0IiwgIlQxNjQ2Il19LCAiTmV0d29yayBNb25pdG9yaW5nIjogeyJ0YWN0aWNzIjogWyJUQTAwMDMiLCAiVEEwMDA1IiwgIlRBMDAwNiIsICJUQTAwMDgiLCAiVEEwMDA5IiwgIlRBMDAxMCIsICJUQTAwMTEiLCAiVEEwMDMwIiwgIlRBMDAzMiIsICJUQTAwMzMiLCAiVEEwMDM0IiwgIlRBMDAzNSIsICJUQTAwMzYiLCAiVEEwMDM3IiwgIlRBMDA0MCIsICJUQTAxMDAiLCAiVEEwMTAxIiwgIlRBMDEwMyIsICJUQTAxMDQiLCAiVEEwMTA1IiwgIlRBMDEwNiIsICJUQTAxMDciLCAiVEEwMTEwIl0sICJ0ZWNobmlxdWVzIjogWyJUMDgwMSIsICJUMDgwMiIsICJUMDgwNiIsICJUMDgwNyIsICJUMDgxMyIsICJUMDgxNCIsICJUMDgxNSIsICJUMDgyMCIsICJUMDgyMSIsICJUMDgyNiIsICJUMDgyNyIsICJUMDgyOSIsICJUMDgzNyIsICJUMDgzOCIsICJUMDg1NSIsICJUMDg1NiIsICJUMDg1OCIsICJUMDg2OCIsICJUMDg2OSIsICJUMDg3MSIsICJUMDg4MCIsICJUMDg4MSIsICJUMDg4MiIsICJUMDg4NSIsICJUMDg4OSIsICJUMTAwOCIsICJUMTAxMSIsICJUMTAyMCIsICJUMTAyMSIsICJUMTAyOSIsICJUMTAzMCIsICJUMTA0MSIsICJUMTA0OCIsICJUMTA1MiIsICJUMTA3MSIsICJUMTA5MCIsICJUMTA5NSIsICJUMTEwMiIsICJUMTEwNSIsICJUMTEzMiIsICJUMTIwNSIsICJUMTQyMSIsICJUMTQyMiIsICJUMTQyMyIsICJUMTQyOCIsICJUMTQzNyIsICJUMTQ2NCIsICJUMTQ4MSIsICJUMTQ5OCIsICJUMTUwOSIsICJUMTUzNyIsICJUMTU0NCIsICJUMTU1NyIsICJUMTU2NyIsICJUMTU3MCIsICJUMTU3MSIsICJUMTU3MiIsICJUMTU4MiIsICJUMTU5OSIsICJUMTYwMCIsICJUMTYwNCIsICJUMTYzOCIsICJUMTYzOSIsICJUMTY0MyIsICJUMTY0NCIsICJUMTY0NiJdfSwgIk9wZXJhdGlvbmFsIE9iamVjdGl2ZSI6IHsidGFjdGljcyI6IFtdLCAidGVjaG5pcXVlcyI6IFtdfSwgIlBlcmlwaGVyYWwgTWFuYWdlbWVudCI6IHsidGFjdGljcyI6IFsiVEEwMDAxIiwgIlRBMDAwNyIsICJUQTAwMDgiLCAiVEEwMDA5IiwgIlRBMDAxMCIsICJUQTAwMTEiLCAiVEEwMDI3IiwgIlRBMDAzMyIsICJUQTAwMzUiLCAiVEEwMTA4Il0sICJ0ZWNobmlxdWVzIjogWyJUMDg0NyIsICJUMDg2NCIsICJUMTAyNSIsICJUMTA1MiIsICJUMTA5MSIsICJUMTA5MiIsICJUMTEyMCIsICJUMTEyMyIsICJUMTEyNSIsICJUMTEzNSIsICJUMTQyOSIsICJUMTQ1OCIsICJUMTUxMiJdfSwgIlBlcnNvbmEgQ3JlYXRpb24iOiB7InRhY3RpY3MiOiBbXSwgInRlY2huaXF1ZXMiOiBbXX0sICJQZXJzb25hcyI6IHsidGFjdGljcyI6IFsiVEEwMDAxIiwgIlRBMDAwMiIsICJUQTAwMDMiLCAiVEEwMDA0IiwgIlRBMDAwNSIsICJUQTAwMDYiLCAiVEEwMDA3IiwgIlRBMDAwOSIsICJUQTAwMTEiLCAiVEEwMDI3IiwgIlRBMDAzMSIsICJUQTAwMzIiLCAiVEEwMDM0IiwgIlRBMDAzNSIsICJUQTAwMzciLCAiVEEwMDQwIiwgIlRBMDA0MyIsICJUQTAxMDAiLCAiVEEwMTA0IiwgIlRBMDEwOCIsICJUQTAxMDkiLCAiVEEwMTEwIl0sICJ0ZWNobmlxdWVzIjogWyJUMDgwMiIsICJUMDgxMSIsICJUMDgxMiIsICJUMDgyMiIsICJUMDg1MiIsICJUMDg1OSIsICJUMDg2MyIsICJUMDg5MSIsICJUMTAzMyIsICJUMTA2OSIsICJUMTA3OCIsICJUMTA4MyIsICJUMTA4NyIsICJUMTA5MiIsICJUMTA5OCIsICJUMTExMyIsICJUMTExOSIsICJUMTEyNSIsICJUMTE5OSIsICJUMTIwNCIsICJUMTIxMiIsICJUMTIxNyIsICJUMTIxOSIsICJUMTQyMCIsICJUMTQ2MSIsICJUMTUxMiIsICJUMTUxMyIsICJUMTUxNyIsICJUMTUzMSIsICJUMTU1NSIsICJUMTU2NiIsICJUMTU4MiIsICJUMTU4OSIsICJUMTU5MyIsICJUMTU5NCIsICJUMTU5OCIsICJUMTYxNiIsICJUMTYzNCIsICJUMTYzNiIsICJUMTY0MCJdfSwgIlBvY2tldCBMaXR0ZXIiOiB7InRhY3RpY3MiOiBbIlRBMDAwMSIsICJUQTAwMDIiLCAiVEEwMDAzIiwgIlRBMDAwNCIsICJUQTAwMDUiLCAiVEEwMDA2IiwgIlRBMDAwNyIsICJUQTAwMDgiLCAiVEEwMDA5IiwgIlRBMDAxMCIsICJUQTAwMTEiLCAiVEEwMDMwIiwgIlRBMDAzMSIsICJUQTAwMzIiLCAiVEEwMDM0IiwgIlRBMDAzNSIsICJUQTAwNDAiLCAiVEEwMDQzIiwgIlRBMDEwMCIsICJUQTAxMDIiLCAiVEEwMTAzIiwgIlRBMDEwNSIsICJUQTAxMDciLCAiVEEwMTA4IiwgIlRBMDEwOSIsICJUQTAxMTAiXSwgInRlY2huaXF1ZXMiOiBbIlQwODAwIiwgIlQwODAxIiwgIlQwODAyIiwgIlQwODA5IiwgIlQwODExIiwgIlQwODEyIiwgIlQwODIwIiwgIlQwODI2IiwgIlQwODI3IiwgIlQwODI5IiwgIlQwODMwIiwgIlQwODQyIiwgIlQwODQ2IiwgIlQwODUyIiwgIlQwODU5IiwgIlQwODYwIiwgIlQwODY4IiwgIlQwODc3IiwgIlQwODgwIiwgIlQwODgzIiwgIlQwODg4IiwgIlQxMDAzIiwgIlQxMDA1IiwgIlQxMDA3IiwgIlQxMDEwIiwgIlQxMDEyIiwgIlQxMDE2IiwgIlQxMDE4IiwgIlQxMDIwIiwgIlQxMDI1IiwgIlQxMDMzIiwgIlQxMDM5IiwgIlQxMDQwIiwgIlQxMDQ2IiwgIlQxMDQ3IiwgIlQxMDQ5IiwgIlQxMDU2IiwgIlQxMDU3IiwgIlQxMDY5IiwgIlQxMDc4IiwgIlQxMDgyIiwgIlQxMDgzIiwgIlQxMDg3IiwgIlQxMTEzIiwgIlQxMTE0IiwgIlQxMTE1IiwgIlQxMTE5IiwgIlQxMTIwIiwgIlQxMTIzIiwgIlQxMTI0IiwgIlQxMTI1IiwgIlQxMTMzIiwgIlQxMTM1IiwgIlQxMTg1IiwgIlQxMjEzIiwgIlQxMjE3IiwgIlQxMjE5IiwgIlQxNDA5IiwgIlQxNDE0IiwgIlQxNDE3IiwgIlQxNDE4IiwgIlQxNDIwIiwgIlQxNDIxIiwgIlQxNDIyIiwgIlQxNDIzIiwgIlQxNDI0IiwgIlQxNDI2IiwgIlQxNDI5IiwgIlQxNDg1IiwgIlQxNDk3IiwgIlQxNTEyIiwgIlQxNTEzIiwgIlQxNTE4IiwgIlQxNTI2IiwgIlQxNTMwIiwgIlQxNTMzIiwgIlQxNTM4IiwgIlQxNTU1IiwgIlQxNTU3IiwgIlQxNTYzIiwgIlQxNTY1IiwgIlQxNTY2IiwgIlQxNTgwIiwgIlQxNTg5IiwgIlQxNTkwIiwgIlQxNTkxIiwgIlQxNTkyIiwgIlQxNTk1IiwgIlQxNTk4IiwgIlQxNjAwIiwgIlQxNjAyIiwgIlQxNjEzIiwgIlQxNjE0IiwgIlQxNjMzIiwgIlQxNjM2IiwgIlQxNjM4IiwgIlQxNjQxIl19LCAiU2VjdXJpdHkgQ29udHJvbHMiOiB7InRhY3RpY3MiOiBbIlRBMDAwMSIsICJUQTAwMDIiLCAiVEEwMDAzIiwgIlRBMDAwNCIsICJUQTAwMDUiLCAiVEEwMDA2IiwgIlRBMDAwNyIsICJUQTAwMDgiLCAiVEEwMDA5IiwgIlRBMDAxMCIsICJUQTAwMTEiLCAiVEEwMDI3IiwgIlRBMDAyOCIsICJUQTAwMjkiLCAiVEEwMDMwIiwgIlRBMDAzMSIsICJUQTAwMzMiLCAiVEEwMDM0IiwgIlRBMDAzNSIsICJUQTAwMzYiLCAiVEEwMDM3IiwgIlRBMDA0MCIsICJUQTAwNDEiLCAiVEEwMTAwIiwgIlRBMDEwMyIsICJUQTAxMDQiLCAiVEEwMTA1IiwgIlRBMDEwNiIsICJUQTAxMDciLCAiVEEwMTA4IiwgIlRBMDEwOSIsICJUQTAxMTAiLCAiVEEwMTExIl0sICJ0ZWNobmlxdWVzIjogWyJUMDgwMCIsICJUMDgwNyIsICJUMDgwOSIsICJUMDgxMCIsICJUMDgxMSIsICJUMDgyMSIsICJUMDgyMiIsICJUMDgyNiIsICJUMDgyNyIsICJUMDgyOSIsICJUMDgzOCIsICJUMDgzOSIsICJUMDg0MyIsICJUMDg0NSIsICJUMDg0NyIsICJUMDg1MSIsICJUMDg1NSIsICJUMDg1NiIsICJUMDg1NyIsICJUMDg1OCIsICJUMDg2NiIsICJUMDg3MSIsICJUMDg3MiIsICJUMDg4MCIsICJUMDg4MSIsICJUMDg4MiIsICJUMDg4OSIsICJUMDg5MCIsICJUMTAwNSIsICJUMTAwOCIsICJUMTAxMSIsICJUMTAxNCIsICJUMTAyMCIsICJUMTAyOSIsICJUMTAzMCIsICJUMTAzOSIsICJUMTA0MSIsICJUMTA0NyIsICJUMTA0OCIsICJUMTA1MiIsICJUMTA1NSIsICJUMTA1OSIsICJUMTA2OCIsICJUMTA3MCIsICJUMTA3MiIsICJUMTA4MCIsICJUMTA5MSIsICJUMTA5MiIsICJUMTA5OCIsICJUMTExMCIsICJUMTExMSIsICJUMTExMiIsICJUMTEzNCIsICJUMTEzNSIsICJUMTEzNiIsICJUMTE4NyIsICJUMTE5NyIsICJUMTE5OSIsICJUMTIwMCIsICJUMTIwMyIsICJUMTIwNyIsICJUMTIxMCIsICJUMTIxMSIsICJUMTIxMiIsICJUMTIxMyIsICJUMTIyMiIsICJUMTQwNCIsICJUMTQwNyIsICJUMTQyOCIsICJUMTQ1OCIsICJUMTQ4OSIsICJUMTUxNiIsICJUMTUyNSIsICJUMTUyOCIsICJUMTUzMCIsICJUMTUzMSIsICJUMTUzMyIsICJUMTUzNSIsICJUMTUzNyIsICJUMTUzOSIsICJUMTU0MiIsICJUMTU0MyIsICJUMTU0NiIsICJUMTU0OCIsICJUMTU1MCIsICJUMTU1MyIsICJUMTU1NiIsICJUMTU1OCIsICJUMTU2MiIsICJUMTU2MyIsICJUMTU2NyIsICJUMTU3NCIsICJUMTU3NyIsICJUMTU4MiIsICJUMTU5OSIsICJUMTYwMCIsICJUMTYwMSIsICJUMTYwMiIsICJUMTYwNCIsICJUMTYwNiIsICJUMTYwOSIsICJUMTYxMSIsICJUMTYxMiIsICJUMTYxNiIsICJUMTYxNyIsICJUMTYyMyIsICJUMTYyNCIsICJUMTYyNSIsICJUMTYyNiIsICJUMTYyOSIsICJUMTYzMCIsICJUMTYzMSIsICJUMTYzMiIsICJUMTYzNCIsICJUMTYzNSIsICJUMTYzOSIsICJUMTY0MCIsICJUMTY0MyIsICJUMTY0NCIsICJUMTY0NiJdfSwgIlNvZnR3YXJlIE1hbmlwdWxhdGlvbiI6IHsidGFjdGljcyI6IFsiVEEwMDAxIiwgIlRBMDAwMiIsICJUQTAwMDMiLCAiVEEwMDA0IiwgIlRBMDAwNSIsICJUQTAwMDYiLCAiVEEwMDA3IiwgIlRBMDAwOCIsICJUQTAwMDkiLCAiVEEwMDExIiwgIlRBMDAyNyIsICJUQTAwMjgiLCAiVEEwMDI5IiwgIlRBMDAzMCIsICJUQTAwMzEiLCAiVEEwMDMyIiwgIlRBMDAzMyIsICJUQTAwMzQiLCAiVEEwMDM1IiwgIlRBMDAzNyIsICJUQTAwNDAiLCAiVEEwMDQxIiwgIlRBMDEwMCIsICJUQTAxMDIiLCAiVEEwMTAzIiwgIlRBMDEwNCIsICJUQTAxMDYiLCAiVEEwMTA3IiwgIlRBMDEwOCIsICJUQTAxMDkiLCAiVEEwMTEwIiwgIlRBMDExMSJdLCAidGVjaG5pcXVlcyI6IFsiVDA4MDAiLCAiVDA4MDIiLCAiVDA4MDMiLCAiVDA4MDQiLCAiVDA4MDUiLCAiVDA4MDYiLCAiVDA4MDciLCAiVDA4MDkiLCAiVDA4MjEiLCAiVDA4MjIiLCAiVDA4MjMiLCAiVDA4MzQiLCAiVDA4MzUiLCAiVDA4MzYiLCAiVDA4MzgiLCAiVDA4MzkiLCAiVDA4NDAiLCAiVDA4NDIiLCAiVDA4NDMiLCAiVDA4NDUiLCAiVDA4NDYiLCAiVDA4NTUiLCAiVDA4NTYiLCAiVDA4NTciLCAiVDA4NjAiLCAiVDA4NjciLCAiVDA4NzQiLCAiVDA4NzgiLCAiVDA4ODciLCAiVDA4ODgiLCAiVDA4ODkiLCAiVDEwMDEiLCAiVDEwMDUiLCAiVDEwMDYiLCAiVDEwMDciLCAiVDEwMTIiLCAiVDEwMTYiLCAiVDEwMTgiLCAiVDEwMjciLCAiVDEwMzMiLCAiVDEwNDAiLCAiVDEwNDYiLCAiVDEwNDciLCAiVDEwNDkiLCAiVDEwNTMiLCAiVDEwNTciLCAiVDEwNTkiLCAiVDEwNjkiLCAiVDEwNzIiLCAiVDEwODIiLCAiVDEwODMiLCAiVDEwODciLCAiVDEwOTEiLCAiVDExMDYiLCAiVDExMTAiLCAiVDExMTkiLCAiVDExMjAiLCAiVDExMjQiLCAiVDExMjkiLCAiVDExMzQiLCAiVDExMzUiLCAiVDExNDAiLCAiVDExOTciLCAiVDEyMDEiLCAiVDEyMDIiLCAiVDEyMTYiLCAiVDEyMTciLCAiVDEyMTgiLCAiVDEyMjAiLCAiVDEzOTgiLCAiVDE0MDQiLCAiVDE0MDYiLCAiVDE0MDkiLCAiVDE0MTgiLCAiVDE0MjAiLCAiVDE0MjEiLCAiVDE0MjIiLCAiVDE0MjMiLCAiVDE0MjQiLCAiVDE0MjYiLCAiVDE0MzAiLCAiVDE0NTgiLCAiVDE0NzEiLCAiVDE0ODUiLCAiVDE0ODYiLCAiVDE0OTYiLCAiVDE1MTYiLCAiVDE1MTgiLCAiVDE1MjEiLCAiVDE1MzEiLCAiVDE1MzIiLCAiVDE1MzMiLCAiVDE1NTQiLCAiVDE1NTkiLCAiVDE1NjAiLCAiVDE1NjEiLCAiVDE1NjQiLCAiVDE1NjkiLCAiVDE1NzMiLCAiVDE1NzUiLCAiVDE1NzciLCAiVDE1NzgiLCAiVDE1ODIiLCAiVDE2MDMiLCAiVDE2MTMiLCAiVDE2MTQiLCAiVDE2MTYiLCAiVDE2MjMiLCAiVDE2MjgiLCAiVDE2MzUiLCAiVDE2NDAiLCAiVDE2NDUiXX0sICJTdG9yeWJvYXJkaW5nIjogeyJ0YWN0aWNzIjogW10sICJ0ZWNobmlxdWVzIjogW119LCAiU3lzdGVtIEFjdGl2aXR5IE1vbml0b3JpbmciOiB7InRhY3RpY3MiOiBbIlRBMDAwMSIsICJUQTAwMDIiLCAiVEEwMDAzIiwgIlRBMDAwNCIsICJUQTAwMDUiLCAiVEEwMDA2IiwgIlRBMDAwOCIsICJUQTAwMTEiLCAiVEEwMDI3IiwgIlRBMDAyOCIsICJUQTAwMzAiLCAiVEEwMDMzIiwgIlRBMDAzNCIsICJUQTAwMzUiLCAiVEEwMDQwIiwgIlRBMDA0MSIsICJUQTAxMDUiLCAiVEEwMTA3IiwgIlRBMDEwOSIsICJUQTAxMTAiXSwgInRlY2huaXF1ZXMiOiBbIlQwODEyIiwgIlQwODI5IiwgIlQwODMyIiwgIlQwODU5IiwgIlQwODc4IiwgIlQxMDAzIiwgIlQxMDM2IiwgIlQxMDUzIiwgIlQxMDcwIiwgIlQxMDc4IiwgIlQxMDgwIiwgIlQxMDkxIiwgIlQxMDkyIiwgIlQxMDk4IiwgIlQxMTEwIiwgIlQxMTEyIiwgIlQxMTMzIiwgIlQxMTM2IiwgIlQxMTM3IiwgIlQxMjA3IiwgIlQxNDI5IiwgIlQxNDU4IiwgIlQxNDkwIiwgIlQxNDk1IiwgIlQxNTE2IiwgIlQxNTMxIiwgIlQxNTQxIiwgIlQxNTUyIiwgIlQxNTU1IiwgIlQxNTYyIiwgIlQxNTY2IiwgIlQxNjAzIiwgIlQxNjE3IiwgIlQxNjI5IiwgIlQxNjMwIiwgIlQxNjM2IiwgIlQxNjQwIl19LCAiVGhyZWF0IE1vZGVsIjogeyJ0YWN0aWNzIjogW10sICJ0ZWNobmlxdWVzIjogW119fQ==
eyJHMDAwMSI6IFsiVDEwMDMiLCAiVDEwMDUiLCAiVDEwNzgiLCAiVDExODkiLCAiVDExOTAiLCAiVDEyMDMiLCAiVDE1NTMiLCAiVDE1NjAiLCAiVDE1NjYiXSwgIkcwMDAyIjogW10sICJHMDAwMyI6IFtdLCAiRzAwMDQiOiBbIlQxMDA1IiwgIlQxMDA3IiwgIlQxMDE2IiwgIlQxMDE4IiwgIlQxMDIwIiwgIlQxMDI3IiwgIlQxMDMzIiwgIlQxMDQxIiwgIlQxMDQ5IiwgIlQxMDU3IiwgIlQxMDU5IiwgIlQxMDc4IiwgIlQxMDgyIiwgIlQxMDgzIiwgIlQxMTA1IiwgIlQxMTE5IiwgIlQxMTMzIiwgIlQxMTQwIiwgIlQxMTkwIiwgIlQxNTYwIl0sICJHMDAwNSI6IFsiVDEyMDMiXSwgIkcwMDA2IjogWyJUMTAwNSIsICJUMTAwNyIsICJUMTAxNiIsICJUMTA0OSIsICJUMTA1NyIsICJUMTExOSIsICJUMTEzNSJdLCAiRzAwMDciOiBbIlQxMDAzIiwgIlQxMDA1IiwgIlQxMDE0IiwgIlQxMDI1IiwgIlQxMDI3IiwgIlQxMDMwIiwgIlQxMDM2IiwgIlQxMDM5IiwgIlQxMDQwIiwgIlQxMDU3IiwgIlQxMDY4IiwgIlQxMDc4IiwgIlQxMDgzIiwgIlQxMDkxIiwgIlQxMDkyIiwgIlQxMTA1IiwgIlQxMTEwIiwgIlQxMTEzIiwgIlQxMTE5IiwgIlQxMTIwIiwgIlQxMTMzIiwgIlQxMTQwIiwgIlQxMTg5IiwgIlQxMTkwIiwgIlQxMTk5IiwgIlQxMjAzIiwgIlQxMjEwIiwgIlQxMjExIiwgIlQxMjEzIiwgIlQxMjIxIiwgIlQxNDk4IiwgIlQxNTI4IiwgIlQxNTYwIiwgIlQxNTY3IiwgIlQxNTk4Il0sICJHMDAwOCI6IFsiVDEwNzgiLCAiVDEyMTkiXSwgIkcwMDA5IjogWyJUMTAxOCIsICJUMTA0NyIsICJUMTA1NyJdLCAiRzAwMTAiOiBbIlQxMDA1IiwgIlQxMDA3IiwgIlQxMDEyIiwgIlQxMDE2IiwgIlQxMDE4IiwgIlQxMDI1IiwgIlQxMDQ5IiwgIlQxMDU1IiwgIlQxMDU3IiwgIlQxMDY4IiwgIlQxMDgyIiwgIlQxMDgzIiwgIlQxMDkwIiwgIlQxMTAyIiwgIlQxMTA1IiwgIlQxMTA2IiwgIlQxMTEwIiwgIlQxMTEyIiwgIlQxMTIwIiwgIlQxMTI0IiwgIlQxMTQwIiwgIlQxMTg5IiwgIlQxMjAxIiwgIlQxMjEzIiwgIlQxNTcwIiwgIlQxNjE1Il0sICJHMDAxMSI6IFsiVDEwNzgiXSwgIkcwMDEyIjogWyJUMTAxNiIsICJUMTAyNyIsICJUMTA1NyIsICJUMTA4MCIsICJUMTA4MiIsICJUMTA4MyIsICJUMTA5MSIsICJUMTEwNSIsICJUMTEyNCIsICJUMTE0MCIsICJUMTE4OSIsICJUMTIwMyIsICJUMTQ5NyJdLCAiRzAwMTMiOiBbXSwgIkcwMDE2IjogWyJUMTAwNSIsICJUMTAzNyIsICJUMTA0NyIsICJUMTA2OCIsICJUMTA3OCIsICJUMTEwNSIsICJUMTEzMyIsICJUMTE5MCIsICJUMTE5OSIsICJUMTIwMyIsICJUMTU2OCIsICJUMTU3MyIsICJUMTYyMSIsICJUMTY0OSIsICJUMTY1MSJdLCAiRzAwMTciOiBbXSwgIkcwMDE4IjogWyJUMTAwNyIsICJUMTAxNiIsICJUMTA0OSIsICJUMTA4MiIsICJUMTA4MyIsICJUMTIwMyJdLCAiRzAwMTkiOiBbIlQxMDE2IiwgIlQxMDE4IiwgIlQxMDQ2IiwgIlQxMDQ3Il0sICJHMDAyMCI6IFsiVDExMjAiXSwgIkcwMDIxIjogWyJUMTAyNyIsICJUMTA1NyIsICJUMTEwNSIsICJUMTE0MCJdLCAiRzAwMjIiOiBbIlQxMDA1IiwgIlQxMDE2IiwgIlQxMDE4IiwgIlQxMDI3IiwgIlQxMDMzIiwgIlQxMDQxIiwgIlQxMDQ5IiwgIlQxMDU3IiwgIlQxMDY5IiwgIlQxMDgyIiwgIlQxMDgzIiwgIlQxMDk1IiwgIlQxMDk4IiwgIlQxMTA0IiwgIlQxMTA1IiwgIlQxMjAzIl0sICJHMDAyMyI6IFtdLCAiRzAwMjQiOiBbIlQxMDI3Il0sICJHMDAyNSI6IFsiVDE1ODUiXSwgIkcwMDI2IjogWyJUMTAyNyIsICJUMTA3OCIsICJUMTA4MiIsICJUMTA4MyIsICJUMTEwNSIsICJUMTEzMyJdLCAiRzAwMjciOiBbIlQxMDA1IiwgIlQxMDEyIiwgIlQxMDE2IiwgIlQxMDE4IiwgIlQxMDI3IiwgIlQxMDMwIiwgIlQxMDMzIiwgIlQxMDQ2IiwgIlQxMDQ3IiwgIlQxMDQ5IiwgIlQxMDY4IiwgIlQxMDc4IiwgIlQxMTA1IiwgIlQxMTEyIiwgIlQxMTE5IiwgIlQxMTMzIiwgIlQxMTQwIiwgIlQxMTg5IiwgIlQxMTkwIiwgIlQxMTk5IiwgIlQxMjAzIiwgIlQxMjEwIl0sICJHMDAyOCI6IFsiVDEwNzIiXSwgIkcwMDI5IjogW10sICJHMDAzMCI6IFtdLCAiRzAwMzIiOiBbIlQwODY1IiwgIlQxMDA1IiwgIlQxMDA4IiwgIlQxMDEwIiwgIlQxMDEyIiwgIlQxMDE2IiwgIlQxMDI3IiwgIlQxMDMzIiwgIlQxMDQxIiwgIlQxMDQ2IiwgIlQxMDQ3IiwgIlQxMDQ5IiwgIlQxMDU3IiwgIlQxMDcwIiwgIlQxMDc4IiwgIlQxMDgyIiwgIlQxMDgzIiwgIlQxMDk4IiwgIlQxMTA0IiwgIlQxMTA1IiwgIlQxMTA2IiwgIlQxMTI0IiwgIlQxMTQwIiwgIlQxMTg5IiwgIlQxMjAyIiwgIlQxMjAzIiwgIlQxMjE4IiwgIlQxNDg1IiwgIlQxNDg5IiwgIlQxNTI5IiwgIlQxNTYwIiwgIlQxNTcxIiwgIlQxNTkxIiwgIlQxNjIwIl0sICJHMDAzMyI6IFsiVDEwMDMiLCAiVDEwMDciLCAiVDEwNDkiLCAiVDEwNTciXSwgIkcwMDM0IjogWyJUMDgwNyIsICJUMDgxOSIsICJUMDg4NCIsICJUMTAwNSIsICJUMTAxOCIsICJUMTAyNyIsICJUMTAzMyIsICJUMTA0MCIsICJUMTA0MSIsICJUMTA0NyIsICJUMTA0OSIsICJUMTA3MiIsICJUMTA3OCIsICJUMTA4MiIsICJUMTA4MyIsICJUMTA5MCIsICJUMTEwNSIsICJUMTEzMyIsICJUMTE0MCIsICJUMTE5OSIsICJUMTIwMyIsICJUMTIxOSIsICJUMTQ4NSIsICJUMTQ4NiIsICJUMTQ5OSIsICJUMTU3MCIsICJUMTU3MSIsICJUMTU5MyIsICJUMTU5NCJdLCAiRzAwMzUiOiBbIlQwODE3IiwgIlQwODYyIiwgIlQxMDA1IiwgIlQxMDEyIiwgIlQxMDE2IiwgIlQxMDE4IiwgIlQxMDMzIiwgIlQxMDM2IiwgIlQxMDU5IiwgIlQxMDc4IiwgIlQxMDgzIiwgIlQxMDk4IiwgIlQxMTA1IiwgIlQxMTEwIiwgIlQxMTEyIiwgIlQxMTEzIiwgIlQxMTMzIiwgIlQxMTM1IiwgIlQxMTg3IiwgIlQxMTg5IiwgIlQxMTkwIiwgIlQxMjAzIiwgIlQxMjEwIiwgIlQxMjIxIiwgIlQxNTYwIl0sICJHMDAzNiI6IFtdLCAiRzAwMzciOiBbIlQxMDA1IiwgIlQxMDE4IiwgIlQxMDQ2IiwgIlQxMDQ3IiwgIlQxMDU5IiwgIlQxMDY4IiwgIlQxMDc4IiwgIlQxMDk1IiwgIlQxMTAyIiwgIlQxMTE5IiwgIlQxMTM0IiwgIlQxMjEzIiwgIlQxNTU1IiwgIlQxNTYwIiwgIlQxNTcyIl0sICJHMDAzOCI6IFsiVDEwMDUiLCAiVDEwMTIiLCAiVDEwMTYiLCAiVDEwMzMiLCAiVDEwNDEiLCAiVDEwNDciLCAiVDEwNTciLCAiVDEwNTkiLCAiVDEwODIiLCAiVDE1NTUiXSwgIkcwMDM5IjogWyJUMTAwMyIsICJUMTA0NiIsICJUMTA3OCJdLCAiRzAwNDAiOiBbIlQxMDA1IiwgIlQxMDMzIiwgIlQxMDgyIiwgIlQxMDgzIiwgIlQxMTA1IiwgIlQxMTEyIiwgIlQxMTE5IiwgIlQxMTg5IiwgIlQxMTk3IiwgIlQxMjAzIiwgIlQxNTYwIl0sICJHMDA0MSI6IFtdLCAiRzAwNDMiOiBbIlQxMDI3IiwgIlQxMTEzIl0sICJHMDA0NCI6IFsiVDEwMTQiLCAiVDEwNTciLCAiVDEwODMiLCAiVDExMDUiXSwgIkcwMDQ1IjogWyJUMTAwNSIsICJUMTAxNiIsICJUMTAxOCIsICJUMTAyNyIsICJUMTAzNiIsICJUMTAzOSIsICJUMTA0NiIsICJUMTA0NyIsICJUMTA0OSIsICJUMTA3OCIsICJUMTA4MyIsICJUMTEwNSIsICJUMTEwNiIsICJUMTExOSIsICJUMTE0MCIsICJUMTE5MCIsICJUMTE5OSIsICJUMTIxMCIsICJUMTU2MCJdLCAiRzAwNDYiOiBbIlQxMDA1IiwgIlQxMDA4IiwgIlQxMDMzIiwgIlQxMDQ3IiwgIlQxMDU5IiwgIlQxMDc4IiwgIlQxMDkxIiwgIlQxMTA1IiwgIlQxMTEzIiwgIlQxMTI1IiwgIlQxMjEwIiwgIlQxMjE5IiwgIlQxNDg2IiwgIlQxNTcxIl0sICJHMDA0NyI6IFsiVDEwMDUiLCAiVDEwMjAiLCAiVDEwMjUiLCAiVDEwMjciLCAiVDEwMzMiLCAiVDEwMzkiLCAiVDEwNDEiLCAiVDEwNDciLCAiVDEwNTciLCAiVDEwODAiLCAiVDEwODIiLCAiVDEwODMiLCAiVDExMDIiLCAiVDExMDUiLCAiVDExMDYiLCAiVDExMTIiLCAiVDExMTMiLCAiVDExMTkiLCAiVDExMjAiLCAiVDExMzciLCAiVDExNDAiLCAiVDEyMjEiLCAiVDE0ODUiLCAiVDE1MzQiLCAiVDE1NjgiXSwgIkcwMDQ4IjogWyJUMTE4OSIsICJUMTIxOSJdLCAiRzAwNDkiOiBbIlQwODE3IiwgIlQwODUzIiwgIlQwODU5IiwgIlQwODY1IiwgIlQwODY5IiwgIlQxMDA3IiwgIlQxMDA4IiwgIlQxMDEyIiwgIlQxMDE2IiwgIlQxMDI3IiwgIlQxMDMzIiwgIlQxMDM2IiwgIlQxMDQ2IiwgIlQxMDQ3IiwgIlQxMDQ5IiwgIlQxMDU3IiwgIlQxMDU5IiwgIlQxMDc4IiwgIlQxMDgyIiwgIlQxMTA1IiwgIlQxMTEwIiwgIlQxMTEzIiwgIlQxMTE5IiwgIlQxMTIwIiwgIlQxMTMzIiwgIlQxMTQwIiwgIlQxMjAxIiwgIlQxNTU1IiwgIlQxNTcyIl0sICJHMDA1MCI6IFsiVDEwMDMiLCAiVDEwMTIiLCAiVDEwMTYiLCAiVDEwMTgiLCAiVDEwMjciLCAiVDEwMzMiLCAiVDEwMzYiLCAiVDEwNDEiLCAiVDEwNDYiLCAiVDEwNDciLCAiVDEwNDkiLCAiVDEwNTUiLCAiVDEwNTkiLCAiVDEwNjgiLCAiVDEwNzIiLCAiVDEwODIiLCAiVDEwODMiLCAiVDExMDIiLCAiVDExMDUiLCAiVDExMTIiLCAiVDExMzUiLCAiVDExMzciLCAiVDExODkiLCAiVDEyMDMiLCAiVDE1NjAiLCAiVDE1NzAiLCAiVDE1NzEiLCAiVDE1ODkiXSwgIkcwMDUxIjogWyJUMTAzMyIsICJUMTA3OCIsICJUMTU3MCJdLCAiRzAwNTIiOiBbIlQxMDkwIl0sICJHMDA1MyI6IFsiVDEwMTgiLCAiVDEwNTkiLCAiVDEwNzgiLCAiVDExMTAiLCAiVDExMTkiLCAiVDExMzMiXSwgIkcwMDU0IjogWyJUMTAwMyIsICJUMTAzOSIsICJUMTA4MiIsICJUMTA4MyIsICJUMTEzNSJdLCAiRzAwNTUiOiBbXSwgIkcwMDU2IjogWyJUMTE4OSJdLCAiRzAwNTkiOiBbIlQxMDA1IiwgIlQxMDE2IiwgIlQxMDE4IiwgIlQxMDI3IiwgIlQxMDMzIiwgIlQxMDQ2IiwgIlQxMDQ3IiwgIlQxMDQ5IiwgIlQxMDU3IiwgIlQxMDcxIiwgIlQxMDgyIiwgIlQxMDgzIiwgIlQxMDkwIiwgIlQxMDk4IiwgIlQxMTA1IiwgIlQxMTEyIiwgIlQxMTEzIiwgIlQxMTE0IiwgIlQxMTg5IiwgIlQxMTkwIiwgIlQxNDgyIiwgIlQxNDg2IiwgIlQxNTYyIiwgIlQxNTY3IiwgIlQxNTcwIiwgIlQxNTcxIiwgIlQxNTcyIiwgIlQxNTczIiwgIlQxNTg5Il0sICJHMDA2MCI6IFsiVDEwMDUiLCAiVDEwMDciLCAiVDEwMTgiLCAiVDEwMzYiLCAiVDEwMzkiLCAiVDEwODAiLCAiVDEwODMiLCAiVDExMDUiLCAiVDExMTMiLCAiVDExMjQiLCAiVDExNDAiLCAiVDExODkiLCAiVDEyMDMiLCAiVDE1MTgiXSwgIkcwMDYxIjogWyJUMTAxOCIsICJUMTAzMyIsICJUMTA0NyIsICJUMTA2OCIsICJUMTA3OCIsICJUMTA4MiIsICJUMTEwMiIsICJUMTEwNSIsICJUMTExMiIsICJUMTQ4MiIsICJUMTQ4NiJdLCAiRzAwNjIiOiBbIlQxMjAzIl0sICJHMDA2MyI6IFsiVDEwMjciXSwgIkcwMDY0IjogWyJUMDg1MiIsICJUMDg1MyIsICJUMDg2NSIsICJUMTAyNyIsICJUMTA0MCIsICJUMTA2OCIsICJUMTA3OCIsICJUMTEwNSIsICJUMTIwMyIsICJUMTU1NSIsICJUMTU3MSJdLCAiRzAwNjUiOiBbIlQxMDAzIiwgIlQxMDI3IiwgIlQxMDQxIiwgIlQxMDQ3IiwgIlQxMDc4IiwgIlQxMTA1IiwgIlQxMTMzIiwgIlQxMTQwIiwgIlQxMTg5IiwgIlQxMTk3IiwgIlQxMjAzIiwgIlQxNTM0IiwgIlQxNTYwIiwgIlQxNTcyIl0sICJHMDA2NiI6IFsiVDEwMjciLCAiVDExMDUiLCAiVDExODkiLCAiVDEyMDMiXSwgIkcwMDY3IjogWyJUMTAwNSIsICJUMTAyNyIsICJUMTAzMyIsICJUMTA1NSIsICJUMTA1NyIsICJUMTA1OSIsICJUMTA4MiIsICJUMTEwNSIsICJUMTEwNiIsICJUMTEyMCIsICJUMTEyMyIsICJUMTE4OSIsICJUMTIwMyIsICJUMTUyOSJdLCAiRzAwNjgiOiBbIlQxMDM2IiwgIlQxMDU1IiwgIlQxMDY4IiwgIlQxMDk1IiwgIlQxMTA1IiwgIlQxMTg5Il0sICJHMDA2OSI6IFsiVDEwMTYiLCAiVDEwMzMiLCAiVDEwNDEiLCAiVDEwNDciLCAiVDEwNDkiLCAiVDEwNTciLCAiVDEwODIiLCAiVDEwODMiLCAiVDExMDQiLCAiVDExMDUiLCAiVDExMTMiLCAiVDExNDAiLCAiVDExOTAiLCAiVDEyMDMiLCAiVDEyMTAiLCAiVDEyMTkiLCAiVDE1MTgiLCAiVDE1NTUiXSwgIkcwMDcwIjogWyJUMTAwNSIsICJUMTAyNyIsICJUMTA4MyIsICJUMTExMyIsICJUMTE4OSJdLCAiRzAwNzEiOiBbXSwgIkcwMDczIjogWyJUMTAxNiIsICJUMTAyNyIsICJUMTAzMyIsICJUMTA1OSIsICJUMTA4MiIsICJUMTExMiIsICJUMTE0MCIsICJUMTE4OSJdLCAiRzAwNzUiOiBbIlQxMTA1Il0sICJHMDA3NiI6IFsiVDEyMTkiXSwgIkcwMDc3IjogWyJUMTAxOCIsICJUMTA0NiIsICJUMTA4MyIsICJUMTE4OSIsICJUMTU1NSJdLCAiRzAwNzgiOiBbIlQxMTA1IiwgIlQxMTA2IiwgIlQxMTEyIiwgIlQxMTQwIl0sICJHMDA3OSI6IFsiVDExODciLCAiVDEyMjEiXSwgIkcwMDgwIjogWyJUMTA0NiIsICJUMTA1NSIsICJUMTA2OCIsICJUMTEwNSIsICJUMTIwMyIsICJUMTIxOSIsICJUMTIyMCIsICJUMTU3MiJdLCAiRzAwODEiOiBbIlQxMDE2IiwgIlQxMDIwIiwgIlQxMDI3IiwgIlQxMDMzIiwgIlQxMDQ2IiwgIlQxMDQ5IiwgIlQxMDU3IiwgIlQxMDgyIiwgIlQxMDgzIiwgIlQxMDkxIiwgIlQxMTA1IiwgIlQxMTA2IiwgIlQxMTE5IiwgIlQxMTM1IiwgIlQxMTQwIiwgIlQxMjAzIiwgIlQxMjIxIiwgIlQxNTE4IiwgIlQxNTczIl0sICJHMDA4MiI6IFsiVDEwMDUiLCAiVDEwMzMiLCAiVDEwNDkiLCAiVDEwNTciLCAiVDEwODIiLCAiVDEwODMiLCAiVDExMDUiLCAiVDExMDYiLCAiVDExMTAiLCAiVDExMTIiLCAiVDExMTUiLCAiVDExMzUiLCAiVDExODkiLCAiVDEyMTciLCAiVDE0ODUiLCAiVDE0ODYiLCAiVDE1MjkiXSwgIkcwMDgzIjogWyJUMTY1NyJdLCAiRzAwODQiOiBbIlQxMDI3Il0sICJHMDA4NSI6IFsiVDEwNzgiXSwgIkcwMDg3IjogWyJUMTAwMyIsICJUMTAwNSIsICJUMTAxMiIsICJUMTAxOCIsICJUMTAyNyIsICJUMTAzMyIsICJUMTA0MSIsICJUMTA0NiIsICJUMTA1NiIsICJUMTA1OSIsICJUMTA3OCIsICJUMTA4MyIsICJUMTEwNSIsICJUMTExMCIsICJUMTExMyIsICJUMTExNSIsICJUMTEzNSIsICJUMTE0MCIsICJUMTE5MCIsICJUMTE5NyIsICJUMTU1NSJdLCAiRzAwODgiOiBbIlQwODE3IiwgIlQwODU5IiwgIlQwODYyIiwgIlQwODg2IiwgIlQxMDc4IiwgIlQxMTMzIiwgIlQxNTcxIl0sICJHMDA4OSI6IFsiVDExMjQiLCAiVDEyMDMiXSwgIkcwMDkwIjogWyJUMTEwNSIsICJUMTE0MCIsICJUMTU3MSJdLCAiRzAwOTEiOiBbIlQxMDE4IiwgIlQxMDU1IiwgIlQxMDcyIiwgIlQxMDc4IiwgIlQxMTA1IiwgIlQxMTA2IiwgIlQxMTEyIiwgIlQxMTEzIiwgIlQxMTI1IiwgIlQxNTcxIl0sICJHMDA5MiI6IFsiVDEwMjciLCAiVDEwNjkiLCAiVDExMDUiLCAiVDExMDYiLCAiVDExMTIiLCAiVDExNDAiLCAiVDE0ODYiXSwgIkcwMDkzIjogWyJUMTAwNSIsICJUMTAxNiIsICJUMTAxOCIsICJUMTAyNyIsICJUMTAzMyIsICJUMTA0MSIsICJUMTA0NyIsICJUMTA0OSIsICJUMTA3OCIsICJUMTEwNSIsICJUMTEzMyIsICJUMTE5MCIsICJUMTU3MCJdLCAiRzAwOTQiOiBbIlQxMDA1IiwgIlQxMDA3IiwgIlQxMDEyIiwgIlQxMDE2IiwgIlQxMDI3IiwgIlQxMDM2IiwgIlQxMDQwIiwgIlQxMDQxIiwgIlQxMDU1IiwgIlQxMDU3IiwgIlQxMDgyIiwgIlQxMDgzIiwgIlQxMDk4IiwgIlQxMTA1IiwgIlQxMTExIiwgIlQxMTEyIiwgIlQxMTMzIiwgIlQxMTQwIiwgIlQxMTc2IiwgIlQxMTkwIiwgIlQxMjE5IiwgIlQxNTM0IiwgIlQxNTU3IiwgIlQxNTg3IiwgIlQxNTkxIiwgIlQxNTk0Il0sICJHMDA5NSI6IFsiVDExODkiXSwgIkcwMDk2IjogWyJUMTAwNSIsICJUMTAwOCIsICJUMTAxNCIsICJUMTAxNiIsICJUMTAyNyIsICJUMTAzMyIsICJUMTA0NiIsICJUMTA0NyIsICJUMTA0OSIsICJUMTA1NSIsICJUMTA3OCIsICJUMTA4MyIsICJUMTA5MCIsICJUMTA5OCIsICJUMTEwNCIsICJUMTEwNSIsICJUMTExMiIsICJUMTEzMyIsICJUMTEzNSIsICJUMTE5MCIsICJUMTE5NyIsICJUMTIwMyIsICJUMTQ4NiIsICJUMTQ5NiJdLCAiRzAwOTciOiBbXSwgIkcwMDk4IjogWyJUMTA0NiIsICJUMTEwNiIsICJUMTE5MCIsICJUMTIwMyJdLCAiRzAwOTkiOiBbIlQxMDI3IiwgIlQxMTA1IiwgIlQxNTcxIl0sICJHMDEwMCI6IFsiVDEwMDUiLCAiVDEwMjciLCAiVDEwNTciLCAiVDEwODIiLCAiVDEwODMiLCAiVDExMDIiLCAiVDEyMDMiLCAiVDEyMjEiLCAiVDE1MTgiXSwgIkcwMTAyIjogWyJUMTAwNSIsICJUMTAxNiIsICJUMTAxOCIsICJUMTAyMSIsICJUMTAzMyIsICJUMTA0MSIsICJUMTA0NyIsICJUMTA1NSIsICJUMTA3NCIsICJUMTA3OCIsICJUMTA4MiIsICJUMTEwNSIsICJUMTExMiIsICJUMTEzMyIsICJUMTEzNSIsICJUMTE5NyIsICJUMTIxMCIsICJUMTQ4OSIsICJUMTQ5MCIsICJUMTUxOCIsICJUMTU3MCJdLCAiRzAxMDMiOiBbIlQxMDI3Il0sICJHMDEwNSI6IFsiVDEwNDAiLCAiVDEwNDYiLCAiVDExMTAiLCAiVDExMzUiLCAiVDEyMDAiLCAiVDEyMTkiLCAiVDE1NzEiXSwgIkcwMTA2IjogWyJUMTAxNCIsICJUMTAxOCIsICJUMTAyNyIsICJUMTAzNyIsICJUMTA0NiIsICJUMTA1NyIsICJUMTA3MSIsICJUMTA4MiIsICJUMTEwMiIsICJUMTEwNSIsICJUMTE0MCIsICJUMTE5MCIsICJUMTQ5NiIsICJUMTU3MSJdLCAiRzAxMDciOiBbIlQxMDI3IiwgIlQxMDU5IiwgIlQxMDY4IiwgIlQxMTA1Il0sICJHMDEwOCI6IFsiVDEwMjciLCAiVDEwNDciLCAiVDEwODIiLCAiVDEwOTAiLCAiVDExMTIiLCAiVDExMzQiLCAiVDExOTAiLCAiVDE0OTYiXSwgIkcwMTEyIjogWyJUMTAyNyIsICJUMTAzMyIsICJUMTAzNiIsICJUMTA0NyIsICJUMTA1NyIsICJUMTA4MiIsICJUMTEwNSIsICJUMTE4OSIsICJUMTQwNiIsICJUMTQwNyIsICJUMTQyMCIsICJUMTQyNiIsICJUMTQyOSIsICJUMTQzMCIsICJUMTUxMiIsICJUMTUxOCIsICJUMTUzMyJdLCAiRzAxMTQiOiBbIlQxMDA3IiwgIlQxMDEyIiwgIlQxMDE2IiwgIlQxMDE4IiwgIlQxMDMzIiwgIlQxMDM5IiwgIlQxMDQxIiwgIlQxMDQ2IiwgIlQxMDQ3IiwgIlQxMDQ5IiwgIlQxMDU3IiwgIlQxMDc4IiwgIlQxMDgyIiwgIlQxMDgzIiwgIlQxMTA1IiwgIlQxMTA2IiwgIlQxMTExIiwgIlQxMTE5IiwgIlQxMTI0IiwgIlQxMTMzIiwgIlQxMTM1IiwgIlQxMjAxIiwgIlQxMjE3IiwgIlQxNDgyIiwgIlQxNTcwIiwgIlQxNTcyIl0sICJHMDExNSI6IFsiVDExMTMiLCAiVDExMzMiLCAiVDExOTAiLCAiVDExOTkiLCAiVDEyMTkiLCAiVDE1NjYiXSwgIkcwMTE3IjogWyJUMTAwNSIsICJUMTAxMiIsICJUMTAxOCIsICJUMTAyNyIsICJUMTAzOSIsICJUMTA0NiIsICJUMTA1OSIsICJUMTA3OCIsICJUMTA4MyIsICJUMTA5MCIsICJUMTEwMiIsICJUMTEwNSIsICJUMTExMCIsICJUMTE5MCIsICJUMTIxMCIsICJUMTIxMyIsICJUMTIxNyIsICJUMTUzMCIsICJUMTU3MiIsICJUMTU4NSJdLCAiRzAxMTkiOiBbIlQxMDA3IiwgIlQxMDE4IiwgIlQxMDQ3IiwgIlQxMTA1IiwgIlQxMTM2IiwgIlQxNDg2IiwgIlQxNDg5Il0sICJHMDEyMCI6IFsiVDExMDUiLCAiVDEyMTkiLCAiVDE1MzkiLCAiVDE1NTUiXSwgIkcwMTIxIjogWyJUMTAxNiIsICJUMTAyMCIsICJUMTAyNyIsICJUMTAzMyIsICJUMTA1NyIsICJUMTA4MiIsICJUMTA4MyIsICJUMTEwNSIsICJUMTExOSIsICJUMTEyNCIsICJUMTIwMyIsICJUMTUxOCJdLCAiRzAxMjIiOiBbIlQxMDc4IiwgIlQxMTE0IiwgIlQxNTk0Il0sICJHMDEyMyI6IFsiVDExMDUiLCAiVDExOTAiXSwgIkcwMTI0IjogWyJUMTAwNSIsICJUMTA1OSIsICJUMTA4MiIsICJUMTA4MyIsICJUMTA5MCIsICJUMTE4OSIsICJUMTUxOCJdLCAiRzAxMjUiOiBbIlQxMDA1IiwgIlQxMDE2IiwgIlQxMDE4IiwgIlQxMDMzIiwgIlQxMDU3IiwgIlQxMDgzIiwgIlQxMDk1IiwgIlQxMDk4IiwgIlQxMTA1IiwgIlQxMTkwIiwgIlQxNTkwIl0sICJHMDEyNiI6IFsiVDEwMTYiLCAiVDEwMjciLCAiVDEwMjkiLCAiVDEwNDEiLCAiVDEwNTciLCAiVDEwODIiLCAiVDExMDYiLCAiVDExMjQiLCAiVDExNDAiLCAiVDEyMDMiLCAiVDEyMjAiXSwgIkcwMTI3IjogWyJUMTAzNiIsICJUMTEwNSJdLCAiRzAxMjgiOiBbIlQxMDEyIiwgIlQxMDE2IiwgIlQxMDMzIiwgIlQxMDM2IiwgIlQxMDQxIiwgIlQxMDY4IiwgIlQxMDgyIiwgIlQxMTA1IiwgIlQxMTI0IiwgIlQxMTQwIiwgIlQxNTk4Il0sICJHMDEyOSI6IFsiVDEwMTYiLCAiVDEwMjciLCAiVDEwNDciLCAiVDEwNDkiLCAiVDEwNTciLCAiVDEwODIiLCAiVDEwODMiLCAiVDEwOTEiLCAiVDExMDIiLCAiVDExMDUiLCAiVDExMTkiLCAiVDEyMDMiLCAiVDEyMTkiLCAiVDE1MTgiLCAiVDE2MDgiXSwgIkcwMTMwIjogWyJUMTEwNSJdLCAiRzAxMzEiOiBbIlQxMDAzIiwgIlQxMDY4IiwgIlQxMTA1IiwgIlQxMTM1IiwgIlQxMjAzIiwgIlQxMjEwIl0sICJHMDEzMyI6IFsiVDEwMzYiLCAiVDExMDUiXSwgIkcwMTM0IjogWyJUMTAyNyIsICJUMTE4OSIsICJUMTIwMyIsICJUMTU2OCJdLCAiRzAxMzUiOiBbIlQxMDI3IiwgIlQxMDQ2IiwgIlQxMDQ5IiwgIlQxMDk1IiwgIlQxMTA1IiwgIlQxMTIwIiwgIlQxMTkwIl0sICJHMDEzNiI6IFsiVDExMDUiXSwgIkcwMTM3IjogW10sICJHMDEzOCI6IFsiVDEwMDUiLCAiVDEwNDkiLCAiVDEwNTciLCAiVDExMDUiLCAiVDExODkiLCAiVDEyMDMiXSwgIkcwMTM5IjogWyJUMTAwNyIsICJUMTAxNCIsICJUMTAxNiIsICJUMTAyNyIsICJUMTAzNiIsICJUMTA0NiIsICJUMTA0OCIsICJUMTA0OSIsICJUMTA1NyIsICJUMTA3MSIsICJUMTA4MiIsICJUMTA4MyIsICJUMTEwMiIsICJUMTEwNSIsICJUMTEyMCIsICJUMTEzMyIsICJUMTE0MCIsICJUMTIxOSIsICJUMTQ5NiIsICJUMTU2OSIsICJUMTYwOSIsICJUMTYxMCIsICJUMTYxMSIsICJUMTYxMyJdLCAiRzAxNDAiOiBbIlQxMDM2IiwgIlQxMTAyIiwgIlQxMTA1Il0sICJHMDE0MiI6IFsiVDEwNDEiLCAiVDEwODIiLCAiVDEwODMiLCAiVDExMDUiLCAiVDExMTkiLCAiVDEyMDMiLCAiVDEyMjEiXSwgIkcwMTQzIjogWyJUMTAwNyIsICJUMTA4MiIsICJUMTEwNSJdLCAiRzEwMDAiOiBbIlQwODE3IiwgIlQwODUyIiwgIlQwODU5IiwgIlQwODY1Il0sICJHMTAwMSI6IFsiVDEwMTAiLCAiVDEwMTYiLCAiVDEwMTgiLCAiVDEwMzMiLCAiVDEwNDkiLCAiVDEwNTciLCAiVDEwODIiLCAiVDExMDUiLCAiVDExMTAiLCAiVDE1MTgiLCAiVDE1MzQiLCAiVDE1NTUiLCAiVDE1ODkiXSwgIkcxMDAyIjogWyJUMTAyNyIsICJUMTA2OCIsICJUMTA5NSIsICJUMTEwNSIsICJUMTIwMyIsICJUMTU2OCIsICJUMTU3MyJdLCAiRzEwMDMiOiBbIlQxMDI3IiwgIlQxMTAyIiwgIlQxMTA1IiwgIlQxMTEyIiwgIlQxMjAzIl0sICJHMTAwNCI6IFsiVDEwMDUiLCAiVDEwNjgiLCAiVDEwNzgiLCAiVDEwOTAiLCAiVDExMTEiLCAiVDExMzMiLCAiVDExOTkiLCAiVDEyMDQiLCAiVDEyMTMiLCAiVDE0ODUiLCAiVDE0ODkiLCAiVDE1MzEiLCAiVDE1ODkiLCAiVDE2MjEiLCAiVDE2NTYiXSwgIkcxMDA1IjogWyJUMTA3OCIsICJUMTA5MCIsICJUMTE5OSJdLCAiRzEwMDYiOiBbIlQxMDA3IiwgIlQxMDE2IiwgIlQxMDE4IiwgIlQxMDI3IiwgIlQxMDMzIiwgIlQxMDQ3IiwgIlQxMDQ5IiwgIlQxMDUzIiwgIlQxMDU3IiwgIlQxMDkwIiwgIlQxMTEyIiwgIlQxMTQwIiwgIlQxMTg5IiwgIlQxMTkwIiwgIlQxMjEwIiwgIlQxNDgyIl0sICJHMTAwNyI6IFsiVDEwODMiLCAiVDEwOTEiLCAiVDEyMDMiLCAiVDE1NzAiXSwgIkcxMDA4IjogWyJUMTAxNiIsICJUMTA4MiIsICJUMTEwNSIsICJUMTEwNiIsICJUMTUxOCIsICJUMTYxNCJdLCAiRzEwMDkiOiBbIlQxMDE2IiwgIlQxMDI3IiwgIlQxMDgyIiwgIlQxMTA1IiwgIlQxMTkwIl0sICJHMTAxMSI6IFsiVDExMDIiLCAiVDEyMDMiLCAiVDE1OTQiLCAiVDE1OTciXSwgIkcxMDEyIjogWyJUMTAwNSJdLCAiRzEwMTMiOiBbIlQxMDI3IiwgIlQxMDk1IiwgIlQxMTA1Il0sICJHMTAxNCI6IFsiVDEwMDUiLCAiVDEwMzAiLCAiVDEwMzMiLCAiVDEwNDEiLCAiVDEwODMiLCAiVDEwOTEiLCAiVDExMDUiLCAiVDExMTIiLCAiVDE1MzkiLCAiVDE1NjAiXSwgIkcxMDE1IjogWyJUMTA2OCIsICJUMTEzMyIsICJUMTU5OCIsICJUMTYyMSJdLCAiRzEwMTYiOiBbIlQxMDA1IiwgIlQxMDE2IiwgIlQxMDM2IiwgIlQxMDQ2IiwgIlQxMDQ3IiwgIlQxMDQ5IiwgIlQxMDY5IiwgIlQxMDgyIiwgIlQxMDgzIiwgIlQxMDg3IiwgIlQxMDk4IiwgIlQxMTA1IiwgIlQxMTMzIiwgIlQxMTM1IiwgIlQxMTQwIiwgIlQxMTkwIiwgIlQxNTU2IiwgIlQxNTY1IiwgIlQxNTcyIiwgIlQxNTg5IiwgIlQxNjU3Il0sICJHMTAxNyI6IFsiVDEwMDUiLCAiVDEwMTIiLCAiVDEwMTYiLCAiVDEwMTgiLCAiVDEwMzMiLCAiVDEwNDciLCAiVDEwNDkiLCAiVDEwNTciLCAiVDEwNzQiLCAiVDEwODIiLCAiVDEwOTAiLCAiVDExOTAiLCAiVDE1MTgiLCAiVDE1NTUiLCAiVDE1NzAiLCAiVDE2NTQiXSwgIkcxMDE4IjogWyJUMTAyNyIsICJUMTA0NyIsICJUMTA1NSIsICJUMTA4MiIsICJUMTEwNSIsICJUMTU2OCJdLCAiRzEwMTkiOiBbIlQxMDY4IiwgIlQxMDkwIiwgIlQxMTEzIiwgIlQxNjU5Il19
eyJlbnRlcnByaXNlIjogeyJncm91cHMiOiBbImFkbWluQDMzOCAoRzAwMTgpIiwgIkFqYXggU2VjdXJpdHkgVGVhbSAoRzAxMzApIiwgIkFuZGFyaWVsIChHMDEzOCkiLCAiQW9xaW4gRHJhZ29uIChHMTAwNykiLCAiQVBULUMtMzYgKEcwMDk5KSIsICJBUFQxIChHMDAwNikiLCAiQVBUMTIgKEcwMDA1KSIsICJBUFQxNiAoRzAwMjMpIiwgIkFQVDE3IChHMDAyNSkiLCAiQVBUMTggKEcwMDI2KSIsICJBUFQxOSAoRzAwNzMpIiwgIkFQVDI4IChHMDAwNykiLCAiQVBUMjkgKEcwMDE2KSIsICJBUFQzIChHMDAyMikiLCAiQVBUMzAgKEcwMDEzKSIsICJBUFQzMiAoRzAwNTApIiwgIkFQVDMzIChHMDA2NCkiLCAiQVBUMzcgKEcwMDY3KSIsICJBUFQzOCAoRzAwODIpIiwgIkFQVDM5IChHMDA4NykiLCAiQVBUNDEgKEcwMDk2KSIsICJBcXVhdGljIFBhbmRhIChHMDE0MykiLCAiQXhpb20gKEcwMDAxKSIsICJCYWNrZG9vckRpcGxvbWFjeSAoRzAxMzUpIiwgIkJJVFRFUiAoRzEwMDIpIiwgIkJsYWNrT2FzaXMgKEcwMDYzKSIsICJCbGFja1RlY2ggKEcwMDk4KSIsICJCbHVlIE1vY2tpbmdiaXJkIChHMDEwOCkiLCAiQm91bmNpbmcgR29sZiAoRzAwOTcpIiwgIkJST05aRSBCVVRMRVIgKEcwMDYwKSIsICJDYXJiYW5hayAoRzAwMDgpIiwgIkNoaW1lcmEgKEcwMTE0KSIsICJDbGVhdmVyIChHMDAwMykiLCAiQ29iYWx0IEdyb3VwIChHMDA4MCkiLCAiQ29uZnVjaXVzIChHMDE0MikiLCAiQ29weUtpdHRlbnMgKEcwMDUyKSIsICJDVVJJVU0gKEcxMDEyKSIsICJEYXJrIENhcmFjYWwgKEcwMDcwKSIsICJEYXJraG90ZWwgKEcwMDEyKSIsICJEYXJrSHlkcnVzIChHMDA3OSkiLCAiRGFya1Zpc2hueWEgKEcwMTA1KSIsICJEZWVwIFBhbmRhIChHMDAwOSkiLCAiRHJhZ29uZmx5IChHMDAzNSkiLCAiRHJhZ29uT0sgKEcwMDE3KSIsICJFYXJ0aCBMdXNjYSAoRzEwMDYpIiwgIkVsZGVyd29vZCAoRzAwNjYpIiwgIkVtYmVyIEJlYXIgKEcxMDAzKSIsICJFcXVhdGlvbiAoRzAwMjApIiwgIkV2aWxudW0gKEcwMTIwKSIsICJFWE9USUMgTElMWSAoRzEwMTEpIiwgIkZlcm9jaW91cyBLaXR0ZW4gKEcwMTM3KSIsICJGSU4xMCAoRzAwNTEpIiwgIkZJTjEzIChHMTAxNikiLCAiRklONCAoRzAwODUpIiwgIkZJTjUgKEcwMDUzKSIsICJGSU42IChHMDAzNykiLCAiRklONyAoRzAwNDYpIiwgIkZJTjggKEcwMDYxKSIsICJGb3ggS2l0dGVuIChHMDExNykiLCAiR0FMTElVTSAoRzAwOTMpIiwgIkdhbGxtYWtlciAoRzAwODQpIiwgIkdhbWFyZWRvbiBHcm91cCAoRzAwNDcpIiwgIkdDTUFOIChHMDAzNikiLCAiR09MRCBTT1VUSEZJRUxEIChHMDExNSkiLCAiR29yZ29uIEdyb3VwIChHMDA3OCkiLCAiR3JvdXA1IChHMDA0MykiLCAiSEFGTklVTSAoRzAxMjUpIiwgIkhFWEFORSAoRzEwMDEpIiwgIkhpZ2Fpc2EgKEcwMTI2KSIsICJJbmNlcHRpb24gKEcwMTAwKSIsICJJbmRpZ29aZWJyYSAoRzAxMzYpIiwgIkluZHJpayBTcGlkZXIgKEcwMTE5KSIsICJLZTNjaGFuZyAoRzAwMDQpIiwgIktpbXN1a3kgKEcwMDk0KSIsICJMQVBTVVMkIChHMTAwNCkiLCAiTGF6YXJ1cyBHcm91cCAoRzAwMzIpIiwgIkxhenlTY3JpcHRlciAoRzAxNDApIiwgIkxlYWZtaW5lciAoRzAwNzcpIiwgIkxldmlhdGhhbiAoRzAwNjUpIiwgIkxvdHVzIEJsb3Nzb20gKEcwMDMwKSIsICJMdW1pbm91c01vdGggKEcxMDE0KSIsICJNYWNoZXRlIChHMDA5NSkiLCAiTWFnaWMgSG91bmQgKEcwMDU5KSIsICJtZW51UGFzcyAoRzAwNDUpIiwgIk1ldGFkb3IgKEcxMDEzKSIsICJNb2FmZWUgKEcwMDAyKSIsICJNb2ZhbmcgKEcwMTAzKSIsICJNb2xlcmF0cyAoRzAwMjEpIiwgIk1vc2VzIFN0YWZmIChHMTAwOSkiLCAiTW91c3RhY2hlZEJvdW5jZXIgKEcxMDE5KSIsICJNdWRkeVdhdGVyIChHMDA2OSkiLCAiTXVzdGFuZyBQYW5kYSAoRzAxMjkpIiwgIk5haWtvbiAoRzAwMTkpIiwgIk5FT0RZTUlVTSAoRzAwNTUpIiwgIk5vbWFkaWMgT2N0b3B1cyAoRzAxMzMpIiwgIk9pbFJpZyAoRzAwNDkpIiwgIk9yYW5nZXdvcm0gKEcwMDcxKSIsICJQYXRjaHdvcmsgKEcwMDQwKSIsICJQaXR0eVRpZ2VyIChHMDAxMSkiLCAiUExBVElOVU0gKEcwMDY4KSIsICJQT0xPTklVTSAoRzEwMDUpIiwgIlBvc2VpZG9uIEdyb3VwIChHMDAzMykiLCAiUFJPTUVUSElVTSAoRzAwNTYpIiwgIlB1dHRlciBQYW5kYSAoRzAwMjQpIiwgIlJhbmNvciAoRzAwNzUpIiwgIlJvY2tlIChHMDEwNikiLCAiUlRNIChHMDA0OCkiLCAiU2FuZHdvcm0gVGVhbSAoRzAwMzQpIiwgIlNjYXJsZXQgTWltaWMgKEcwMDI5KSIsICJTY2F0dGVyZWQgU3BpZGVyIChHMTAxNSkiLCAiU2lkZUNvcHkgKEcxMDA4KSIsICJTaWRld2luZGVyIChHMDEyMSkiLCAiU2lsZW5jZSAoRzAwOTEpIiwgIlNpbGVudCBMaWJyYXJpYW4gKEcwMTIyKSIsICJTaWx2ZXJUZXJyaWVyIChHMDA4MykiLCAiU293YnVnIChHMDA1NCkiLCAiU3RlYWx0aCBGYWxjb24gKEcwMDM4KSIsICJTdHJpZGVyIChHMDA0MSkiLCAiU3Vja2ZseSAoRzAwMzkpIiwgIlRBMjU0MSAoRzEwMTgpIiwgIlRBNDU5IChHMDA2MikiLCAiVEE1MDUgKEcwMDkyKSIsICJUQTU1MSAoRzAxMjcpIiwgIlRlYW1UTlQgKEcwMTM5KSIsICJURU1QLlZlbGVzIChHMDA4OCkiLCAiVGhlIFdoaXRlIENvbXBhbnkgKEcwMDg5KSIsICJUaHJlYXQgR3JvdXAtMTMxNCAoRzAwMjgpIiwgIlRocmVhdCBHcm91cC0zMzkwIChHMDAyNykiLCAiVGhyaXAgKEcwMDc2KSIsICJUb250byBUZWFtIChHMDEzMSkiLCAiVHJhbnNwYXJlbnQgVHJpYmUgKEcwMTM0KSIsICJUcm9waWMgVHJvb3BlciAoRzAwODEpIiwgIlR1cmxhIChHMDAxMCkiLCAiVm9sYXRpbGUgQ2VkYXIgKEcwMTIzKSIsICJWb2x0IFR5cGhvb24gKEcxMDE3KSIsICJXaGl0ZWZseSAoRzAxMDcpIiwgIldpbmRpZ28gKEcwMTI0KSIsICJXaW5kc2hpZnQgKEcwMTEyKSIsICJXaW5udGkgR3JvdXAgKEcwMDQ0KSIsICJXSVJURSAoRzAwOTApIiwgIldpemFyZCBTcGlkZXIgKEcwMTAyKSIsICJaSVJDT05JVU0gKEcwMTI4KSJdLCAidGFjdGljcyI6IFsiQ29sbGVjdGlvbiAoVEEwMDA5KSIsICJDb21tYW5kIGFuZCBDb250cm9sIChUQTAwMTEpIiwgIkNyZWRlbnRpYWwgQWNjZXNzIChUQTAwMDYpIiwgIkRlZmVuc2UgRXZhc2lvbiAoVEEwMDA1KSIsICJEaXNjb3ZlcnkgKFRBMDAwNykiLCAiRXhlY3V0aW9uIChUQTAwMDIpIiwgIkV4ZmlsdHJhdGlvbiAoVEEwMDEwKSIsICJJbXBhY3QgKFRBMDA0MCkiLCAiSW5pdGlhbCBBY2Nlc3MgKFRBMDAwMSkiLCAiTGF0ZXJhbCBNb3ZlbWVudCAoVEEwMDA4KSIsICJQZXJzaXN0ZW5jZSAoVEEwMDAzKSIsICJQcml2aWxlZ2UgRXNjYWxhdGlvbiAoVEEwMDA0KSIsICJSZWNvbm5haXNzYW5jZSAoVEEwMDQzKSIsICJSZXNvdXJjZSBEZXZlbG9wbWVudCAoVEEwMDQyKSJdLCAidGVjaG5pcXVlcyI6IFsiQWJ1c2UgRWxldmF0aW9uIENvbnRyb2wgTWVjaGFuaXNtIChUMTU0OCkiLCAiQWNjZXNzIFRva2VuIE1hbmlwdWxhdGlvbiAoVDExMzQpIiwgIkFjY291bnQgQWNjZXNzIFJlbW92YWwgKFQxNTMxKSIsICJBY2NvdW50IERpc2NvdmVyeSAoVDEwODcpIiwgIkFjY291bnQgTWFuaXB1bGF0aW9uIChUMTA5OCkiLCAiQWNxdWlyZSBBY2Nlc3MgKFQxNjUwKSIsICJBY3F1aXJlIEluZnJhc3RydWN0dXJlIChUMTU4MykiLCAiQWN0aXZlIFNjYW5uaW5nIChUMTU5NSkiLCAiQWR2ZXJzYXJ5LWluLXRoZS1NaWRkbGUgKFQxNTU3KSIsICJBcHBsaWNhdGlvbiBMYXllciBQcm90b2NvbCAoVDEwNzEpIiwgIkFwcGxpY2F0aW9uIFdpbmRvdyBEaXNjb3ZlcnkgKFQxMDEwKSIsICJBcmNoaXZlIENvbGxlY3RlZCBEYXRhIChUMTU2MCkiLCAiQXVkaW8gQ2FwdHVyZSAoVDExMjMpIiwgIkF1dG9tYXRlZCBDb2xsZWN0aW9uIChUMTExOSkiLCAiQXV0b21hdGVkIEV4ZmlsdHJhdGlvbiAoVDEwMjApIiwgIkJJVFMgSm9icyAoVDExOTcpIiwgIkJvb3Qgb3IgTG9nb24gQXV0b3N0YXJ0IEV4ZWN1dGlvbiAoVDE1NDcpIiwgIkJvb3Qgb3IgTG9nb24gSW5pdGlhbGl6YXRpb24gU2NyaXB0cyAoVDEwMzcpIiwgIkJyb3dzZXIgRXh0ZW5zaW9ucyAoVDExNzYpIiwgIkJyb3dzZXIgSW5mb3JtYXRpb24gRGlzY292ZXJ5IChUMTIxNykiLCAiQnJvd3NlciBTZXNzaW9uIEhpamFja2luZyAoVDExODUpIiwgIkJydXRlIEZvcmNlIChUMTExMCkiLCAiQnVpbGQgSW1hZ2Ugb24gSG9zdCAoVDE2MTIpIiwgIkNsaXBib2FyZCBEYXRhIChUMTExNSkiLCAiQ2xvdWQgQWRtaW5pc3RyYXRpb24gQ29tbWFuZCAoVDE2NTEpIiwgIkNsb3VkIEluZnJhc3RydWN0dXJlIERpc2NvdmVyeSAoVDE1ODApIiwgIkNsb3VkIFNlcnZpY2UgRGFzaGJvYXJkIChUMTUzOCkiLCAiQ2xvdWQgU2VydmljZSBEaXNjb3ZlcnkgKFQxNTI2KSIsICJDbG91ZCBTdG9yYWdlIE9iamVjdCBEaXNjb3ZlcnkgKFQxNjE5KSIsICJDb21tYW5kIGFuZCBTY3JpcHRpbmcgSW50ZXJwcmV0ZXIgKFQxMDU5KSIsICJDb21tdW5pY2F0aW9uIFRocm91Z2ggUmVtb3ZhYmxlIE1lZGlhIChUMTA5MikiLCAiQ29tcHJvbWlzZSBBY2NvdW50cyAoVDE1ODYpIiwgIkNvbXByb21pc2UgQ2xpZW50IFNvZnR3YXJlIEJpbmFyeSAoVDE1NTQpIiwgIkNvbXByb21pc2UgSW5mcmFzdHJ1Y3R1cmUgKFQxNTg0KSIsICJDb250YWluZXIgQWRtaW5pc3RyYXRpb24gQ29tbWFuZCAoVDE2MDkpIiwgIkNvbnRhaW5lciBhbmQgUmVzb3VyY2UgRGlzY292ZXJ5IChUMTYxMykiLCAiQ29udGVudCBJbmplY3Rpb24gKFQxNjU5KSIsICJDcmVhdGUgQWNjb3VudCAoVDExMzYpIiwgIkNyZWF0ZSBvciBNb2RpZnkgU3lzdGVtIFByb2Nlc3MgKFQxNTQzKSIsICJDcmVkZW50aWFscyBmcm9tIFBhc3N3b3JkIFN0b3JlcyAoVDE1NTUpIiwgIkRhdGEgRGVzdHJ1Y3Rpb24gKFQxNDg1KSIsICJEYXRhIEVuY29kaW5nIChUMTEzMikiLCAiRGF0YSBFbmNyeXB0ZWQgZm9yIEltcGFjdCAoVDE0ODYpIiwgIkRhdGEgZnJvbSBDbG91ZCBTdG9yYWdlIChUMTUzMCkiLCAiRGF0YSBmcm9tIENvbmZpZ3VyYXRpb24gUmVwb3NpdG9yeSAoVDE2MDIpIiwgIkRhdGEgZnJvbSBJbmZvcm1hdGlvbiBSZXBvc2l0b3JpZXMgKFQxMjEzKSIsICJEYXRhIGZyb20gTG9jYWwgU3lzdGVtIChUMTAwNSkiLCAiRGF0YSBmcm9tIE5ldHdvcmsgU2hhcmVkIERyaXZlIChUMTAzOSkiLCAiRGF0YSBmcm9tIFJlbW92YWJsZSBNZWRpYSAoVDEwMjUpIiwgIkRhdGEgTWFuaXB1bGF0aW9uIChUMTU2NSkiLCAiRGF0YSBPYmZ1c2NhdGlvbiAoVDEwMDEpIiwgIkRhdGEgU3RhZ2VkIChUMTA3NCkiLCAiRGF0YSBUcmFuc2ZlciBTaXplIExpbWl0cyAoVDEwMzApIiwgIkRlYnVnZ2VyIEV2YXNpb24gKFQxNjIyKSIsICJEZWZhY2VtZW50IChUMTQ5MSkiLCAiRGVvYmZ1c2NhdGUvRGVjb2RlIEZpbGVzIG9yIEluZm9ybWF0aW9uIChUMTE0MCkiLCAiRGVwbG95IENvbnRhaW5lciAoVDE2MTApIiwgIkRldmVsb3AgQ2FwYWJpbGl0aWVzIChUMTU4NykiLCAiRGV2aWNlIERyaXZlciBEaXNjb3ZlcnkgKFQxNjUyKSIsICJEaXJlY3QgVm9sdW1lIEFjY2VzcyAoVDEwMDYpIiwgIkRpc2sgV2lwZSAoVDE1NjEpIiwgIkRvbWFpbiBQb2xpY3kgTW9kaWZpY2F0aW9uIChUMTQ4NCkiLCAiRG9tYWluIFRydXN0IERpc2NvdmVyeSAoVDE0ODIpIiwgIkRyaXZlLWJ5IENvbXByb21pc2UgKFQxMTg5KSIsICJEeW5hbWljIFJlc29sdXRpb24gKFQxNTY4KSIsICJFbWFpbCBDb2xsZWN0aW9uIChUMTExNCkiLCAiRW5jcnlwdGVkIENoYW5uZWwgKFQxNTczKSIsICJFbmRwb2ludCBEZW5pYWwgb2YgU2VydmljZSAoVDE0OTkpIiwgIkVzY2FwZSB0byBIb3N0IChUMTYxMSkiLCAiRXN0YWJsaXNoIEFjY291bnRzIChUMTU4NSkiLCAiRXZlbnQgVHJpZ2dlcmVkIEV4ZWN1dGlvbiAoVDE1NDYpIiwgIkV4ZWN1dGlvbiBHdWFyZHJhaWxzIChUMTQ4MCkiLCAiRXhmaWx0cmF0aW9uIE92ZXIgQWx0ZXJuYXRpdmUgUHJvdG9jb2wgKFQxMDQ4KSIsICJFeGZpbHRyYXRpb24gT3ZlciBDMiBDaGFubmVsIChUMTA0MSkiLCAiRXhmaWx0cmF0aW9uIE92ZXIgT3RoZXIgTmV0d29yayBNZWRpdW0gKFQxMDExKSIsICJFeGZpbHRyYXRpb24gT3ZlciBQaHlzaWNhbCBNZWRpdW0gKFQxMDUyKSIsICJFeGZpbHRyYXRpb24gT3ZlciBXZWIgU2VydmljZSAoVDE1NjcpIiwgIkV4cGxvaXQgUHVibGljLUZhY2luZyBBcHBsaWNhdGlvbiAoVDExOTApIiwgIkV4cGxvaXRhdGlvbiBmb3IgQ2xpZW50IEV4ZWN1dGlvbiAoVDEyMDMpIiwgIkV4cGxvaXRhdGlvbiBmb3IgQ3JlZGVudGlhbCBBY2Nlc3MgKFQxMjEyKSIsICJFeHBsb2l0YXRpb24gZm9yIERlZmVuc2UgRXZhc2lvbiAoVDEyMTEpIiwgIkV4cGxvaXRhdGlvbiBmb3IgUHJpdmlsZWdlIEVzY2FsYXRpb24gKFQxMDY4KSIsICJFeHBsb2l0YXRpb24gb2YgUmVtb3RlIFNlcnZpY2VzIChUMTIxMCkiLCAiRXh0ZXJuYWwgUmVtb3RlIFNlcnZpY2VzIChUMTEzMykiLCAiRmFsbGJhY2sgQ2hhbm5lbHMgKFQxMDA4KSIsICJGaWxlIGFuZCBEaXJlY3RvcnkgRGlzY292ZXJ5IChUMTA4MykiLCAiRmlsZSBhbmQgRGlyZWN0b3J5IFBlcm1pc3Npb25zIE1vZGlmaWNhdGlvbiAoVDEyMjIpIiwgIkZpbmFuY2lhbCBUaGVmdCAoVDE2NTcpIiwgIkZpcm13YXJlIENvcnJ1cHRpb24gKFQxNDk1KSIsICJGb3JjZWQgQXV0aGVudGljYXRpb24gKFQxMTg3KSIsICJGb3JnZSBXZWIgQ3JlZGVudGlhbHMgKFQxNjA2KSIsICJHYXRoZXIgVmljdGltIEhvc3QgSW5mb3JtYXRpb24gKFQxNTkyKSIsICJHYXRoZXIgVmljdGltIElkZW50aXR5IEluZm9ybWF0aW9uIChUMTU4OSkiLCAiR2F0aGVyIFZpY3RpbSBOZXR3b3JrIEluZm9ybWF0aW9uIChUMTU5MCkiLCAiR2F0aGVyIFZpY3RpbSBPcmcgSW5mb3JtYXRpb24gKFQxNTkxKSIsICJHcm91cCBQb2xpY3kgRGlzY292ZXJ5IChUMTYxNSkiLCAiSGFyZHdhcmUgQWRkaXRpb25zIChUMTIwMCkiLCAiSGlkZSBBcnRpZmFjdHMgKFQxNTY0KSIsICJIaWphY2sgRXhlY3V0aW9uIEZsb3cgKFQxNTc0KSIsICJJbXBhaXIgRGVmZW5zZXMgKFQxNTYyKSIsICJJbXBlcnNvbmF0aW9uIChUMTY1NikiLCAiSW1wbGFudCBJbnRlcm5hbCBJbWFnZSAoVDE1MjUpIiwgIkluZGljYXRvciBSZW1vdmFsIChUMTA3MCkiLCAiSW5kaXJlY3QgQ29tbWFuZCBFeGVjdXRpb24gKFQxMjAyKSIsICJJbmdyZXNzIFRvb2wgVHJhbnNmZXIgKFQxMTA1KSIsICJJbmhpYml0IFN5c3RlbSBSZWNvdmVyeSAoVDE0OTApIiwgIklucHV0IENhcHR1cmUgKFQxMDU2KSIsICJJbnRlci1Qcm9jZXNzIENvbW11bmljYXRpb24gKFQxNTU5KSIsICJJbnRlcm5hbCBTcGVhcnBoaXNoaW5nIChUMTUzNCkiLCAiTGF0ZXJhbCBUb29sIFRyYW5zZmVyIChUMTU3MCkiLCAiTG9nIEVudW1lcmF0aW9uIChUMTY1NCkiLCAiTWFzcXVlcmFkaW5nIChUMTAzNikiLCAiTW9kaWZ5IEF1dGhlbnRpY2F0aW9uIFByb2Nlc3MgKFQxNTU2KSIsICJNb2RpZnkgQ2xvdWQgQ29tcHV0ZSBJbmZyYXN0cnVjdHVyZSAoVDE1NzgpIiwgIk1vZGlmeSBSZWdpc3RyeSAoVDExMTIpIiwgIk1vZGlmeSBTeXN0ZW0gSW1hZ2UgKFQxNjAxKSIsICJNdWx0aS1GYWN0b3IgQXV0aGVudGljYXRpb24gSW50ZXJjZXB0aW9uIChUMTExMSkiLCAiTXVsdGktRmFjdG9yIEF1dGhlbnRpY2F0aW9uIFJlcXVlc3QgR2VuZXJhdGlvbiAoVDE2MjEpIiwgIk11bHRpLVN0YWdlIENoYW5uZWxzIChUMTEwNCkiLCAiTmF0aXZlIEFQSSAoVDExMDYpIiwgIk5ldHdvcmsgQm91bmRhcnkgQnJpZGdpbmcgKFQxNTk5KSIsICJOZXR3b3JrIERlbmlhbCBvZiBTZXJ2aWNlIChUMTQ5OCkiLCAiTmV0d29yayBTZXJ2aWNlIERpc2NvdmVyeSAoVDEwNDYpIiwgIk5ldHdvcmsgU2hhcmUgRGlzY292ZXJ5IChUMTEzNSkiLCAiTmV0d29yayBTbmlmZmluZyAoVDEwNDApIiwgIk5vbi1BcHBsaWNhdGlvbiBMYXllciBQcm90b2NvbCAoVDEwOTUpIiwgIk5vbi1TdGFuZGFyZCBQb3J0IChUMTU3MSkiLCAiT2JmdXNjYXRlZCBGaWxlcyBvciBJbmZvcm1hdGlvbiAoVDEwMjcpIiwgIk9idGFpbiBDYXBhYmlsaXRpZXMgKFQxNTg4KSIsICJPZmZpY2UgQXBwbGljYXRpb24gU3RhcnR1cCAoVDExMzcpIiwgIk9TIENyZWRlbnRpYWwgRHVtcGluZyAoVDEwMDMpIiwgIlBhc3N3b3JkIFBvbGljeSBEaXNjb3ZlcnkgKFQxMjAxKSIsICJQZXJpcGhlcmFsIERldmljZSBEaXNjb3ZlcnkgKFQxMTIwKSIsICJQZXJtaXNzaW9uIEdyb3VwcyBEaXNjb3ZlcnkgKFQxMDY5KSIsICJQaGlzaGluZyAoVDE1NjYpIiwgIlBoaXNoaW5nIGZvciBJbmZvcm1hdGlvbiAoVDE1OTgpIiwgIlBsaXN0IEZpbGUgTW9kaWZpY2F0aW9uIChUMTY0NykiLCAiUG93ZXIgU2V0dGluZ3MgKFQxNjUzKSIsICJQcmUtT1MgQm9vdCAoVDE1NDIpIiwgIlByb2Nlc3MgRGlzY292ZXJ5IChUMTA1NykiLCAiUHJvY2VzcyBJbmplY3Rpb24gKFQxMDU1KSIsICJQcm90b2NvbCBUdW5uZWxpbmcgKFQxNTcyKSIsICJQcm94eSAoVDEwOTApIiwgIlF1ZXJ5IFJlZ2lzdHJ5IChUMTAxMikiLCAiUmVmbGVjdGl2ZSBDb2RlIExvYWRpbmcgKFQxNjIwKSIsICJSZW1vdGUgQWNjZXNzIFNvZnR3YXJlIChUMTIxOSkiLCAiUmVtb3RlIFNlcnZpY2UgU2Vzc2lvbiBIaWphY2tpbmcgKFQxNTYzKSIsICJSZW1vdGUgU2VydmljZXMgKFQxMDIxKSIsICJSZW1vdGUgU3lzdGVtIERpc2NvdmVyeSAoVDEwMTgpIiwgIlJlcGxpY2F0aW9uIFRocm91Z2ggUmVtb3ZhYmxlIE1lZGlhIChUMTA5MSkiLCAiUmVzb3VyY2UgSGlqYWNraW5nIChUMTQ5NikiLCAiUm9ndWUgRG9tYWluIENvbnRyb2xsZXIgKFQxMjA3KSIsICJSb290a2l0IChUMTAxNCkiLCAiU2NoZWR1bGVkIFRhc2svSm9iIChUMTA1MykiLCAiU2NoZWR1bGVkIFRyYW5zZmVyIChUMTAyOSkiLCAiU2NyZWVuIENhcHR1cmUgKFQxMTEzKSIsICJTZWFyY2ggQ2xvc2VkIFNvdXJjZXMgKFQxNTk3KSIsICJTZWFyY2ggT3BlbiBUZWNobmljYWwgRGF0YWJhc2VzIChUMTU5NikiLCAiU2VhcmNoIE9wZW4gV2Vic2l0ZXMvRG9tYWlucyAoVDE1OTMpIiwgIlNlYXJjaCBWaWN0aW0tT3duZWQgV2Vic2l0ZXMgKFQxNTk0KSIsICJTZXJ2ZXIgU29mdHdhcmUgQ29tcG9uZW50IChUMTUwNSkiLCAiU2VydmVybGVzcyBFeGVjdXRpb24gKFQxNjQ4KSIsICJTZXJ2aWNlIFN0b3AgKFQxNDg5KSIsICJTaGFyZWQgTW9kdWxlcyAoVDExMjkpIiwgIlNvZnR3YXJlIERlcGxveW1lbnQgVG9vbHMgKFQxMDcyKSIsICJTb2Z0d2FyZSBEaXNjb3ZlcnkgKFQxNTE4KSIsICJTdGFnZSBDYXBhYmlsaXRpZXMgKFQxNjA4KSIsICJTdGVhbCBBcHBsaWNhdGlvbiBBY2Nlc3MgVG9rZW4gKFQxNTI4KSIsICJTdGVhbCBvciBGb3JnZSBBdXRoZW50aWNhdGlvbiBDZXJ0aWZpY2F0ZXMgKFQxNjQ5KSIsICJTdGVhbCBvciBGb3JnZSBLZXJiZXJvcyBUaWNrZXRzIChUMTU1OCkiLCAiU3RlYWwgV2ViIFNlc3Npb24gQ29va2llIChUMTUzOSkiLCAiU3VidmVydCBUcnVzdCBDb250cm9scyAoVDE1NTMpIiwgIlN1cHBseSBDaGFpbiBDb21wcm9taXNlIChUMTE5NSkiLCAiU3lzdGVtIEJpbmFyeSBQcm94eSBFeGVjdXRpb24gKFQxMjE4KSIsICJTeXN0ZW0gSW5mb3JtYXRpb24gRGlzY292ZXJ5IChUMTA4MikiLCAiU3lzdGVtIExvY2F0aW9uIERpc2NvdmVyeSAoVDE2MTQpIiwgIlN5c3RlbSBOZXR3b3JrIENvbmZpZ3VyYXRpb24gRGlzY292ZXJ5IChUMTAxNikiLCAiU3lzdGVtIE5ldHdvcmsgQ29ubmVjdGlvbnMgRGlzY292ZXJ5IChUMTA0OSkiLCAiU3lzdGVtIE93bmVyL1VzZXIgRGlzY292ZXJ5IChUMTAzMykiLCAiU3lzdGVtIFNjcmlwdCBQcm94eSBFeGVjdXRpb24gKFQxMjE2KSIsICJTeXN0ZW0gU2VydmljZSBEaXNjb3ZlcnkgKFQxMDA3KSIsICJTeXN0ZW0gU2VydmljZXMgKFQxNTY5KSIsICJTeXN0ZW0gU2h1dGRvd24vUmVib290IChUMTUyOSkiLCAiU3lzdGVtIFRpbWUgRGlzY292ZXJ5IChUMTEyNCkiLCAiVGFpbnQgU2hhcmVkIENvbnRlbnQgKFQxMDgwKSIsICJUZW1wbGF0ZSBJbmplY3Rpb24gKFQxMjIxKSIsICJUcmFmZmljIFNpZ25hbGluZyAoVDEyMDUpIiwgIlRyYW5zZmVyIERhdGEgdG8gQ2xvdWQgQWNjb3VudCAoVDE1MzcpIiwgIlRydXN0ZWQgRGV2ZWxvcGVyIFV0aWxpdGllcyBQcm94eSBFeGVjdXRpb24gKFQxMTI3KSIsICJUcnVzdGVkIFJlbGF0aW9uc2hpcCAoVDExOTkpIiwgIlVuc2VjdXJlZCBDcmVkZW50aWFscyAoVDE1NTIpIiwgIlVudXNlZC9VbnN1cHBvcnRlZCBDbG91ZCBSZWdpb25zIChUMTUzNSkiLCAiVXNlIEFsdGVybmF0ZSBBdXRoZW50aWNhdGlvbiBNYXRlcmlhbCAoVDE1NTApIiwgIlVzZXIgRXhlY3V0aW9uIChUMTIwNCkiLCAiVmFsaWQgQWNjb3VudHMgKFQxMDc4KSIsICJWaWRlbyBDYXB0dXJlIChUMTEyNSkiLCAiVmlydHVhbGl6YXRpb24vU2FuZGJveCBFdmFzaW9uIChUMTQ5NykiLCAiV2Vha2VuIEVuY3J5cHRpb24gKFQxNjAwKSIsICJXZWIgU2VydmljZSAoVDExMDIpIiwgIldpbmRvd3MgTWFuYWdlbWVudCBJbnN0cnVtZW50YXRpb24gKFQxMDQ3KSIsICJYU0wgU2NyaXB0IFByb2Nlc3NpbmcgKFQxMjIwKSJdfSwgIm1vYmlsZSI6IHsiZ3JvdXBzIjogWyJBUFQyOCAoRzAwMDcpIiwgIkJvdW5jaW5nIEdvbGYgKEcwMDk3KSIsICJDb25mdWNpdXMgKEcwMTQyKSIsICJEYXJrIENhcmFjYWwgKEcwMDcwKSIsICJFYXJ0aCBMdXNjYSAoRzEwMDYpIiwgIk1vdXN0YWNoZWRCb3VuY2VyIChHMTAxOSkiLCAiU2FuZHdvcm0gVGVhbSAoRzAwMzQpIiwgIldpbmRzaGlmdCAoRzAxMTIpIl0sICJ0YWN0aWNzIjogWyJDb2xsZWN0aW9uIChUQTAwMzUpIiwgIkNvbW1hbmQgYW5kIENvbnRyb2wgKFRBMDAzNykiLCAiQ3JlZGVudGlhbCBBY2Nlc3MgKFRBMDAzMSkiLCAiRGVmZW5zZSBFdmFzaW9uIChUQTAwMzApIiwgIkRpc2NvdmVyeSAoVEEwMDMyKSIsICJFeGVjdXRpb24gKFRBMDA0MSkiLCAiRXhmaWx0cmF0aW9uIChUQTAwMzYpIiwgIkltcGFjdCAoVEEwMDM0KSIsICJJbml0aWFsIEFjY2VzcyAoVEEwMDI3KSIsICJMYXRlcmFsIE1vdmVtZW50IChUQTAwMzMpIiwgIlBlcnNpc3RlbmNlIChUQTAwMjgpIiwgIlByaXZpbGVnZSBFc2NhbGF0aW9uIChUQTAwMjkpIl0sICJ0ZWNobmlxdWVzIjogWyJBYnVzZSBFbGV2YXRpb24gQ29udHJvbCBNZWNoYW5pc20gKFQxNjI2KSIsICJBY2Nlc3MgTm90aWZpY2F0aW9ucyAoVDE1MTcpIiwgIkFjY291bnQgQWNjZXNzIFJlbW92YWwgKFQxNjQwKSIsICJBZHZlcnNhcnktaW4tdGhlLU1pZGRsZSAoVDE2MzgpIiwgIkFwcGxpY2F0aW9uIExheWVyIFByb3RvY29sIChUMTQzNykiLCAiQXBwbGljYXRpb24gVmVyc2lvbmluZyAoVDE2NjEpIiwgIkFyY2hpdmUgQ29sbGVjdGVkIERhdGEgKFQxNTMyKSIsICJBdWRpbyBDYXB0dXJlIChUMTQyOSkiLCAiQm9vdCBvciBMb2dvbiBJbml0aWFsaXphdGlvbiBTY3JpcHRzIChUMTM5OCkiLCAiQ2FsbCBDb250cm9sIChUMTYxNikiLCAiQ2xpcGJvYXJkIERhdGEgKFQxNDE0KSIsICJDb21tYW5kIGFuZCBTY3JpcHRpbmcgSW50ZXJwcmV0ZXIgKFQxNjIzKSIsICJDb21wcm9taXNlIEFwcGxpY2F0aW9uIEV4ZWN1dGFibGUgKFQxNTc3KSIsICJDb21wcm9taXNlIENsaWVudCBTb2Z0d2FyZSBCaW5hcnkgKFQxNjQ1KSIsICJDcmVkZW50aWFscyBmcm9tIFBhc3N3b3JkIFN0b3JlIChUMTYzNCkiLCAiRGF0YSBEZXN0cnVjdGlvbiAoVDE2NjIpIiwgIkRhdGEgRW5jcnlwdGVkIGZvciBJbXBhY3QgKFQxNDcxKSIsICJEYXRhIGZyb20gTG9jYWwgU3lzdGVtIChUMTUzMykiLCAiRGF0YSBNYW5pcHVsYXRpb24gKFQxNjQxKSIsICJEb3dubG9hZCBOZXcgQ29kZSBhdCBSdW50aW1lIChUMTQwNykiLCAiRHJpdmUtQnkgQ29tcHJvbWlzZSAoVDE0NTYpIiwgIkR5bmFtaWMgUmVzb2x1dGlvbiAoVDE2MzcpIiwgIkVuY3J5cHRlZCBDaGFubmVsIChUMTUyMSkiLCAiRW5kcG9pbnQgRGVuaWFsIG9mIFNlcnZpY2UgKFQxNjQyKSIsICJFdmVudCBUcmlnZ2VyZWQgRXhlY3V0aW9uIChUMTYyNCkiLCAiRXhlY3V0aW9uIEd1YXJkcmFpbHMgKFQxNjI3KSIsICJFeGZpbHRyYXRpb24gT3ZlciBBbHRlcm5hdGl2ZSBQcm90b2NvbCAoVDE2MzkpIiwgIkV4ZmlsdHJhdGlvbiBPdmVyIEMyIENoYW5uZWwgKFQxNjQ2KSIsICJFeHBsb2l0YXRpb24gZm9yIENsaWVudCBFeGVjdXRpb24gKFQxNjU4KSIsICJFeHBsb2l0YXRpb24gZm9yIFByaXZpbGVnZSBFc2NhbGF0aW9uIChUMTQwNCkiLCAiRXhwbG9pdGF0aW9uIG9mIFJlbW90ZSBTZXJ2aWNlcyAoVDE0MjgpIiwgIkZpbGUgYW5kIERpcmVjdG9yeSBEaXNjb3ZlcnkgKFQxNDIwKSIsICJGb3JlZ3JvdW5kIFBlcnNpc3RlbmNlIChUMTU0MSkiLCAiR2VuZXJhdGUgVHJhZmZpYyBmcm9tIFZpY3RpbSAoVDE2NDMpIiwgIkhpZGUgQXJ0aWZhY3RzIChUMTYyOCkiLCAiSGlqYWNrIEV4ZWN1dGlvbiBGbG93IChUMTYyNSkiLCAiSG9va2luZyAoVDE2MTcpIiwgIkltcGFpciBEZWZlbnNlcyAoVDE2MjkpIiwgIkluZGljYXRvciBSZW1vdmFsIG9uIEhvc3QgKFQxNjMwKSIsICJJbmdyZXNzIFRvb2wgVHJhbnNmZXIgKFQxNTQ0KSIsICJJbnB1dCBDYXB0dXJlIChUMTQxNykiLCAiSW5wdXQgSW5qZWN0aW9uIChUMTUxNikiLCAiTG9jYXRpb24gVHJhY2tpbmcgKFQxNDMwKSIsICJMb2Nrc2NyZWVuIEJ5cGFzcyAoVDE0NjEpIiwgIk1hc3F1ZXJhZGluZyAoVDE2NTUpIiwgIk5hdGl2ZSBBUEkgKFQxNTc1KSIsICJOZXR3b3JrIERlbmlhbCBvZiBTZXJ2aWNlIChUMTQ2NCkiLCAiTmV0d29yayBTZXJ2aWNlIFNjYW5uaW5nIChUMTQyMykiLCAiTm9uLVN0YW5kYXJkIFBvcnQgKFQxNTA5KSIsICJPYmZ1c2NhdGVkIEZpbGVzIG9yIEluZm9ybWF0aW9uIChUMTQwNikiLCAiT3V0IG9mIEJhbmQgRGF0YSAoVDE2NDQpIiwgIlBoaXNoaW5nIChUMTY2MCkiLCAiUHJvY2VzcyBEaXNjb3ZlcnkgKFQxNDI0KSIsICJQcm9jZXNzIEluamVjdGlvbiAoVDE2MzEpIiwgIlByb3RlY3RlZCBVc2VyIERhdGEgKFQxNjM2KSIsICJQcm94eSBUaHJvdWdoIFZpY3RpbSAoVDE2MDQpIiwgIlJlbW90ZSBBY2Nlc3MgU29mdHdhcmUgKFQxNjYzKSIsICJSZXBsaWNhdGlvbiBUaHJvdWdoIFJlbW92YWJsZSBNZWRpYSAoVDE0NTgpIiwgIlNjaGVkdWxlZCBUYXNrL0pvYiAoVDE2MDMpIiwgIlNjcmVlbiBDYXB0dXJlIChUMTUxMykiLCAiU01TIENvbnRyb2wgKFQxNTgyKSIsICJTb2Z0d2FyZSBEaXNjb3ZlcnkgKFQxNDE4KSIsICJTdGVhbCBBcHBsaWNhdGlvbiBBY2Nlc3MgVG9rZW4gKFQxNjM1KSIsICJTdG9yZWQgQXBwbGljYXRpb24gRGF0YSAoVDE0MDkpIiwgIlN1YnZlcnQgVHJ1c3QgQ29udHJvbHMgKFQxNjMyKSIsICJTdXBwbHkgQ2hhaW4gQ29tcHJvbWlzZSAoVDE0NzQpIiwgIlN5c3RlbSBJbmZvcm1hdGlvbiBEaXNjb3ZlcnkgKFQxNDI2KSIsICJTeXN0ZW0gTmV0d29yayBDb25maWd1cmF0aW9uIERpc2NvdmVyeSAoVDE0MjIpIiwgIlN5c3RlbSBOZXR3b3JrIENvbm5lY3Rpb25zIERpc2NvdmVyeSAoVDE0MjEpIiwgIlZpZGVvIENhcHR1cmUgKFQxNTEyKSIsICJWaXJ0dWFsaXphdGlvbi9TYW5kYm94IEV2YXNpb24gKFQxNjMzKSIsICJXZWIgU2VydmljZSAoVDE0ODEpIl19LCAiaWNzIjogeyJncm91cHMiOiBbIkFMTEFOSVRFIChHMTAwMCkiLCAiQVBUMzMgKEcwMDY0KSIsICJBUFQzOCAoRzAwODIpIiwgIkRyYWdvbmZseSAoRzAwMzUpIiwgIkZJTjYgKEcwMDM3KSIsICJGSU43IChHMDA0NikiLCAiR09MRCBTT1VUSEZJRUxEIChHMDExNSkiLCAiSEVYQU5FIChHMTAwMSkiLCAiTGF6YXJ1cyBHcm91cCAoRzAwMzIpIiwgIkxlYWZtaW5lciAoRzAwNzcpIiwgIk9pbFJpZyAoRzAwNDkpIiwgIlNhbmR3b3JtIFRlYW0gKEcwMDM0KSIsICJURU1QLlZlbGVzIChHMDA4OCkiLCAiV2l6YXJkIFNwaWRlciAoRzAxMDIpIl0sICJ0YWN0aWNzIjogWyJDb2xsZWN0aW9uIChUQTAxMDApIiwgIkNvbW1hbmQgYW5kIENvbnRyb2wgKFRBMDEwMSkiLCAiRGlzY292ZXJ5IChUQTAxMDIpIiwgIkV2YXNpb24gKFRBMDEwMykiLCAiRXhlY3V0aW9uIChUQTAxMDQpIiwgIkltcGFjdCAoVEEwMTA1KSIsICJJbXBhaXIgUHJvY2VzcyBDb250cm9sIChUQTAxMDYpIiwgIkluaGliaXQgUmVzcG9uc2UgRnVuY3Rpb24gKFRBMDEwNykiLCAiSW5pdGlhbCBBY2Nlc3MgKFRBMDEwOCkiLCAiTGF0ZXJhbCBNb3ZlbWVudCAoVEEwMTA5KSIsICJQZXJzaXN0ZW5jZSAoVEEwMTEwKSIsICJQcml2aWxlZ2UgRXNjYWxhdGlvbiAoVEEwMTExKSJdLCAidGVjaG5pcXVlcyI6IFsiQWN0aXZhdGUgRmlybXdhcmUgVXBkYXRlIE1vZGUgKFQwODAwKSIsICJBZHZlcnNhcnktaW4tdGhlLU1pZGRsZSAoVDA4MzApIiwgIkFsYXJtIFN1cHByZXNzaW9uIChUMDg3OCkiLCAiQXV0b21hdGVkIENvbGxlY3Rpb24gKFQwODAyKSIsICJCbG9jayBDb21tYW5kIE1lc3NhZ2UgKFQwODAzKSIsICJCbG9jayBSZXBvcnRpbmcgTWVzc2FnZSAoVDA4MDQpIiwgIkJsb2NrIFNlcmlhbCBDT00gKFQwODA1KSIsICJCcnV0ZSBGb3JjZSBJL08gKFQwODA2KSIsICJDaGFuZ2UgQ3JlZGVudGlhbCAoVDA4OTIpIiwgIkNoYW5nZSBPcGVyYXRpbmcgTW9kZSAoVDA4NTgpIiwgIkNvbW1hbmQtTGluZSBJbnRlcmZhY2UgKFQwODA3KSIsICJDb21tb25seSBVc2VkIFBvcnQgKFQwODg1KSIsICJDb25uZWN0aW9uIFByb3h5IChUMDg4NCkiLCAiRGFtYWdlIHRvIFByb3BlcnR5IChUMDg3OSkiLCAiRGF0YSBEZXN0cnVjdGlvbiAoVDA4MDkpIiwgIkRhdGEgZnJvbSBJbmZvcm1hdGlvbiBSZXBvc2l0b3JpZXMgKFQwODExKSIsICJEYXRhIGZyb20gTG9jYWwgU3lzdGVtIChUMDg5MykiLCAiRGVmYXVsdCBDcmVkZW50aWFscyAoVDA4MTIpIiwgIkRlbmlhbCBvZiBDb250cm9sIChUMDgxMykiLCAiRGVuaWFsIG9mIFNlcnZpY2UgKFQwODE0KSIsICJEZW5pYWwgb2YgVmlldyAoVDA4MTUpIiwgIkRldGVjdCBPcGVyYXRpbmcgTW9kZSAoVDA4NjgpIiwgIkRldmljZSBSZXN0YXJ0L1NodXRkb3duIChUMDgxNikiLCAiRHJpdmUtYnkgQ29tcHJvbWlzZSAoVDA4MTcpIiwgIkV4ZWN1dGlvbiB0aHJvdWdoIEFQSSAoVDA4NzEpIiwgIkV4cGxvaXQgUHVibGljLUZhY2luZyBBcHBsaWNhdGlvbiAoVDA4MTkpIiwgIkV4cGxvaXRhdGlvbiBmb3IgRXZhc2lvbiAoVDA4MjApIiwgIkV4cGxvaXRhdGlvbiBmb3IgUHJpdmlsZWdlIEVzY2FsYXRpb24gKFQwODkwKSIsICJFeHBsb2l0YXRpb24gb2YgUmVtb3RlIFNlcnZpY2VzIChUMDg2NikiLCAiRXh0ZXJuYWwgUmVtb3RlIFNlcnZpY2VzIChUMDgyMikiLCAiR3JhcGhpY2FsIFVzZXIgSW50ZXJmYWNlIChUMDgyMykiLCAiSGFyZGNvZGVkIENyZWRlbnRpYWxzIChUMDg5MSkiLCAiSG9va2luZyAoVDA4NzQpIiwgIkkvTyBJbWFnZSAoVDA4NzcpIiwgIkluZGljYXRvciBSZW1vdmFsIG9uIEhvc3QgKFQwODcyKSIsICJJbnRlcm5ldCBBY2Nlc3NpYmxlIERldmljZSAoVDA4ODMpIiwgIkxhdGVyYWwgVG9vbCBUcmFuc2ZlciAoVDA4NjcpIiwgIkxvc3Mgb2YgQXZhaWxhYmlsaXR5IChUMDgyNikiLCAiTG9zcyBvZiBDb250cm9sIChUMDgyNykiLCAiTG9zcyBvZiBQcm9kdWN0aXZpdHkgYW5kIFJldmVudWUgKFQwODI4KSIsICJMb3NzIG9mIFByb3RlY3Rpb24gKFQwODM3KSIsICJMb3NzIG9mIFNhZmV0eSAoVDA4ODApIiwgIkxvc3Mgb2YgVmlldyAoVDA4MjkpIiwgIk1hbmlwdWxhdGUgSS9PIEltYWdlIChUMDgzNSkiLCAiTWFuaXB1bGF0aW9uIG9mIENvbnRyb2wgKFQwODMxKSIsICJNYW5pcHVsYXRpb24gb2YgVmlldyAoVDA4MzIpIiwgIk1hc3F1ZXJhZGluZyAoVDA4NDkpIiwgIk1vZGlmeSBBbGFybSBTZXR0aW5ncyAoVDA4MzgpIiwgIk1vZGlmeSBDb250cm9sbGVyIFRhc2tpbmcgKFQwODIxKSIsICJNb2RpZnkgUGFyYW1ldGVyIChUMDgzNikiLCAiTW9kaWZ5IFByb2dyYW0gKFQwODg5KSIsICJNb2R1bGUgRmlybXdhcmUgKFQwODM5KSIsICJNb25pdG9yIFByb2Nlc3MgU3RhdGUgKFQwODAxKSIsICJOYXRpdmUgQVBJIChUMDgzNCkiLCAiTmV0d29yayBDb25uZWN0aW9uIEVudW1lcmF0aW9uIChUMDg0MCkiLCAiTmV0d29yayBTbmlmZmluZyAoVDA4NDIpIiwgIlBvaW50ICYgVGFnIElkZW50aWZpY2F0aW9uIChUMDg2MSkiLCAiUHJvZ3JhbSBEb3dubG9hZCAoVDA4NDMpIiwgIlByb2dyYW0gVXBsb2FkIChUMDg0NSkiLCAiUHJvamVjdCBGaWxlIEluZmVjdGlvbiAoVDA4NzMpIiwgIlJlbW90ZSBTZXJ2aWNlcyAoVDA4ODYpIiwgIlJlbW90ZSBTeXN0ZW0gRGlzY292ZXJ5IChUMDg0NikiLCAiUmVtb3RlIFN5c3RlbSBJbmZvcm1hdGlvbiBEaXNjb3ZlcnkgKFQwODg4KSIsICJSZXBsaWNhdGlvbiBUaHJvdWdoIFJlbW92YWJsZSBNZWRpYSAoVDA4NDcpIiwgIlJvZ3VlIE1hc3RlciAoVDA4NDgpIiwgIlJvb3RraXQgKFQwODUxKSIsICJTY3JlZW4gQ2FwdHVyZSAoVDA4NTIpIiwgIlNjcmlwdGluZyAoVDA4NTMpIiwgIlNlcnZpY2UgU3RvcCAoVDA4ODEpIiwgIlNwZWFycGhpc2hpbmcgQXR0YWNobWVudCAoVDA4NjUpIiwgIlNwb29mIFJlcG9ydGluZyBNZXNzYWdlIChUMDg1NikiLCAiU3RhbmRhcmQgQXBwbGljYXRpb24gTGF5ZXIgUHJvdG9jb2wgKFQwODY5KSIsICJTdXBwbHkgQ2hhaW4gQ29tcHJvbWlzZSAoVDA4NjIpIiwgIlN5c3RlbSBGaXJtd2FyZSAoVDA4NTcpIiwgIlRoZWZ0IG9mIE9wZXJhdGlvbmFsIEluZm9ybWF0aW9uIChUMDg4MikiLCAiVHJhbnNpZW50IEN5YmVyIEFzc2V0IChUMDg2NCkiLCAiVW5hdXRob3JpemVkIENvbW1hbmQgTWVzc2FnZSAoVDA4NTUpIiwgIlVzZXIgRXhlY3V0aW9uIChUMDg2MykiLCAiVmFsaWQgQWNjb3VudHMgKFQwODU5KSIsICJXaXJlbGVzcyBDb21wcm9taXNlIChUMDg2MCkiLCAiV2lyZWxlc3MgU25pZmZpbmcgKFQwODg3KSJdfX0=
Click image to expand
Copyright © 2022 The MITRE Corporation. All Rights Reserved.